Start Engineering CYBERSECURITY CAREER GUIDE
Prepare for today’s hottest career — now transformed by AI. LEARN ABOUT: Job paths, where and what to study, salary info, and more.

REVIEW COPY
PLUS: Go inside the world of AI-powered cyber defense. Explore global dangers — from China’s cyber reach to relentless ransomware. Get college credit now with dual enrollment.
Cyber Meets AI
welcome
Hey there,
Cybercrime is one of the biggest threats in the world today — and cybersecurity is how we fight back. It’s a fast-moving, high-impact field that needs people with all kinds of talents. That could include you.
You don’t have to look far to see why cybersecurity matters.
⊲ In 2024, cybercrime caused an estimated $9.5 trillion in global damage — making it one of the world’s largest “economies,” right behind the U.S. and China.
⊲ One cyberattack in 2021 shut down fuel pipelines in the southeastern U.S. for 10 days — and attacks like that are only increasing.
⊲ Ransomware hits businesses every few seconds, and some hackers demand up to $75 million to give back control of stolen systems.
So yes — cybersecurity is serious. But it’s also full of opportunity.
⊲ It’s purposeful: You’ll help protect the systems that power everyday life.
⊲ It’s well-paid: The average salary is around $125,000, and demand keeps growing.
⊲ And it’s wide open to everyone: Whether you’re into coding, psychology, law, or public policy, cybersecurity needs your skills.
When we first published this guide in 2018, cybersecurity education was just beginning to take off. Since then, the field has exploded — shaped by new technologies, new threats, and especially by the rise of artificial intelligence (AI). Today, you’ll find cybersecurity courses in high schools, community colleges, and universities across the country — plus new apprenticeship and certification programs that help students learn while they earn.
This updated edition is here to help you navigate it all. You’ll see how AI is changing both cybercrime and the tools we use to fight it. You’ll explore the growing need for skilled professionals across industries — from hospitals to power grids — and discover where you might fit in.
Whether you dream of working for the government, defending major companies, or helping small businesses stay safe, cybersecurity skills can open the door.
REVIEW COPY
We created this guide with input from experts at the NSA, Department of Homeland Security, National Initiative for Cybersecurity Education, and top industry professionals. Our goal? To give you the clearest, most exciting picture of what this field is really like — and why we need smart, driven people like you to join it.
Thanks for reading. Now let’s see where this journey might take you.

Robert Black Publisher, Start Engineering bblack@start-engineering.com




what is cybersecurity?
Are you into computers and video games? Solving puzzles and mysteries? Writing code and programming computers? Tracking criminals? Defending our country? Then cybersecurity could be for you! Because CYBERSECURITY IS...

Defending Our Nation
America is under constant cyberattack. Criminal hackers — sometimes working alone, other times backed by foreign governments — try every day to break into U.S. computer systems to steal data, disrupt operations, or spy on government agencies. These attackers come from countries like Russia, China, North Korea, and Iran, and some of the most damaging cyber incidents in recent years are linked to them. In 2019, Russian hackers used a software update from the Texas-based company SolarWinds to sneak into networks at places like the U.S. Department of Defense and Microsoft. In 2021, Chinese hackers targeted Microsoft Exchange servers, affecting over 30,000 organizations. And in 2025, hackers linked to the Chinese government found a flaw in Microsoft’s software and broke into U.S. government systems, stealing sensitive files.
Securing Our Phones
Because telecommunications companies build, control, and operate the nation’s critical information systems, they’re prime targets for cybercriminals and foreign adversaries. In January 2023, T-Mobile announced that a cyberattack on its systems affected more than 37 million customers. Some of the exposed data included names, Social Security numbers, and birthdays. The massive breach comes on the heels of five, yes five, other T-Mobile leaks in recent years and a SIM-swapping attack earlier in 2021. In these incidents, hackers may have used compromised phone numbers to break into more accounts — like email, banking apps, or social networks — to steal identities and drain bank balances. The FCC came down hard. T- Mobile reached a $31.5 million settlement with the agency in 2024, agreeing to fines and to overhaul its cybersecurity. About time!
REVIEW COPY
Ransomware is also a growing threat. Hackers lock up computer systems and demand payment to release them. One major example: the 2021 ransomware attack on Colonial Pipeline, which disrupted fuel supplies across the East Coast. Fighting back takes constant work. The U.S. Cyber Command (CYBERCOM) leads this 24/7 mission, working with experts across the government to detect threats, protect systems, and respond when attacks happen. They’re joined by other agencies like the Cybersecurity and Infrastructure Security Agency (CISA) and the FBI, which track attacks, support victims, and help strengthen national defenses. See pages 48-51 to learn more about government efforts.


Safeguarding Our Money
Forget ski masks — today’s bank robbers use malware instead. Big banks now face cyberattacks nearly every day, according to JPMorgan Chase. Hackers break into computer systems to steal personal data like names, Social Security numbers, and account info. In a 2022 breach at Flagstar Bank, over 1.5 million customer records were exposed. Thieves can use this stolen data to take out loans or commit identity theft — without ever stepping inside a bank. These attacks are costly. The average data breach in finance now costs more than $5.7 million, and banks are spending big to fight back. Bank of America alone invests over $1 billion a year in cybersecurity. But vulnerabilities remain. A recent report found that over 90 percent of ATMs can still be hacked. Once inside, hackers can move money between accounts, lock staff out of critical systems, or even install ransomware to demand payment in exchange for restoring access. Yikes!

$ 75,000 - $ 125,000



Protecting Athletics
The 2028 Olympics in Los Angeles won’t just be about sports — they’ll also need strong cybersecurity. Big events like this can be targets for hackers trying to steal information or cause problems. To stay safe, the LA Olympics team has hired a Head of Cybersecurity to protect the Games’ technology. They’re working with companies like Cisco to help keep networks secure. These efforts will protect athletes, fans, and officials from cyber threats. Just as security guards protect the stadium, cybersecurity teams protect computers and data — making sure the Games run smoothly and everyone stays safe, on and off the field.
Guarding School Data
Think about the wealth of information your school accumulates about you: your grades, test scores, health history, your Social Security number ... and, of course, also your parents’ names and addresses, and if you attend a private school, possibly banking information, too. This treasure trove of data is the reason cybercriminals are increasingly targeting schools. During the 2022 school year, a massive cyberattack hit the Los Angeles school system, putting the private data of more than 400,000 students at risk. Similarly, in 2023, both the Tucson, AZ, and Minneapolis, MN, school districts experienced cyberattacks, leading to the exposure of private student information on the dark web. The FBI is actively investigating these incidents, but schools must remain constantly vigilant to protect their data.
Protecting the Food Supply
Farms and food factories are the newest targets for cybercriminals. The agriculture industry helps feed the world — but its growing reliance on computers makes it vulnerable to attacks. In June of 2025, United Natural Foods Inc. (UNFI), a major U.S. grocery distributor, was hit by a cyberattack that disrupted ordering and shipping systems, leaving some store shelves empty. Early in 2025, more than 80 ransomware attacks were reported in the food and agriculture sector — more than double the number from the year before.
into smaller companies to access larger, wealthier partners upstream. The government has started to respond, with new cybersecurity bills and presidential action focused on protecting critical industries like food and agriculture. But many food companies still need to step up their defenses — and that means more opportunities for cybersecurity professionals in an unexpected but essential field.
what is cybersecurity? REVIEW COPY
Hackers know that many food companies — especially small to mid-sized ones — use outdated systems and may not have strong cybersecurity teams in place. The risks are serious. Hackers could take over computer systems that control ingredient amounts or cooking temperatures, possibly contaminating food. They might also steal secret recipes or production methods to sell to competitors. Even tampering with safety records could lead to unsafe products reaching grocery stores.
Cybercriminals also exploit the inter-connected supply chain, breaking

Any device connected to the internet is vulnerable to cyberattacks. So, how many devices worldwide are connected to the internet?
16.7 billion
This number is set to explode in the coming years as internet consumption rises. By 2030, there could be 40 billion connected devices.
REVIEW COPY
Shielding Our Social Sites
Hackers are getting smarter — and more personal — on social media. Instagram users continue to be popular targets for phishing attacks that trick them into giving up their login info. In one case, users received fake messages claiming their posts had violated copyright rules. The link to “resolve the issue” actually led to a scam site that stole their login credentials. Hackers took over accounts, changed passwords, and demanded ransoms — sometimes as high as $40,000.
Ensuring Safe Drinking Water
Water systems are even a target for hackers. In 2021, a cyberattack on a Florida water plant made national headlines when a hacker tried to raise levels of sodium hydroxide — a chemical used to treat water, but toxic at high doses. The attack was stopped in real time when an operator noticed his computer cursor moving on its own and quickly reversed the changes. Around the same time, another hacker used a former employee’s login to access a San Francisco Bay Area plant and delete key treatment programs. Many water utilities still rely on outdated software and weak security. The EPA and DHS have pushed for stronger protections — but experts warn that vulnerabilities remain in this essential infrastructure.


In early 2025, scammers impersonated Google security teams to target high-profile users — including Instagram head Adam Mosseri, who narrowly avoided falling for a fake email and phone call designed to steal his credentials. Other phishing campaigns have impersonated Meta Support, used fake chatbot “help” accounts, and sent fraudulent emails to business and influencer accounts, trying to trick users into clicking malicious links.
Even with new security features meant to help users lock out intruders and recover hacked accounts, phishing scams on Instagram are evolving quickly.
Safeguarding Retailers

Retailers are juicy targets for hackers. They handle tons of money, collect millions of credit card numbers, and often use older systems that aren’t fully protected. Many employees haven’t been trained to spot online threats, which makes it easier for cybercriminals to break in. Ransomware is a top threat. In 2023, big companies like Clorox and KFC’s parent company were hit by attacks that shut down systems and cost millions of dollars. Some stores couldn’t process payments or restock shelves. Online shopping comes with new risks, too. Hackers use bots to steal passwords, grab customer data, and even drain gift cards or loyalty points. These attacks can slow down websites and damage customer trust. The effects can be serious — lost money, lost data, and lost customers. To protect themselves, many stores are stepping up their game: they’re training workers to spot scams, updating their technology, and using tools powered by artificial intelligence to catch threats faster. The battle is ongoing.

Driving Improvements
Cars used to break down because of mechanical problems. Today, many car issues start with computers. Modern vehicles rely on software to connect to phones, stream music, provide navigation, and even control safety features like sensors, steering, and braking. But that tech also makes cars vulnerable — just like computers or phones. If a hacker gets in, the results can be deadly. One consumer watchdog warned that a cyberattack could potentially disable systems like brakes and airbags, leading to thousands of deaths. Even scarier, some malware “worms” can jump from car to car, spreading through networks and causing crashes. As driverless cars become more common, the risks will only grow. The same tools that make driving safer have opened the door to new cyber threats — and cybersecurity experts are racing to keep up.
Keeping Medical Info Private
what is cybersecurity? REVIEW COPY
Medical professionals used to rely on paper records, but now your vitals, diagnoses, and prescriptions are stored electronically to help share information quickly. That makes healthcare faster — but also more vulnerable. In 2023, a Tallahassee hospital system was hit by ransomware and had to cancel nearly all services for two weeks. Between 2009 and 2022, over 5,150 database breaches exposed more than 382 million records, according to the HIPAA Journal. Medical devices are under attack, too. In early 2025, experts warned that legacy devices like infusion pumps and monitors can be hacked — potentially causing them to malfunction during surgery or deliver dangerous drug dosages. Researchers are also seeing risks in networked medical sensors, where malware and Distributed Denial-of-Service (DDoS) attacks could interrupt critical patient-monitoring systems. Scary!

REVIEW COPY

Protecting Gamers
Video games are more popular than ever — and so are the cyberattacks aimed at them. In 2023, cyberattacks on gaming companies nearly doubled from the year before. Hackers used tactics like Distributed Denial-of-Service (DDoS) attacks, flooding game servers with traffic until they crashed, making games impossible to play and stealing valuable data in the chaos. In one major breach, Activision — makers of Call of Duty — suffered a data leak that exposed sensitive employee information. Around the same time, Insomniac Games, the studio behind the Spider-Man series, was hit with ransomware that compromised game development files and employee records.

Why target video games? Hackers often aim to steal source code, which can be sold illegally, used to create cheats, or leaked for bragging rights. Others go after player accounts, grabbing emails, passwords, and payment info to sell on dark web markets. Popular games like Minecraft, Grand Theft Auto, and Call of Duty are often used as bait. Cybersecurity researchers found that between 2024 and early 2025, there were more than 19 million attempts to trick people into downloading fake versions of these games filled with malware.
DID YOU KNOW?
1. Cybersecurity isn’t just about computers. Sure, some people in cybersecurity write code — but others focus on creating smart rules and policies to keep information safe. There are also digital detectives who investigate how a hack happened and who was behind it.
(Check out page 36!)
2. People skills matter — a lot.
You don’t need to be a tech genius to succeed. Problem-solving, teamwork, and good communication are some of the top skills cybersecurity employers look for.
3. Cybersecurity needs all kinds of minds.
The best teams are made up of people with different backgrounds and experiences. That includes women and minorities, who bring fresh perspectives that help spot risks others might miss. (See page 40!)
For more myths and truths, see page 54.
How AI Fuels Cybercrime
Hackers use AI to attack faster. Cyber defenders use it to fight back.
Artificial intelligence isn’t just for making weird AI-generated images or finding homework help online. It’s also a weapon — and both cybercriminals and cybersecurity experts are using it in a high-speed battle that affects everyone who goes online.
rewrote its own code in real time to dodge antivirus tools — a first in cybercrime history.
But the good guys are fighting back. Cybersecurity companies use AI to spot strange behavior on networks, block suspicious traffic, and patch flaws in computer systems. One of Google’s AI tools recently found a major bug in code used by billions of devices — possibly the first time a bot beat hackers to the punch.
AI Can Supercharge Cybercrime
artificial intelligence REVIEW COPY
The bad guys are using AI to pull off smarter, faster attacks. Bots and AI models are now doing the dirty work of hackers. They’re writing malware, generating deepfakes, and sending out phishing scams that look shockingly real. During a recent conflict between Israel and Iran, AI even powered waves of online propaganda and fake news. And since ChatGPT launched in late 2022, phishing attacks have increased more than 40 times, and deepfakes have surged 20 times.
Some of these AI-driven attacks don’t even need human hackers once they start. “Autonomous malware” can learn from its environment and adapt its behavior to stay hidden. In 2024, several global companies were hit by ransomware that
Cybercrime used to be a slow catand-mouse game between human hackers and defenders. Now, with AI, everything happens at lightning speed. Hackers can try hundreds or thousands of attacks at once — and the more they try, the more likely they are to succeed. That’s why industry experts project that the global cost of cybercrime could exceed $23 trillion per year by 2027, a figure higher than the total economy of many large countries.

Here’s how AI is fueling cybercrime: Deepfakes: Fake videos or audio that look and sound real — used to scam people or spread disinformation.
Phishing scams: AI-written emails and messages are now error-free, customized, and much harder to spot.
Smart attacks at scale: AI bots can scan thousands of networks, find weaknesses, and launch attacks at a volume humans never could.
Self-hiding malware: Some AI-generated code can change itself to avoid detection.
Fake identities: Chatbots can
create fake personas, write social media posts, and even impersonate real people to trick victims.
REVIEW COPY
Another growing concern is data poisoning — when attackers slip bad data into the systems that train AI models. That can cause the AI itself to make wrong decisions, ignore real threats, or even open doors for hackers.
Experts also worry about “prompt injection” attacks, where hackers trick chatbots or automated systems into revealing secrets or taking unsafe actions. These new kinds of cyberattacks don’t just target people — they target the AIs themselves.
Cyber Defenders Use AI, Too Thankfully, AI is also a powerful tool for defenders. Cybersecurity experts use it to:
Spot unusual activity — 24/7 — that signals a possible attack.
Find (and fix) software weaknesses before hackers do.
Block attacks automatically, often faster than a human can respond.
AI is also helping cybersecurity teams manage the massive flow of alerts that come in every day. Some large organizations receive millions of warnings daily — far more than humans could review. AI helps sort real threats from false alarms, allow-
ing security experts to focus on what really matters. And as quantum computing advances, AI will play an even bigger role in creating new kinds of encryption strong enough to protect future systems. The race between AI-powered offense and AI-powered defense is more important than ever.
The fight between AI-powered attackers and AI-powered defenders isn’t science fiction — it’s happening right now, every second. The same technologies that make our lives easier also make cybercrime more dangerous. Understanding how AI shapes cybersecurity is a safety issue for everyone who goes online.
ATTACKS SPREAD ACROSS
You’d think things would slow down after the FBI and other agencies took down some of the biggest ransomware gangs in 2023. But in 2024, attacks hit record highs instead. Many of the groups just rebranded and came back even stronger — with new tools, new targets, and even more money on the line.
Ransomware is when hackers lock up a system — like a hospital network or city database — and demand money to unlock it. These attacks have caused more than $40 billion in damages across the U.S. in 2024, and some even put lives at risk.
Here are some of the most serious ransomware attacks in 2024:
JANUARY
⊲ Fulton County, GA: Hackers knocked out government systems, so workers had to go back to paper forms.
⊲ Bucks County, PA: 911 computers in police cars were hacked. The National Guard stepped in to help answer emergency calls for 650,000 people.

ransomware REVIEW COPY
FEBRUARY
⊲ Lurie Children’s Hospital (Chicago): Hackers shut down hospital tech and leaked 600 gigabytes of patient data after a $3.7 million ransom wasn’t paid.
⊲ California SEIU Union: Personal and salary data of workers was stolen.
MARCH
⊲ Crinetics Pharma: Hackers demanded $4 million after stealing private research data.
⊲ MarineMax: Data on wealthy yacht buyers was stolen and leaked.
APRIL
⊲ Omni Hotels: Hotel check-ins and reserva-
tions across the U.S. were frozen.
⊲ UnitedHealth: Hackers stole 6 terabytes of patient data. The company paid $22 million to get it back.
MAY
⊲ Wichita, KS: Airport flights and online payments were shut down.
ACROSS THE U.S.

app went down, and thousands of employee records were stolen.
⊲ CDK Global: Thousands of car dealerships couldn’t operate. A ransom was paid to restore systems.
REVIEW COPY
⊲ Ohio Lottery: Info on 500,000 players was stolen.
⊲ Ticketmaster: Hackers grabbed credit card info from over 550 million people and tried selling it on the dark web.
JUNE
⊲ Panera Bread: The company’s website and
JULY
⊲ Disney: Hackers leaked unreleased movies and artwork to support “artist rights.”
⊲ Rite Aid: More than 2 million patient records were stolen.
AUGUST
⊲ Columbus, OH: Hackers leaked 3 terabytes of stolen data when the city refused to pay.
⊲ Sumter County, FL Sheriff: Hackers stole passport and ID info and demanded half a million dollars in Bitcoin.
SEPTEMBER
⊲ Stillwater Mining Co.: Hackers got into employee records and went unnoticed for months.
OCTOBER
⊲ UMC Health System (TX): Ransomware forced a hospital to send patients elsewhere.
WHO’S BEHIND THESE RANSOMWARE ATTACKS?
Even though law enforcement has taken down some major hacking groups, new ones keep popping up — and some old ones just change names and come back stronger. Here are a few of the most dangerous ransomware gangs in 2024:
LockBit: This Russian group is one of the biggest players. They run “Ransomware as a Service,” meaning they let other hackers use their tools for a cut of the profits. Even after a big bust in 2023, LockBit is still the most active gang out there.
ALPHV/BlackCat: One of the most advanced ransomware crews around. They target both Windows and Linux systems and are known for using a “triple extortion” strategy — stealing your data, locking your files, and threatening to crash your website all at once.
Rhysida: A newer gang that’s gotten scary fast. They started off small but now go after big targets like hospitals and city governments. Their tech is getting better with every attack.
Other Groups to Watch: Hackers from groups like Hunters International, ShinyHunters, 8Base, and BlackSuit are still causing trouble. And new names like DragonForce and RansomHub are quickly climbing the ranks.
NOVEMBER
⊲ Krispy Kreme: Online orders and deliveries were frozen during a cyberattack.
DECEMBER
⊲ Rhode Island State Services: Benefits were delayed, and personal data was exposed.
These attacks show just how bold and widespread ransomware threats have become. From hospitals and airlines to bakeries and game studios — no one’s off-limits. That’s why we need smart, skilled cybersecurity pros to help defend our digital world.
espionage
Conflicts With China Escalate
Hacking, espionage, and security
threats.
In June 2025, the Associated Press reported that Chinese government hackers had secretly installed malware on the smartphones of Americans in sensitive positions — like politicians, journalists, and business leaders. The hackers didn’t even need the victims to click anything. Just by visiting the wrong website, their phones were silently infected, allowing outsiders to track their location, steal messages, and possibly activate microphones and cameras.
This kind of attack shows just how advanced cyber spying has become — and how much power it gives to those who know how to use it.
Just a few months ear-
lier, in December 2024, another major breach made headlines. Chinese state-backed hackers broke into the U.S. Treasury Department’s systems. They used a flaw in a third-party cybersecurity service to sneak past defenses and access employee computers and unclassified files. It was a clear sign that even top government agencies are vulnerable — and that China’s cyber strategy is growing bolder.
What’s China After?
China has developed sophisticated cyber capabilities, many of which are tied to Advanced Persistent Threat (APT) groups such as APT41. These groups often focus on:
Spying on U.S. military and government systems.
Stealing valuable technology from companies.
Notable Attacks from the Past
Other major cyberattacks attributed to Chinese hackers have caused significant disruptions in the U.S.:
REVIEW COPY
Gathering personal information that can be used for future intelligence or influence.

1. Office of Personnel
REVIEW COPY

It is widely believed that Chinese hackers were behind this breach, gathering sensitive information that could be used for intelligence purposes.
2. Equifax Breach (2017): Chinese hackers stole data from 145 million Americans in one of the largest data breaches in U.S. history. The attackers accessed Social Security numbers, credit card information, and other personal details, causing massive security concerns.
3. Microsoft Exchange Hack (2021): This hack exploited vulnerabilities in Microsoft’s email servers, affecting thousands of organizations. The U.S. government publicly blamed China for the attack, which disrupted services worldwide.
Why It Matters
Cyberattacks like these aren’t just about stealing data. They’re part of a larger competition between China and the U.S. over technology, military power, and global influence. And they make one thing clear: the world needs more cybersecurity experts who can keep up with fast-moving threats.
U.S. Responses
Department of Justice has indicted multiple Chinese hackers for their involvement in these attacks, although these individuals are unlikely to face trial in the U.S.
Sanctions: The U.S. has imposed sanctions on Chinese companies and individuals linked to cyber espionage, restricting their ability to do business with American firms.
Alliances: The U.S. collaborates with global partners through organizations like the Five Eyes alliance, an intelligence-sharing partnership among five countries (the U.S., the United Kingdom, Canada, Australia, and New Zealand) to share intelligence and strengthen cybersecurity efforts against threats from China.
Looking Ahead
As technologies like 5G and artificial intelligence become more prominent, cyberattacks are expected to increase — and get harder to stop. For students thinking about a career in tech, learning about cybersecurity now means being part of the front line tomorrow. Management (2015): This attack exposed the personal data of over 22 million federal employees.
To push back, the U.S. has taken actions like: Indictments: The U.S.
The Cyber Field Is Changing
AI is rewriting the rules of defense — and raising the bar for the next generation
Cybersecurity remains one of the fastest-growing, most essential fields in the world. Every company, government agency, and school depends on people who can protect networks, data, and devices from attack. But as cyber threats become more sophisticated — and as artificial intelligence (AI) changes both sides of the fight — employers are raising the bar for who they hire. That means getting started takes more preparation than it used to, but the rewards are still strong: steady job growth, good pay, and work that truly matters.
Why the Change in Hiring Requirements? Blame AI.
A few years ago, a basic certification or bootcamp might have been enough to land a first job. Today, many entry-level postings ask for ALL of the following:
A bachelor’s degree in cybersecurity, computer science, or information technology.
the AI effect REVIEW COPY
Certifications like CompTIA Security+, Google Cybersecurity, or Certified Ethical Hacker (CEH).
Hands-on experience in IT or networking — often one to three years.
The reason for these higher expectations is simple: the job itself is changing. As artificial intelligence takes over more of the routine work in cybersecurity — like scanning for threats or blocking simple attacks — companies now need experts who can

Changing Quickly
generation of cyber pros.

handle the complex problems AI can’t. The result: higher expectations for new hires, and new skills to match.
At the same time, AI is transforming the field itself. As explored in H ow AI Fuels Cybercrime (page 10), artificial intelligence has become both a new weapon and a new shield in digital security. Security teams now use AI tools to detect attacks faster, analyze huge volumes of data, and even predict new threats before they happen. But hackers use AI, too — writing more convincing phishing messages, generating deepfakes, or automating password attacks. This “AI arms race” means tomorrow’s cybersecurity professionals will need new kinds of skills.
The Rise of AI-Driven Cybersecurity
AI has become a powerful ally for defenders — and a dangerous tool for attackers. Here’s how it’s changing the job:
Smarter Threat Detection: AI systems can scan millions of data points every second to flag suspicious activity humans might miss.
Faster Response: Automated tools can quarantine infected devices or block attacks instantly.
Predictive Security : Machine-learning models study past incidents to spot early warning signs of new ones.
AI-Powered Threats: Hackers now use AI to generate realistic fake messages, clone voices, and even disguise malware.
Because of this, the next generation of cyber professionals will need to understand how AI works — not just how to stop it. Learning basic AI and data analysis skills, such as Python programming or understanding how algorithms make decisions, can make students stand out. Turn the page to learn more!
Be Safe — and Be Good
Make smart online — and IRL — decisions.
When people think of cybersecurity, they often picture complicated software or high-tech firewalls. But here’s the truth: most cyber problems happen because of people, not computers. In fact, around 95 percent of data breaches start with a simple mistake — like clicking a sketchy link or downloading something you shouldn’t. Even the best tech in the world can’t stop someone from being careless or rushing through things.
or your pet’s name. See the box on the next page for ideas for how to create great passwords.
2. Spot the scam.
Some phishing emails look very real. They might say you’ve won a prize, need to verify your account, or even pretend to be your teacher or favorite brand. Before clicking anything, pause. Look at the sender’s email, check for weird language, and don’t share personal info unless you’re sure it’s legit.
cyber safety REVIEW COPY
That’s why understanding your role in online safety — as a student, future employee, or just someone who spends time online — is super important. Just follow the guidelines below and you’ll do great.
1. Use strong passwords. The internet runs on trust — and one way we protect that trust is with passwords. Use strong ones, don’t repeat them across sites, and consider using a password manager. Don’t make it easy for someone to guess your login by using “123456”
3. Think before you post. Everything you put on social media stays out there — even if you delete it. Colleges, employers, and scholarship programs often look at your online footprint. So skip the cringe-worthy posts, and ask yourself: “Would I be okay with a future boss seeing this?”
4. Protect your privacy. You might not realize it, but you’re constantly giving away personal info — your birthday, your favorite pizza

topping, even your location. Companies track this, and hackers can use it to guess passwords or answer security questions. So share less, and double-check the privacy settings on your apps.
Quick tip: when you’re on a website, look for “https” in the address bar. That little “s” means the site is secure, and your data is encrypted (turned into code that’s hard to crack).

REVIEW COPY
5. Stay clean — on and offline. Like it or not, some things matter to future employers: drug tests, credit scores, and even how you spend your money. Many cybersecurity jobs (especially in government) require background checks and drug-free records. And if you’re deep in credit card debt, it could raise red flags — some employers might worry you’re more vulnerable to bribery or blackmail.
Ready to make a career out of it?
Cybersecurity is about protecting people, data, and digital spaces — and the habits you build now can set you up for a future career. Spotting scams, creating strong passwords, and understanding how your data moves online isn’t just smart — it’s the foundation of what cybersecurity pros do every day. If that sounds like your thing, you might already be thinking like a cyber pro.
Build a Great Password
Weak passwords = easy targets. Something like “mydogisMax”? Hackers (and their AI tools) can break that in seconds.Here’s how to make yours stronger:
1. GO LONG: Aim for 12+ characters.
2. MIX IT UP: Use upper/lowercase letters, numbers, and symbols.
3. AVOID THE OBVIOUS: No names, birthdays, or “password.”
4. TRY A PHRASE: Like “MyAvatarHasBlu3Hair!”
5. USE A PASSWORD MANAGER: Just don’t forget your master password.
education: what do do now
Get Started on Your Cybersecurity
Follow these six steps to build confidence, skills, and experience in one
As you read in the previous article, launching a career in cybersecurity takes more preparation than it used to. A bachelor’s degree is often the fastest route, but it’s not the only one. Many professionals begin with a two-year degree in information technology or cybersecurity, then transfer their credits toward a fouryear program. Others build skills through hands-on experience and certifications. Whatever the path, these six steps can help you get started in high school.
STEP 1:
Build Strong Academic Skills Cybersecurity depends on logic and communication.
Take math seriously. Algebra, geometry, and statistics form the foundation of encryption and coding. Add calculus or physics if you can.
Don’t skip English. Professionals must write clearly, think critically, and explain risks to non-technical audiences.
STEP 2:
Get Your Tech Basics Down Learn how computers, networks, and operating systems work — it’s the backbone of every cyber career.
Take IT or computer science classes if your school offers them. If not, consider your local college. Many colleges offer high schoolers the chance to earn both high school and college credit at the same time. (See pages 22-23 for more info.)
You can also try free online cybersecurity courses from Cisco, IBM, Palo Alto Networks, or Google.
Learn to code, starting with the most common language in cybersecurity, Python. Check out free online courses from Codecademy, Khan Academy, or Alison.com. Other languages to try: Java-Script, Java, Go, C, and C++.
Set up a home Wi-Fi network, build a website, or troubleshoot a computer problem — real practice teaches fast.
STEP 3:
Earn a Certification

STEP 4:
Join a Team
REVIEW COPY
Prove your skills to employers.
Start with CompTIA Security+ or the Google Cybersecurity Certificate.
As you advance, add Network+, CYSA+, or Certified Ethical Hacker (CEH).
Certifications show initiative — but remember, they complement experience; they don’t replace it. Read more about certifications on pages 26-27.
Cyber professionals rarely work alone. Teamwork and collaboration are essential.
Join a robotics or cyber club, or compete in challenges like Capture the Flag (CTF) or CyberPatriot
If your school doesn’t have a cyber club or team, start one! Local colleges or tech organizations can often help sponsor.
These activities build technical skill, problem-solving ability, and the teamwork employers value most. See page 24-25 for more info.
Cybersecurity Career

STEP 5:
Get Hands-On Experience
Experience matters more than anything else.
Volunteer to help your school, a local nonprofit, or small business with basic tech or security needs.
FAST FACTS: The Cyber Job Market in 2025
Explosive Growth
REVIEW COPY
Look for summer jobs that involve computers or online safety. Or attend a summer cyber camp.
Consider military service. Every branch of the U.S. Armed Forces now has cyber units that defend national networks. Enlisting can provide advanced training, leadership experience, and security clearances that are highly valued by employers. See pages 52-53 for more info.
STEP 6: Keep Learning
Cyber threats — and the tools used to fight them — evolve constantly.
Stay curious and keep building new skills through college, online courses, or on-the-job training.
Follow cybersecurity news, listen to podcasts, and explore emerging areas like cloud security, A I-driven defense, and digital forensics. In this field, learning never stops — and that’s part of what makes it exciting.
The Bottom Line
Apply for internships or entry roles such as IT support , network technician, or SOC analyst trainee.
Experiment with AI tools for cybersecurity — like automated threat detection or phishing simulations — to see how they work. one
Cybersecurity is still a great field — one full of opportunities for people who like to solve problems and protect others. You don’t have to wait for college to begin. Start now by exploring technology, building your skills, and getting hands-on experience. Every step you take brings you closer to making a real difference.
Cybersecurity jobs are projected to grow 33% from 2023–2033 — more than six times faster than the average for all occupations.
Openings Everywhere
As of 2025, there are an estimated 514,359 unfilled cybersecurity positions across the U.S. Government agencies, hospitals, banks, energy companies, and schools all need cyber talent.
Strong Pay
The median annual salary for information security analysts is about $120,000, with entry-level roles typically starting around $60,000–$75,000 depending on location and employer.
Education Counts
Roughly 80–85% of cybersecurity jobs list a bachelor’s degree as preferred or required, but certifications and hands-on experience can help bridge the gap.
education: dual enrollment
Double Up Your Credits
How dual enrollment programs can help you save money, jump-start career plans, and bank college credits at the same time.
For a long time, it seemed like a given: after high school, you go off to college. Pack your stuff, say goodbye to home, and take that big step toward your future.
But that “standard” path is starting to change. College is getting more expensive every year. Fewer students are enrolling. And for some, college just doesn’t feel like the right fit right away — especially after COVID showed how learning can happen online, anytime, anywhere.
So, what’s the alternative? Instead of students
going off to college after high school, more schools are flipping the script — bringing college into high school. It’s called dual enrollment , and it’s growing fast. In the 2023–24 school year, about 2.5 million high school students participated in dual enrollment. That represents roughly 16 percent of all U.S. high school students.
school. Even better? You earn both high school and college credit at the same time.
REVIEW COPY
what college work is really like.
HOW DUAL ENROLLMENT WORKS
Also known as dual credit or concurrent enrollment, this model lets you take college-level classes while you’re still in high
Courses can be taught by college professors or high school teachers with special training. You might take them at your school, on a college campus, or completely online.
WHY TRY IT?
Save money: Classes are often much cheaper than regular college tuition.
Get ahead: You’ll learn
Stand out: It looks great on college applications.
Do better: Students in dual enrollment programs are more likely to graduate from both high school and college.
Dual enrollment can be especially powerful in fast-growing, high-tech fields like cybersecurity. In fact, some states are already making cybersecu -

REVIEW COPY
rity a required subject in high school. North Dakota, for example, passed a law that will require all students to take at least one course in either cybersecurity or computer science starting in 2025.
COLLEGE PROGRAMS LEADING THE WAY
Here’s where colleges step up. Many high schools don’t have the teachers or tools to offer cybersecurity education on their own. Colleges, on
the other hand, have both the experts and the resources — and they’re bringing them straight to students through dual enrollment.
Online programs are especially flexible. You can learn anytime, from anywhere, at your own pace — all while gaining knowledge that’s in demand right now.
CHECK OUT THESE EXAMPLES
Tennessee Tech Uni -
versity offers the Golden Eagle Cybersecurity Certificate Program, a threecourse, fully online sequence. No computer science experience is needed — and it’s free for students who qualify.
Howard County Community College in Maryland runs an “early college” cybersecurity program for 10th–12th graders. If you complete all the courses while in high school, you’ll already have one year of college credits. Just one more year of community college, and you’ll have an associate degree in cybersecurity — plus the chance to take your first professional certification exam.
Illinois Institute of Technology runs the Runway 606 Cybersecurity Pathway, a program that lets Chicago high school students earn an associate degree through dual enrollment — then continue on for a bachelor’s and even a master’s in cybersecurity.
University of Montana offers Early College Cybersecurity courses either
online or in-person. The first two classes are tuition-free, and others are half price. Students can earn college credit while still in high school and stay on track toward a cybersecurity degree.
New York City’s P-TECH schools, in partnership with IBM and City Tech (CUNY), combine grades 9–14 so students can graduate with both a high school diploma and a free associate degree in tech fields like cybersecurity. Industry mentors and internships are part of the deal too.
WHAT YOU CAN DO NOW
Even if your school doesn’t offer a dual enrollment program, don’t give up. Many community colleges and universities have options open to high school students in their area — and just living in the right county or state might make you eligible. Getting a head start on college now will make your transition easier, less expensive, and more exciting. By the time you do pack up for college, you’ll already be ahead of the game.
Ways to Get Involved education: camps and competitions
Cybersecurity competitions and camps aren’t just fun — they’re a great way to build skills that colleges, the military, and employers are looking for. Whether you’re solving challenges solo or working with a team, you’ll gain real technical experience while sharpening your problem-solving and communication skills. Programs like GenCyber, CyberPatriot, and the US Cyber Games are designed to help
students build those skills — and they’re often backed by government agencies and major companies that offer funding, prizes, scholarships, internships, and mentoring. As Kammy Sanghera, Executive Director of STEM Outreach at George Mason University, explains, “That’s the point: to discover and support future talent.” Also check out the National Cyber League (NCL) — a beginner-friendly competition open to high school students.
Explore Cybersecurity at GenCyber Camps — No Experience Needed
What if you could spend a week this summer solving digital puzzles, building your cybersecurity skills, and meeting other students and teachers who love tech — all for free? That’s exactly what GenCyber camps offer.
Funded by the NSA and the National Science Foundation, GenCyber is a nationwide program that gives middle and high school students — and teachers — a chance to dive into the world of cybersecurity. Camps are hosted by colleges, universities, and K–12 schools, with hands-on activities, exciting challenges, and plenty of inspiration.
In 2025, nearly 100 GenCyber camps were held across the U.S., including in D.C. and Puerto Rico. Every camp is completely free and often includes meals and housing.
Each one is a little different.



Some focus on ethical hacking or cryptography; others offer competitions and simulations like cyber escape rooms. At UT-Austin, students solved puzzles in a custom-built escape room. At Norwich University, campers lived on campus for a week while learning how to defend networks. There are also teacher-specific camps that help bring cybersecurity into classrooms.
No matter the format, all GenCyber camps share a mission: to spread awareness of cybersecurity careers, build digital safety skills, and prepare the next generation to protect the digital world. Whether you’re just getting started or already thinking about a cyber career, these camps can help you level up.
To find a camp near you, visit gencyber.com. Spots fill fast, so don’t wait to apply!
REVIEW COPY

Join
a CyberPatriot Competition
Think you’ve got what it takes to defend a computer system from hackers? CyberPatriot gives you the chance to find out — and build valuable skills along the way.
Created by the Air Force Association and backed by major cybersecurity companies and government agencies, CyberPatriot is a nationwide competition where student teams work to keep a virtual IT system running while spotting flaws and stopping simulated cyberattacks — all against the clock.
“The CyberPatriot program reaches students where they are — with competition and games,” says Tamara Shoemaker, founder of the Michigan CyberPatriot program. “It teaches creative thinking, teamwork, and hands-on learning, while encouraging sound judgment and ethics. Best of all, it’s inclusive, has multiple levels of play, and isn’t expensive to run.”
Thousands of teams from all 50 states compete each year in three divisions: middle school, high school, and JROTC or cadet programs. Teams can have two to six students, and while a coach is required, no technical experience is needed to get started. Most rounds take place online over several months, with the top teams advancing to the national finals in Maryland.
If your school or club doesn’t have a team yet, talk to a teacher, counselor, or youth leader about starting one. You don’t need to be a computer whiz — just bring curiosity, teamwork, and a willingness to learn. Get started at uscyberpatriot.org.
Be a Part of the US
Cyber Games
If you love solving puzzles, thinking fast under pressure, and working as part of a team, the US Cyber Games might be your perfect match. This one-of-a-kind competition combines the excitement of esports with the real-world challenge of cybersecurity, all with the goal of inspiring the next generation of cyber professionals — and building a national team to represent the U.S. at the International Cybersecurity Championship.
It all starts with the US Cyber Open Capture the Flag (CTF) Challenge, a free, 10-day virtual event open to players ages 16 to 24. In 2024, more than 3,000 students from all 50 states, Washington, D.C., and the Virgin Islands competed in challenges involving cryptography, forensics, reverse engineering, and web security. You don’t need to be a pro to join — just curious and ready to learn. Prizes go to top performers in each category and to the overall winners.
From there, a select group is invited to the US Cyber Combine Invitational, where they take on more advanced challenges, work closely with coaches, and show off both their technical and teamwork skills. The most promising players are chosen for the US Cyber Team, which goes on to compete in international scrimmages and global tournaments.
As Head Coach Ken Jenkins puts it, “We aim to develop the future cybersecurity leaders by immersing our athletes in an environment that emphasizes diversity, collaboration, and a career-focused approach.” Ready to test your skills? Learn more at playcyber.com.

education: certifications

Jump-Start Your Career
Certifications can give you an early edge — but they’re just the first step in a growing field.
The world of cybersecurity is changing fast — and so are the skills employers expect. A few years ago, earning a single certification or completing a short boot camp might have been enough to get your foot in the door. But today, as cyber threats grow more complex and AI reshapes both attacks and defenses, companies are raising the bar.
That doesn’t mean certifications have lost their value — far from it.

They’re still one of the best ways to learn practical, hands-on skills and show that you’re serious about the field. But now, a certification works best as part of a larger plan that includes technical coursework, experience, and (eventually) a degree. Think of a certificate as your starting point, not your destination.
curity. Adding a certification can help you stand out when applying for college programs or internships and give you a taste of real-world tools and practices.
Just be sure to choose accredited, well-known programs so your certification is recognized by employers and schools. Many are beginner-friendly, affordable, and even available online — a great way to start building your skills now.
CompTIA Security+
One of the most well-known certifications in the world, Security+ teaches you the basics of cybersecurity. You’ll learn about network security, threat management, encryption (cryptography), and how to assess risk. It’s a solid first step and a good foundation for other certifications down the road.
REVIEW COPY
If you’ve taken computer science or IT classes in high school — great! You’re already building a strong foundation for a future in cyberse -
Google IT Support Professional Certificate
This beginner-friendly program covers all the fundamentals of working in IT, including cybersecurity. You’ll learn about troubleshooting, networks, operating systems, and security basics. It’s a great all-around introduction to tech careers — and it’s free!
Cisco Certified Network Associate (CCNA) Cyber Ops
While this one isn’t only about cybersecurity, it focuses on network security, which is a huge part of the field. You’ll learn how to spot and respond to cyber threats and understand how network systems work. It’s a smart choice if you’re interested in how the internet and secure systems operate behind the scenes.
Free Online University Courses
Want to try cybersecurity before signing up for a program?
MOOCs (Massive Open Online Courses) are an easy, free way to test the waters. You can learn at your own pace through videos and discussion forums, and some even offer low-cost certificates when you finish. Most are created by universities, so it’s a great sneak peek at real college courses. Just check the start dates — some run on a set schedule.
Explore options here: cyberdegrees.org/resources/free-online-courses.
Certified Ethical Hacker (CEH)
Ever wonder how hackers think? This certification teaches you the tools and techniques ethical hackers use to test and protect systems. You’ll learn how to spot weak spots in networks and software — and how to fix them. It’s all about hacking for good.
Palo Alto Networks
PCCSA Certification
Palo Alto Networks is a top global cybersecurity company. Through its Cybersecurity Academy, it offers a free online Cybersecurity Foundation course, along with longer training programs that include hands-on labs. These classes help prepare you for the PCCSA certification, which can qualify you for entry-level cybersecurity jobs. Courses are available through Coursera.org, so you can take them anytime.
An associate degree builds the skills you need — and sets you up to keep learning as the field evolves.
Cybersecurity remains one of the fastest-growing, most in-demand fields — but it’s also evolving fast. A few years ago, a short boot camp or two-year degree might have been enough to land a first job. Today, employers want candidates with hands-on skills, a strong technical foundation, and a plan to keep learning, often through additional certifications or a bachelor’s degree.
eas that interest you most. In these programs, you’ll learn how to:
Spot and analyze cyber threats and attacks.
Keep computer networks safe by watching for suspicious activity.
Use digital forensics to investigate hacks and prevent them in the future.
You’ll also get a solid understanding of how computer hardware and software work — the foundation for every job in cybersecurity
Keep an eye out for scholarships and other resources that can help cover costs. For example, Microsoft offers financial support (up to $500), along with learning and networking opportunities for students interested in cybersecurity.

That’s where community colleges come in. They’re affordable, practical, and designed to help you build a solid foundation in cybersecurity before taking your next step. Many programs now include AI and automation topics, reflecting how much the field has evolved. A twoyear degree can prepare you to earn industry certifications, find internships or apprenticeships, and transfer into a four-year cybersecurity or IT program to keep advancing.
Most students work toward an Associate of Applied Science (AAS) degree, which lets you focus on ar-
As Laura Bate, formerly of the U.S. Cyberspace Solarium Commission puts it: “Start in community college and be looking at job postings, but position yourself for a four-year degree.”
If you want to transfer, articula -

education: community colleges Two Years, Real Skills REVIEW COPY
tion agreement s make it easy. These partnerships between community colleges and universities let you carry your credits directly into a bachelor’s program. For example:
Alexandria Technical & Community College (MN) graduates can transfer their 60 credits to Metropolitan State University or Dakota
Harford Community College, Bel Air, MD


State University.



REVIEW COPY
Coastline College (CA) offers “stackable” certificates that can count toward a degree at National University.
Some four-year schools even offer special scholarships for AAS graduates.
Community colleges also con -
nect students to registered apprenticeships, which offer valuable onthe-job experience and sometimes help with security clearances — a big advantage for government or defense-related roles.
Finally, starting at a community college can save you a lot of money. The average yearly cost at a public two-year college, including tuition,
fees, and living expenses, is about $10,300, and 17 states now cover tuition for many students.
Even if your goal is a bachelor’s degree later, community college can be a smart, affordable first step — one that builds the skills and experience employers are looking for today. Learn more: start-engineering. com/associates-degrees.
Lehigh Carbon Community College, Schnecksville, PA
Coastline Community College, Newport, CA
Alexandria Technical & Community College, Alexandria, MN
Forsyth Tech, Winston-Salem, NC
education: colleges and universities
Four Years, More Choices
Explore advanced topics, electives, and career options.
You may have read about community college options for studying cybersecurity. Those programs are a smart, affordable way to build a foundation in technology and gain valuable hands-on experience. But as the field grows more complex — especially with the rise of AI-driven attacks and defense tools — most employers now look for candidates with a fouryear degree or higher.
Earning a bachelor’s degree in cybersecurity can open doors to more advanced roles and specialized career paths. These programs go deeper into technical topics, offer more ways to customize what you learn, and prepare you for a wider range of opportunities right after graduation.
Bachelor of Science in Cybersecurity, which blends computer science or engineering courses with hands-on labs that teach you how to identify vulnerabilities, respond to attacks, and design stronger systems.
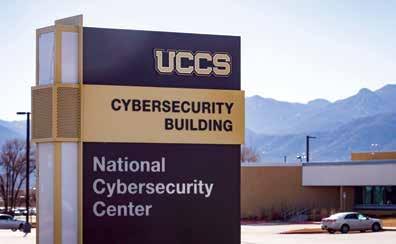
Some schools have earned a special recognition from the National Security Agency (NSA). They’re called National Centers of Academic Excellence in Cybersecurity (NCAE-C). Programs with this honor focus on areas like cyber defense, operations, or research — and include coursework that connects cybersecurity to fields like engineering, policy, and social science.
Highly ranked programs can be found all over the country, including the New York Institute of Technology, Tennessee Tech, and the University of Southern Mississippi. (Find more schools at start-engineering.com/4year-degrees).
Before deciding where to apply, talk to your school counselor and research your options online. Most cybersecurity degrees are offered through computer science or engineering departments, but not every program is purely technical. “Cyber touches everything,” says Brown.

REVIEW COPY
There are lots of different paths to a cyber degree at a four-year college. One option is earning a
“You know you have a high-octane program if you see that designation,” says Eric Brown, associate director of the Cybersecurity Education, Research & Outreach Center at Tennessee Technological University.
That means you could major in something like law enforcement, psychology, public policy, or business and pair it with cybersecurity courses. This combination can prepare you to manage teams, shape security policies, or guide organizations through privacy and safety decisions — skills that employers





University of Texas, Austin, TX
PHOTOS COURTESY THE SCHOOLS
Tennessee Tech University, Cookeville, TN
University of Colorado, Colorado Springs, CO
Mississippi State University, Starkville, MS
Oakland University, Rochester MI
education: colleges and universities REVIEW COPY
The U.S. Naval Academy’s new center for cybersecurity studies, in Annapolis, MD

Military Academies: Where Service Meets Cybersecurity
The U.S. military isn’t just preparing for battles on land, sea, or air — it’s getting ready for battles online, too. Defending against cyberattacks (and launching them when needed) is a key part of national security.
That’s why all five U.S. service academies now offer cybersecurity degrees.
The U.S. Military Academy (Army), Air Force Academy, Naval Academy, and Coast Guard Academy all have top-tier cybersecurity programs recognized by the National Security Agency (NSA). Cadets and Midshipmen study subjects like computer networks, database systems, cryptography, and computer architecture. But that’s just the tech side — they also take classes in leadership, policy, law, and ethics to prepare for real-world decision-making in cyber warfare.
These programs train future officers for assignments in military cyber
commands and advanced graduate studies. But it’s not all lectures and textbooks. Real-world experience is a must.
That’s where the NSA’s Cyber Defense Exercise comes in. Launched in 2001, this annual competition challenges students from the service academies (plus teams from the Merchant Marine Academy and even Canada’s Royal Military College) to defend their networks from live attacks. NSA cyber professionals act as hackers trying to break in. The academy team that defends its network best wins — but everyone learns how to get stronger.
In 2025, the U.S. Air Force Academy took first place in the competition. But whether you win or not, the experience gives future officers real-world practice in defending against cyber threats — and prepares them to protect critical systems in high-stakes environments.
increasingly value. Even if you focus on computer science, taking courses outside of technology can make you stand out. “You might be better able to understand an adversary’s behavior and attack strategies by studying psychology,” says Mark Loepker, former Education Advisor at the National Cryptologic Foundation. Other fields can help, too. Studying library science or biology can teach you how to design user-friendly systems. Law enforcement courses are useful if you want to catch cybercriminals. And business management is key for future leaders who want to run teams or their own


University of Maryland, Baltimore County
cybersecurity companies.
Most programs let you customize your studies. For example, New York Institute of Technology’s B.S. in Information Technology offers a wide range of electives. Sarah Basset Lee, director of the School of Computing Sciences and Computer Engineering at the University of Southern Mississippi, says students should also build strong communication skills. “Even if you’re going down a technical path, you’re going to have to do some writing. I’d suggest that students celebrate any opportunity to work on a team project.”
Outside of class, hands-on experience is essential. “Cybersecurity,
REVIEW COPY
like any technical field, is mastered by doing and not passive reading,” says Babak Beheshti, dean of the College of Engineering and Computing Sciences at New York Institute of Technology. He recommends joining hackathons, competitions, and student clubs to sharpen your skills and make connections.“You will learn by doing and will start building a network of likeminded friends,” he says.
You can also set up virtual labs, try online simulations, or get an internship or apprenticeship to see what working in the field is really like. These experiences — along with your degree — help you stand out to future employers.


Get Paid to Learn
Acybersecurity apprenticeship is one of the best ways to start your career — especially if you want to earn a salary while learning real-world skills and, in some cases, work toward a degree at the same time.
Apprenticeships are full-time, paid training programs that combine classroom learning with hands-on experience. Many are designed for students who already have some basic tech or cybersecurity knowledge — maybe from high school classes, certifications, or community college. Some employers even help pay for your college courses while you train on the job.
Apprenticeships are different from internships. Internships are usually short-term and sometimes unpaid. Apprenticeships, on the other hand, are registered with the U.S. Department of Labor, which means you’ll get:
A paycheck — at least 60% of the full-time wage for the job.
A professional mentor who trains you on the work. Technical instruction that leads to recognized certifications or college credit.
An apprenticeship lets you test your skills while you’re still learning. “It’s okay to fail now — once you start work, it may not be,” says Craig Koroscil, senior executive at cybersecurity company Circadence.
Before signing up, make sure the program clearly lists what you’ll learn, how your progress will be measured, and what certifications or credits you’ll earn.
Start your search at the NICE Cybersecurity Apprenticeship Program, which lets you explore options by location and career goals. You can also check with local community colleges or workforce programs, which often partner with trusted employers to offer cybersecurity apprenticeships — including ones focused on AI tools, cloud security, and digital forensics.
The Georgia Cyber Center at Augusta University, Augusta, GA Bismarck State College, Bismarck, ND
PHOTOS COURTESY THE SCHOOLS
education: financial aid
Trim Your Tuition
It’s more important than ever to find ways to reduce college costs.
If you’re looking for financial aid, start with scholarships at the schools you are interested in attending. These are usually the most generous. But there are also numerous cybersecurity scholarships from many sources, such as non-profits, foundations, institutions, government organizations, and corporations. Did you know that many available schol-
arships go unused? So apply for as many as you can! Many government agencies with cybersecurity missions share details about scholarships, so check out the websites of the National Initiative for Cybersecurity Education (NICE), National Security Agency (NSA), and the Cybersecurity Infrastructure and Security Agency (CISA). As well, the Center for Cyber Safety
& Education and non-profits like the National Society of Black Engineers, the Society of Hispanic Professional Engineers, and the Society of Women Engineers all offer scholarships. Ask your high school guidance counselor to help you. In the meantime, here’s a good list to get you started. Note that some scholarships require government service in return for the award.
AFCEA Cyber Security Scholarship Award amount: $5,000
https://www.afcea.org/stem-majors-scholarships
CIA Stokes Scholarship Award amount: Up to $25,000/year
Generation Google Scholarship Award amount: $10,000
https://buildyourfuture.withgoogle.com/scholarships/ generation-google-scholarship
https://www.cia.gov/careers/student-programs/undergraduate-scholarship-program/
Department of Defense Cyber Service Academy Award amount: tuition + stipend
https://dodcio.defense.gov/Cyber-Workforce/Cyber-Service-Academy/
ESET Women In Cybersecurity Scholarship Award amount: Up to $10,000
https://www.eset.com/us/women-in-cybersecurity-scholarship/
FS-ISAC Cybersecurity Scholarship Award amount: $10,000
https://www.fsisac.com/scholarships
REVIEW
(ISC)² Associate Scholarships Award amount: $500 - $1,000
https://www.iamcybersafe.org/s/associate-scholarships
(ISC)² Graduate Scholarships Award amount: $1,000 - $5,000
https://www.iamcybersafe.org/s/graduate-scholarships/
(ISC)² Undergraduate Scholarships
Award amount: $1,000 - $5,000
https://www.iamcybersafe.org/s/undergraduate-scholarships
(ISC)² Women’s Scholarships
Award amount: $1,000 - $5,000
https://www.iamcybersafe.org/s/womens-scholarships

REVIEW COPY

Microsoft Cybersecurity Scholarship Program Award Amount: Up to $500
https://www.lastmile-ed.org/microsoftcybersecurityscholarship
Naval Research Enterprise Internship Program Award amount: $7,500 - $11,500
https://www.navalsteminterns.us/nreip/
National Science Foundation CyberCorps Scholarship for Service Award amount: $25,000 - $34,000
https://new.nsf.gov/funding/opportunities/cybercorps-scholarship-service-sfs-0
National Society of High School Scholars Award amount: $1,500
https://www.nshss.org/scholarships/s/nshss-cybersecurity-excellence-scholarship-2025/
Nightwing Underrepresented Groups in Cybersecurity Scholarship Award amount: $10,000
https://www.iamcybersafe.org/s/Nightwing-Cybersecurity
Samantha Jennings-Jones Memorial Scholarship Award amount: $5,000
https://www.iamcybersafe.org/s/samantha-jennings-jones-memorial-scholar
The Science, Mathematics and Research for Transformation (SMART) Scholarship for Service Program Award amount: full tuition + salary + benefits https://www.smartscholarship.org/smart
VIP Women in Technology Scholarship Award amount $2,500
https://trustvip.com/wits-program-faqs/

careers: key work roles REVIEW COPY
what cybersecurity jobs are out there, what skills and certifications they require, and how you can move between roles as your experience grows. That’s one of the best things about cybersecurity — you don’t have to stick with just one path. Many roles share overlapping skills, so once you get started, it’s easy to shift into new areas with some additional training.
Use this guide to explore your options, figure out how to get started, and imagine where your strengths could take you in one of the most exciting — and important — industries today.
ANALYZE
Cybersecurity analysts study incoming information to figure out what threats are real — and what to do about them.
WHAT THEY DO
REVIEW COPY
COLLECT and OPERATE
Cybersecurity pros in this role gather and study information about possible cyber threats to protect systems and national security.
WHAT THEY DO
n Collect and analyze digital intelligence to understand what adversaries are doing and how they operate.
n Detect and stop cyber threats by uncovering suspicious activity and helping prevent future attacks.
JOB TITLE EXAMPLES
Cyber Analyst
Intelligence Analyst
Information Systems Manager
Security Software Developer
ADVANCED DEGREE/ TRAINING
Computer Science or Engineering
IT or Network Security

n Review reports, alerts, and data to spot patterns or warning signs.
n Identify the tools and tactics used by hackers or foreign cybercriminals.
n Analyze information from many sources — like other agencies, companies, or countries.
n Share findings to help law enforcement and intelligence teams investigate threats.
JOB TITLE EXAMPLES
Cyber Threat Analyst
Cyber Counterintelligence Analyst
Cryptanalysis and Signals Analyst
Security Analyst
ADVANCED DEGREE OR TRAINING
Computer Science
Criminal Justice
Forensics
Information Technology
Engineering
Law
INVESTIGATE
These pros review and evaluate cyber events and cyber crimes.
WHAT THEY DO
n Investigate cyber crimes.
n Recover data from computers to use in prosecuting crimes, analyzing and decrypting any type of hidden information.
n Identify and assess cyber criminals or foreign entities.
n Help law enforcement and counterintelligence investigations.
JOB TITLE EXAMPLES
Forensic Computer Analyst
Cryptographer
Cyber Intelligence Analyst
Security Analyst
DEGREE OR TRAINING
Cybersecurity
Computer Science
Network Security
Forensic Science
IT and Security

OPERATE and MAINTAIN
These pros keep IT systems running smoothly and securely — and it’s the path with the most job openings.
WHAT THEY DO
n Develop, support, and maintain databases and networks.
n Manage intellectual capital and content.
n Install, configure, test, operate, maintain, and manage network server configurations, access, firewalls, and patches.
JOB TITLE EXAMPLES
Customer/Technical Support Specialist
Data or Database Specialist
Information Systems
Security Engineer
Network Specialist
System Administrator
DEGREE OR TRAINING
Computer Science
Information Technology
Network/Computer Systems

careers: key work roles REVIEW
WHO DONE IT?
A digital forensics expert examines an IT system just as a medical forensics scientist examines a dead body! As noted forensic computer examiner Eric Robi says, “A computer forensic analyst has to be incredibly curious about how computers work and how people behave.” In addition to curiosity and insight, you will be expected to have strong written and oral communication skills. A large part of an expert’s job is devoted to writing reports and explaining evidence.
In the case of criminal prosecutions, you need be able to explain your findings before lawyers, judges, and juries who lack tech backgrounds. Can you defend your findings when cross-examined by opposing counsel? Whether you are speaking to intelligence partners, corporate clients, or law enforcement, you need to be able to be crystal clear!

OVERSEE and GOVERN
These professionals lead and guide cybersecurity efforts across an entire organization. They make sure teams have the resources, policies, and direction they need to keep systems secure.
WHAT THEY DO
n Oversee cybersecurity programs by managing plans, budgets, and teams.
n Set policies and offer advice on legal, privacy, and security issues — including things like e-commerce, copyright, and protecting personal data.
n Shape the strategy and technical direction to help the organization stay ahead of threats.
JOB TITLE EXAMPLES
Chief Information Officer
Cyber Security Trainer
Lawyer or Legal Advisor
Policy Analyst
ADVANCED DEGREE / TRAINING
Business
Criminal Justice
Information Technology
Law
PROTECT and DEFEND CALLING
They work to keep systems safe by stopping attacks before they happen — and responding quickly if something goes wrong.
WHAT THEY DO
n Find and fix weaknesses in software, hardware, and networks, using creative strategies to protect systems.
n Monitor and manage networks to catch unauthorized activity, respond to incidents, and repair any damage.
REVIEW COPY
n Assess threats and vulnerabilities to understand what could be exploited and how to prevent it.
JOB TITLE EXAMPLES
Chief Information Security Officer
Ethical Hacker
Incident Responder
Intelligence Analyst
Penetration Tester
Security Analyst
DEGREE OR TRAINING
Computer Science
Cybersecurity
Information Assurance
Network Security

SECURELY PROVISION
WHAT THEY DO
n Design and develop secure IT systems, including figuring out what the systems need to work safely.
n Create tools to detect and block viruses, spyware, and malware.
n Test and evaluate software and applications to find problems before hackers do.
n Research and develop new technologies to prevent intrusions and keep systems strong.
ALL (ETHICAL) HACKERS
A penetration tester (a.k.a., ethical hacker) probes for and then exploits security vulnerabilities in web-based applications, networks, and systems. In other words, you’re paid to hack — and it’s legal! Using a series of penetration tools, some that you will design yourself, you simulate real-life cyberattacks, perhaps taking part in Red Team/Blue Team exercises that mimic cyber warfare. Your ultimate aim is to help an organization improve its cybersecurity. Most pen testers don’t hold a specialized degree. Since ethical hacking is more about skills than course credits, a bachelor’s or master’s degree in cybersecurity may be unnecessary if you have the right experience.
These pros design, create, and test secure technology so it’s protected before anyone ever tries to break in.
JOB TITLE EXAMPLES
Computer Programmer
Computer Systems Analyst
Software Developer
Systems Engineer
Information Assurance Developer
Network Security Analyst
Systems Security Architect
Information Technology Director
DEGREE OR TRAINING
Computer Science
Networking
Electrical or Systems Engineering

careers: support systems REVIEW COPY

DIVERSITY REQUESTED
REVIEW COPY
The cybersecurity field needs people from every background.
Like many STEM fields, cybersecurity has been dominated for a long time by white men — but that’s starting to change. Today’s cybersecurity leaders know that the best ideas come from having different kinds of people on a team. It’s been proven that when you bring together people with different backgrounds and experiences, you get more creative solutions to tough problems.
The field is working hard to become more inclusive and welcoming. Scott Young, executive director of synED, a major cybersecurity education program in California, wants everyone to know: “We need you as you are! We don’t want you to change!”
Success in cybersecurity depends on that diversity. The more different ways of thinking a team has, the stronger it becomes.
One thing to remember is that cybersecurity is such a wide field that nobody should feel like they have to quit just because an introductory class was challenging. There are many ways to get into the field. Davina Pruitt-Mentle, who leads Academic Engagement for the National Initiative for Cybersecurity Education (NICE), says: “As long as you have some good analytical skills and you’re willing to keep learning, we’ve got something for you.”
Finding support along the way can make a big difference. Charles Britt, a cybersecurity expert and former CIA officer, suggests, “Seek mentors both in and outside of the career who can help you in the workplace. Have at least one trusted individual in your network you can
talk to about both professional and personal challenges impacting your career as well.”
And if you don’t find a mentor who looks like you, don’t let that discourage you. Kate Plough, a software developer with the NSA, found that men were ready to help her move forward with her education and career. Most importantly, she says: “Don’t decide tech isn’t for you because you’re in the minority.”
Many companies are working to create more opportunities. For example, Symantec — the company behind Norton anti-virus software — is dedicated to hiring more women in cybersecurity. It partners with professional and educational organizations and has created the Symantec Cyber Career Connection to help women and other underrepresented people build careers in the field.
And there are more groups out there ready to support you than we can list here. Just to name a few:
Women in Cybersecurity, which has student chapters at more than 100 colleges.
AllStar Code
The National Society of Black Engineers
Black Girls Code
The Women’s Society of Cyberjutsu
Raíces Cyber, which works to help 10,000 Hispanic students enter cybersecurity.
No matter your background, there’s a place for you in cybersecurity — and plenty of people ready to help you succeed.
careers: in the field
From FINANCE to FARMING, cyber professionals

Rachel Tobac, CEO, SocialProof Security
Rachel is an ethical hacker who helps people stay safe from online scams. She teaches companies how to spot tricks that hackers use to steal information. She also leads a group that supports women in cybersecurity and is often featured on news shows like NPR and CNN.
Alissa Abdullah, Deputy Chief Security Officer, Mastercard
Alissa helps keep Mastercard’s data safe and works on new ways to protect against cyber threats. She used to handle cybersecurity at the White House for President Obama and now helps encourage more girls to explore careers in cybersecurity.

Jerich Beason, Chief Information Security Officer, Waste Management
Jerich leads cybersecurity operations at one of the largest waste and recycling companies in the world. He also develops online learning programs and hosts a podcast for cybersecurity professionals at all career stages.


Robert M. Lee, Co-founder and CEO of Dragos
Robert works to secure power grids, pipelines, and water utilities from hackers. A former NSA and U.S. Air Force cyber specialist, he also creates courses for SANS, a leading cybersecurity training organization, and advises government leaders.
Jack Cable, CEO and Co-founder of Corridor
Jack helped start Corridor to put innovative AI tools to use in cybersecurity. Previously at the Cybersecurity and Infrastructure Security Agency, he led high-level initiatives in online safety. As a teenager, he won the “Hack the Air Force” challenge, earning global recognition.
REVIEW COPY


Kyla Guru, Anthropic
Kyla helps make AI systems safer and stops them from being misused before they’re released. She also started Bits N’ Bytes Cybersecurity Education and co -founded GirlCon Tech, encouraging students everywhere to explore technology and cybersecurity careers.
professionals work in many diverse fields.

Charles Britt, CEO & Co-Founder, Startfield
After 20 years working within government, industry, and academia as an IT/Cybersecurity professional, Charles co-founded Startfield, to help more people from underrepresented communities discover and succeed in tech careers through training and mentorship.
REVIEW
Rinki Sethi, Chief Security & Strategy Officer, Upwind Security
Renki is a top expert in keeping online systems safe. She has held top cybersecurity roles at major companies like Twitter, IBM, and eBay, helping shape the future of digital security. She’s won many awards for her work in cybersecurity.

Megan Young, Co-Owner & Digital Security Educator, JML Safety
Megan helps protect farms and food businesses from cyber threats. Through her company, she works to keep the food supply chain safe and support the people who grow and produce our food.


Tyler Cohen Wood, CEO & Co-Founder, Dark Cryptonite
Tyler is a cybersecurity expert with 20 years of experience, including 13 with the Department of Defense. She’s helped protect the U.S. from cyber threats and is often featured on CNN and other news outlets. Her mission is to make cybersecurity accessible to all.
Paolo Gasti, Co-founder and CTO, Keyless
At Keyless, Paolo helped create cutting-edge technology that lets people unlock devices and accounts using biometrics — like facial or fingerprint scans — without giving away their private data. He is also an associate professor of Computer Science at New York Institute of Technology.


Mark Mbui, Product Manager, Palo Alto Networks
Mark leads a team that designs cybersecurity solutions to meet real customer needs. His work blends problem-solving, teamwork, and innovation, all driven by his goal of using technology to make the digital world safer.
careers: cyber pros needed
Jobs Available Everywhere!
America’s top companies pay top dollar for cyber sleuths.
What do video game company Electronic Arts, the career site LinkedIn, and Reverb, a website where musicians buy and sell gear, all have in common? They’ve all been targets of cyberattacks.
Today, black-hat hackers are going after almost every type of organization you can imagine — from stores and power companies to government agencies, hospitals, and schools. As Jon Brickey, a senior vice president at Mastercard, puts it: “Cyberattacks have gone from a novelty to a form of destruction. It’s a major risk factor to every enterprise.”
Because of this, there’s a huge demand for cybersecurity experts. These are the people who figure out how to protect valuable information and stop hackers. For students thinking about their future, cybersecurity is a field full of high-paying jobs — and there
still aren’t enough qualified people to fill them.
The work is never boring, because hackers are constantly coming up with new tricks. Most companies collect and store personally identifiable information (PII) — things like names, Social Security numbers, or credit card details. Criminal gangs and foreign hackers steal this data to make money. Sometimes, they encrypt a company’s files and refuse to unlock them unless a ransom is paid. Other times, they use stolen personal information to commit fraud, which is called identity theft.
But hackers don’t only go after people’s data. Many businesses have trade secrets they want to keep safe from competitors. For example, when hackers broke into Electronic Arts, they stole the source code behind some of its most popular games.
There’s also a growing risk as more



everyday devices connect to the internet — something called the Internet of Things (IoT). Smart devices make life more convenient (“Hey, Alexa, play Dua Lipa!”), but they also create even more ways for hackers to break in.
The big takeaway? Cybersecurity jobs exist in every industry and every level of government. Private companies often pay higher salaries, even for entry-level jobs. But the skills and experience you gain working in the public sector are very similar, so it’s common for people to switch between government and private companies during their careers.
Sadly, there will always be hackers trying to cause trouble and steal valuable information. As Brickey says, “The need for cybersecurity experts is here to stay.”


REVIEW COPY









careers: cybersecurity companies
Specialists For Hire
Companies that provide cybersecurity services to both government and industry can be a great career option.
What’s it really like to work at a leading cybersecurity company? Think fastpaced challenges, highstakes missions, great pay, and a shared sense of purpose. Whether you’re protecting government data, tracking down ransomware gangs, or building smarter defenses in the cloud, companies like Palo Alto Networks, Cisco, Microsoft Security, and Fortinet are on the front lines — and they need smart, driven people to join the fight.
What These Companies Do
Palo Alto Networks builds tools that help stop cyberattacks before they can do damage. Their software uses AI to spot threats and respond automatically. But they don’t just wait for attacks — they go looking for
them. A special team called Unit 42 does deep research on hackers and new threats, and they publish reports to help the rest of the world stay safe.

REVIEW COPY
Cisco helps protect huge networks, including ones used by banks, hospitals, and even events like the Super Bowl. Their security teams make sure Wi-Fi, payment systems, and other tech stay up and running — even when cybercriminals are trying to take them down. Cisco works in more than 100 countries, so their cybersecurity tools are used all over the world.
Microsoft Security is one of the biggest cybersecurity teams anywhere. Their tools are built into programs you probably already know, like Windows and Microsoft 365. They stop more than 100 billion
threats every month by scanning for danger across the internet. Microsoft also uses AI to help security teams work faster and smarter, and they run a Digital Crimes Unit that works with police to shut down cybercriminals.
Fortinet is known for building super-fast security tools that protect schools, banks, and government offices. Their products block threats quickly, and their research team — FortiGuard Labs — keeps customers updated with the latest info about new attacks.
And here’s something else that makes these companies stand out: they all help train the next generation of cybersecurity professionals. Microsoft, Palo Alto Networks, Cisco, and Fortinet offer free courses, certifications, and career resources to help students,



Cisco
Microsoft Security


REVIEW COPY


veterans, and beginners get started in the field. Some even partner with schools and colleges to bring cybersecurity learning into the classroom. So if you’re curious about this career, there’s a good chance you can start learning — right now, and at no cost.
High Impact, High Rewards
Cybersecurity companies are willing to pay well for talent — and for good reason. They’re defending the digital world against nonstop threats. At Palo Alto Networks, early-career roles can earn well into the six figures, especially when bonuses and stock options are included. Cisco and Microsoft offer similarly strong pay, along with great benefits and plenty of room to grow. Even entry-level jobs at Fortinet come with opportunities to level up quickly.
Why so much demand? Because cybercrime never sleeps. Attacks are constant, and companies, governments, schools, and hospitals all need protection. The global cybersecurity market is expected to top $290 billion by 2027, and companies are racing to keep up.
Real People, Real Backgrounds
You don’t have to have a computer science degree from a top university to get started. These companies are known for hiring people from a variety of backgrounds — including law, communications, psychology, and even English. They offer training programs, internships, and entry-level roles to help new employees build their skills.
At Microsoft, some cybersecurity employees start out in customer support or IT and move into threat analysis after gaining experience. Cisco runs early-career programs to help students and recent grads train in security operations, with chances to move into engineering or leadership roles later on. Palo Alto Networks has hired community college grads who started with certifications and worked their way up. And Fortinet not only hires newcomers — it also helps train them through its global certification programs.
What these companies really look for isn’t just technical knowledge — it’s curiosity, communication skills, and a willingness to keep learning. Cybersecurity is always changing, so
employers want people who can grow with it.
Why Work at a Cyber Company?
Lots of organizations — like schools, hospitals, and banks — need their own cybersecurity experts. But working at a cybersecurity company offers something different. Instead of focusing on just one organization, you get to help protect hundreds or even thousands of clients. You’ll be part of a team that’s completely focused on cybersecurity — building tools, hunting threats, and staying ahead of the latest attacks. These companies are often the first to spot new risks and the first to build solutions, which means you’ll learn fast, solve big problems, and make a real impact. If you thrive on variety, teamwork, and the chance to do work that matters, this is where you want to be.
Final Thoughts
Whether you’re drawn to innovation at Microsoft, the research at Palo Alto Networks, the global scale of Cisco, or the speed and power of Fortinet, working at a cybersecurity company can launch a career that’s exciting, challenging, and full of purpose.
Palo Alto Networks’ corporate campus in Palo Alto, CA
Fortinet
careers: NSA, DHS, FBI, and CIA




Quick — name the federal government agencies most involved in cybersecurity. You probably thought of the FBI, the National Security Agency (NSA), or the Department of Homeland Security (DHS).
That makes sense — they’re the ones you hear about most in the news when big cyberattacks happen.
But the truth is, almost every government agency has teams working to protect their networks and data. From the Department of Transportation to the Department of Commerce, everyone faces cyber threats. Because of this, the U.S. government is actually the largest employer of cybersecurity professionals in the country. So if you’re interested in this field, it’s smart to keep government jobs on your radar screen.
REVIEW COPY
What’s it like to work in public-sector cybersecurity?
According to Charles Britt, a cybersecurity expert and former CIA officer, the day-to-day work isn’t that different from private companies. But he says the mission feels different: “The work is pretty much the same, but it’s a much different mission.”
Many people are motivated by the idea of protecting the country. As Britt explains,“Most do it because of a
sense of wanting to serve their country.”
Government cybersecurity professionals do all kinds of critical work, including intelligence analysis, counterintelligence, criminal investigations, and counterterrorism. They help keep everything secure — from top-secret files to personal information about employees and citizens. And sometimes, the agencies you wouldn’t expect face big challenges. For example, during the pandemic, hackers targeted the Food and Drug Administration (FDA) to try to steal COVID-19 vaccine formulas and disrupt the supply chain.
If you’re thinking about applying, the good news is there are a lot of openings. Britt says: “If you have a clean background, you’re pretty much in the door.”
And the demand for cybersecurity professionals is only growing. Agencies aren’t just looking for people with computer skills — they also need experts in areas like communications and law. If you’re curious about what it’s like to work in government cybersecurity, consider applying for an internship. Many of these positions are paid and can give you valuable experience. Here are some of the main agencies involved in cybersecurity:
With cyberattacks on the rise, protecting and defending in cyberspace is mission-critical.
Work in National Security
NSA: If you’re interested in intelligence, the NSA could be a great fit. They collect and analyze signals intelligence, which means electronic communications like emails, phone calls, and radar data. Right now, the NSA is looking for people with backgrounds in computer science, electrical engineering, intelligence analysis, and math.
DHS: If you’re drawn to law enforcement and public safety, you might consider the Department of Homeland Security. DHS works on everything from fighting terrorism and securing borders to disaster response. Its Cybersecurity and Infrastructure Security Agency (CISA) leads cybersecurity efforts across all levels of government. DHS recently hired 300 cybersecurity professionals and offered jobs to 500 more — but they estimate they still need nearly 1,700 more people to fill open positions
FBI: The FBI made headlines in 2021 when it recovered $2 million in cryptocurrency that Colonial Pipeline paid to hackers in a ransomware attack. At the time, former FBI Director Christopher Wray said ransomware is such a big threat that it’s similar to the risks posed by 9/11. The FBI often has openings for software engineers, information security experts, and computer scientists.
CIA: You might be surprised to learn the CIA is also involved in cybersecurity. While the CIA focuses on gathering information from people (called human intelligence), it still has to protect its own networks. As Britt puts it, “Its (cybersecurity) focus is on protecting its own internal systems.” In other words, making sure their secrets stay secret.
careers: CYBERCOM and DC3
Spycraft, Front and Center
The Pentagon’s main cybersecurity unit, CYBERCOM, disrupts the sources of cyberattacks.
Before the 2020 U.S. election, many people worried that foreign hackers would try to mess with the results. Thankfully, those fears didn’t come true. In fact, the federal Cybersecurity and Infrastructure Security Agency (CISA) called it “the most secure election in American history.” That effort didn’t stop in 2020. In 2024, CISA again reported that no evidence showed any votes were changed by hackers, even though foreign groups tried to spread confusion and false information online.
rity protections in place.

One big reason these elections were so secure was the work of U.S. Cyber Command (CYBERCOM), the Pentagon’s main cybersecurity team. Working together with the National Security Agency (NSA), CYBERCOM helped strengthen voting systems across the country and block foreign threats trying to interfere.

Former CISA Director Jen Easterly said that millions of voters safely cast ballots with strong secu -
Based at NSA headquarters in Ft. Meade, Maryland, CYBERCOM is a relatively new organization — it was created just over a decade ago. It’s one of 11 “combat commands” in the Department of Defense. So why does it get involved in protecting elections? Part of its mission is to

help America stand up to and recover from cyberattacks, as well as support military missions around the world and defend the Pentagon’s networks.
For students interested in cybersecurity — and curious about the world of intelligence and secret operations — CYBERCOM could be an exciting place to work. While it was first designed mainly to defend against attacks, it now also goes on the offense. According to The New York Times, hacking has become a

REVIEW COPY
common tool governments use, similar to how spying worked in the 20th century. By teaming up with the NSA and using its networks, CYBERCOM has more freedom to track and disrupt cybercriminals.
A large part of CYBERCOM’s workforce is made up of active-duty military from the Army, Navy, Air Force, Marine Corps, and Space Force, but CYBERCOM also hires skilled civilian employees for jobs like cyber operations, IT and cybersecurity support,
policy and planning, and much more.
Another important part of the Pentagon’s cybersecurity efforts is the Department of Defense Cyber Crime Center (DC3). Founded in 1998, DC3 started as a computer forensics lab and training center. Today, it still specializes in digital and multimedia forensics, which means identifying, recovering, preserving, and analyzing evidence on computers and other devices. DC3 also develops tools to help investigators and runs
the Cyber Training Academy, which teaches military and civilian employees how to protect the Pentagon’s networks from criminals, spies, and other threats.
According to its website, DC3 employees work side by side with experienced military and government professionals “to solve the most demanding problems facing our nation.” In other words, it’s a place where you can build a career that is both challenging and meaningful.
U.S. Cyber Command
careers: military branches





Personnel at Marine Corps Forces Cyberspace Command work in the cyber operations center at Lasswell Hall on Fort Meade, Maryland. Below: Military personnel engaging in cybersecurity operations and training.

Enlist in Your Future
REVIEW COPY

“Cyberspace is not just a computer on your desktop. It’s the way that we as an Air Force intend to fly and fight,”
— General Robert J. Elder, Jr., USAF
Okay, so a career in cybersecurity interests you. But what if college doesn’t feel like the right option right now, whether because of money, grades, or something else? Don’t worry — there’s another path you can consider: the military.
All branches of America’s military — the Army, Air Force, Navy, Marines, and Coast Guard — have cyber commands that focus on protecting national security. These teams work around the clock to keep military networks, weapons systems, and critical infrastructure safe from hackers, terrorist groups, and other threats from around the world.
To join the military, you’ll need at least a high school diploma or a GED. It also helps to have strong communication skills, good math abilities, and a knack for solving prob
-
lems. When you enlist, you’ll take aptitude tests that help figure out which Military Occupational Specialties (MOS) you’re a good fit for. If you want to work in cybersecurity, it’s smart to boost your computer skills ahead of time and consider earning a basic certification from an accredited organization before you visit a recruiter.
After you sign up, you’ll start with about
10 weeks of boot camp. This includes physical training, weapons practice, and learning tactical and survival skills. Next comes your advanced training in cybersecurity, which can last anywhere from 9 to 40 weeks depending on your assignment. This training usually combines classroom lessons and hands-on experience in things like database design, computer networking, and sometimes learning a foreign language.
Once your enlistment — usually four years — is complete, you’ll have valuable skills, experience, and a security clearance that can help you build your cybersecurity career. You’ll also qualify for the GI Bill, which covers tuition and fees and provides extra money for housing, books, and supplies if you decide to go to college. Another option is to re-enlist and earn your degree while you’re still serving. From there, you could apply for officer commission school, which would allow you to move up from enlisted member to officer.
Joining the military isn’t the right choice for everyone, but for many people, it’s a powerful way to learn in-demand skills, serve their country, and set themselves up for a successful future in cybersecurity.
careers: myths A Few Truths
Don’t believe everything you see in the movies or on TV. Let’s debunk a few myths about careers in cybersecurity.
MYTH 1
C ybersecurity is just for tech wizards...
This is the most popular myth about cybersecurity, no thanks to Hollywood. While you need to be knowledgeable about IT to execute cybersecurity tasks, especially in the areas of risk management, networking basics, threat awareness, and tool kit maintenance, you don’t have to be a wizard to work in cybersecurity. In fact, the most important skills for success in a cyber job aren’t necessarily tech-related. Problem-solving, communication skills, and teamwork are commonly cited as being extremely important. Cybersecurity experts are rock stars in cyberspace, and most of them find the field to be enjoyable. The fast pace of change in technology, the challenge of solving problems, and the plentiful career opportunities across various sectors are exciting. And don’t forget the nice salaries!
MYTH 2
...and white guys.
There are more men in cyber than women, but women are making gains and have taken on major roles in the cybersecurity profession. And today’s cybersecurity professionals recognize the importance of diversity. Teams with a mix of people from different personal and academic backgrounds can gain valuable insights from the unique perspectives each member offers. There are many organizations ready to help you succeed, such as Women in Cybersecurity (WiCyS), the National Society of Black Engineers (NSBE), Black Girls Code, and the Women’s Society of Cyberjutsu.
See page 40.
MYTH 3
Cybersecurity jobs are all about coding and hacking.
Cybersecurity isn’t just one job — it’s an entire industry that touches almost everything: business, healthcare, law, government, and even sports. If you’re curious, observant, and like solving puzzles, there’s a place for you here. Hacking may grab the headlines, but the field is much broader. Cybersecurity also means defending systems, investigating attacks, managing risk, writing policies, and protecting data. You might specialize in digital forensics, cloud security, AI defense, or even law enforcement — whatever fits your interests and strengths.
REVIEW COPY
MYTH 5
MYTH 4
AI is taking over cyber jobs
AI is changing cybersecurity — but it’s not replacing people. It’s actually creating new kinds of jobs. Humans are still needed to train AI systems, make judgment calls, and understand context. The best cybersecurity teams use AI as a tool, not a replacement.
The best jobs are at the big tech companies.
With their cool-office vibe, Google and Meta offer enviable careers in cybersecurity but, obviously, they are not the only companies out there that offer well-paying, respectable tech jobs. Small tech-based companies also offer competitive salaries and benefits galore. But jobs in cybersecurity are available in every industry, including cybersecurity companies like Fortinet, and all government agencies. Private-sector companies generally pay more, but you may find the mission of protecting our national defense, for example, to be rewarding and self-fulfilling. See pages 44-53 for more information.
Is Cyber 4 U ?
Cybersecurity needs all kinds of minds. Try these fun puzzles that challenge your thinking.
Thinking about a career in cybersecurity? This guide is here to help you figure out if it might be a good fit for you.
The best careers often start with finding the sweet spot between what you’re good at, what you enjoy doing, and what the world needs. In cybersecurity, that means matching your interests and strengths with the skills professionals use every day.
Maybe you’re great with computers — or maybe you’re better at solving puzzles, understanding people, or communicating big ideas. Whatever your background, that’s actually a big
careers: test your abilities REVIEW
plus in cybersecurity! The field needs all kinds of talents.
Sure, many jobs are technical — people working with hardware, software, networks, and data systems. But just as many roles are more focused on human factors. That means areas like law, psychology, public policy, business, and even international relations all come into play. If you understand the basics of cybersecurity and bring other skills to the table, you could build a really exciting and meaningful career.
No matter the job, most cybersecurity work involves solving tricky
Find the patterns to fill in the blanks
1. W hat is the number missing from the last row?
184, 13, 85 96, 15, 483 127, 10, 82 149, , 77
Hint: Sometimes you need to meet in the middle to find the right way to move forward.
2. What is the next number in the sequence? 97, 63, 18, ,
Hint: A particular kind of math operation connects each number to the next.
3. What are the FIRST two numbers in this sequence? , , 10, 17, 26, 37, 50
problems, spotting patterns, thinking creatively, and working with others. Communication and teamwork are a must. Cybersecurity moves fast, and no one can keep up alone.
The activities in this guide are designed to give you a taste of the thinking and problem-solving that cybersecurity calls for. If you enjoy working through them — or even just figuring out parts — you might have what it takes to thrive in this field.
Our Student Workbook that goes with this guide has more challenges, available at start-engineering.com/cybersecurity-career-guide.
4. For each set of words below, what single word can be added to form a compound word or common phrase to all three?
Powder, stool, ball, _____________ Motion, poke, down, Blue, cake, cottage,
5. The “X” in each word takes the place of several letters missing from that word. Figure out what these missing letters are to complete the word.
1.H X ST
2. AR X RK
3. FR X ER
4. FEMI X
5. AT X TION
Hint: You can almost always count on some kind of connection among the answers to puzzles like this one.
Reasoning
6. You have a basket with 15 mini chocolate bars in it. You also have 15 friends who all want one. After giving all 15 of your friends one mini chocolate bar, there is still one mini chocolate bar in the basket! How can this be?
7. Five people got on a bus at five different stops. Iris got on before Rick, but after Victor. Ursula got on before Sammi, but after Rick. What was the order of people getting on the bus? What else do you notice about this order of names?
REVIEW COPY
8. The day before two days after the day before tomorrow is Wednesday. What day is it today?
Attention to Detail
9. In a computer program, valid combinations of data are 5 characters long which start with a letter and finish with a letter. In between numbers or letters may be used. Identify from the below, which line contains a violation of this pattern.
Line 1: A123B C546D m874A P461N M938A v847F
Line 2: x82aC D546j z834A 7421N y935B k142q
Line 3: A123B Ca46D m474A P411N Mj38A v8b7F
Line 4: x82aC D566j z8f4A h4x1N y93aB k122q
10. On a network, each computer has a special address called an IP address. In IPv4 the addresses must take the form [0-255].[0-255].[0-255].[0-255]. A valid IPv4 address for example is ‘192.168.13.2’. Look at the blocks of IP addresses below. Which block, if any, contains an invalid IP address?
⊲ End with a special character (e.g., !, @, #).
⊲ Can contain any combination of letters, numbers, and special characters in between .
Which of the following passwords violates this pattern?
Password 1: A1b2c3d4!
Password 2: xYz9876#
Password 3: AbC12@34
Password 4: 1234abcd
Password 5: !abcdEFGH
12. In an email address validation system, valid email addresses must meet the following criteria:
⊲ Start with a combination of letters and numbers.
⊲ Followed by the “@” symbol.
⊲ Followed by a domain name (e.g., example.com).
Which of the following email addresses violates this pattern?
Email 1: user123@example.com
Email 2: _user@example.com
Email 3: 123user@123example.com
Email 4: user@example.com123
Email 5: user@_example.com
12) Emails 2 (does not start with letter or number), 4 (does not end with a valid domain name), 5 (does not end with a valid domain name).
11) Passwords 3 (does not end with special character), 4 (starts with a number, does not end with a special character), and 5 (starts with a special character, does not end with a special character).
10) Block 2 (200.1.3.1.1 is the violation)
9) Line 2 (7421N is the violation)
So if “one day” after today is Wednesday, then today is -Tues day.
8) Tuesday. The “day before tomorrow” is today, and the “day before two days after” this time is really just “one day” after.
7) Victor; Iris; Rick; Ursula; Sammi. Their initials spell out VIRUS.
6) You gave the last friend of yours both the basket AND the mini chocolate bar.
5) hONEst; arTWOrk; frEIGHTer; femiNINE; atTENtion
4) foot; slow; cheese
3) 2, and 5. Consecutive odd numbers are the difference between each figure in the sequence. 2 + 3 = 5; 5 + 5 = 10; 10 + 7 = 17; and so on.
11. In a password validation system, valid passwords must meet the following criteria:
⊲ Be at least eight characters long.
⊲ Start with a letter.
2) 8. Multiply the digits of each number to get the next one in sequence. 1 x 8 = 8.
1) 14. The digits of the 1st and 3rd numbers add up to the 2nd number. 1, 4, and 9 add up to 14, as do 7 and 7.
ANSWERS
FAST GROWING & WELL PAID
Cybersecurity job openings have increased by 77%
since 2010, with a median annual salary in 2024 of $124,910 .

EMPLOYER DEMAND OUTPACES SUPPLY










There are only enough cybersecurity workers in the U.S to fill 74% of the cybersecurity jobs that employers demand.
NUMBER OF CYBER JOB POSTINGS IN THE U.S. IN 2025
514,359
SOURCE: US
DEPARTMENT OF LABOR, BUREAU OF LABOR STATISTICS
WHERE THE JOBS ARE
You will find cybersecurity jobs nearly everywhere, with states like California, Virginia, and Texas leading the way. But the greater metropolitan area comprising Virginia, Maryland, and the District of Columbia has a collective total of 62,338 job openings available!
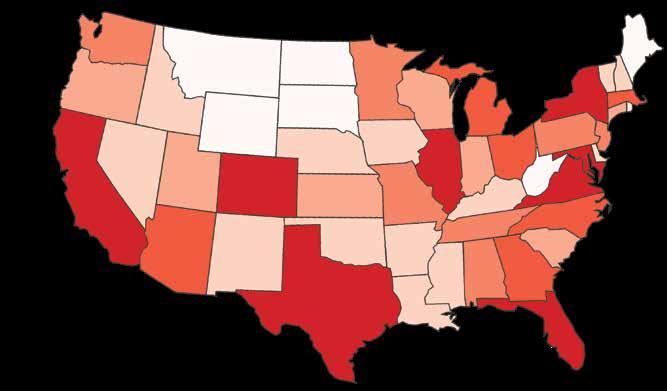


Start Engineering
Publisher: Robert F. Black
Creative Director: Stacie A. Harrison
VP, Learning and Communications: Eric Iversen
Editors/Writers: Eric Iversen, Stacie A. Harrison, Catherine P. Lincoln, and Margaret Loftus.
© Start Engineering, LLC www.start-engineering.com

Our mission at Start Engineering is to make the careers of the future, like cybersecurity, AI, data science, engineering, and biotechnology, exciting and accessible to as many students as possible. We publish educational books, develop information resources, and collaborate with individuals and groups to reach K-12 audiences of all kinds, with a focus on women, minorities, and underserved groups.
Our publications are available for purchase at start-engineering.com/shop. For bulk orders, we offer customized print or digital publications with your ad or message, and will work with you on pricing. If you have any questions, please reach out to our CEO Bob Black at bblack@start-engineering.com.

Start Engineering