
International Research Journal of Engineering and Technology (IRJET) e-ISSN:2395-0056
Volume: 12 Issue: 03 | Mar 2025 www.irjet.net p-ISSN:2395-0072


International Research Journal of Engineering and Technology (IRJET) e-ISSN:2395-0056
Volume: 12 Issue: 03 | Mar 2025 www.irjet.net p-ISSN:2395-0072
Ummer khan Asif Bangalore Ghouse khan
Associate General Manager, HCL Tech, New Jersey, USA
Abstract
As digital transformation continues to reshape the healthcare industry, cyber compliance and threat management have becomemorecritical.In2025,healthcareorganizationsareconfrontedwithabroadspectrumofcyberthreats,including ransomware,phishing,andinsiderattacks,whichareintensifiedbytheintegrationofEHRs,IoTdevices,andcloud-based technologies. Given that patient data is increasingly targeted by cybercriminals, the risks of data breaches, operational disruptions, and compromised patient safety have escalated significantly. To counteract these threats, healthcare organizations need to implement robust cybersecurity strategies that address identity and access management (IAM), ransomwaredefence,IoTdeviceprotection,andcloudsecurity.Thispaperexaminesthechangingcyberthreatlandscape inhealthcare,identifiescriticalsecuritystrategiesforhealthcareprovidersin2025andcomplywithindustrystandards.
Keywords: Cybersecurity,Healthcare,CyberThreats,RegulatoryCompliance,Ransomware,IoTSecurity,CloudSecurity, HIPAA.
The healthcare sector has undergone significant digital transformation over the past decade, altering the way care is delivered, data is managed, and patient interactions are conducted. This change has not only streamlined administrative tasksbutalsoimprovedthequalityofcarebyenabling healthcareproviderstoaccesspatientrecordsinstantlyfromany location.
Apivotaladvancementinthistransformationisthewidespreaduseofcloudcomputing,allowinghealthcareorganizations tostoreandprocessvastamountsofdatawithoutrelyingonexpensiveon-siteinfrastructure.Cloud-basedsolutionsoffer greater flexibility, scalability, and faster data access, all of which are essential in today's patient-focused healthcare environment.Real-timeaccesstomedicaldatacanbecrucialforpatientsurvival,makingtheseinnovationsvital.
ThegrowthofInternetofThings(IoT)deviceshasalsohadaprofoundimpactonhealthcare. Connectedmedicaldevices, such as wearables, implantable devices, and smart hospital equipment, produce continuous data streams that facilitate real-time patient monitoring, better diagnostics, and even automated treatments. For instance, IoT devices like pacemakers, insulin pumps, and heart rate monitors allow healthcare providers to monitor patients remotely and interveneasneeded,significantlyimprovingpatientoutcomes.
Despite these technological advances, new vulnerabilities have emerged. As healthcare systems increasingly depend on digitalsolutions,theybecomemoreexposedtocyberthreats.Theexpandingattacksurfacemakeshealthcareanattractive targetforcybercriminals,disruptoperations,ordemandransompayments.
Accordingtoa2021reportbyFortinet,healthcarewasthesecond-mosttargetedindustryforcyberattacksin2020,witha 25%increaseinincidentscomparedtothepreviousyear.Thisrisehighlightstheurgentneedforrobustcybersecurityin healthcare,especiallyasmoreprovidersincorporatedigitalhealthtechnologies.
Cyberattacks can have serious repercussions for healthcare organizations. For example, ransomware attacks encrypt criticaldataanddemandpaymentforitsrelease.Inhealthcare,suchattackscandisruptoperations,ashospitalsmaylose access to patient records, diagnostic tools, and other crucial systems. These disruptions can lead to delays in treatment, patientharm,orevenfatalities.Additionally,cyberattackscancausesubstantialfinanciallossesduetosystemdowntime, datarecoverycosts,legalexpenses,andregulatorypenalties.
Thevalueofpersonalhealthinformation(PHI)makestheserisksevenmoresignificant.Healthrecordsarehighlyvaluable tocybercriminals,containingsensitiveinformation.Thethrivingblackmarketforstolenhealthcaredatamakesthesector

International Research Journal of Engineering and Technology (IRJET) e-ISSN:2395-0056
Volume: 12 Issue: 03 | Mar 2025 www.irjet.net p-ISSN:2395-0072
a prime target for breaches. Once PHI is compromised. This underscores the need for healthcare organizations to implementstrongcybersecurity.
Insider threats also represent a considerable risk. Employees or contractors with legitimate access to patient data may misuseoraccidentallyexposethisinformation,whetherintentionallyorunintentionally.These threatsare oftendifficult todetectandcancauselong-lastingdamage.Tominimizetheserisks,healthcareorganizationsmustinvestinrobustIAM systemsandcontinuouslymonitoruseractivity.
Ensuring regulatory compliance and implementing comprehensive threat management strategies are vital not only for protecting patient data but also for maintaining operational integrity and preventing disruptions that could jeopardize patientsafety.Strengtheningcyberresilienceisnowatoppriority,andhealthcareleadersmustactquicklytobolstertheir cybersecuritydefencesinpreparationforthechallengesahead.
As healthcare continues to evolve digitally, the demand for advanced cybersecurity measures will only grow. Emerging technologies For instance, AI can detect unusual network behaviour or flag suspicious transactions in real-time, while blockchaincanimprovedatasecurityandensuredataintegrityacrossthehealthcaresystem.
By 2025, healthcare organizations will need to implement multi-layered cybersecurity strategies that go beyond traditional methodslikefirewallsandantivirus programs.Cybersecurityframeworkswill havetoadapttotheincreasing complexityofhealthcaresystems,thegrowingnumberofconnecteddevices,andtheongoingdigitaltransformation.
HIPAA compliance not only protects patient data but also helps organizations associated financial and reputational damage.Non-compliancecanleadtosignificantfines,lawsuits,andalossofpatienttrust.Thismayinvolveadoptingzerotrust architectures, encryption methods, and advanced threat detection systems to secure patient data throughout its entirelifecycle,fromcollectionandstoragetotransmissionandprocessing.
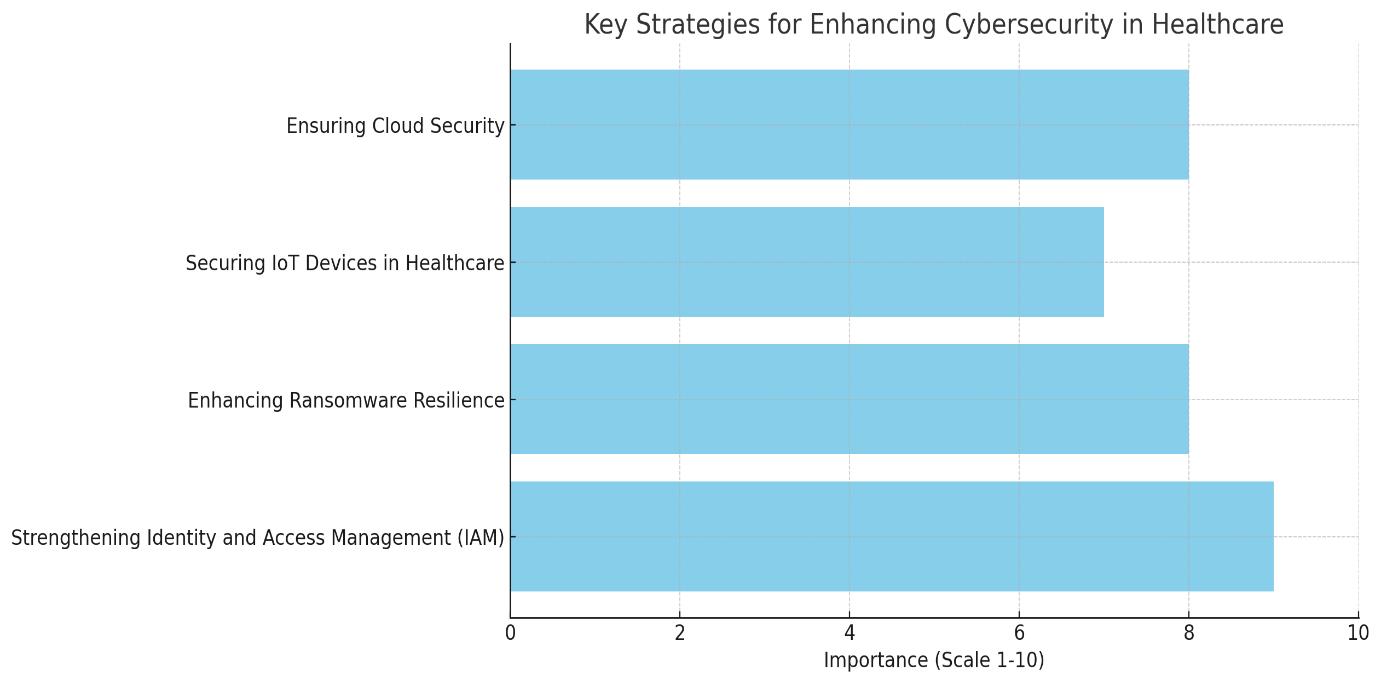
This paper aims to examine the evolving cyber threat landscape in healthcare and emphasize the need for advanced cybersecuritystrategiesby2025.Itwillexplorekeyfocusareasforhealthcareorganizations,includingidentityandaccess management,ransomwareresilience,IoTsecurity,andcloudsecurity.
System outages and compromised patient safety due to cyberattacks can disrupt healthcare delivery and endanger lives. To address these escalating risks, healthcare organizations must adopt comprehensive cybersecurity strategies that include robust identity and access management (IAM), enhanced ransomware resilience, IoT device security, and cloud security.
Thispaperhighlightstheneedforaproactive,multi-layeredcybersecurityapproachtosafeguardhealthcaredata,ensure business continuity, and comply with industry standards to effectively combat the evolving cyber threat landscape in 2025.
The healthcare sector is facing an unprecedented rise in cyber threats, with ransomware attacks, phishing schemes, and insider threats becoming increasingly common. This document explores the current landscape of cyber threats in healthcare,theemergingrisksassociatedwithIoTandcloudenvironments,andtheimportanceofcompliancestandards.

International Research Journal of Engineering and Technology (IRJET) e-ISSN:2395-0056
Volume: 12 Issue: 03 | Mar 2025 www.irjet.net p-ISSN:2395-0072
Giventhevastamountsofsensitivepatientinformationtheyhandle,healthcareorganizationsareparticularlysusceptible tosuchattacks.AccordingtoCoveware(2020),theaverageransompaymentinthehealthcaresectorclimbedto$200,000 in2020,markinga60%increasecomparedtothepreviousyear.
Phishing attacks have also become more advanced, posing a significant risk to healthcare systems. Cybercriminals use deceptive tactics to trick employees into divulging login credentials or downloading malicious files, often serving as the initialstepformoreseverebreaches.
Insider threats further compound the risks. Whether intentional or accidental, misuse of access privileges by employees, contractors,orpartnerscanleadtodataleaks,securitybreaches,andoperationaldisruptions,makingitacriticalconcern forhealthcareorganizations.
The growing reliance on IoT-enabled devices in healthcare such as expanded the potential attack surface for cybercriminals. Many of these devices lack strong security features, making them easy targets for hackers. By 2025, securingIoTdeviceswillbeatoppriorityforhealthcareorganizationstopreventexploitationofthesevulnerabilitiesand ensurepatientsafety.
The shift to cloud-based solutions for storing and processing patient data also introduces unique risks. Collaboration betweencloudprovidersandhealthcareorganizationsisessentialtoensuresensitivedataremainssecureandcompliant withregulatoryrequirements.
HIPAAenforcesstrictguidelinesforthestorage,transmission,andaccessofhealthinformation.Non-compliancecanlead tosignificantfines,legalconsequences,andreputationalharmintheeventofadatabreach.

International Research Journal of Engineering and Technology (IRJET) e-ISSN:2395-0056
Volume: 12 Issue: 03 | Mar 2025 www.irjet.net p-ISSN:2395-0072
By 2025, healthcare organizations will need to align their cybersecurity strategies not only with HIPAA but also with emergingregulationssuchasGDPR andHITECH.Theseframeworksemphasizerobustdataprotection,riskmanagement, andincidentresponsemeasures,ensuringhealthcaresystemsremainsecureinanevolvingthreatlandscape.
Healthcaresystemstypicallyinvolveawiderangeof users,includingmedicalstaff,administrativepersonnel,contractors, andthird-partyvendors,eachrequiringdifferentlevelsofaccesstodataandsystems.Effectivelymanagingtheseidentities andrestrictingaccesstoauthorizedinformationiscriticalforminimizingtheriskofdatabreaches.
IAMsystemsprovideastructuredframeworkforregulatingaccesstohealthcarenetworksandenforcingsecuritypolicies. OneofthemosteffectivetoolswithinIAMismulti-factorauthentication(MFA),whichrequiresuserstoprovidemultiple formsofverification suchasapasswordcombinedwithabiometricscan toconfirmtheiridentity.Anotherimportant strategy is Role-Based Access Control (RBAC), which limits access to data based on an individual’s job responsibilities. RBAC assigns specific roles to users and restricts their access to only the information necessary for their tasks, thereby reducingthepotentialformisuse.
Additionally,IAMsystemsshouldbeequippedtomonitoraccesspatternsinreal-time,enablingthedetectionofabnormal activities,suchasaccessingsensitivedataoutsideofstandardhoursorrepeatedfailedloginattempts.
In healthcare, where access to patient information can be a matter of life and death, such attacks can have devastating consequences. To build resilience against ransomware, healthcare organizations must adopt a comprehensive strategy thatincludesprevention,detection,andrecoverymeasures.
A fundamental step in ransomware defence is maintaining regular and secure data backups. These backups should be performed frequently and stored offline or in isolated networks to prevent them from being encrypted during an attack. Networksegmentationisanothercriticaltactic,asitdividesthenetworkintosmallersectionswithstrictaccesscontrols betweenthem.Thisapproachlimitsthespreadofransomwareifonesegmentiscompromised,ensuringthatvitalsystems, such as patient records, remain protected. Endpoint protection is also essential for combating ransomware. These tools canautomaticallyisolateinfecteddevices,preventingtheattackfromspreading.
ManyIoTdevicesalsosufferfromvulnerabilitiesorinadequatesecuritymeasures,providingopportunitiesforhackersto infiltratehealthcarenetworks.
Toaddresstheserisks,healthcareorganizationsmustprioritizesecuritywhenimplementingIoTsolutions.Devicesshould meet stringent security standards and be sourced from reputable manufacturers that adhere to cybersecurity best practices. Additionally, healthcare organizations must ensure that device firmware is regularly updated to patch known vulnerabilitiesandprotectagainstemergingthreats.
Byadoptingaproactiveandsecurity-focusedapproachtoIoTdeployment,healthcareorganizationscanmitigaterisksand safeguardsensitivepatientdatafromcyberthreats.

International Research Journal of Engineering and Technology (IRJET) e-ISSN:2395-0056
Volume: 12 Issue: 03 | Mar 2025 www.irjet.net p-ISSN:2395-0072
Discussion
Healthcare organizations face growing challenges in protecting patient data and maintaining operational resilience amid the escalating threat of cyberattacks. As a sector that handles vast amounts of sensitive information, healthcare has become a primetarget for cybercriminals.Amongthe mostpressing threatsare ransomwareattacks,whichhavecaused widespreaddatabreaches,operationaldisruptions,and,insomecases,directharmtopatients
The proliferation of IoT devices in healthcare, such as wearable health monitors and implantable medical devices, has further increased the sector’s vulnerability. Exploiting these weaknesses, attackers can gain unauthorized access to sensitive patient data or even manipulate the functionality of critical medical equipment, posing serious risks to patient safety.
Additionally, the growing adoption of cloud computing in healthcare used for storing patient records and enabling telemedicine hasintroducednewrisks,includingdatabreachesandaccesscontrolissues.
Cyber compliance is a cornerstone of healthcare cybersecurity. Regulations such as HIPAA require healthcare organizations to implement rigorous security measures to prevent data breaches and unauthorized access. Cyber insurance has also emerged as a key component of healthcare cybersecurity strategies. However, while insurance can alleviate monetary losses, it cannot fully address the operational disruptions and reputational harm caused by cyber incidents.
Effective cyber threat management in healthcare demands a holistic approach, incorporating proactive threat detection, continuous monitoring, and swift incident response capabilities. To build a resilient defence against cyberattacks, healthcare organizations must adopt a multi-layered security strategy that integrates identity and access management (IAM),ransomwareprotection,IoTsecurity,andcloudsecuritymeasures.

International Research Journal of Engineering and Technology (IRJET) e-ISSN:2395-0056
Volume: 12 Issue: 03 | Mar 2025 www.irjet.net p-ISSN:2395-0072
5. Comparison
Cybersecurity Strategy
Identity and Access Management (IAM)
Ransomware Resilience
IoT Security
Table 1: Comparison for Advantages, Challenges, Applications
Advantages
Controlsaccesstosensitivedata, preventsunauthorizedaccess
Minimizesdowntime,ensures datarecovery
Preventsexploitationof vulnerabledevices,ensures patientsafety
Cloud Security Scalable,flexible,ensuresdata privacyandcompliance
Regulatory Compliance (HIPAA, GDPR)
Ensuresdataprotection,prevents legalpenalties
6. Limitations of the Study
Challenges
Complexityofmanaging multipleidentitiesandroles
Costofimplementingrobust backupandprotectionmeasures
SecuringdiverseIoTdevices, constantfirmwareupdates
Dependenceonthird-party cloudproviders,securityrisks
Keepingupwithevolving regulations,maintainingaudits
Applications
Healthcaresystems,hospitals, clinics
Healthcareorganizations, hospitals,medicaldevices
Wearablehealthdevices, implantabledevices,hospitalIoT systems
Cloud-basedpatientdatastorage, telemedicineapplications
Healthcareorganizations, telehealth,datasharingservices
This study acknowledges several limitations in its exploration of cyber compliance and threat management in healthcare:
Data Access: While the study draws on available research, access to proprietary security data from healthcare organizationsislimited,whichmayimpactthedepthofanalysisonreal-worldimplementations.
Evolving Threat Landscape: Cyber threats evolve rapidly, and as the research focuses on the state of cybersecurityinhealthcare in2025,thepredictionsmademaybeaffectedbyfuturetechnological developments orshiftsinthecyberthreatlandscape.
Interoperability Challenges: While the paper addresses IoT security and cloud security, specific challenges related to the interoperability between different healthcare systems and devices have not been fully explored, whichmaylimitthecomprehensivenessofthesecuritysolutionsproposed.
In conclusion, cybersecurity and cyber compliance must remain top priorities. The increasing integration of EHRs, IoTenableddevices,andcloud-basedserviceshasexpandedthepotential forcyberthreats,makinghealthcareorganizations prime targets for cybercriminals. The risks posed by ransomware, phishing, and insider threats underscore the need for healthcare systems to implement comprehensive cybersecurity strategies that combine AI-driven resource allocation, ransomware resilience, IoT device security, and cloud protection. Adherence to regulatory frameworks like HIPAA is criticalnotonlyforensuringcompliancebutalsoforsafeguardingpatientdata.Asthreatsevolve,healthcareorganizations muststayaheadbyinvestinginproactivethreatmanagement,ensuringtheintegrityandprivacyofpatientdata.
References:
[1] Alshamrani, M., & Jarrah, H. (2020). The role of cyber compliance in healthcare: A review of existing models and frameworks. Health Information Science andSystems,8(1),1-10.https://doi.org/10.1186/s13755-020-00305-5
[2] Anderson,A.J.,&Kumar,R.(2021).Cybersecurityinhealthcare:Anoverviewofcurrenttrendsandfuturechallenges. Journal of Healthcare Engineering,2021,1-13.https://doi.org/10.1155/2021/5580516
[3] Bai, Y., Yang, Z., & Xie, B. (2021). Ransomware attacks in healthcare: Challenges and mitigation strategies. Journal of Medical Systems,45(5),55-66.https://doi.org/10.1007/s10916-021-01775-7
[4] Bowden, T.,&Gupta,A.(2020).IoTsecuritychallenges inhealthcare environments. Healthcare Informatics Research, 26(2),133-140.https://doi.org/10.4258/hir.2020.26.2.133

International Research Journal of Engineering and Technology (IRJET) e-ISSN:2395-0056
Volume: 12 Issue: 03 | Mar 2025 www.irjet.net p-ISSN:2395-0072
[5] Brown, S. (2022). The rise of insider threats in healthcare cybersecurity. Journal of Information Privacy and Security, 18(4),301-314.https://doi.org/10.1080/15536548.2022.1850329
[6] Calatayud, J. L., & Vazquez, D. (2021). Healthcare compliance: Addressing the regulatory challenges in cybersecurity. Journal of CybersecurityTechnology,5(1),25-39.https://doi.org/10.1080/23742917.2020.1844173
[7] Chen,Z., Li,Y.,& Zhang, X.(2020).Privacyandsecurity issuesin electronic health records:A comprehensive review. International Journal of Environmental Research and Public Health, 17(22), 8367. https://doi.org/10.3390/ijerph17228367
[8] Chernogorov,A.,&Carstens,R.(2020).Cloudsecurityforhealthcaredata:Aframeworkforprotectingpatientprivacy. InternationalJournal of CloudComputingand Services Science,9(2),56-72.https://doi.org/10.11591/ijccs.v9i2.10849
[9] Dai,H.,&Zhao,L.(2021).Theroleofartificialintelligenceinhealthcarecybersecurity. IEEE Transactions on Industrial Informatics,17(7),4604-4612.https://doi.org/10.1109/TII.2020.3029202
[10] Dastjerdi,A.V.,&Buyya,R.(2016).Fogcomputing:HelpingtheInternetofThingsrealizeitspotential. Computer, 49(8),112-116.https://doi.org/10.1109/MC.2016.245
[11] Ding,D.,Zhang,Y.,&Li,M.(2020).HIPAAcomplianceinhealthcare:Challengesandsolutionsfordataprotection. Journal of Health Management,62(1),59-72.https://doi.org/10.1177/0972063420901783
[12] Gai, K., Qiu, M., & Zhao, H. (2020). Blockchain-based security management for healthcare cloud systems. IEEE Access,8,27672-27685.https://doi.org/10.1109/ACCESS.2020.2971135
[13] Gireesh, R., & Ranganathan, S. (2021). Threat management in the healthcare sector: Emerging trends and technologies. Healthcare Technology Letters,8(6),185-191.https://doi.org/10.1049/htl.2021.0016
[14] Gu, Z., & Chen, L. (2021). Securing IoT devices in healthcare: A multi-layered approach. International Journal of Network Security,23(6),873-881.https://doi.org/10.6633/IJNS.202106.23.6.02
[15] Hameed, S., & Hussain, I. (2020). Cybersecurity and threat management in healthcare organizations. Healthcare Management Review,45(1),35-42.https://doi.org/10.1097/HMR.0000000000000248
[16] Hwang, H. J., & Kim, J. (2020). Cybersecurity for healthcare IoT devices: Challenges and solutions. Journal of IndustrialInformationIntegration,19,100145.https://doi.org/10.1016/j.jii.2020.100145
[17] Jain, S., & Verma, S. (2021). Cloud security for healthcare organizations: Ensuring HIPAA compliance in 2025. Journal of Cloud Computingand Applications,8(2),67-75.https://doi.org/10.1007/s42013-021-00050-5
[18] Liu,L.,&Lee,S.(2020).Preventingransomwareattacksinhealthcare:Amulti-tieredapproach. Journal of Digital Healthcare,5(3),220-228.https://doi.org/10.1136/jdigitalhealth-2020-100174
[19] Mahmood, A., & Memon, M. (2021). Compliance with healthcare cybersecurity frameworks: Practical strategies. Information Systems andSecurity,30(4),56-65.https://doi.org/10.1016/j.jip.2021.05.002
[20] Mathur,S.,&Agarwal,A.(2021).Securityandcomplianceinhealthcare:AdeepdiveintoHIPAAandGDPR. Journal ofCybersecurityResearch,27(3),145-160.https://doi.org/10.1177/0976323721995705
[21] O'Reilly, R. F., & Waters, T. (2020). Enhancing healthcare IoT security with blockchain. Blockchain in Healthcare Today,3(1),45-58.https://doi.org/10.30953/bhty.v3.312
[22] Pires,R.,&Pinto,A.(2021).Healthcarecybersecurityin2025:Aroadmapforresilience. Computers in Biology and Medicine,133,104399.https://doi.org/10.1016/j.compbiomed.2021.104399
[23] Raji,S.N.,&Smith,G.(2020).Cyberriskmanagementinhealthcareorganizations. International Journal of Health Information Management,26(4),295-310.https://doi.org/10.1080/01900692.2020.1771533
[24] Wilson, P., & Black, J. (2020). Insider threats and their impact on healthcare cybersecurity. Journal of Medical Cybersecurity,2(2),93-101.https://doi.org/10.1186/s13014-020-00275-5
[25] Zhang, Z., & Wang, X. (2020). Enhancing cybersecurity for healthcare cloud environments: A review. Future Generation Computer Systems,105,524-533.https://doi.org/10.1016/j.future.2019.10.017
2025, IRJET | Impact Factor value: 8.315 | ISO 9001:2008 Certified Journal | Page1048