
International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 03 | Mar 2025 www.irjet.net p-ISSN: 2395-0072


International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 03 | Mar 2025 www.irjet.net p-ISSN: 2395-0072
Rajesh
1Student, Thakur College of Engineering & Technology, Maharashtra, India
2Professor, Thakur College of Engineering & Technology, Maharashtra, India
Abstract - In today's digital landscape, securing networks against cyber threats is of paramount importance. Theproject titled “Securing Network Using Honeypot and Detecting MaliciousIPAddresses”presentsacomprehensivesolutionto network security challenges. This Flask-based application integrates multiple features to ensure real-time monitoring, threat detection, and response, making it an essential tool for modern cybersecurity.
The application incorporates functionality to retrieve the server’s local IP address, resolve domain names to their corresponding IPs, and fetch geolocation details of IP addresses. By integrating with the honeydb.io API, it leverages honeypot intelligence to check whether a givenIPis flaggedas malicious. The Scapy library is employed for monitoring network traffic and detecting suspicious activity based on configurable parameters such as packet thresholds. Upon identifying malicious IPs, they are dynamically blocked using Windows netsh commands, and administrators receive realtime email alerts via the yagmail library.
Designed for ease of use, the application allows users to define monitoring parameters, block durations, and trusted IPs through a simple interface. Key technologies utilized include Flask for backend development, Scapy for traffic analysis, yagmail for email notifications, and netsh for IP blocking. Hosted on GitHub and Render, and developedusingAnaconda, the project addresses bothcurrent andemergingcybersecurity challenges, offeringa robust frameworkfor securingnetworks.
Key Words: Honeypot, Cybersecurity, Flask Application, Malicious IP Detection, Network Security, Real-time Monitoring,Threat
The exponential growth of digital technologies has significantlyincreasedthecomplexityandscaleofnetwork infrastructures. With this growth comes a surge in cyber threats, making network security a top priority for organizationsworldwide.CyberattackssuchasmaliciousIP activitiesposesevererisks,rangingfromdatabreachesto operationaldisruptions.Traditionalsecuritymeasuresoften fallshortinprovidingreal-timedetectionandmitigationof such threats, necessitating innovative and comprehensive solutions.
This project, “Securing Network Using Honeypot and Detecting Malicious IP Addresses,” addresses these
challengesbyintegratingadvancednetworkmonitoringand threat prevention mechanisms. By leveraging honeypot intelligence from the honeydb.io API, the application identifies malicious IP addresses and prevents potential attacks.Theinclusionofreal-timenetworktrafficanalysis through the Scapy library ensures early detection of abnormalactivity,whichisindicativeofmaliciousbehavior. MaliciousIPsaredynamicallyblockedusingWindowsnetsh commands,minimizingtheattack’simpactandsecuringthe network.
Theproject’suser-friendlydesignempowersadministrators to customize monitoring parameters and receive timely alerts through email notifications. Static HTML interfaces provideanintuitiveandlightweightuserexperience,making thetoolaccessibleforuserswithvaryinglevelsoftechnical expertise. Key technologies such as Flask for backend development, Render for deployment, and Anaconda for developmentenvironmentmanagementfurtherenhancethe project’sreliabilityandscalability.
Through its proactive and multifaceted approach, this projectoffersasignificantadvancementinnetworksecurity. Itaddressesthelimitationsoftraditionalmethods,ensuring networkintegrityandreducingtheriskofcyberattacks.The integration of honeypot intelligence and malicious IP detectionsetsanewstandardincybersecurity,makingthis projectavitalresourcefororganizationsaimingtosafeguard theirdigitalassets.
M. Kharrazi et al., "A Survey of Honeypot Techniques in Cybersecurity,"[1] This paper provides a comprehensive overviewofhoneypottechniques,includinglow-interaction, high-interaction, and hybrid honeypots. It highlights their differencesincomplexity,interactionlevels,andusecases. Advantages, such as cost-effectiveness and detailed threat analysis, and limitations, including resource demands and detection risks, are discussed. The authors emphasize selecting honeypot types based on organizational security needs.
H.HaslumandT.Fray,"TheUseofHoneypotsforIntrusion Detection in Industrial Control Systems,"[2] This study examineshoneypotdeploymentinIndustrialControlSystems (ICS),addressingchallengessuchasmimickingICSprotocols andensuringminimaldisruption.Casestudiesdemonstrate honeypots' effectiveness in detecting malware and

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 03 | Mar 2025 www.irjet.net p-ISSN: 2395-0072
unauthorizedaccess,emphasizingtheirroleinenhancingICS securitywhencarefullydesignedandmanaged.
J.Levineetal.,"AdvancedHoneypotArchitectureforNetwork ThreatDetection,"[3]Thispaperintroducesamulti-layered honeypot architecture for enhanced threat detection. The architecture employs low-interaction honeypots for initial probesandhigh-interactionhoneypotsfordetailedanalysis. Evaluation results show improved detection rates and insightsintoattackmethodologies,makingthearchitecture adaptabletovariousnetworkenvironments.
M.S.Hossainetal.,"AComparativeStudyofHoneypotTools for Malware Analysis,"[4] This paper compares honeypot tools, including Dionaea, Honeyd, and Kippo, based on deployment ease, malware capture effectiveness, and interaction levels. Each tool's strengths, such as Dionaea’s widemalwarecaptureandHoneyd’slowresourceusage,are highlighted.Theauthorsrecommendselectingtoolsbasedon specificusecases.
P. Spathoulas and S. K. Katsikas, "Dynamic Honeypot Deployment for Autonomous Security,"[5] This research proposesa dynamic honeypot framework for autonomous securitymanagement.Usingmachinelearning,honeypotsare deployed based on real-time network conditions. Experimentalresultsdemonstrateimprovedthreatdetection andreducedoverheadcomparedtostaticsetups,highlighting theframework'sadaptabilityandresilience.
K. G. Kyriakopoulos et al., "High-Interaction Honeypots: Design and Implementation Challenges,"[6] This paper discusses the challenges of high-interaction honeypots, including realistic system behavior, data volume management,andsecuritymaintenance.Theauthorsprovide guidelines for overcoming technical and operational difficulties,emphasizingtheimportanceofrobustdesignand maintenanceforeffectivedeployment.
L. Spitzner, "Honeypots and Honeynets: Analysis and Case Studies,"[7]Thispaperexploreshoneypotsandhoneynets, supportedbyreal-worldcasestudies.Honeynets,consisting of multiple networked honeypots, offer insights into coordinated attacks. Case studies demonstrate their effectiveness in detecting botnets and APTs, underscoring theirvalueinthreatintelligenceandnetworksecurity.
D. M. E. Inácio et al., "Effective Use of Honeypots for CybersecurityTraining,"[8]Thispaperhighlightstheuseof honeypotsincybersecuritytraining.Bysimulatingreal-world attack scenarios, honeypots provide hands-on learning experiences.Resultsfromtrainingsessionsshowimproved understandingofattacktechniquesanddefensivestrategies, demonstratinghoneypots'valueinpracticaleducation.
A. C. Clark et al., "HoneyBot: A Novel Approach to Botnet Detection Using Honeypots,"[9] This paper introduces HoneyBot,ahoneypotsystemdesignedforbotnetdetection.
Combininglowandhigh-interactionhoneypotswithmachine learning, HoneyBot effectively identifies botnet behaviors. Evaluation results demonstrate its efficacy in detecting command-and-control communications and propagation techniques.
S. L. Garfinkel, "Legal and Ethical Issues in Honeypot Deployment," [10] This paper addresses legal and ethical concerns in honeypot deployment, such as entrapment, privacyviolations,anddatacollection.Theauthorprovides guidelines for responsible deployment, emphasizing transparency, consent, and legal compliance to avoid potentialpitfalls.
The proposed system integrates advanced network monitoring and threat mitigation features to enhance cybersecurity.Theapplication’sarchitectureconsistsofthe followingcomponents:
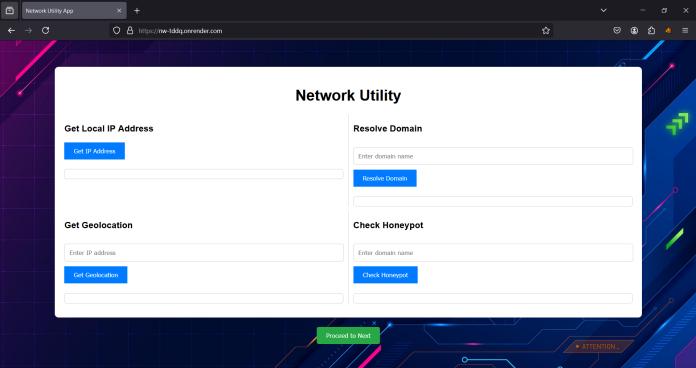
1.LocalIPRetrievalandDomainResolution:Theapplication retrievestheserver’slocalIPaddressandresolvesdomain namestoIPs,providingessentialnetworkdetails.
2.HoneypotIntelligenceIntegration:Usingthehoneydb.io API, the system checks IP addresses against a database of flaggedmaliciousIPs.
3.NetworkTrafficMonitoring:TheScapylibrarymonitors real-time network traffic, analyzing packets to detect suspiciousactivitybasedoncustomizablethresholds.
4.DynamicIPBlocking:IdentifiedmaliciousIPsareblocked dynamically using Windows netsh commands to prevent furthernetworkaccess.
5. Real-Time Alerts: The yagmail library enables email notifications, ensuring administrators are informed of securityeventspromptly.
6.UserInterface:StaticHTMLfilesprovidealightweightand intuitive interface for configuring monitoring parameters, blockdurations,andtrustedIPs.
7.DeploymentandScalability:Theapplicationishostedon Render and version-controlled on GitHub, ensuring accessibilityandcontinuousupdates.
The system begins by initializing and retrieving essential network details, such as the server’s local IP address and resolving domain names to IPs. This foundational step ensuresthattheapplicationisawareofitsenvironmentand ready to monitor incoming and outgoing traffic. Using the Scapy library, the application continuously analyzes realtime network traffic, focusing on packet data to detect

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 03 | Mar 2025 www.irjet.net p-ISSN: 2395-0072
irregularitiesoranomaliesthatmaysignalpotentialthreats, suchassuspiciousIPactivities.
When an IP address is detected, it is cross-verified with honeypot intelligence from the honeydb.io API. This integrationallowstheapplicationtocheckiftheIPhasbeen flaggedasmaliciousinaglobaldatabase.IfanIPisidentified asmaliciousorsuspicious,theapplicationtakesimmediate actionbydynamicallyblockingtheIPusingWindowsnetsh commands.ThisprocessensuresthattheIPcannotaccessor disruptthenetworkfurther.
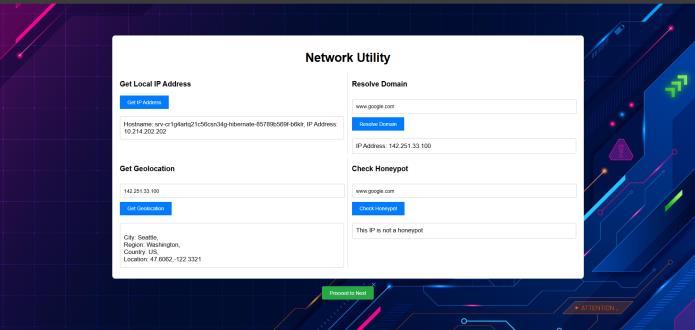
Tokeepadministratorsinformed,theapplicationgenerates real-timeemailalertsusingtheyagmaillibrary.Thesealerts containdetailedinformationaboutthedetectedthreatand theactionstaken,enablingpromptfollow-up.Additionally, the application’s interface allows administrators to customize monitoring parameters, such as setting packet thresholds,definingblockdurations,andmanagingtrusted IPs. The user interface, designed with static HTML files, providesanintuitiveandlightweightexperience,makingthe applicationaccessibleeventouserswithlimitedtechnical expertise.
The application is hosted on Render for deployment and version-controlled on GitHub, ensuring it is both scalable andreliable.Regularupdatescanbeseamlesslyintegrated, makingthetooladaptabletoevolvingcybersecurityneeds. Overall,thesystem’sworkingmechanismensuresarobust, real-time, and user-friendly approach to detecting and mitigatingnetworkthreats.
In conclusion, the project “Securing Network Using Honeypot and Detecting Malicious IP Addresses” offers a comprehensive and adaptable solution to modern cybersecurity challenges. By integrating honeypot intelligence, real-time threat detection, and malicious IP identification, the Flask-based application ensures robust networkprotection.Keyfunctionalitiessuchasgeolocation tracking, malicious IP detection through honeydb.io, and dynamicIPblockingusingnetshempowerorganizationsto respond effectively to evolving cyber threats. The use of Scapyfortrafficanalysisandreal-timeemailalertsfurther enhances its proactive security framework. Designed for simplicity and user accessibility, the application provides configurablemonitoringandanintuitiveinterface.Builtwith technologieslikeFlask,Scapy,andyagmail,andhostedon platforms such as GitHub and Render, this project demonstrates a forward-thinking approach to securing digitalinfrastructuresagainstemergingcyberrisks.
Lookingahead,theprojecthassignificantpotentialforfuture enhancements. These include integrating cloud-based honeypot systems for improved threat intelligence, supporting cross-platform IP blocking mechanisms, and incorporatingmachinelearningforanomalydetectionand predictiveanalytics.Additionally,thedevelopmentofrealtime visualization dashboards for monitoring network activity and expanding support for multiple operating systemsanddiversedeploymentenvironmentswillfurther enhance its versatility and effectiveness in addressing advancedcybersecurityneeds.
I would like to express my sincere gratitude to my guide, Prof.RajeshBansode,forhisvaluableguidanceandsupport throughout this project. I also extend my thanks to my institutionThakurCollegeofEngineering&Technologyand facultyforprovidingresourcesandencouragement.Special thanks to my peers and family for their motivation and understanding.
[1] M.Kharrazi,etal.,"ASurveyofHoneypotTechniquesin Cybersecurity," Journal of Cybersecurity and Privacy, vol.2,no.1,pp.15–30,Jan.2021.
[2] H. Haslum and T. Fray, "The Use of Honeypots for IntrusionDetectioninIndustrialControlSystems,"IEEE TransactionsonIndustrialInformatics,vol.15,no.7,pp. 3883–3892,Jul.2019.
[3] J. Levine, et al., "Advanced Honeypot Architecture for Network Threat Detection," IEEE Communications Magazine,vol.58,no.5,pp.42–49,May2020.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 03 | Mar 2025 www.irjet.net p-ISSN: 2395-0072
[4] M.S.Hossain,etal.,"AComparativeStudyofHoneypot Tools for Malware Analysis," International Journal of NetworkSecurity,vol.22,no.2,pp.190–200,Mar.2020.
[5] P. Spathoulas and S. K. Katsikas, "Dynamic Honeypot Deployment for Autonomous Security," IEEE Systems Journal,vol.14,no.2,pp.2053–2062,Jun.2020.
[6] K.G.Kyriakopoulos,etal.,"High-InteractionHoneypots: Design and Implementation Challenges," IEEE TransactionsonInformationForensicsandSecurity,vol. 14,no.6,pp.1506–1517,Jun.2019.
[7] L. Spitzner, "Honeypots and Honeynets: Analysis and CaseStudies,"IEEESecurity&Privacy,vol.17,no.5,pp. 50–57,Sep.2019.
[8] D. M. E. Inácio, et al., "Effective Use of Honeypots for Cybersecurity Training," IEEE Transactions on Education,vol.62,no.3,pp.208–215,Aug.2019.
[9] A.C.Clark,etal.,"HoneyBot:ANovelApproachtoBotnet Detection Using Honeypots," IEEE Access, vol. 8, pp. 12400–12411,Jan.2020.
[10] S. L. Garfinkel, "Legal and Ethical Issues in Honeypot Deployment,"IEEESecurity&Privacy,vol.16,no.6,pp. 79–85,Nov.2018.