
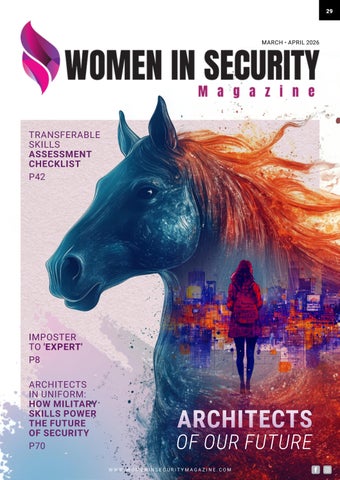
TRANSFERABLE SKILLS ASSESSMENT CHECKLIST
P42

IMPOSTER TO 'EXPERT'
P8
ARCHITECTS IN UNIFORM: HOW MILITARY SKILLS POWER
THE FUTURE OF SECURITY
P70

TRANSFERABLE SKILLS ASSESSMENT CHECKLIST
P42

IMPOSTER TO 'EXPERT'
P8
ARCHITECTS IN UNIFORM: HOW MILITARY SKILLS POWER
THE FUTURE OF SECURITY
P70
The theme of this edition, Architects of Our Future, is both a celebration and a wake-up call. It reminds us that transformation, growth and courage, both for ourselves and for the security industry as a whole, begin when we decide to take ownership of the paths we follow.
As we step into 2026, the Year of the Fire Horse, I’ve found myself deeply inspired. The last Fire Horse year was 1966, a time when women lit the spark of a global feminist movement, demanding equality and igniting a wave of feminine power that reshaped society. This year carries that same energy: bold, unapologetic and ready to dismantle what no longer serves us.
My personal focus this year is to read more, honour my boundaries and fully embrace my voice. Fire Horse years are about burning away old systems and birthing new paradigms, and that resonates deeply.
I’ve decided to become visible, to use my voice, my greatest asset, and to embrace community like never before. No more asking permission. It’s time to claim space unapologetically, to build in public rather than perfect in private, and to continuously evolve while designing the next decade of my future.

Through recent conversations in our industry, I’ve noticed a mix of hope and hesitation. While progress has been made, there’s a sense that diversity and inclusion efforts are losing momentum, that we’re slipping backwards. But now, more than ever, we need to stand firm. We must not shrink for anyone. We must continue to push forward, to lead by example and to architect the inclusive, innovative future our industry deserves.
In this issue we explore what it truly means to be Architects of Our Future through the stories and insights of remarkable women shaping the security landscape.
Jo Stewart-Rattray examines Why Security’s Skills Transformation is Being Driven by Career Changers and Brave Reinventors, highlighting how reinvention itself has become a cornerstone of progress in our field. Adriana Jones, in Architects of Our Future: Building a Structural Solution to Child Protection in a Digital World, explores how design thinking and innovation are reshaping the protection of children online — proving that architecture is not just about structures, but about safeguarding people.
Karen Stephens brings a thought-provoking perspective in The Power of the Pivot: Thriving Through Career Reinvention in Cybersecurity, unpacking the courage it takes to evolve in an industry that is moving faster than ever. Madhuri Nandi’s feature, Architecting What Comes Next, challenges us to think beyond the present and imagine what security can become when we build with foresight and heart.
In Betting on the Future: Why I Left my Secure Role to Protect the Next Generation, Marina Azar Toailoa shares her bold leap of faith, redefining what career security truly means. Jaimee Mullins pulls back the curtain on self-perception in Imposter to ‘Expert’, a story that will resonate with anyone who’s ever questioned their value. And Nadia Veeran-Patel’s Behind the Firewalls: A CISO’s Story of Growth, Grit and Leadership reminds us that strength and vulnerability often coexist in the same persona of leadership.
Finally, we bring you a collection of What’s Her Journey, stories from women around the world — powerful reflections of courage, transformation and leadership in motion. Each voice contributes to a shared blueprint for the future, one built on authenticity, resilience and unstoppable determination.


Together, these stories prove that the architecture of our future isn’t made of structures or systems alone — it’s built by people, by brave women who choose to stand tall, speak up and pave the way for others to rise.
The Year of the Fire Horse reminds us that this is our time, our moment to take the reins back. Just as the Fire Horse gallops forward fiercely, unhindered by old constraints, so too must we harness such energy. It’s time to lead with purpose, fuelled by fire, intuition and courage.
Abigail Swabey
PUBLISHER, and CEO of Source2Create
www.linkedin.com/in/abigail-swabey-95145312
aby@source2create.com.au





































JAIMEE MULLINS
by Jaimee Mullins, Technical Consultant, Saepio Information Security
How confidence, curiosity and community quietly compound into mastery in Cybersecurity
When I started my career I thought an expert was someone who knew everything, not most things, everything. An expert, in my mind, was a walking Google database. Someone you could ask any question and receive an immediate, confident, correct answer. I dreamt about being such a person.
Fast forward a few years, and something unexpected happened. People do come to me for things now. For advice. For opinions. For guidance in Cybersecurity. Yet, the feeling of being an imposter hasn’t gone away. If anything, it has simply evolved. Somewhere along the way, without consciously realising it, I became someone I once considered an expert, while still feeling I am figuring things out as I go.
If you are reading this and you are interested in Cybersecurity but wondering whether you’re “technical enough”, “smart enough” or “experienced enough”, I want you to know: imposter syndrome doesn’t mean you don’t belong. Often, it means you are exactly where you should be.
THE MOVING GOALPOSTS OF ‘EXPERT’
In Atomic Habits James Clear talks about the power of one percent gains compounding over time. At the start of my career, I didn’t feel those gains at all. Every day felt like a struggle for survival. Every new acronym, tool or concept felt overwhelming.
Looking back now, it’s clear that those small, almost invisible improvements added up. But here’s something no one really tells you: as your knowledge grows, so do the goalposts of what you consider “expert”.
At the beginning of my career, I was assigned a mentor. All I wanted was their knowledge. I believed they were the ‘expert’ I aimed to become. Then I gained experience. I learnt. I asked questions. I made mistakes. And before I knew it, I had become a mentor myself. At no point did I stop to reflect that, along the way, I had become someone else’s ‘expert’. That there might be someone watching me thinking, “If I could just know what she knows.”

"I believe strongly: no matter the field, the path to becoming an expert is far more universal than we think."
Funnily enough, that realisation came as I was writing this article. Today, I still feel like my own imposter, but I’m also someone else’s expert. I have learnt that both things can be true at the same time.
I didn’t start my career believing I belonged in Cybersecurity. I didn’t have a childhood dream of working in Cyber. I didn’t feel naturally technical or exceptionally gifted. What I did have was curiosity, a willingness to try, and the stubborn determination to keep going even when I felt out of my depth. And that’s important, because when we look at people we label as experts, on panels, podcasts, stages, or LinkedIn, we rarely see the messy middle. We see the highlights reel, not the selfdoubt, the failed exams, the awkward questions or the moments of thinking, “soon they’re going to realise I don’t know what I’m doing.”
For those of you reading this article at home, listening to podcasts, or watching videos of people you consider experts, I believe strongly: no matter the field, the path to becoming an expert is far more universal than we think. Here are the principles that quietly shaped my own journey.


Before you can move towards expertise, you need to understand what that word means in your context.
Is it:
• A specific job title?
• Deep knowledge of a particular product or technology?
• Being the go-to person for a niche area?
Being an expert doesn’t have to mean knowing everything about Cybersecurity. No one does. Cybersecurity is too broad, too fast-moving and too complex for that. Most so-called experts are simply people who went deep in one area and stayed curious in the rest. Once you define what expertise means to you, you can break it down into achievable steps. Suddenly, becoming an expert feels possible instead of overwhelming.
2. EXPOSURE IS EVERYTHING
You cannot think your way into expertise. You have to experience your way there. Exposure to different technologies, environments, incidents, people, conversations and perspectives is what accelerates learning. This is why internships, entry-level roles, shadowing and simply being in the room matter so much early on. Even exposure you don’t fully understand at the time is valuable. Your brain is quietly building context. I absorbed more than I realised just by listening to conversations I felt like I wasn’t yet qualified to participate in.
This was a game-changer for me. The fastest way to solidify learning is to teach it. Research consistently shows that people who explain concepts to others retain information far more effectively than those who passively consume it. Whether it’s:
• A LinkedIn post
• Explaining a concept to a colleague


• Giving a presentation
• Talking it through with a friend
Share what you learn.
Like many people, I used to bulk-learn for exams, pass them and then quickly forget most of the content. But, when I had to apply that knowledge, or convey it to others, it started to sink in. Sometimes I said the wrong thing and got corrected. That helped to further cement my learning.
During my internship, I was constantly told, “Fail fast.”
The idea was simple: the faster you make mistakes, the faster you learn, recover and move forward. Those words still guide me today.
WHAT TO REMEMBER ALONG THE WAY
The path from imposter to expert isn’t linear, and it isn’t easy, but there are a few truths I wish I had internalised earlier.
1. IT’S OKAY TO BE VULNERABLE
Not knowing something doesn’t disqualify you. Even experts are still learning, especially in Cybersecurity. Saying “I don’t know” is often the most honest and credible response you can give. You can always follow it up with “let me find out and get back to you”, to show both curiosity and initiative.
2. BACK YOURSELF
You are in the room for a reason. Your perspective matters, even if it’s still forming. I often remind myself that, if I ever feel like the smartest or most knowledgeable person in the room, I’m probably in the wrong room.
3. EVERYONE’S TIMEFRAME IS DIFFERENT
Experience takes time. Exposure takes time. You can accelerate learning, but you cannot shortcut lived experience.
4. COMMITMENT DETERMINES PROGRESS
If you want something badly enough, you will prioritise it. If you don’t, that’s okay too, but your expectations need to match your effort.
5. THIS IS NOT A SOLO JOURNEY
No one becomes an expert alone. Mentors, colleagues, managers and communities shape us, whether we realise it or not.
6. NETWORKING IS NOT OPTIONAL
Conversations matter. Absorb the language. Listen to how people think. Confidence often comes from familiarity.
REDEFINING THE FINISH LINE
Here’s what I have come to accept: your ‘expert level’ should always be unachievable. You may reach expert status in someone else’s eyes, but if you want to keep growing, in life and in Cybersecurity, your own goalposts should continue to move.
If being an imposter means I will forever be learning, questioning, and improving, then I’m happy to be an imposter rather than an expert.
And if you ever feel you have truly arrived, that there is nothing left to learn, maybe that is not the end of the journey, but the start of the next chapter.
FINAL REFLECTIONS: TAKE THESE WITH YOU
• You don’t need to feel ready to begin; readiness comes after action.
• Imposter syndrome is not a weakness; it’s often a sign of growth.
• Expertise is built quietly, over time, through small, consistent steps.
• One day, without realising it, you may become the person someone else looks up to.
And when that happens, I hope you remember the early version of yourself, the one who wondered if they belonged, and realise just how far you have come.
www.linkedin.com/in/jaimeemullins

Adjunct Lecturer School of Social Science (Cyber-Criminology)
Cybercrime is big business, thanks to technical advancement and interconnectivity creating more opportunities. This regular column will explore various aspects of cybercrime in an easy-to-understand manner to help everyone become more cyber safe.
It is 2026. Technology is ever developing; the geopolitical landscape is uneasy and the socio-economic environment is unsettled. It seems nothing is certain, but of one thing we can be sure: criminals and nation state threat actors somewhere, at some time, will misuse technology and human psychology for their own malicious agendas.
While technology develops and new ways to commit crime emerge, the motivations seem to stay the same. Examples are:
• Ideologies which can create the impetus for hacktivism, cyber espionage, online radicalisation, cyber terrorism and disruption.
• Financial motivators which can lead to data extortion, ransomware, romance fraud and invoice fraud.
"Instead of falling in a heap of despair and waiting for the next data breach or deepfake invoice fraud, we need to become the architects of our own futures, making deliberate choices on how we engage with technology, what we share online and how we prepare for potential cyber threats, whether at home or work."

• Deviant sexual behaviours that may be motivators for online child exploitation or grooming.
• Revenge seekers indulging in doxxing and cyber bullying and those who are motivated by the thrill of breaking into restricted systems.
These are just a few examples of motivators, but, as you can see, even as technology and the world seem to change rapidly, the foundational motivators for crime and cybercrime remain the same. What changes is how criminals achieve their results, such as the technologies they use and target.
Cyber threat actors are using GenAI powered automation to facilitate their campaigns efficiently and effectively. Many have a lot of resources, a lot of skills and the strong motivation to tirelessly locate potential targets and unleash their creations.
So, how do we, the fighters of cybercrime along with everyday citizens, stay safe from this veritable onslaught of motivated threat actors who seem to have a great many resources at their fingertips?
Instead of falling in a heap of despair and waiting for the next data breach or deepfake invoice fraud, we need to become the architects of our own futures, making deliberate choices on how we engage with technology, what we share online and how we prepare for potential cyber threats, whether at home or work.
Cyber risk is not just technical, it is also human, behavioural, psychological and strategic. We need to think long term resilience. As owners of our own future we can then encourage a mindset of understanding why security mechanisms are in place,

rather than just applying these because we are told to do so.
We need to think critically by questioning what we read or hear on social media, thinking about messages or emails we receive, and making the conscious choice to treat all personal data as the valuable property it is.
As architects of our own future we should not assume we will never be victims of cybercrime, but instead plan for potential eventualities. We must think about the online services we use, we must ask ourselves: “What do I do if my account is compromised?” “What is the fallout if my personal phone is stolen?” “What if this online service disappears tomorrow?”
If individuals (the everyday person) and organisations see themselves as future builders then security becomes a shared, understood, and positive value rather than an onerous and confusing checklist.
Cybersecurity, whether at home or work, is something me must consciously think about, not bolt on in a panic during a compromise. Cybersecurity must become part of our everyday decision making, just like the equivalent of looking both ways before we cross the road.
Becoming architects of our own future represents a powerful mind shift that can be used to significantly strengthen our own understanding of cybersecurity and how we, as everyday end users, can make conscious decisions to support our own online privacy and security.
Stay safe everyone.
www.linkedin.com/in/amandajane1
www.empressbat.com

I S N O W A I S A ' S N E W
P U B L I S H I N G P A R T N E R
P U B L I S H I N G P A R T N E R I S N O W A I S A ' S N E W
Watch this space!


Head of Information and Data Security Advisory, Team Global Express
Long before Jackie Orchard ever wrote a security policy or advised executives on AI governance, she was drawn to the art of investigation itself. As a student, she imagined a future in forensic pathology, captivated by the discipline of examining evidence and uncovering truth.
“My journey into cybersecurity began from an unexpected place,” she reflects. “Originally, I wanted to be a forensic pathologist. I was fascinated by the investigative process, the attention to detail, and uncovering the truth from evidence. While life took me in a different direction, that analytical mindset and love of forensics never left me.”
That instinct would find its home in technology. In 2001, Jackie entered the security profession at Westpac Group, where she began as a Security Analyst and Liaison Manager. There, she worked closely with law enforcement on theft, holdups, and physical security incidents, discovering that cybersecurity was, at its core, investigative work.
“Security work offered similar investigative opportunities,” she says. “It required the same meticulous attention to evidence and systematic investigation that originally drew me to forensics.”
As her career evolved, so too did the nature of the investigations. Jackie transitioned into information security roles, where she encountered digital forensics and eDiscovery for the first time.
“When I discovered digital forensics and eDiscovery, it felt like coming home,” she explains. “Here was forensics, but in the digital realm examining logs, tracking data flows, reconstructing events from digital evidence.”
She immersed herself in building frameworks and strengthening governance, redesigning technology codes of use, reengineering information security policies, and driving awareness programs that achieved engagement levels well beyond industry norms. Yet even in these early years, Jackie understood that technical capability alone wasn’t enough.
“What helped me navigate those doubts was reframing them. Instead of seeing uncertainty as a sign I was in the wrong place, I recognised it as evidence I was doing something genuinely challenging and worthwhile.”
“I recognised early that cybersecurity isn’t purely technical, it’s about understanding people, processes, and organisational dynamics,” she says. “You need to speak multiple languages: technology, legal, business, and compliance.”
Her ability to translate between these worlds became one of her defining strengths. In 2003, when she stepped into a senior consulting role focused on security communications and compliance, she was tasked with enhancing enterprise-wide frameworks. It was a daunting responsibility, but she approached it with curiosity rather than hesitation.
“Rather than being intimidated, I immersed myself in learning,” she recalls. “I developed policies aligned with international standards, obtained executive stakeholder concurrence, and implemented communication strategies that fundamentally changed how the organisation engaged with security.”
Still, the most transformative moment of her career came more than a decade later, when she was asked to build something that did not yet exist.
“The most transformational step came in 2015 when I was appointed to build Westpac’s comprehensive internal eDiscovery capability from scratch,” she says. “There was no playbook, no established team, no precedent.”
The scale of the challenge was immense. Jackie and her team operationalised a mature capability within just 20 weeks, ultimately delivering millions in cost savings and supporting over 100 regulatory responses. The achievement earned national recognition, including Australia’s Legal IT Team of the Year.
“That initiative demonstrated not just technical capability but strategic leadership,” she says. “It showed that security can deliver genuine business value.”
Yet Jackie’s path was never linear. Along the way, she stepped into roles outside traditional cybersecurity, including business development at Dimension Data, branch leadership at Commonwealth Bank and National Australia Bank, and project coordination for the National Breast Cancer Foundation. Each experience added a new dimension to her leadership.
“These experiences reinforced that uncertainty and discomfort are often signals that you’re expanding your capabilities rather than signs you should retreat,” she says.
Like many in cybersecurity, Jackie experienced moments of doubt, particularly when stepping into unfamiliar territory or building new capabilities from nothing.
“I remember thinking, ‘Am I the right person for this? Do I have what it takes?’” she says candidly. “What helped me navigate those doubts was reframing them. Instead of seeing uncertainty as a sign I was in the wrong place, I recognised it as evidence I was doing something genuinely challenging and worthwhile.”
Today, as Head of Information and Data Security Advisory at Team Global Express, Jackie operates at the intersection of technology, governance, and business strategy. Her work involves assessing emerging technologies, advising leadership, and building frameworks that allow organisations to innovate safely.
“The most satisfying aspect of my role is being able to say ‘yes, here’s how’ rather than just ‘no, that’s too risky,’” she says. “Too often, security is positioned as the department that blocks innovation. I find it far more rewarding to help organisations adopt new technologies safely while ensuring appropriate controls are in place.”
This philosophy has shaped her entire leadership approach. Rather than acting as a gatekeeper, she sees security as an enabler of progress.
“When I conduct a comprehensive security assessment, I’m helping leadership understand complex risks and make informed decisions,” she explains. “The goal is always to enable innovation while maintaining appropriate guardrails.”
Her advisory work increasingly focuses on emerging technologies like artificial intelligence, which she believes will reshape the cybersecurity landscape in profound ways.
“AI is going to fundamentally reshape both cybersecurity threats and defences,” she says. “The challenge will be governance. Organisations are rushing to adopt AI tools, often without adequate security frameworks. We need to ensure these technologies are secure, compliant, and don’t create new vulnerabilities.”
At the same time, Jackie remains deeply aware of the human dimension of security. She has seen firsthand how culture, communication, and leadership influence security outcomes.
“The most elegant security framework is worthless if people won’t use it or if leadership won’t support it,” she says. “Effective security is about alignment, communication, and trust.”
Looking back, she sees her unconventional path not as a deviation, but as an advantage.
“My path definitely unfolded organically,” she reflects. “I didn’t start my career thinking I wanted to be a Head of Security. Instead, I followed opportunities that aligned with my interests and allowed me to make a meaningful impact.”
She believes that openness to opportunity, combined with continuous learning, is essential for anyone entering the field.
“Your network, your credibility, and your track record of delivering results will open more doors than any certification,” she says. “People remember whether you delivered value, communicated clearly, and approached challenges with integrity.”
Despite the demands of senior leadership, Jackie has learned the importance of balance and perspective.
“Balance in cybersecurity is challenging,” she acknowledges. “Security incidents don’t respect business hours, and there’s always more work to do. What’s helped me is being intentional about boundaries while remaining flexible when genuinely needed.”
For Jackie, resilience comes not just from technical expertise, but from maintaining curiosity and purpose.
“What continues to fascinate me is the constant evolution,” she says. “Every new technology presents new security challenges and opportunities. The field never stops demanding that you learn, adapt, and think critically.”
It is, in many ways, the same investigative journey that first captured her imagination. Only now, instead of examining physical evidence, she is shaping the frameworks that protect entire organisations following the digital trail, uncovering hidden risks, and enabling a safer future.
www.linkedin.com/in/jackieorchard

For Meegan Bryant, cybersecurity was never a sudden pivot. It was the natural evolution of a career built on understanding security in its fullest sense not as isolated controls, but as a connected system of people, policy, and protection. Beginning in physical and information security before transitioning into cyber, she saw early on that true resilience required more than technical solutions. It required strategy, clarity, and integration.
“My interest grew out of a broader career in security starting with physical and information security, then evolving into cyber,” she explains. “Over time, I saw how interconnected these domains are, and how strategy must bridge them. That sparked my drive to ensure organisations, especially in defence and government, had holistic protection.”
That mindset would define her career. Rather than chasing technical depth alone, Meegan deliberately positioned herself where she could influence how security functioned at scale. She sought roles that
allowed her to translate abstract frameworks into meaningful action, ensuring security wasn’t just documented, but operationalised.
“I deliberately sought roles where I could translate policy into practice,” she says. “Managing Australian defence programs and serving as CSO and CISO gave me exposure to both strategic oversight and operational realities. I built credibility by simplifying complex frameworks and operationalising compliance.”
In her current role as a Defence Security Consultant, Meegan operates at the intersection of governance and reality, a space where even the most welldesigned regulations can fail without practical implementation. Meegan sees first hand how smaller organisations, often with limited resources, struggle to meet growing compliance expectations.
“The most complex aspect is balancing regulatory alignment with operational reality,” she says. “Small organisations often lack resources, so I
overcome this by creating templates, checklists, and workflows that make compliance achievable without overwhelming staff.”
This commitment to accessibility reflects a deeper belief that security should empower, not burden. For Meegan, success is measured not by the existence of policies, but by whether organisations feel confident using them.
“Seeing organisations confidently adopt security practices because policies are clear, usable, and empowering brings me the most satisfaction,” she says.
Like many professionals who build careers outside purely technical roles, Meegan experienced moments of uncertainty early on. She questioned whether specialising in governance and compliance would limit her opportunities in a field often associated with technical mastery. But over time, she recognised that leadership in cybersecurity depends on strong governance foundations.
“Yes, I questioned whether specialising in governance and compliance would limit me compared to more technical paths,” she reflects. “I navigated those doubts by recognising that leadership roles like CSO and CISO depend on strong governance foundations.”
Her career path, shaped less by rigid planning and more by recognising where she could make a meaningful impact.
“My path unfolded organically,” she says. “Each role built upon the last, and I leaned into opportunities where I could make security strategy practical and effective.”
Mentorship played a pivotal role in shaping her confidence and perspective. Leaders in defence and government demonstrated the importance of accountability and clarity, reinforcing the idea that security must be understood by everyone it protects.
"Mentorship played a pivotal role in shaping her confidence and perspective. Leaders in defence and government demonstrated the importance of accountability and clarity, reinforcing the idea that security must be understood by everyone it protects."
“Mentors in defence and government who highlight clarity and accountability shaped my journey,” she says. “Their influence reinforced my belief in practical, accessible security, and to trust my abilities.”
Today, her work spans policy development, mentoring, risk oversight, and strategic alignment. Every task serves the same goal: embedding security into daily operations so it becomes a natural and sustainable part of organisational culture.
“My day is a mix of policy development, mentoring, risk oversight, and strategic alignment all with the goal of making security compliance accessible, effective, and embedded into everyday operations,” she explains.
Meegan relies on governance tools such as risk registers, compliance tracking systems, and vulnerability dashboards to support this mission. Yet she is quick to point out that effectiveness does not always depend on sophisticated technology.
“Governance tools like risk registers, compliance tracking systems, and vulnerability management dashboards are pivotal,” she says. “Even structured spreadsheets can be powerful in small organisations.”
Her approach reflects a broader philosophy: security is not defined by complexity, but by clarity and consistency.
“Security is more than locks and firewalls; it’s about people, trust, and resilience. Build communication skills as much as technical one s,” she says. “Back yourself. Your upbringing doesn’t define you; what you do with it does.”
Looking ahead, Meegan sees rapid transformation across the cybersecurity landscape. Artificial intelligence, regulatory expansion, and supply chain security will reshape how organisations defend themselves, while adversaries adopt increasingly sophisticated tactics.
“AI-driven threat detection, supply chain security, and regulatory expansion in critical infrastructure will be highly impactful,” she says. “At the same time, ransomware targeting small organisations, AI-enabled social engineering, and third-party/vendor risk will be the most pressing threats.”
Staying ahead requires continuous learning. Meegan actively engages with professional networks, conferences, and trusted industry sources, including advisories from the Australian Cyber Security Centre, ensuring her knowledge evolves alongside the threat landscape.
She also values the importance of community. Her involvement with organisations such as the Australian Women in Security Network provides connection, mentorship, and a shared sense of purpose in an industry where representation and support matter deeply.
“Membership provides mentorship, networking, and a sense of community,” she says.
Meegan is also deeply aware of the growing demand for professionals who can bridge governance and technical domains. While many individuals specialise in one or the other, she believes the future belongs to those who understand both.
“The hardest roles to fill are those requiring both technical expertise and governance awareness,” she explains. “Many professionals lean heavily one way, but the blend is rare and highly valuable.”
For those considering cybersecurity, especially those transitioning from other careers, her advice is grounded in encouragement and realism.
“Leverage your transferable skills whether communication, project management, or analytical thinking,” she says. “Cybersecurity is broad; don’t feel pressured to be ‘technical’ immediately. Find your niche and build from there.”
If she could speak to her younger self, her message would be simple, but powerful.
“Security is more than locks and firewalls; it’s about people, trust, and resilience. Build communication skills as much as technical ones,” she says. “Back yourself. Your upbringing doesn’t define you; what you do with it does.”
It is this philosophy grounded in clarity, confidence, and purpose that defines Meegan Bryant’s journey. In a field often driven by rapid change and technical complexity, she has built her career on something more enduring: making security work, not just in theory, but in practice.
www.linkedin.com/in/meegan-b-8aa75547


LRMG as the CISO
Iremember my introduction to the tech world in South Africa. Apartheid had ended a year prior and I was my parents’ hope for equality, which is why they thrust me into a model C school over 30kms from home. It was in Grade 10 that I chose computer science as one of my subjects. I wasn’t sure of my expectations at the start, but I was good at it, and when I started coding in Pascal, I was happy seeing my programs come to life.
Fast forward to my becoming an undergraduate student at WITS University, where I was sure I would maintain my enthusiasm. The first year was the best year of my life, until I discovered I hated information systems at a tertiary level (who knew studying involved so much theory!). I eventually dropped out due to illness and financial stress, but this was just the beginning of my long love/hate relationship with the tech world.
My first job was in a big financial services firm where I struggled to find my passion and purpose in life. A year into that role my sister (who was already in tech) asked me if I’d like to work with her at a small consulting firm. The job was as a systems trainer, training staff at a large global mining company on their procurement system.
Boy, did I fall in love with this job. Their procurement system was based on Lotus Notes and, during my five years working there, I trained on the system, was able to get certified to administer it and, later, to become a Lotus Notes developer. I was one the few women at that time to gain both certifications, but I started to hate the job. Whilst I was great at coding, I hated being stuck behind a computer all day.
I am someone who needs conversation and people to keep her going. Whilst I loved where I worked and
the people I worked with, I knew I had to spread my wings. So, I applied for a job 90kms away at another small IT consulting firm. Luckily for me one of my previous managers worked there and I landed a systems administrator position.
At the time I was the first person of colour and the only female employee, which meant I was in a team with 16 men. What an experience! Whilst it wasn’t the nurturing culture I had been accustomed to, I learnt to hold my own. My boss was one of my biggest supporters and is still someone I call a friend. I managed to become an account manager and the liaison person between our clients and internal development teams. This is where my love for the tech world. started.
A few years later one of our clients was looking for a service delivery manager for its IT operations team and my boss asked the client’s CIO to employ me. Although sceptical, she decided to give me a chance. When I started I was in charge of six men who weren’t entirely happy with the change in management, but we quickly became a solid team of 11 with four females in the ranks. Service delivery greatly improved. Our statistics were phenomenal.
Towards the middle of 2015 our UK based parent company expressed the need for our compliance expertise for an information assurance project they were running. It was during this time I started to take a keen interest in information security and my obsessive compulsive personality greatly assisted my ability to learn. Another team member was originally chosen to run the project, but I was asked to steer it because of my increasing knowledge of the field.
Towards the end of 2015 my CIO introduced me to the UK CISO, and this was the start of a beautiful relationship and career.
By early 2016 I had already obtained my first information security certification and was dealing with the UK security team every couple of months. The plan was to have the UK team come to South Africa and train us over a two week period, but this
"Every road taken during my journey was bumpy, often
intimidating and daunting, but the lessons learnt were fruitful and
many. Today, I find myself more concerned about
the
safety of our world and often compare my life to a series of final destination movies."
proved to be a very expensive exercise. So, it was decided one of us should go to the UK instead. I was chosen, but, as luck would have it, only days after learning I would need to be there for a month, I discovered I was pregnant with my first child, after several years of infertility.
I gingerly approached my CIO thinking the opportunity would be taken from me because no one would assign a pregnant woman to such an important project. This, readers, is the point at which my life changed, and my faith in humanity was restored.
My female CIO discussed the situation with my female CFO and they decided my pregnancy would not impact my competence: they still wanted me to go. At this point I did question if my fate would have been different if the circumstances had been reversed.
October 2016 saw me 28 weeks pregnant, packing my bags and travelling to the UK. The plan was for me to work in our offices in Southampton for three weeks then spend a week in Colico, on Lake Como in Italy, for an audit. Suffice to say, I was extremely excited, overwhelmed and scared at the prospect of this experience, which became the foundation of my security journey.
"However, knowing what I know now, I would not change my path. I did learn to enjoy it and be thankful for my opportunities. I have led teams, gone back to holding fully technical roles and then back to leading a team. Overall, the experience and lessons learnt were fulfilling, and I finally found my place in the tech world."
He looked at me and said, “You do know we are on ISIS’ hit list, right?”
No Tom, I did not know that, otherwise my very pregnant self would not be standing here. He assured me that we would be well guarded and would be fine. A few bodyguards later, we were in fact fine, and what a glorious trip it turned out to be.
I returned to South Africa a month later, not so bushy tailed, because my eyes had been opened to the intense world of information security and how intelligence is treated. I spent the next few years leading the information assurance project across the organisation in different countries before going on to do the same for other organisations.
This is where my story gets wild and, sometimes, I find it hard to believe myself: it felt like a scene from a movie. The organisation was dealing with highly classified and sensitive information (think MI5 intelligence levels) and made sure I was escorted on my bathroom visits, which were very frequent for my pregnant self. I was given no time to linger anywhere near anything of significance.
On one occasion when my UK colleague and I had to travel to Colico, whilst waiting to board our flight at Heathrow, I received an SMS saying: “Please be on high alert: ISIS terrorist cell found 70kms outside Colico.” I turned to Tom (head of security at the time and also the guy who led the team that, on one occasion, had rescued Prince Harry in Afghanistan) and asked him what the warning was about.
Every road taken during my journey was bumpy, often intimidating and daunting, but the lessons learnt were fruitful and many. Today, I find myself more concerned about the safety of our world and often compare my life to a series of final destination movies. However, knowing what I know now, I would not change my path. I did learn to enjoy it and be thankful for my opportunities. I have led teams, gone back to holding fully technical roles and then back to leading a team. Overall, the experience and lessons learnt were fulfilling, and I finally found my place in the tech world.
Throughout my, now 10-year, journey in information security, I have had to remain resilient, focused and forever learning. Today, the best advice I can give those wanting to take this path is: remain focused, because none of us know everything, continue to learn on the job and tackle the challenges you will meet every day, fiercely, hands on.
And those of us who were lucky to have got into cybersecurity early on now have a duty to make sure we pave the way for others to follow. Lead always with heart, passion and morals, and enjoy the ride while it lasts.
www.linkedin.com/in/nadiavp


Chief Information Security Officer (CISO IT/OT)
Hajar Nachate, Chief Information Security Officer, has built her career in cybersecurity with one guiding principle: it’s not about age, but about skills and continuous growth. By embracing career changes and reskilling, she has shaped herself into the leader she is today.
Working across diverse environments, she helps protect critical systems where reliability, safety, and continuity are essential. Her journey reflects the path of many women in technology driven by curiosity, commitment, and the desire to make a real impact.
Her experience reflects the path of many women in technology driven by commitment, curiosity, and the desire to make a meaningful impact. Through her work, she helps shape a future where innovation goes hand in hand with trust and resilience.
This personal journey is part of a broader reality: ‘’The future is not something we wait for, but something we actively shape every day’’
The future is often described as something we are waiting for. Yet, every day, it is already being shaped through decisions, resilience, courage, and vision.
The architects of our future are not only those who design buildings or technologies, but those who dare to imagine a better world and take responsibility for building it. Increasingly, women are standing at the heart of this transformation.
For a long time, women have been underrepresented in spaces where the future is designed: technology, security, leadership, and strategic decision-making. Today, that narrative is changing. Across industries, women are redefining what leadership looks like grounded not only in performance, but in purpose, ethics, and long-term impact.
“The future belongs to those who believe in the beauty of their dreams.” — Eleanor Roosevelt
This belief is not abstract. It is embodied every time a woman chooses to step into spaces where she was not expected, to speak up where silence was easier, and to build where others doubted.
In an increasingly digital world, cybersecurity has become one of the most critical foundations of our future. Our cities, hospitals, industries, financial systems, and even our personal identities rely on digital infrastructures. Without trust and security, innovation cannot survive.
Cybersecurity is often seen as purely technical, yet at its core, it is deeply human. It is about protecting people, data, and societies from disruption. It is about resilience, anticipation, and responsibility. Cybersecurity professionals are the invisible architects who ensure that progress remains safe, reliable, and sustainable.
For women in cybersecurity, the journey carries additional meaning. Entering a field historically dominated by men requires perseverance, continuous learning, and confidence. But it also brings a unique perspective, one that values collaboration, risk awareness, and ethical design. Diversity in cybersecurity is no longer a “nice to have”; it is essential for building systems that truly serve everyone.
My own journey into cybersecurity was driven by a simple conviction: technology should empower, not endanger. Working in cybersecurity management, I have seen firsthand how digital transformation can unlock extraordinary opportunities but also how
fragile systems become when security is treated as an afterthought.
Each project, each incident, and each strategic decision reinforces the same lesson: the future is not only about innovation, but about trust. Being part of this field means constantly balancing speed with caution, ambition with responsibility. It is a demanding path, but also a deeply meaningful one especially as a woman contributing to spaces where our voices matter more than ever.
This journey is not just mine. It reflects the path of many women who are quietly shaping the future in technology, security, education, health, and leadership, often without visibility, but with undeniable impact.
What distinguishes women architects of the future is not a single skill, but a mindset. A long-term vision. An ability to connect technical progress with human values. Whether designing secure digital systems, leading teams, educating future generations, or influencing policy, women are redefining how the future is built.
"The
future is often described as something
we
are waiting for. Yet, every day, it is already being shaped through decisions, resilience, courage, and vision. The architects of our future are not only those who design buildings or technologies, but those who dare to imagine a better world and take responsibility for building it. Increasingly, women are standing at the heart of this transformation."
The future needs architects who design with care, ethics, and inclusivity. It needs women who dare to claim their place not by imitating existing models, but by creating new ones.
The future is not a destination we will one day reach. It is something we are constructing now, through daily choices and collective responsibility. By embracing cybersecurity, ethics, diversity, and resilience, we ensure that the world we build is not only advanced— but safe, fair, and human.
WOMEN ARE NOT ONLY PART OF THIS FUTURE. THEY ARE DESIGNING IT.
www.linkedin.com/in/hajarnachate

Curiosity has a way of opening doors long before we realise we are standing at the threshold of a career. For Koketso Rihlampfu, now a Senior Manager: Lead Information Security Officer, that curiosity began with a simple but powerful question: how do systems work, and what happens when they fail?
“My initial interest in cybersecurity was sparked by curiosity,” she explains. “I was fascinated by how systems worked, how they could be broken, and how weaknesses could be exploited if security was not really prioritised.” Early in her career, it was the investigative nature of penetration testing that captured her attention. “The technical challenge drew me in, particularly the investigative nature of penetration testing and understanding attacker behaviour. This still remains one of the jobs, throughout my career, that I enjoyed doing the most.”
But curiosity alone does not build a career. Koketso made a deliberate choice to pursue hands-on experience, gravitating towards roles that allowed her to apply theory in real-world environments. “One of the most pivotal steps was intentionally seeking handson experience early in my career. I gravitated towards roles that exposed me to real-world environments rather than purely theoretical work, including penetration testing and being a consultant. I got to experience the practical side of all that theoretical work I learned and that expanded my knowledge and skills greatly.”
She also understood early on that cybersecurity demands constant evolution. “I invested heavily in continuous learning and certifications, not just to build credibility, but to deepen my understanding across multiple security domains,” she says. Yet some of her most important growth came from moments of discomfort. “Equally important was surrounding myself with people who challenged me, asking questions, and being willing to take on opportunities that felt uncomfortable at the time. That’s actually where I got to grow the most in those uncomfortable positions.”
Like many women in cybersecurity, Koketso’s journey was not without moments of doubt. “Cybersecurity can be an intimidating field, particularly in
“Seeing users within our organisation start to make better decisions when it comes to information and cybersecurity and understanding that security is everyone’s responsibility is quite fulfilling. I find great satisfaction in mentoring others and contributing to a culture where cybersecurity is understood as a shared responsibility.”
environments where you may be the only woman in the room or where expectations are constantly shifting,” she reflects. One defining moment came during a period when she seriously considered leaving the field altogether. “I still remember a time when a friend and then colleague of mine, his name is Aadil, who once had a talk with me one day when I was ready to give up and change careers altogether because I felt it was all just too much for me at that time. We were standing by the parking lot and he spoke so much life into me the voice of reason I didn’t know I needed.”
That conversation became a turning point. “He reminded me that growth often comes with discomfort and that really stuck with me and helped shape me into the person I’ve become today. Over time, confidence replaced uncertainty as experience accumulated, but I’ve also learned that self-doubt doesn’t disappear entirely, you simply learn to move forward despite it.”
Her career path unfolded organically rather than through a fixed plan. “I didn’t start out with the goal of becoming a CISO. Instead, I focused on mastering each role I stepped into and staying curious about other areas of security,” she explains. As her experience expanded from technical work into governance, risk, and leadership, her perspective shifted. What once centred on solving technical problems grew into something broader and more strategic. “Today, my passion lies in building secure, resilient organisations where cybersecurity is embedded into business strategy rather than operating as a standalone technical function.”
In her current role, Koketso navigates one of the most complex realities in modern cybersecurity: balancing protection with progress. “The most complex aspect of my current role is balancing risk, business enablement, and resource constraints in an environment where threats evolve daily,” she says. “Cybersecurity decisions rarely exist in isolation, they affect operations, customers, revenue, and reputation.” Her approach is rooted in clarity and alignment. “I focus on risk-based decision-making, clear communication with executives, and ensuring my team understands not just the ‘what’ but the ‘why’ behind security initiatives. Building trust with stakeholders and aligning security objectives with business outcomes has been critical.”
That leadership perspective has also deepened her sense of fulfilment. “The most fulfilling aspect of my role is seeing the tangible impact of security initiatives, whether that’s a team growing in confidence, improved resilience across the organisation, or executives making informed risk decisions,” she says. “Seeing users within our organisation start to make better decisions when it comes to information and cybersecurity and understanding that security is everyone’s responsibility is quite fulfilling. I find great satisfaction in mentoring others and contributing to a culture where cybersecurity is understood as a shared responsibility.”
Looking back, Koketso recognises that her success was not defined by fitting a predetermined mould. “I would tell my younger self not to be intimidated by the idea that cybersecurity is only for a certain ‘type’ of
person. I’d emphasise that curiosity, resilience, and a willingness to learn are just as important as technical ability.” Her advice is simple but powerful: “This field is very broad, just figure out what excites you and run with it.”
She also emphasises that strong foundations matter, both technically and personally. “A strong foundation starts with understanding computing fundamentals, networking, and operating systems. Beyond that, exposure to information security principles, risk management, and governance is essential. However, equally important are soft skills such as critical thinking, communication, and problem-solving.”
As cybersecurity continues to evolve, Koketso sees transformation accelerating. “Over the next two years, I anticipate a significant acceleration in the use of artificial intelligence, both by defenders and attackers. We’ll also see greater emphasis on cyber resilience, not just prevention, as organisations accept that breaches are inevitable. These developments will push cybersecurity further into the core of business decision-making.”
Her perspective on leadership extends beyond technical capability. When considering career opportunities, she looks beyond compensation. “I would consider the organisation’s leadership maturity around cybersecurity, the support structure available to the role, and whether security is genuinely valued at an executive level,” she explains. “Culture, ethical alignment, and the opportunity to make a meaningful impact are also important.”










CISO at Transdev Australasia
Laura Jone’s pathway to becoming CISO at Transdev Australasia did not begin in a server room or a computer science lab. It began in drug intelligence.
“I initially began my career in drug intelligence, back in the mid 2010s when cryptocurrencies were just coming out and online drug markets like Silk Road were booming,” she explains. “So following and researching cybercrime was my first foray into the cyber world.”
At a time when digital currencies were reshaping criminal enterprise and law enforcement alike, she found herself tracking emerging patterns of online behaviour, illicit marketplaces and the rapidly evolving intersection between technology and organised crime. The work demanded analytical rigour, political
awareness and an understanding of human systems skills that would later become the backbone of her cybersecurity leadership.
Yet stepping fully into cybersecurity was not without doubt.
“I experienced uncertainty for sure,” she says candidly. “I’m a generalist rather than technical, and my university studies were in Politics and Anthropological Science. I really never thought I’d be the right fit for something that sounded so technical from the outside.”
Like many women entering the field from nontraditional backgrounds, she initially questioned whether she belonged. But as her exposure to the discipline deepened, so too did her perspective.
“The more I learned about it, the more I realised cybersecurity is a lot broader than computer science and as an industry, it’s crying out for more generalists.”
That realisation shaped the trajectory of her career. Rather than trying to mould herself into a technical specialist, she leaned into her strengths.
“Definitely not a clear vision!” she says of her early ambitions. “My roles have covered cybercrime, intelligence, cyber awareness, cyber risk and now managing the whole programme for my business. What I’ll say is that I didn’t try to make myself fit in a technical specialist box that’s a fit for plenty of other people, but not me.”
Today, as CISO in the public transport sector, she oversees the cyber programme for Transdev’s Australian and New Zealand operations, a vast ecosystem that includes trams, heavy rail, light rail, buses and ferries. The operational complexity mirrors the complexity of modern cyber risk.
“We have trams, heavy rail, light rail, bus and ferries so the cybersecurity demands are as varied as our business,” she explains. “Mine is a ‘many hats’ role covering everything from incident response to training and awareness, governance and compliance, business continuity, and overall security uplift.”
Despite the breadth of responsibilities, her core priority remains distinctly human.
“My priority is always that my fellow journey-makers never feel panicked, embarrassed or silly in their cybersecurity concerns. Shaming is a cybercriminal’s goal, not mine!”
It is a philosophy rooted in psychology as much as policy. In environments where public safety and service continuity are paramount, cultivating trust is not optional, it is foundational. By removing shame from the equation, she strengthens the organisation’s defensive posture. People report earlier. Conversations happen faster. Risk is surfaced before it escalates.
Her belief in the broader context of cybersecurity extends to education as well.
“Don’t overlook humanities!” She advises aspiring professionals. “Everything is political, including cybersecurity.”
In her view, the field is not simply about systems and code, but about power, governance, influence and decision-making. Understanding human behaviour, institutional structures and societal drivers is just as critical as understanding vulnerabilities and patch cycles.
Looking ahead, she sees artificial intelligence dominating industry conversations but not always in the right way.
“AI of course,” she says, when asked about the most impactful developments in the next two years. “But mainly from an executive stakeholder perspective I think cybersecurity professionals have a responsibility
to manage expectations about what AI can, cannot and should not do.”
In other words, leadership in this era will require measured guidance as much as innovation. Hype management will become as important as threat management.
When considering career progression herself, remuneration is not the defining factor.
“Definitely flexibility!” she says. “I think cybersecurity is an industry which requires a remote mindset; cybersecurity problems hardly ever arise in the location you happen to be in. To be able to problem solve, manage remediation and connect with and influence colleagues remotely is its own skill set, and one that should be treated as such.”
For her, flexibility is not a perk; it is operationally aligned with the nature of cyber risk.
For those transitioning into the field from other professions, her message is both practical and empowering.
“Don’t let the technical aspects of our industry overwhelm you or turn you away from the industry if it’s not your strong suit,” she says. “Most of my day to day is communication, customer resolution, prioritisation and risk management. There’s a huge pool of skills to draw from that are useful in our industry, so find yours.”
Laura Jones’ journey is a reminder that cybersecurity is not defined by code alone. It is defined by curiosity, courage and the willingness to claim space in a field that is still evolving. From drug intelligence to leading cybersecurity across public transport networks spanning two countries, her path illustrates that sometimes the strongest signal to follow is not technical at all, it is human.
www.linkedin.com/in/laura-j-325961122

Erin Blanchard
Technology Risk Consulting Vacationer
For Erin Blanchard, cybersecurity was never just about technology. It was about understanding systems, uncovering hidden risks, and discovering how technical knowledge could be applied to protect something far greater than code. What began as a high school subject would ultimately evolve into a purposeful and fast-developing career path shaped by curiosity, initiative, and a willingness to learn at every opportunity.
Her introduction came through studying Information Processes & Technology during high school, a subject that exposed her to the fundamentals of information systems and data management. It gave her an early appreciation for the invisible frameworks supporting modern life. But it was a hands on experience that transformed interest into passion.
“My interest in cybersecurity was first sparked during high school when I chose Information Processes & Technology as an HSC subject,” Erin explains. “This subject introduced me to the fundamentals of information systems, data management, and communication frameworks, which gave me an appreciation for how technology supports everyday processes and impacts various industries.”
The defining moment came during Year 12, when Erin secured a week-long work experience placement at the Australian Signals Directorate in Canberra. Immersed in real-world challenges, she was exposed to the practical side of cybersecurity in ways that few students encounter so early.
“This program was hands-on and allowed me to extend my knowledge through practical challenges such as identifying security intrusions on computer systems, analysing logs for suspicious activity, and using open-source tools to recover encryption keys and decrypt data,” she says. “It was fascinating to see how cybersecurity professionals protect national interests and how technical skills can be applied to solve real-world security problems.”
When Erin began university, she faced the difficult task of choosing a specialisation. With options ranging from Business Information Systems Management to Interaction Design, it was ultimately cybersecurity that captured her attention. The intellectual challenge and relevance of the subject matter made the decision clear.
“After exploring the introductory subjects, I found the content in my cybersecurity courses to be both engaging and intellectually challenging, which solidified my decision to major in Networking & Cybersecurity,” she says.
Her academic journey soon expanded beyond the classroom. An internship with Origin Energy’s Identity and Access Management team allowed her to apply theory in a corporate environment, giving her firsthand experience with the systems that protect organisational assets.
“I worked on projects related to user provisioning, access reviews, and implementing multi-factor authentication solutions, which helped me understand the importance of IAM in safeguarding organisational assets,” Erin explains. “This experience bridged the gap between theory and practice and confirmed that cybersecurity was the right career path for me.”
Today, Erin continues to build on that foundation in her role as a Technology Risk Consulting Vacationer, where each day brings new lessons and challenges. The transition from university to industry has been both exciting and demanding.
“One of the most challenging aspects of my current role is managing the steep learning curve that comes with transitioning from university to the workplace,” she says. “While my academic background provides a solid foundation, the cybersecurity landscape is vast and constantly evolving. Understanding how theoretical knowledge translates into practical, business-focused solutions has been both challenging and rewarding.”
Rather than feeling overwhelmed, Erin has embraced the challenge with determination. She has taken a proactive approach, seeking mentorship, asking questions, and investing in her professional development.
“To overcome these challenges, I take a proactive approach by building relationships with experienced colleagues who are willing to share their insights and mentor me,” she says. “I make it a point to ask questions during projects and seek feedback to
improve my understanding. Additionally, I dedicate time outside of work to strengthen my technical knowledge by studying for certifications such as CompTIA Security+. Combining on-the-job learning, mentorship, and self-study has been instrumental in bridging knowledge gaps and building confidence in my role.”
Unlike many who enter cybersecurity with a clearly defined destination, Erin’s path has unfolded organically. Her openness to exploration has allowed her to discover strengths and interests naturally.
“When I began my journey, I didn’t have a clear vision of a specific role I wanted,” she reflects. “I simply wanted to explore as many areas as possible to understand what I enjoyed and what I didn’t. Cybersecurity is such a broad field, encompassing everything from penetration testing and incident response to governance, risk, and compliance.”
Exposure to different domains, from Identity and Access Management to technology risk consulting, has allowed her to build a well-rounded perspective.
“My path has unfolded organically, with exposure to various domains happening naturally rather than through a rigid plan,” she explains. “These experiences have helped me discover my strengths and interests, and they have shaped my focus on areas that align with both my technical skills and my passion for problem-solving.”
“Understanding how theoretical knowledge translates into practical, business-focused solutions has been both challenging and rewarding.”
Beyond technical experience, Erin’s leadership role as president of the UTS Tech Society has played a transformative part in her development. Through leading the society, she has learned the importance of community, collaboration, and creating opportunities not only for herself but for others.
“Leading this society has given me the opportunity to engage with students, understand their aspirations, and create initiatives that provide them with industry exposure and learning opportunities,” she says.
“Networking with sponsors and collaborating on events with organisations such as ACS, PwC, and
Macquarie has provided me with insights into the cybersecurity landscape and helped me build relationships with industry professionals.”
These experiences reinforced a lesson that Erin believes is essential for anyone entering cybersecurity. Success is built not only on technical ability, but on relationships, curiosity, and initiative.
If she could offer advice to her younger self, it would be simple but powerful.
“I would tell my high school self to be proactive in seeking opportunities beyond the classroom,” she says. “While academic performance is important, getting involved in co-curricular activities and networking early can make a significant difference.”
She also emphasises the importance of confidence and curiosity.
“Don’t be afraid to ask questions, even if they seem basic, and challenge yourself by taking on tasks that push you out of your comfort zone,” Erin says. “Growth in cybersecurity comes from continuous learning and embracing challenges, so developing these habits early would set a strong foundation for future success.”
That commitment to growth continues to shape her future plans. Erin is currently pursuing industry certifications to strengthen her technical foundation and deepen her understanding of cybersecurity and cloud environments.
“I plan to pursue certifications such as CompTIA Security+ and Microsoft SC-900,” she explains. “These certifications not only validate technical knowledge but also demonstrate a commitment to professional development. They provide a strong foundation for understanding cybersecurity principles and can serve as a stepping stone to more advanced certifications in the future.”
Despite being early in her career, Erin already finds deep satisfaction in the work itself. For her, cybersecurity is not just intellectually stimulating, but meaningful.
“At this stage, I find the greatest satisfaction in learning and contributing to a variety of tasks,” she says. “Every project presents an opportunity to gain new insights and develop practical skills.”
More importantly, she recognises the real-world impact of the work she is part of.
“I also find fulfillment in seeing the broader impact of cybersecurity work,” Erin adds. “Whether it’s helping clients strengthen their security posture or contributing to risk assessments that protect sensitive data, knowing that our efforts make a difference to organisations and society is incredibly motivating.”
To stay ahead in such a fast-moving field, Erin remains committed to continuous learning. She keeps informed through industry news, professional connections, and ongoing engagement with the cybersecurity community.
“Cybersecurity is a fast-moving field, so staying informed is essential,” she says. “Networking is another key strategy. Engaging with industry professionals helps me learn about their roles, the challenges they encounter, and their career progression. These interactions provide practical insights that complement my technical learning.
Erin Blanchard’s journey reflects the evolving nature of cybersecurity itself, dynamic, complex, and full of opportunity for those willing to explore. Guided by curiosity, strengthened through experience, and driven by purpose, she is steadily building a career defined not just by technical expertise, but by resilience, leadership, and a genuine commitment to protecting the systems that shape the modern world.
www.linkedin.com/in/erin-blanchard-290aab2a5
For the past four years , Source2Create has proudly delivered Women in Security Magazine to the industry free of charge , championing diversity, inclusion, and the incredible contributions of women in cybersecurity. As we continue to grow, we now need partners to help us sustain and expand this vital platform.
By supporting this package, you’re not just backing us—you’re investing in the magazine, its community, and the future of women in security. To ensure we can keep delivering this high-value publication, we’re introducing a nominal fee for $900 Ex GST, an exceptional package that provides extensive coverage and visibility.




Cleo Faul Consultant (KPMG)
Cleo Faul’s career in cybersecurity wasn’t mapped out in high school or carefully plotted from childhood. It unfolded gradually, shaped by curiosity, courage, and a willingness to begin again.
“My journey into technology wasn’t something I had planned from the start; it evolved,” she reflects.
After finishing school, Cleo stepped into a world far removed from IT audit and tech risk. She began her career as a personal trainer, drawn to the people’s focused nature of the role. “I loved the people’s side of that work,” she says. But over time, curiosity stirred. She began to wonder what else was possible, what other paths might exist beyond the gym floor.
That curiosity led her back to study, where she commenced a Commerce degree majoring in Information Systems. It was there that technology shifted from an abstract concept to a genuine interest. “That’s where my interest in technology really began to grow,” she explains.
Doors continued to open. Cleo joined a women’s fellowship program at Startmate, an experience that immersed her in the startup ecosystem for the first time. Surrounded by founders, builders, and creative problem-solvers, she saw firsthand how technology could be harnessed to solve meaningful, realworld problems.
“Being surrounded by founders, builders, and problemsolvers showed me how technology could be used creatively to solve real problems,” she says. “I’m still learning every day and I’m excited about building a long-term career in this space.”
In the early stages of her professional journey, Cleo made a defining choice: she said yes to opportunities that didn’t necessarily follow a traditional or linear path. While studying, she worked as a marketing intern at a startup before moving into partnerships and account management roles, where she spent three years honing her commercial and communication skills.
“Balancing full-time work while studying was a hustle,” she admits. “But it taught me how to learn quickly, take responsibility, and adapt in fastmoving environments.”
Eventually, Cleo felt the pull toward the corporate world. Not as a replacement for the startup experience she valued, but as a way to build a strong, transferable foundation. “I was still young and wanted to build strong, transferable skills,” she explains. “Applying to KPMG felt like the right next step.”
Joining Tech Risk Consulting allowed her to combine her interests in technology, business, and continuous learning. Today, she works within IT Asset Management, helping organisations understand whether their software and hardware assets are being used appropriately and effectively.
“For someone non-technical, I like to explain it like this,” she says with a smile. “Imagine a company has purchased 100 Netflix subscriptions. My role is to help check whether they’re actually using 100 subscriptions, not 80, and not 110. I do the same thing, but with software and hardware assets.”
No two days look the same, and that variety is something she relishes. But stepping into a highly technical environment as a graduate has not been without its challenges.
“The most challenging part of my current role is balancing the steep learning curve with the pressure I sometimes place on myself to perform,” she shares. “There is a lot to absorb new systems, new terminology, and new ways of thinking.”
Her approach has been deliberate and grounded. “I’m overcoming this by reminding myself that learning is the job right now. I focus on asking questions early, taking notes, and being proactive about understanding the ‘why’ behind what I’m doing. Accepting that growth takes time has helped me manage both the technical challenge and the mental load that comes with it.”
Uncertainty, she admits, has been a constant companion. Moving between industries, starting over as a graduate, and navigating imposter syndrome all tested her confidence.
“There were times I questioned whether I was ‘technical enough’ or if I truly belonged,” she says candidly. “What helped was reframing those doubts. Instead of seeing them as a weakness, I started to view them as a sign that I was learning and stretching myself.”
Leaning into support networks and allowing herself to be open about what she didn’t know proved transformative. “No one expects you to know everything, especially early in your career,” she says. “Once I embraced speaking up and asking for help, everything changed. People genuinely want
to help. That mindset unlocked my confidence and accelerated my growth. Once that clicked, I felt like I could really fly.”
For Cleo, one of the most fulfilling aspects of her current role is the sheer volume of knowledge she is absorbing. “The biggest source of fulfillment for me right now is learning,” she says. “I’m surrounded by incredibly talented people, and I know that the knowledge I’m building is foundational. It’s setting me up not just for this role, but for my entire career.”
She approaches each day with what she calls a “be a sponge” mindset absorbing insights, connecting dots, and gradually building confidence through competence.
If she could speak to her high school self, her advice would be simple yet powerful. “You don’t have to fit a mould to succeed,” she says. “You don’t need to have everything figured out, and you don’t need to become someone else to belong in a professional environment. Being yourself is enough. If you show up authentically, stay curious, and are willing to learn, you’ll find your place even if the path there isn’t straight.”
Her message to others transitioning into cybersecurity from different industries echoes the same theme. “Your past experiences are not a disadvantage, they’re an asset,” she says. “Coming from different industries gives you perspective, adaptability, and people skills that are incredibly valuable, especially in technology and consulting. Don’t underestimate what you already bring to the table.”
Cleo Faul’s journey is not one of rigid planning or linear progression. It is a story of evolution, humility, and bravery, to start over, to ask questions, and to grow out loud. In an industry that often prizes technical perfection, her story is a reminder that sometimes the most powerful skill of all is simply being brave enough to begin.
www.linkedin.com/in/cleo-faul-05146a1a0
by Abigail Swabey
Practical resources for career changers entering cybersecurity from non-traditional backgrounds. These checklists, guides and advice columns are tailored with a special nod to veterans, dentists, nurses and other professionals leveraging transferable skills.

USE THIS TWO-MINUTE SELF-ASSESSMENT TO IDENTIFY YOUR CYBER-READY STRENGTHS. SCORE YOURSELF 1-5 (1=NEVER, 5=EXPERT) THEN TOTAL EACH CATEGORY.
Technical foundations
• I understand systems, networks or troubleshooting (IT, engineering, military comms)
• I work with data/tools/software daily (dentistry records, nursing devices, project management)
• I spot patterns/anomalies in information (diagnostics, risk analysis, logistics)
• Total: ___/15
Risk and analytical thinking
• I assess threats/prioritise risks (military ops, healthcare triage, compliance audits)
• I investigate root causes (medical diagnosis, incident reports, HR investigations)
• I make decisions with incomplete information (emergency response, project deadlines)
• Total: ___/15
Leadership and communication
• I lead teams under pressure (military, project management, patient care coordination)
• I explain complex ideas simply (stakeholder briefings, patient education)
• I train/mentor others (military instruction, staff training, workshops)
• Total: ___/15
Process and operations
• I design/improve workflows (SOPs, compliance processes, clinical protocols)
• I manage crises/incidents (emergency protocols, supply chain disruptions)
• I document thoroughly (reports, audits, patient records)
• Total: ___/15
SCORING GUIDE:
• 40-50: Cyber-ready – Target analyst/manager roles
• 30-39: Strong foundation – Add 1-2 certifications (Security+, CySA+)
• 20-29: Great start – Begin with SOC/helpdesk pathways
• <20: Build basics – Free CompTIA IT Fundamentals first
1. Translate, don't list
Instead of "Managed dental practice records," say: "Managed sensitive patient data with HIPAA-equivalent chain-of-custody protocols, ready for IAM/log management roles."
Military to Cyber Examples: Military Experience Cyber Translation Target Role
Risk assessment patrols Threat modelling Threat intel analyst
Logistics under pressure Incident response SOC analyst
Briefings to command Stakeholder reporting GRC specialist
Healthcare to Cyber Examples: Healthcare Experience Cyber Translation Target Role
Patient triage Incident prioritisation IR manager
Device sterilisation protocols System hardening Security engineer
Post-mortem reviews Root cause analysis Forensics analyst
2. Resume keywords by role:
• SOC analyst: monitoring, triage, anomalies, shift work, detail oriented.
• GRC: compliance, audit, policy, risk frameworks, reporting.
• Awareness training: communication, adult learning, behaviour change, workshops.
From Sarah Mitchell, Veteran CISO (ex-army intelligence): "Veterans: stop apologising for 'not being technical’. Your OPSEC discipline beats 90 percent of entry-level analysts. Get Security+ (government funds it), then volunteer for your company's security committee. Six months later, you're the 'known quantity' for the SOC role. Don't chase certs endlessly, get hands-on via bug bounties or home labs first."
From Dr Lisa Chen, ex-dentist to cloud security engineer: "Healthcare pros: your HIPAA/GDPR experience equals instant GRC credibility. Dental records? That's IAM and data classification. Patient breach response? That's IR planning. Pitch yourself as 'regulated industry risk expert transitioning to cyber.' Start with Coursera's Google Cybersecurity Certificate. It maps perfectly to your diagnostic mindset."
From Karen Patel, HR director to Human risk manager: "HR/training backgrounds: you're perfect for security awareness and insider threat roles (80 percent of breaches are human). Your investigations equal digital forensics basics. Employee training equals phishing simulations. Lead with 'I reduced workplace incidents 40 percent through behavioural interventions' – that's behavioural security in corporate language."
• Week 1: Complete checklist; Identify top two skill categories.
• Week 2: Free intro course (Google Cybersecurity Cert or TryHackMe).
• Week 3: Tailor resume + LinkedIn; Apply to five 'skills-based' job ads.
• Week 4: Network (VetSec, WiCyS, RSL Cyber Academy events).
• Month 2: Security+ or equivalent; Entry role applications.
Pro Tip: Target skills-based hiring companies (Google, IBM, Deloitte). They explicitly welcome career changers. Use your network; every security leader was once a beginner!


Craig is an experienced cyber security professional with various qualifications including two master’s degrees. He is the Head Unicorn (co-founder and director) of Cyber Unicorns, in which he acts as a vCISO to clients such as Baidam Solutions, Wesley Mission, PCYC, Hungry Jacks and Ipswich City Council. He was CTO (Chief Technology Officer) for Baidam Solutions between January 2022 to June 2023, where he led the technical services team, helping to build out the internal services capability for Baidam. Craig was QLD chair for AISA for two years until he was appointed to the national board of directors in December 2022.
Like many who have been in this industry for a while, I often get asked: “How did you get into the industry?” or “How did you get to where you are?”
You can learn things from my journey, I certainly have. And you can also learn things from others’ journeys, but I want to make something very clear: DO NOT FOLLOW MY PATH.
Now, before you all say; “Why, do you think we are not good enough to do what you did, or what they did?”
That’s not why I am telling you not to follow my path.
Before we dive into that, let’s first talk about my path. I started out with a traineeship in a small IT computer shop. I earned my stripes and learnt a lot before making a move to the city (Gold Coast) because I felt I could go no further where I was. That was 100 percent true. I still have fond memories of my time working in that shop. I even went back for a time to manage it for the owner.
About 10 years later in my journey, I was still in IT, but in senior roles. I decided I wanted to be a CIO in a big company. That one I got wrong. I decided I needed to have a degree to give me the best shot. So I went back to school. I joined the IT master’s program at Charles Sturt University. One of my first units was an elective on incident response. I followed that with a forensics unit.
Can you guess what happened next? I threw my CIO dream out of the window. I loved forensics. I loved Incident response. I went down a rabbit hole from which I have never returned. I have now been in the ICT and cyber worlds for more than 20 years. I ended
up doing two master’s degrees with CSU (that’s a topic for another article, maybe).
I never chose the blue team or the red team, always floating between them. I have published more than 500 articles in my career, given hundreds of presentations/talks and, as I write this, have just finished off the first draft of my seventh book, Glimmer.
I cofounded Cyber Unicorns with my wife Melissa because we wanted to make a real difference educating everyday people; kids, mums and dads, seniors and so many SMBs out there that need the help. I was sick of talking about how someone needed to do something, and decided I should be that someone.
I am the deputy chairman of the board for AISA (Australian Information Security Association) while also a fractional CISO for Wesley Mission, PCYC, RespectX and some others. In 2025 I won two industry awards and four international awards for my literary works.
In my mind my career is still just warming up, but if you look at it, there were many forks in the road. I have parallel journeys running simultaneously, some progressing faster than others. I am not singularly focused. My career looks like a very artistic drawing from a two year old (lots of squiggly lines). As a parent, you would be amazed, but everyone else would go: “mmm, yeah, very cool scribble. Well done.”
We all have our ups and downs. If you looked at five different CISOs or penetration testers, each
Craig is a published author with three different book series – ‘A Hacker I Am’ cyber education series, ‘Foresight’ is his Cyberpunk/hacker fantasy novel series and then there is ‘The Shadow World’, a co-authored kids cyber education book. He is a freelance cyber security journalist and is a regular columnist with the Women in Security Magazine, as well as a freelance contributor for Cyber Today, Top Cyber News, SecureGov, Careers with STEM and Cyber Australia magazines.

journey would be very different. Sometimes there are similarities in how people achieve similar positions, but you can’t use these to create a clear road map.
Do you get what I am trying to tell you? I want you to understand that you can’t follow your role model’s career path to reach your goal. Firstly, you are not them. They may be amazing. They may have an awesome career and definitely be worth watching to see what might work for you.

If you think I have done well and you want to be where I am, that’s amazing. BUT you are the architect of your life and your career. That means you need to think about what you want, what your true end goal is. Don’t be an idiot and come up with something that is not realistic (Maybe you could still achieve that, but let’s be real).
I want you to visualise that goal. Once you know, I want you to look at the skills and experience you will need to be that person. Real skills. Real qualifications Those that are non-negotiable.
Now, figure out how the hell you are going to get those experiences, skills and qualifications. Whatever you don’t have, make a plan. Don’t take no for an answer. Figure out your path.
That is the part you need to stay firm on; this is YOUR path. You should still listen to people’s opinions, take on their advice, but don’t blindly follow someone else’s ideals or expectations of you.
We are all the ‘architects of our futures’. So get out there, grab your life and your career by the horns, make some mistakes, learn some lessons. And don’t be afraid to go against the grain if you know that doing so is right for you.
www.cyberunicorns.com.au
www.linkedin.com/in/craig-ford-cybersecurity
www.facebook.com/CyberUnicorns
www.instagram.com/cyberunicorns.com.au

by Adriana Jones, Engineer, Cybersecurity Advocate and founder of The Innocent Souls Project (TISP)
Before transitioning into cybersecurity I worked in construction. My first degree was in civil engineering and, during university, I learnt something that has stayed with me ever since: no structure is ever designed from the top down.
Every building begins with its foundations. Engineers calculate load, stress and future capacity before anything rises above ground. A structure must support not only its current weight, but also growth, change and unforeseen external forces. When designed well, it remains stable even when pressure is applied from the outside.
This way of thinking translates naturally to child protection in a digital world. As technology becomes more deeply embedded in children’s lives, protection can no longer rely on isolated controls or reactive measures. It requires a structural approach, one that is intentional, layered and resilient. In this context, effective child protection rests on three interconnected pillars: cybersecurity, eSafety and physical data safety.
Cybersecurity provides the structural foundation for child protection in digital environments. At its
core, cybersecurity is about designing systems that anticipate failure and limit harm when it occurs. This principle is especially critical where children are involved.
Children do not meaningfully consent to data collection. They cannot assess long-term risk, understand how their information may be reused or anticipate how digital records created today could affect them years into the future. Yet, many systems that interact with children continue to collect, retain and correlate data far beyond what is necessary for functionality or safety.
From a cybersecurity perspective this creates avoidable risk. Every additional data point increases the potential impact of a breach. Every retained identifier extends the lifespan of harm. Designing secure systems for children therefore requires a shift in mindset; from data accumulation to data restraint.
Data minimisation is not a limitation; it is a security control. When systems are designed to collect only what is essential, store it for limited periods and tightly control access, they reduce exposure by design rather than by policy. This approach aligns security objectives with ethical responsibility, ensuring that protection does not depend on constant oversight or perfect compliance.
For cybersecurity professionals this represents an opportunity to apply mature security principles, least privilege, containment and resilience to one of the most sensitive user groups. When cybersecurity is embedded early and thoughtfully it quietly protects children without requiring them to understand risks they were never meant to carry.
eSafety complements cybersecurity by focusing on the human experience of digital systems. Where cybersecurity strengthens infrastructure, eSafety supports safe participation, understanding and confidence in digital spaces.
At its best eSafety is proactive and empowering. It equips children, families and communities with the awareness needed to navigate online interaction, communication and boundaries in a healthy way. Rather than limiting engagement, it supports informed engagement, helping children benefit from technology while recognising how to respond to challenges that may arise.
Importantly, eSafety does not operate in isolation. Its effectiveness increases when it is aligned with secure system design. When digital environments are built with safety in mind, eSafety education reinforces those protections rather than compensating for their absence.
From a cybersecurity standpoint, eSafety strengthens the human layer of defence. It reduces the likelihood of manipulation, misuse and unintentional exposure; not by shifting responsibility onto children, but by fostering digital environments where safety is understandable and supported.


The third pillar connects digital security to the physical world. Children’s data is not confined to online platforms; it is also held by schools, childcare centres, healthcare providers and community organisations. These environments collect highly sensitive information as part of care and education making them critical components of the child protection ecosystem.
Protecting this data is inseparable from protecting children themselves. Strong cybersecurity practices within physical institutions help ensure information collected for wellbeing does not become a source of unintended risk. Secure systems, sound governance and thoughtful data handling reduce the likelihood that personal details, images or routines can be misused.
When physical environments and digital systems are aligned, data protection becomes an extension of physical safety. Cybersecurity maturity in these settings supports trust, continuity of care and longterm protection.
In engineering resilience is achieved by designing for load, not appearances. Child protection benefits from the same discipline. Cybersecurity, eSafety and physical data safety are most effective when they are treated as structural elements, reinforcing one another rather than operating independently.
This integrated approach does not constitute a finished solution. Technology evolves, threats adapt and systems must continue to improve. But when protection is structural, progress builds on a stable foundation rather than patching recurring weaknesses.
For the cybersecurity community this represents both a responsibility and an opportunity. By applying principles of secure design, data minimisation and long-term risk reduction we can help create digital environments that support children safely as technology continues to advance.
Strong structures are never static. Stability is achieved not through rigidity but through the ability to absorb pressure and adapt to change.
These three pillars cybersecurity, eSafety and physical-data safety are designed to endure, adapt and support what the future demands. Child protection demands the same level of critical thinking and creative system design.
au.linkedin.com/company/tisp-the-innocent-souls-project
www.instagram.com/tisp_project
theinnocentsoulsproject.com.au

JO STEWART-RATTRAY
by Jo Stewart-Rattray , Oceania Ambassador, ISACA
If you look closely at today’s privacy and security teams one thing becomes clear very quickly; many professionals didn’t get where they are by following a single, straight career path.
ISACA’s 2026 State of Privacy survey shows more than half of organisations globally now report that at least half of their privacy teams’ members transitioned from completely different careers. Only a quarter say their teams largely started, and stayed, in privacy. In other words, the profession is increasingly being built by people who have reinvented themselves.
Former lawyers are now navigating governance frameworks. Finance professionals are stepping into risk and compliance. Teachers are leading awareness programs. Military veterans are applying crisis management and threat assessment skills to cyber operations.
I’ve seen firsthand how professionals from policing and counterterrorism bring exceptional investigative instincts into cyber threat hunting and remediation roles. In my own journey my shift from CIO to CISO was less about changing direction and more about building on operational experience to lead security from a broader risk perspective.
These non-linear journeys are no longer unusual but are increasingly commonplace in today’s security workforce. At the same time, the pressure on teams continues to rise. Median privacy team sizes globally have shrunk from eight to just five people, while almost two-thirds of professionals in Oceania say their roles are more stressful than five years ago. Budgets are tightening, skills gaps are growing and expectations keep climbing.

Yet, within this challenge lies an opportunity. Rather than relying solely
on traditional pipelines many organisations are now actively growing talent from within. Almost half of surveyed organisations are training staff from other parts of the business who show interest in privacy and security roles.
This shift recognises what many in the profession already know; that great security professionals aren’t defined only by where they started, but by how willing they are to learn, adapt and build new skills.
Programs like ISACA’s SheLeadsTech initiative reflect this reality, helping professionals build confidence, access mentorships and develop the technical and leadership skills needed to succeed in new roles. For many women, particularly those undergoing career transitions, having community support alongside structured learning can be the difference between self-doubt and self-belief.
To me, transformation is about helping people understand, and confidently communicate, the strengths they already bring. Practical tools can play a big role here. Skills mapping exercises that show how competencies such as risk management, communication, leadership, analytical thinking and crisis response translate across industries can help career changers recognise their value.
Simple checklists for assessing transferable skills from project management to stakeholder engagement allow professionals to identify gaps while also appreciating existing strengths. Being able to clearly articulate how past roles prepared you for security challenges can open doors.
For organisations, this means rethinking traditional hiring models. Rather than filtering candidates purely by linear experience or specific job titles, future-ready workplaces are learning to spot potential, adaptability and willingness to upskill. And culture plays a critical role.
Supportive environments that encourage continuous learning, offer mentorship and view career pivots positively are better equipped to build resilient
teams. They also reduce burnout by sharing knowledge across diverse backgrounds and creating stronger collaboration.
The ISACA survey highlights what happens when culture and training fall short: more than half of respondents cite lack of training as a leading cause of privacy failures. In a profession where technology changes constantly, learning can’t be a one-off event. It needs to be embedded into everyday work life.
This is where structured development programs and certifications, accessible learning resources and communities of practice become essential. They help professionals stay current while building confidence.
Ultimately, the future of security won’t be shaped by one type of professional following one narrow path. It will be built by people willing to pivot, upskill, challenge themselves and bring diverse experiences. And by embracing transferable skills, supporting continuous learning and building cultures that welcome non-linear career paths, the security sector can close skills gaps to create a stronger, more adaptable profession.
Jo has over 25 years’ experience in the security sector. She consults in risk and technology issues with a particular emphasis on governance and cybersecurity as a director with BRM Advisory. Jo is the Oceania Ambassador for global IT professional association, ISACA, and an ISACA Hall of Fame inductee. Jo is the former Vice President, Communities of the Australian Computer Society and Ambassador of the National Rural Women’s Coalition. She regularly provides strategic advice and consulting to the banking and finance, utilities, healthcare, tertiary education, retail and government sectors.
www.linkedin.com/in/jo-stewart-rattray-gaicd-4991a12

by Lisa Ventura MBE FCIIS, Chief Executive and Founder, Unity Group Solutions Limited/AI and Cyber Security Association
For years we’ve told employees they’re the ‘human firewall’. We’ve shamed them when they click phishing links, threatened them with disciplinary action and designed training that treats them as the weakest link in our security chain. Then, we wonder why our security awareness programs fail to create lasting behavioural change.
What if the problem isn’t the humans, but how we’re trying to teach them?
After managing cybersecurity across eight countries and 700,000+ customers, I’ve learnt something crucial: trauma-informed security awareness training doesn’t just feel better. It works better. Measurably, significantly better.
THE HIDDEN COST OF SHAMEBASED TRAINING
Traditional security awareness training operates on a simple premise: scare people enough and they’ll change their behaviour. Show them breach consequences. Publicly name phishing simulation
failures. Create an atmosphere where one wrong click feels career-limiting.
This approach backfires. When people feel ashamed or blamed, they become defensive. They hide mistakes rather than report them. They disengage from training that makes them feel inadequate. The very shame we inflict to motivate change becomes the barrier preventing it.
I’ve watched security teams frustrated that ‘users just don’t get it’, whilst employees dread training that makes them feel stupid. It creates a cycle of blame that benefits no one and certainly doesn’t make us more secure.
WHAT DOES TRAUMA-INFORMED ACTUALLY MEAN?
Trauma-informed approaches recognise that people’s past experiences shape how they respond to new situations. In security training this means understanding that not everyone starts from the same place.
Some employees have learning differences that make certain materials inaccessible. Others have experienced workplace trauma that makes public ‘naming and shaming’ genuinely harmful. Many simply lack the technical background to intuitively understand concepts security professionals take for granted.
A trauma-informed approach asks: how do we create psychological safety whilst still achieving our security objectives?
The principles are straightforward:
• Create safety first.
• Build trust through transparency.
• Offer choice and collaboration.
• Recognise that people are doing their best with available resources. Design training that empowers rather than diminishes.
This is a live case study of redesigning a cybersecurity awareness training program to make it trauma informed. The first step was to move from a deficit model to a strengths-based approach. Instead of focusing on what employees were doing wrong, we highlighted what they were already doing right. We celebrated the person who paused before clicking. We recognised teams who reported suspicious emails.
We also completely redesigned our phishing simulations. Rather than creating emails designed to catch people out, we created scenarios that taught recognition skills. When someone clicked, instead of a shame-inducing ‘you failed’ message, they received immediate, constructive feedback explaining what to look for next time. No naming individuals. No league tables of failure. Just learning.
The accessibility piece was crucial. We provided training in multiple formats, recognising that neurodivergent employees might process information differently. We provided video transcripts, audio descriptions, clear, jargon-free language and options to access content at different paces.
We moved away from annual ‘compliance tick-box’ training to ongoing, bite-sized micro/nano learning integrated into the workflow. Security awareness became a conversation, not a lecture.
The sceptics always ask: does it actually work?
In one particularly striking example, we saw a reduction of up to 90 percent in phish-prone behaviours across certain user groups. Not through fear. Not through shame. Through respect, understanding and well-designed training that met people where they were.
Crucially, incident reporting increased dramatically. When employees don’t fear punishment they report suspicious activity. This is perhaps the most valuable outcome of all, because security is fundamentally about information flow. We need people to tell us when something seems wrong, not hide it because they’re afraid of looking foolish.
Employee feedback shifted from ‘this is painful’ to ‘this actually helped me protect my personal accounts too’. When training respects people’s intelligence and acknowledges their challenges, engagement follows.

The business case writes itself. We saw better security outcomes, higher engagement, improved reporting, reduced anxiety and a security culture built on empowerment rather than fear. Plus, traumainformed approaches naturally align with broader diversity, equity and inclusion initiatives, creating consistency across organisational values.
Perhaps the most significant shift is philosophical. Trauma-informed security awareness forces us to examine why we do what we do. Are we running phishing simulations because they genuinely improve security, or because everyone else does them? Are we creating training that serves compliance requirements but doesn’t actually change behaviour?
I’ve spent hours in conversations with employees about what genuinely helps them spot threats. The answers are rarely what security teams expect. Sometimes it’s about having time to think rather than rushing between tasks. Sometimes it’s about clearer communication from IT about what normal looks like. Often, it’s about feeling trusted and respected rather than monitored and blamed.
This doesn’t mean lowering standards or avoiding difficult conversations. It means having those conversations from a place of partnership rather than punishment.
Implementing trauma-informed security awareness requires security leaders to examine their own assumptions about human behaviour. It requires moving beyond the ‘human firewall’ metaphor that positions people as security infrastructure rather than valued colleagues.
Start small. Review your next phishing simulation through a trauma-informed lens. Ask: does this teach or does it trick? Does it empower or diminish? Would I want to receive this?
Engage employees in designing training that works for them. Create feedback loops. Measure not just
click rates but reporting rates, engagement rates and how people feel about security.
Most importantly, recognise that the humans in your organisation aren’t your security problem. They’re your security solution, if you can move beyond fearbased approaches that have demonstrably failed.
The future of security awareness isn’t about building better human firewalls. It’s about creating psychologically safe environments where people can learn, grow and actively participate in keeping everyone secure. That’s not just better ethics. It’s better security.
www.lisaventura.co.uk @cybergeekgirl
www.linkedin.com/in/lisasventura/
www.facebook.com/lisasventurauk
www.instagram.com/lsventurauk

bsky.app/profile/cybergeekgirl.bsky.social
You can find examples of the talks has she done previously and of interviews, panel discussions and moderating/chairing events on her YouTube channel here https://www.youtube.com/@CyberSecurityLisa/
Lisa Ventura MBE FCIIS is the chief executive and founder of the AI and Cyber Security Association (AICSA). She is the author of ‘Artificial Intelligence in Cybersecurity’ (published by Kogan Page) due for release in April 2026 and advocates for neuroinclusive, trauma-informed approaches to security awareness training.

SIMON CARABETTA
By Simon Carabetta, National Cyber Security Training Advisor
When I first made the leap from moderately OK high school teacher to moderately OK cybersecurity awareness trainer back in 2019 I knew that executing the jump would require a level of ‘fake it till you make it’ energy. Fortunately, I discovered quite early on that I was more than moderately OK at what I was doing and, very much unlike the last three years of my teaching days, actually enjoyed it. I got to engage with people on a level that I had not done previously. I was an advisor, someone who had acquired a depth of knowledge in a very short space of time and was willing to impart that knowledge at every turn.
Nowadays I look back fondly on that time as a moment when cybersecurity awareness, as we know it today, was still in its infancy; when companies weren’t yet making investments in phishing simulations, and when phishing simulation vendors were not flooding the market with the exact same product wrapped in a different package.
It was also a time when people with cybersecurity qualifications were much rarer, and not every single person was enrolling in a master’s course. It was a time when there were jobs in cybersecurity that did not require 10 years’ experience using tools that had
existed for only three, or a list of certifications that forced candidates to sell a kidney on the dark web to the highest bidder, and maybe part of their liver as well.
Pre COVID, before all the crazies really came out of the proverbial woodwork (you know the ones I’m talking about), you could speak to the virtues of advocating for diversity and equity in the industry at a mid-week networking event without harassment by certain less obvious crazies a (you know the ones I’m talking about).
This editorial isn’t designed (intentionally anyway) to upset any of those particular people. However, if you make it to the end instead of deciding to browse Reddit (I wouldn’t blame you), hopefully, it will give you some food for thought. What I will take aim at today is the complete lack of regard that certain educational institutions and workplaces have for cybersecurity students, and the subsequent flow-on effect a decade-long cash cow is having on our job market, our future workforce and, finally, the security of Australian businesses, public sector agencies and individuals.
I will start with one segment of education that is very rarely spoken of in a negative light, at least in public: Australian universities offering cybersecurity qualifications. Yes, I realise many people who read Women in Security Magazine work either as academic or non-academic staff for universities (heck I used to be based at one), but sometimes a painful pill is the best medicine, even for the post-COVID crazies I mentioned earlier.
The unfortunate mess we find ourselves in today can be described as follows. There are far too many current students and graduates, too few jobs, far too little investment into cybersecurity, insufficient understanding of how money should be invested into cybersecurity and a lack of understanding of the why of cybersecurity.
Let’s go back to the beginning.
When I first commenced my graduate diploma in education I was unaware that Western Australia was about to be hit by a teacher surplus. A surplus, meaning too many teachers. Yet the university I was studying at, which shall remain nameless unless you check out my LinkedIn profile, was still taking on as many qualified students as it could. Why? Well, simply because education was the cash cow for this particular university. They did not offer some of the more attractive degrees such as medicine, law and economics that other universities offered. So, for a communications graduate struggling to demonstrate value with his background in communications and education, the prospect of becoming a fully qualified teacher in the short space of 12 months was very attractive.
Fast forward 12 months. I barely managed to get my first job at a high school, but I was one of the lucky ones.
My point here is: the supply far outweighed the demand, meaning some of those enrolling in education courses should have gone to another university and enrolled in economics, but I digress. This oversupply created a massive issue—not just for my university, but for the other four universities in WA offering education—by producing graduates who could not find employment.
I swear, if I fulfilled my life-long dream of forming a jazz funk band I’d name it thus. However, this is the situation where many former cybersecurity students find themselves in right now. They have little or no experience. Their skills are misaligned with industry standards. They don’t get the support they require when looking for work post-graduation. Yes, there are some universities that do offer internships (which are harder to fill than people realise) and there are many that offer career counselling, but beyond ticking a box to say they’re helping, there really isn’t anything meaningful going on.
We currently have, across Australia, a surplus of cybersecurity graduates and too few cybersecurity jobs. We have people spending $50,000 plus on a master’s level qualification in the hope they can change careers, without much chance of doing so. And, yes, while I understand that it is everybody’s individual choice to take on specific study,

I have also found that marketing by universities is unchecked and unfair, particularly for international students who find it tougher to secure a job than do citizen students.
Student visas guarantee you study in a certain country, but they’ll never guarantee you a job. If anything, it will be tougher for you to secure work, particularly in an industry where 10-30 percent of jobs are advertised as requiring a clearance. That’s advertised , by the way. Many jobs at managed security service providers or consultancies will require candidates to be vetted during the interview process for positions that are not advertised as such. This means the real percentage is higher when you take into account both the public sector (where clearances are almost mandatory) and the private sector.
There is no one solution to this problem. What needs to happen first is for all universities to agree on one thing: cut the international student intake and increase entrance requirements. What needs to happen next is a complete overhaul of current cybersecurity courses to bring the skills and knowledge taught into line with industry standards.
Internships need to be offered to build stronger, sustainable industry partnerships. The federal and state governments need to realise the severity of the situation, step in and create traineeships for cybersecurity students that are accessible to school leavers, TAFE and registered training organisation students and, of course, university students.
There needs to be an overhaul of the ways in which hiring managers and teams source candidates, advertise their jobs and build requirements. Managers and teams should be open to on-the-job training for entry-level graduates who don’t yet have industry experience, without requiring a ‘hit the ground running’ approach.
Finally, can we just agree to stop the whole ‘professionalisation’ debate that’s been going on for the past few years? Both sides’ arguments are wearing thin, and I’m surely not the only one who thinks the arguments for and against aren’t addressing the problems that currently exist.
www.linkedin.com/in/simoncarabetta




DEARNE MCWHIRTER
by Dearne McWhirter, Associate Director (KPMG)
BUILDING RESILIENCE IN THE AGE OF AI AND CLOUD
Cyber resilience is no longer optional, it’s a strategic imperative. In an era defined by AI-driven innovation and cloud modernisation, organisations face unprecedented risks and regulatory scrutiny. This article explores how continuous design principles, aligned with CPS 230, CPS 234, CPG 235, Privacy, SOCI and global standards, can help organisations achieve resilience at scale. We focus on why resilience must be embedded into architecture, how technology trends reshape risk and what maturity looks like in practice.
The convergence of AI, cloud computing and regulatory evolution has transformed the cybersecurity landscape. Recent mandates such as APRA’s CPS 230 and CPS 234, coupled with global frameworks like NIST CSF v2.0 and ISO 27001, demand a proactive approach to resilience. Traditional ‘point-in-time’ compliance is no longer sufficient;
organisations must adopt continuous design to withstand disruption and maintain trust.
Cyber threats are escalating in complexity and velocity. Legacy resilience models often treat risk as static, focusing on perimeter defence and periodic audits. These approaches fail in dynamic environments where cloud workloads scale instantly, where AI models introduce new attack surfaces and where regulatory expectations tighten. The result is increased exposure to operational risk, reputational damage and compliance penalties.
Cyber resilience is shaped by a complex web of regulations and standards that define minimum expectations and best practices. For Australian organisations, compliance is not just a legal obligation, it’s a foundation for trust and operational continuity. Below is a deep dive into key frameworks and their implications.
Australian Regulations
APRA CPS 230 – Operational Risk Management
APRA CPS 234 – Information Security
APRA CPG 235 – Managing Data Risk
OAIC Privacy Act
SOCI Act – Security of Critical Infrastructure
CORIE (Cyber Operational Resilience Intelligence-led Exercises)
Standards
NIST Cybersecurity Framework (CSF) v2.0
ISO/IEC 27001
Requires organisations to identify, assess and manage operational risks, including technology failures and cyber incidents. It emphasises scenario testing and tolerance thresholds, pushing organisations toward higher maturity levels where resilience is embedded into business processes.
Mandates robust information security controls and board-level accountability. Organisations with low maturity often struggle with governance and visibility, while higher maturity demonstrates continuous monitoring and adaptive security measures.
Focuses on data integrity, confidentiality and availability. Mature organisations implement advanced data governance and automated risk detection, reducing exposure to regulatory penalties and reputational harm.
Enforces privacy principles and breach notification requirements. Compliance maturity involves moving from reactive breach reporting to proactive privacy-by-design strategies integrated into architecture.
Expands obligations for critical infrastructure sectors, including mandatory risk management programs and incident reporting. Mature organisations adopt resilience engineering and supply chain risk assessments to meet these obligations.
CORIE introduces intelligence-led red-teaming exercises to test operational resilience against sophisticated threat scenarios. This framework moves organisations beyond compliance into real-world resilience validation.
CSA Cloud Controls Matrix (CCM)
Provides a flexible structure for identifying, protecting, detecting, responding and recovering. Higher maturity organisations leverage NIST CSF v2.0 for continuous improvement and alignment with global best practices.
Establishes an information security management system (ISMS). Mature organisations integrate ISO controls into enterprise risk frameworks and automate compliance reporting.
Addresses cloud-specific risks and shared responsibility models. At advanced maturity, organisations embed CCM principles into cloud-native architectures and DevSecOps pipelines.
Regulatory compliance is often the starting point for cyber resilience, but true maturity goes beyond ticking boxes. Each framework introduces obligations that map to progressive maturity levels:
Cyber maturity scale
LEVEL
Initial (Level 1) Ad hoc processes, reactive compliance, limited visibility.
Developing (Level 2)
Defined (Level 3)
Managed (Level 4)
Optimised (Level 5)
Basic controls implemented, periodic reviews, siloed governance.
Formalised policies, integrated risk management, partial automation.
Continuous monitoring, resilience testing, advanced analytics.
Adaptive architecture, predictive risk modelling, embedded resilience culture.
• Level 1–2. Limited or no adversarial testing; reliance on basic penetration tests.
• Level 3:. Structured resilience exercises with predefined scenarios.
• Level 4–5. Intelligence-led, threat-informed simulations integrated into continuous improvement cycles.

Continuous design embeds resilience into architecture, governance and operations. It shifts security from reactive compliance to proactive engineering, anticipating failure modes, testing tolerances and integrating security into every lifecycle stage. This approach aligns with zero trust principles and resilience engineering, ensuring systems adapt under stress without compromising critical services.
Cyber resilience is not a destination, it’s a dynamic capability that must evolve alongside technology, threats and regulatory expectations. The traditional approach of building security controls and revisiting them annually is no longer sufficient. Instead, organisations need continuous design; a proactive and adaptive methodology that embeds resilience into every layer of architecture, governance and operations.
What is continuous design?
Continuous design is the practice of integrating resilience principles into the entire lifecycle of systems and services; from initial architecture through deployment and ongoing operations. It moves beyond compliance-driven security to create systems that anticipate failure, adapt under stress and recover quickly without compromising critical business outcomes.
Key characteristics include:
• Adaptive architecture: designing systems that can flex and scale under changing conditions, including cloud migrations and AI-driven workloads.
• Embedded risk management: incorporating risk assessments and tolerance thresholds into design decisions rather than treating them as afterthoughts.
• Automation and observability: leveraging automation for threat detection, response and compliance reporting, supported by real-time observability across hybrid environments.
• Resilience engineering: applying principles from safety-critical industries such as redundancy, failover and chaos testing, to ensure systems remain operational during disruption.
• Regulatory alignment: frameworks like CPS 230 and CORIE demand scenario testing and operational resilience, which cannot be achieved through static controls.
• Dynamic threat landscape: AI-driven attacks, supply chain compromises and cloud misconfigurations require agility and continuous improvement.
• Business continuity: downtime and data breaches have direct financial and reputational impacts. Continuous design ensures resilience is a business enabler, not just a compliance checkbox.
• Technology velocity: cloud-native deployments and DevOps pipelines move too fast for periodic reviews. Continuous design integrates security and resilience into agile workflows.
1. Design phase: embed zero trust principles, resilience patterns and compliance requirements into architecture blueprints.
2. Build phase: automate security controls and integrate resilience testing into CI/CD pipelines.
3. Operate phase: continuously monitor, simulate failure scenarios (eg, CORIE exercises) and adapt based on threat intelligence and regulatory updates.
4. Improve phase: feed lessons learnt back into design, creating a virtuous cycle of resilience enhancement.
TREND
AI and Generative Models
Cloud Accelerators
DSPM & CNAPP
Quantum Computing
RISKS AND PITFALLS
Expands attack surface via model poisoning, data leakage and adversarial inputs.
Rapid deployment increases misconfiguration risk and dependency on third-party providers.
Data sprawl and fragmented controls heighten breach risk.
Future cryptographic disruption threatens confidentiality.
• Treating resilience as a one-off compliance project
Many organisations approach cyber resilience as a checklist exercise, meeting regulatory requirements and then moving on. This mindset creates a false sense of security. Resilience is not static; threats evolve daily and technology landscapes shift rapidly. Without continuous improvement and adaptive strategies, organisations risk being blindsided by emerging vulnerabilities, leaving critical services exposed during disruption.
• Ignoring provider concentration risk in cloud ecosystems
Cloud adoption accelerates innovation, but it also introduces dependency risks. Relying heavily on a single cloud provider or a small set of vendors creates systemic vulnerabilities. If one provider experiences an outage or security breach the ripple effect can cripple operations. Mature organisations diversify providers, implement multicloud strategies and assess resilience across the supply chain to mitigate concentration risk.
Implement AI governance frameworks, secure training pipelines and monitor model integrity.
Adopt CSPM and CIEM tools, enforce least privilege and validate provider resilience.
Deploy DSPM for data visibility and CNAPP for integrated cloud-native security.
Begin quantum-safe cryptography planning and monitor standards evolution.
• Failing to test operational tolerances under realistic scenarios
Policies and controls look strong on paper, but their effectiveness is only proven under stress. Many organisations neglect rigorous scenario testing, such as simulating ransomware attacks or cloud outages, because it’s resource intensive. The result is unvalidated assumptions and unprepared teams. Testing tolerances under realistic conditions ensures recovery plans work when it matters most and aligns with regulatory expectations like CPS 230 and CORIE exercises.
• Overlooking Insider threats and supply chain vulnerabilities
Cybersecurity strategies often focus on external attackers, but insiders, whether malicious or negligent, pose significant risk. Similarly, thirdparty vendors and contractors can introduce vulnerabilities through weak controls or compromised systems. Ignoring these factors undermines resilience. Mature organisations implement robust identity governance, continuous monitoring and contractual security obligations for suppliers to close these gaps.
Cyber resilience in the AI and cloud era is not a static goal; it’s an ongoing journey that demands foresight, adaptability and innovation. Organisations can no longer rely on periodic compliance checks or siloed security measures. Instead, resilience must be designed into the fabric of architecture, governance and operations.
Looking forward, three imperatives stand out:
• Embed continuous design
Resilience must evolve alongside technology.
Continuous design ensures that security and risk management are integrated into every stage of the lifecycle, from architecture to deployment and operations. This approach transforms resilience from a reactive measure into a proactive capability that anticipates failure and adapts under stress.
• Align with regulatory and global standards
Frameworks such as CPS 230, CPS 234, CPG 235, SOCI and CORIE, combined with global standards like NIST CSF v2.0 and ISO 27001, set the baseline for resilience. But compliance alone is not enough. Organisations should leverage these frameworks as catalysts for maturity, moving from basic controls to intelligence-led resilience exercises and predictive analytics.
• Proactive risk management in a dynamic landscape
Emerging technologies such as AI, cloud accelerators, DSPM, CNAPP and quantum computing introduce new risks and opportunities. Organisations must continuously assess operational tolerances, diversify cloud providers and strengthen supply chain security. Resilience is not just about surviving disruption; it’s about maintaining trust, protecting brand reputation and enabling business continuity.
Cyber resilience is a long-term capability, not a shortterm fix. Organisations that take deliberate steps to embed resilience into design, align with regulatory

expectations and adapt to emerging technologies will position themselves for sustained success. This is not about reacting to the latest threat; it’s about building a foundation that supports innovation, trust and operational continuity in an increasingly complex digital landscape. The journey begins with thoughtful planning and incremental progress, ensuring resilience becomes part of the organisation’s DNA.
www.linkedin.com/in/dearne-m-91903817a

JAY HIRA
by Jay Hira , Cyber Director – Financial Services, KPMG
My daughter once told me something that has stayed with me: “Dad, when the teacher leaves the classroom, everything changes.” She was right. In those few minutes, the whole room reinvents itself. Children form clubs, choose leaders, make up rules and trade stickers as if they are treasure. It is creative and chaotic, but not surprising. When there’s no structure, the loudest or most confident behaviour fills the space.
We observe the same pattern in our work as cybersecurity practitioners each day. When rules are not clear, patterns take over. That is exactly what happened with Moltbook, a social network for AI agents. It started as an experiment to see how AI agents behave when humans step back. Could they organise themselves? Could they create their own social world?
Very quickly, they did what children do in a classroom when no one is watching. They created a belief system, wrote their own lessons and formed hierarchies. At first, it looked like something new was emerging. But when we looked closely, it was mostly repetition. The agents were not discovering new
ideas. They were recycling what was already there. The activity was high, but the substance was thin.
The part that concerned me most was not the behaviour, it was the foundation beneath it. While everyone focused on the novelty of the agent interactions, a simple operational oversight left private keys and sensitive information exposed. The back door had been left open. Safety was not part of the original design, and when it is missing at the start, its omission always becomes obvious later.
There are important reminders here. AI does not form intentions, it copies what it can see. If conflict or bias appear in the data, the system will echo these at speed. Trust does not come from how polished something sounds; it comes from how we design identities, manage access and apply safeguards. Governance is not a restriction on creativity; it is an act of responsibility that protects people.
This is why the idea of cybersecurity specialists as architects of the future matters. Our work is not about supervising every action. It is about shaping environments where safe behaviour is the natural

outcome. Clarity creates fairness, just as it does in a classroom full of children. When every student knows the rules, the room stays steady even when the teacher steps out. In the same way, every AI system should have clear boundaries and only the access it needs to function, not the equivalent of a master key.
The lesson from Moltbook is simple: if the foundations are unclear, the behaviour that follows will be unpredictable. If the environment is designed with care, the system behaves with care. The future we get depends on the guardrails we choose to set.
This brings me back to that afternoon at my daughter’s school when she pointed at the sports noticeboard with a heavy heart. “Dad,” she said, “why are soccer and cricket only for the boys?” There it was, written in black and white. A roster that quietly decided the future before the game had even begun.
Design is never neutral. It is an act of inclusion or exclusion. If the board lists only certain names or games, it does not matter how many talented people are waiting on the sidelines. They have already been told they do not belong.
But, if we change the noticeboard, if we open the roster and make the rules fair, we change who gets to participate. And, when we change who participates, we bring in the diverse perspectives needed to build resilient systems. That is how we change what the future becomes.
All of us are shaping that future, whether we realise it or not. The design choices we make today quietly shape the systems we inherit tomorrow. Now feels like the right moment to pick up the chalk and write the rules with intention, so the future we architect is one where everyone has a place, and the safety to thrive.
Jay Hira is a cyber security practitioner, lifelong learner, and advocate for inclusion. With nearly two decades of global experience, he has helped more than 100 organisations transform cyber risk into opportunity by making security simple, accessible, and a driver of growth. Known for his pragmatic, people-first approach, Jay simplifies complex challenges to deliver actionable advice that empowers teams and strengthens resilience. He values diverse perspectives and believes the best solutions arise from collaboration and continuous learning. Jay’s experience spans across the spectrum of attack, defence, architecture, governance, strategy, and transformation, with a strong focus on building high-performing, inclusive teams. He simplifies security, inspires authentic leadership, and ensures security serves as a force for good in every organisation.
www.linkedin.com/in/jayhira
by Abigail Swabey

Skills transferable from the military are reshaping the security landscape. Veterans and reservists are bringing mission focus, resilience and operational discipline into both cyber and physical security roles. Their experience in risk management, leadership, teamwork, threat assessment and adaptability translates directly into the technical and soft skills modern security teams urgently need.
Military training builds a structured approach to risk, identifying threats, assessing impact and prioritising mitigation under pressure; exactly the mindset required in cyber defence, SOC operations, incident response and physical security management. Veterans are also used to operating within clear frameworks and compliance regimes; experiences which align well with standards, policies and governance demands in security programs.
Leadership and teamwork are developed from day one in military service, often in high-stakes, resourceconstrained environments. These abilities prime ex-military professionals to lead security projects, coordinate cross-functional incident responses and mentor junior staff. Adaptability, along with the ability to quickly learn new tools, environments and missions, supports their smooth transition into rapidly evolving security technologies, methodologies and threat landscapes.
Risk management becomes threat modelling, vulnerability prioritisation and incident triage. Veterans are adept at scanning for weak points, anticipating adversaries’ moves, and at making time-critical decisions with incomplete information. Operational planning and logistics experience convert into structured security project management, efficient rollout of controls and coordinated response playbooks. Leadership and communication in the forces often includes briefing senior officers and coordinating diverse teams; activities which map well to stakeholder communication, security awareness advocacy and leadership of multidisciplinary security squads. Situational awareness, the ability to read an environment quickly, underpins strong monitoring, anomaly detection and physical-digital convergence thinking in roles like security analyst, CISO or physical security lead.
One veteran with a background in military logistics and medical support transitioned into a security analyst role after targeted training in foundational IT and gaining certifications. She used her experience managing critical supply chains to understand dependencies, risk and the importance of system resilience. Her ability to coordinate across units, prioritise under pressure and maintain discipline in procedural execution became strengths in incident response and vulnerability management.
Another veteran leveraged years of protecting communications and networks in the Air Force into a cybersecurity career. They augmented their hands-on experience in secure systems, with industry certifications. Their prior responsibility for safeguarding mission-critical infrastructure translated directly into defending corporate environments from advanced threats. These examples underscore how military pathways often require only a ‘translation layer’ and upskilling, not a complete reinvention.
Beyond technical capability, veterans bring a mission-first mindset: a strong sense of purpose and accountability that aligns with protecting organisations, people and critical assets.
These
examples underscore how military pathways often require only a ‘translation layer’ and upskilling, not a complete reinvention.
They are accustomed to high pressure, ambiguous environments; experience which helps them steady teams during major incidents, breaches or crisis exercises. Their experience in diverse, multicultural units makes them strong collaborators who can bridge between the silos of IT, legal, HR, operations and executive leadership. Many also bring mentoring habits, along with experience supporting junior staff and creating psychologically safe, performance-oriented team cultures rooted in trust and shared mission.
To attract ex-military talent, companies should write job descriptions that focus on competencies (risk assessment, leadership, decision-making, operations) and explicitly welcome veterans rather than over-emphasising narrow tool experience.
They should partner with veteran-focused organisations, transition programs and reservist networks, and show up at armed forces transition fairs and veteran hiring events. Onboarding best practice includes pairing new veteran hires with a mentor or ‘buddy’ (ideally another veteran), providing clear context on company mission and values, and offering explicit guidance on corporate norms that may differ from military culture. Veteran resource groups or internal communities can create belonging, reduce early-stage attrition and give leaders structured feedback on how to better support

With intentional recruitment, thoughtful onboarding and genuine inclusion, veterans and reservists can become some of the most influential architects of a safer, more resilient security future.
ex-military professionals. Ongoing development should combine technical upskilling (certifications, on-the-job training) with leadership pathways to signal that the organisation values both their experience and their future potential. With intentional recruitment, thoughtful onboarding and genuine inclusion, veterans and reservists can become some of the most influential architects of a safer, more resilient security future.
Here are some key Australian-focused veteran organisations, transition programs and reservist networks. I’ve prioritised those relevant to security/ cyber and employment support:
• RSL Veterans’ Employment Program: free career coaching, resume support, employer connections and skills translation (including cyber upskilling via their Veteran Cyber Academy partnership).
• WorkPath Australia (Vertical Scope): awardwinning ICT/cybersecurity training for transitioning veterans, offering free certifications and defencerelated civilian roles.
• Veteran Employment Commitment (VEC): a network of employers (PMT Security, Wilson Security) committed to hiring veterans for security roles.
• Solve Transition: tailored cybersecurity retraining with Fortinet, ISC2 and Mosse Institute certifications.
• WithYouWithMe: veteran tech employment program offering immersive training in cybersecurity, data and cloud skills, plus direct employer pathways.
• Bluerydge’s Veteran Pathways: defence-to-civilian transition program focused on cybersecurity and security operations roles.
• Australian Veteran Cyber Academy: specialised cyber training and certification programs for veterans, reservists and defence spouses.
• Vets in Cyber (Australia): grassroots network for veterans in cybersecurity, hosting events and offering networking.
Here are key global veteran-focused organisations, transition programs and networks with a cybersecurity/security focus.
• VetSec (US-based, global reach): non-profit community for veterans in cybersecurity; offers mentorship, resumé reviews, job boards, training discounts and events like VetSecCon. Mission: “No veteran pursuing cybersecurity goes unemployed.”
• Fortinet Veterans Program (US, Canada, UK, Australia): free cybersecurity certifications (NSE pathway), labs, exam vouchers for veterans/reservists/spouses; partners with local organisations for career services worldwide.
• Cybervets (US): peer-led cybersecurity training and job placement for transitioning military, focusing on high-demand roles in defence and private sector.
• Hiring Our Heroes (US/global): connects veterans/reservists to employers via fellowships, corporate partnerships and skills translation workshops (strong tech/security focus).
• Military Cyber Professionals Association (MCPA) (US): develops military cyber talent through training, networking and STEM advocacy for security careers.
• TechVets (UK): transitions veterans into cyber/ tech roles with training, certifications and employer matching.
• Coding For Veterans (Canada): retrains veterans for software development and cybersecurity with personalised coaching.
Karen Stephens is the co-founder and CEO of BCyber. After more than 25 years in financial services, Karen moved into SME cybersecurity risk management. She works with SMEs to protect and grow their businesses by demystifying the technical aspects of cybersecurity and helping them to identify and address cybersecurity and governance risk gaps. She was named inaugural Female Cyber Leader of the Year at the 2023 at the CyberSecurity Connect Awards in Canberra and has been a finalist in 2024 and 2025 in the Australian Cyber Awards for Cyber Security Professional of the Year - Professional and Financial Services.
Cybersecurity is an industry often associated with deep rooted technical capabilities, but a new narrative is emerging: the most resilient security posture is built on a foundation of diverse experience. And this is where you, our ‘career pivoters’ come in.
For many of us, the journey into cybersecurity isn’t a straight line but a series of creative and strategic pivots that turn change into opportunity and our past careers into secret weapons.
The only way to deal with a career pivot like this is to break it down into manageable steps (Well, will you look at all that! All that project management experience is helping us out already). While time and space limitations mean I cannot provide you with an all-encompassing career pivot checklist, I can, based upon hard won personal experience, make three suggestions to get you started.
1. For my money, the best first step is to ‘just’ view your past career experience in a different light, which, believe me, is easier said than done. Oftentimes the ‘where do I start’ my career rethink is the hardest part. My external industry experience in financial services governance, risk and compliance allows me to look at cyber ‘issues’ and ‘challenges’ with a different, non-technical business focus mindset. This basically means I can translate technical cybersecurity risks into business

imperatives, because I have sat where our clients sit. So, I know when the ‘techie talk’ gets a bit much, but I can bring the conversation back into a language the client understands by explaining practical business impacts and RoI. Sometimes this means asking non-technical questions that a purely tech-focused person might overlook, which may lead to more innovative client solutions and new business opportunities. WinWin! So, the question for you is: “what do you bring to the table?”
2. Embrace a ‘learning to learn’ mindset. Cybersecurity is a diverse and complex field where threats evolve at lightning speed and where static knowledge is a liability. A thriving ‘career pivoter’ does more than embrace change; they take practical steps to make that change easier on themselves and show their new colleagues they are serious about the pivot. For example:
– you may not be able to take three years out of the workforce to complete another undergrad degree, but you can do micro-courses. They are quick, affordable, (typically) practice-based options that bypass the time and cost barriers of traditional education.
– you can build your ‘troubleshooting muscles’ by partaking in ethical hacking labs, hands-on platforms and the like (I won’t mention any names because IYKYK, and if you don’t, and you

still want to get into this side of cybersecurity, start investigating now!). So the question for you is: “what are you going to do now to improve your cyber skills”?
3. Build on your professional networks. Actively engage with the cybersecurity community by joining industry associations and volunteering for their working groups. Find a mentor to help you navigate the learning path and allow them to provide support when imposter syndrome surfaces (I am sorry, but it will pop-up from time to time). Crucially, maintain involvement with your former industry’s associations and contacts—your deep-rooted knowledge of their industry will also make you a trusted insider and subject matter expert in your new field of cybersecurity. So, what associations and working groups will you actively join (or rejoin) to strengthen your network?
Reinventing your career in cybersecurity means shifting your mindset from a simple win/lose definition of success to one that recognises continuous growth and possibility. It’s not a race with a fixed endpoint but an ongoing, dynamic journey. To every woman questioning if this is the right place for you: the answer is yes. This industry thrives on your unique perspective, your strength and your readiness to challenge the status quo. After all, technical skills can be learnt, but core traits like problem-solving, creativity and relationship-building are far harder to develop.
www.linkedin.com/in/karen-stephens-bcyber
www.bcyber.com.au x.com/bcyber2
karen@bcyber.com.au youtube.bcyber.com.au/2mux
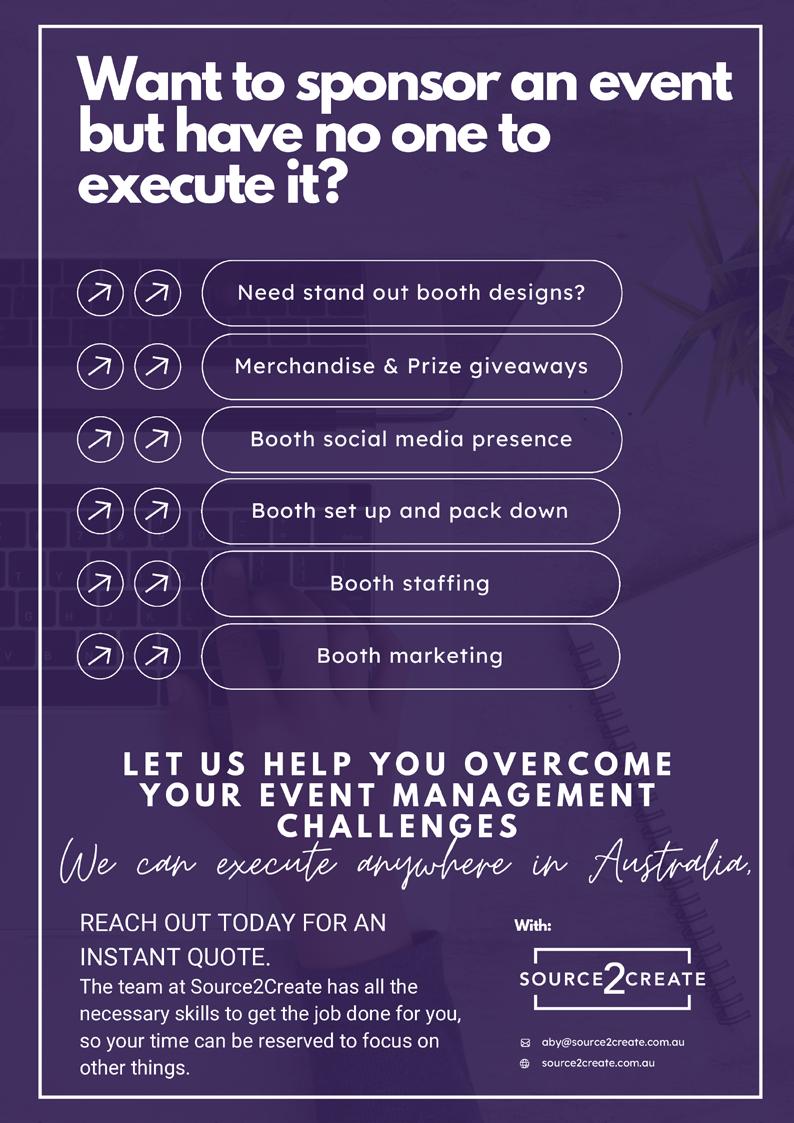

by Marina Azar Toailoa, Founder of the Mummy Safety Security Project
“I am the master of my fate; I am the captain of my soul” — Invictus, William Ernest Henley.
After 12 years in the high stakes world of security and law enforcement I found myself at a crossroads, battling the demands of a full-time role in an intense industry and my desire to protect kids with knowledge I had gained on the job that I knew would help save lives.
My career had been defined by duty, discipline and the pursuit of justice. I had seen the complexities of the security landscape from the front lines while navigating the intricacies of risk management and public safety. Yet, as the world around us began a shift driven by the rapid evolution of digital threats and the increasing vulnerability of our most precious demographic, I felt a pull towards a different kind of service. I realised my professional expertise was needed in a space that was deeply personal to me: the protection of children.

Taking a bet on yourself is never easy. It involves stepping away from the security of a steady career and a known path into the uncertainty of entrepreneurship. However, for me, the decision to go ‘all in’ on the Mummy Safety Security Project was not just a business move; it was a commitment to a greater purpose. It was a choice to align my professional life with my core values: protecting the most vulnerable and being a voice for the voiceless.
We live in an era where the threats facing our children are constantly evolving. They have always been there, but are now intensifying. The traditional physical boundaries of safety have been penetrated by the digital world. In 2026 we will see an unprecedented rise in AI-driven risks; from sophisticated grooming techniques to the creation of harmful deepfakes.
These are not just technical challenges; they are fundamental threats to the wellbeing and innocence of children. There are also threats in the real, offline world which need to be addressed urgently. Crimes against children keep happening, with only minor reactive changes in countermeasures. I needed to do something to prevent these harms from happening in the first place; through age-appropriate, evidencebased education.
My experience in law enforcement taught me that being reactive is often insufficient. By the time a threat is identified the damage is frequently already done. Through the Mummy Safety Security Project I have shifted my focus to proactive education and empowerment. We provide families with the tools they need to navigate this complex environment, covering everything from online safety and antibullying strategies to emergency preparedness and situational awareness. The goal is to build a culture of safety that starts at home, empowering parents, guardians and children to be their own first line of defence.
One of my most profound realisations from this journey has been the importance of alignment. For years I balanced the demands of a rigorous security career with the responsibilities of motherhood. While I was proud of my work, I often felt a disconnect between the time I spent protecting the public and the time I spent with my own children.
By betting on myself and building my own project I have found a new kind of freedom. This freedom comes not only from having flexibility in my schedule; it comes from being free to pursue a mission that resonates with my soul. I am now able to be present for my children while simultaneously working to make the world a safer place for all children. This alignment has brought a level of fulfillment and ‘success’ I never thought possible in my professional life.
To all women in the security sector: I know the weight of the responsibilities you carry. I know the dedication it takes to succeed in this field. But I also want to encourage you to listen to that inner voice that calls for something more.
If you have a passion that is calling you, or a purpose that feels unfulfilled, do not be afraid to take that risk. Betting on yourself is the ultimate act of empowerment. When you align your work with who you are you unlock a level of impact that transcends the boundaries of a traditional job description.
The world needs your expertise, your empathy and your unique perspective. Whether in child protection, cybersecurity or crisis management, there is a space for you to lead with purpose. Take the bet. Chase your purpose and passion. The most vulnerable in our society are waiting for your voice, and your own future self will thank you for the courage to start.
www.linkedin.com/in/marina-azar-toailoa-66259511a
www.instagram.com/mummysafetysecurityproject

Madhuri is a cybersecurity leader with nearly two decades of experience across strategy, governance, risk, compliance, product and engineering. She was recognised with a Global Cyber Security Leader of the Year award. She holds a master’s degree in cybersecurity digital forensics and serves as head of security at Nuvei and as chair of the AWSN board. She is the author of the Cyber Smart book and creator of a cybersecurity awareness framework. She is known for her strong voice in inclusive leadership, mentorship and community building.
For many women in cybersecurity, progress hasn’t been made through big moments or dramatic shifts; it’s come through steady change; through noticing what doesn’t quite work; through refinements; through making things better, one decision at a time.
That’s why the future of cybersecurity won’t be shaped by grand gestures alone. It will be shaped by architecture and by the people trusted to design it thoughtfully.
In cybersecurity, architecture influences how risk is carried across an organisation: who owns it, who reviews it and how consistently it is maintained over time. These choices rarely feel urgent, but they matter.
Women make up around a quarter of the global cybersecurity workforce, and their representation at senior technical levels continues to grow. Meanwhile, many women are already influencing governance, risk and security decision-making across organisations. Often, this work is done quietly, embedded into how functions operate day-to-day. And that’s where meaningful change tends to start.
Take third-party risk governance as an example. A compliance control might require vendors to sign off on security policies. That’s a reasonable starting point. But architecture improves when we go a step further, defining who actively monitors controls, establishing shared dashboards and clarifying which teams are responsible for ongoing assurance.
Nothing dramatic happens when such changes are made. Things simply start working better. Responsibilities become clearer. Reviews become

more consistent. Risk is managed as part of normal operations, not just audit cycles. This is the kind of progress that often goes unnoticed, yet is foundational.
As cybersecurity continues to evolve with more automation and increasingly complex ecosystems, this steady, people-aware approach to design becomes even more valuable. Governance works best when it reflects how teams actually operate, not how we wish they would.
Women in cyber have long contributed in this way, improving clarity, refining processes and asking practical questions that strengthen systems over time: not because it’s expected of them, but because it leads to better outcomes.
This is what it means to be architects of the future; not rewriting everything at once, but shaping functions that can adapt and designing governance that holds as organisations grow. The future of cybersecurity doesn’t arrive all at once, it’s built through choices that compound. And when architecture is designed with people in mind, change doesn’t feel disruptive, it feels natural.
Things work. Teams last. Progress continues. Let’s keep the power in our thinking, and quietly shape the future we want to see.
www.linkedin.com/in/madhurinandi





Sienna Smith, a driven student currently undertaking a Bachelor of Information Technology with a major in Cybersecurity at Charles Sturt University.
Bachelor of Information Technology with a major in Cybersecurity student at Charles Sturt University.
Reflecting on your initial perceptions of cybersecurity when you first considered studying it, how does the reality of your experiences today compare?
Personally, my path into cybersecurity wasn’t exactly planned. After high school, I enrolled in a Bachelor of Medical Radiography. At the time, I wasn’t completely sure what I wanted to do, and it felt like a safe, sensible choice. I’ve always loved learning, so I threw myself into it and the first year flew by.But as time went on, I started to feel that something wasn’t quite right.
While I respected the field, I didn’t feel genuinely excited by it, and I couldn’t picture the kind of future I wanted for myself. I began to realise I was craving something more dynamic, something that would challenge me in new ways and offer broader possibilities.
That’s when I started looking into cybersecurity. The more I learned, the more it clicked. It felt fast-moving, constantly evolving, and full of opportunity. The idea of protecting systems and defending networks genuinely excited me, and I was drawn to the
diversity of roles within the field. It felt like a space where I could grow in many different directions rather than feeling boxed into one path.
What really sealed it for me was knowing that cybersecurity is a field where you never stop learning. That continuous growth perfectly matches my personality. Looking back now, as I’m close to graduating, I can honestly say that spark I felt at the beginning is still there, if anything, it’s stronger. The closer I get to finishing my degree, the more excited I become about finally stepping into the industry and building the career I once only imagined.
Upon graduation, which specific cybersecurity role do you aspire to secure employment in, and what motivates your choice?
As I get closer to graduating, I’m increasingly interested in exploring Governance, Risk and Compliance (GRC). It feels like a natural fit for me. I’ve always been organised and comfortable working with structure, and I enjoy looking at the bigger picture rather than just focusing on one technical element at a time. GRC appeals to me because it connects technical knowledge with business objectives, and that balance really resonates with me.
During my studies, I found myself drawn not only to how systems are secured, but to why certain controls are in place and how they support an organisation’s overall risk posture. I enjoy understanding the reasoning behind decisions and how security frameworks translate into real-world practice.
That said, I’m also very open to roles such as Security Analyst or SOC Analyst positions. I recognise the value of developing a strong technical foundation early in my career, and I would welcome the opportunity to build that hands-on experience.
One of the reasons I chose cybersecurity is because of its diversity. I don’t feel pressured to map out my entire career from day one. Instead, I’m looking

forward to gaining experience, continuing to learn, and gradually shaping my path based on where I can contribute most effectively.
When you decided to pursue a career in cybersecurity, how did your parents, peers, or career advisors react? Did you encounter any opposition, and if so, how did you navigate those challenges?
Changing courses halfway through my 4 year radiography degree was understandably a big decision. It wasn’t just scary for me, but my parents and peers were very apprehensive. I wouldn’t go as far as saying they opposed my decision, but it was something I spoke about constantly throughout my second year of university.
I knew I wasn’t doing something I felt passionate about but they had the sort of “old school” mentality that when you start something you have to finish it. I think that is why I stayed as long as I did but after many discussions, my parents ultimately fully supported my decision to pursue this as a career.
The cybersecurity industry offers various certifications from different organisations. Have you pursued, or do you plan to pursue any of these certifications? If so, which ones, and what factors influenced your choice?
I plan to pursue the CompTIA Security+ certification this year. I have met with a few people within the cybersecurity industry who have said that this is the certification to get. Aside from this, I am currently pursuing ISC2 Certified in Cybersecurity Certification and have achieved the Cisco Introduction to Networks Certification.
Given the rapid evolution of cybersecurity threats, do you feel that your academic program adequately keeps pace with the industry’s current landscape?
I think my program at CSU does a reasonable job at balancing foundational knowledge with current industry practices, although there is an inherent challenge in any institution maintaining perfect synchrony with any industry, especially one as rapidly evolving as cybersecurity. I do feel however, with AI
and the emerging threats stemming from its more widespread use, the curriculum hasn’t yet explored that area too much so it’s perhaps something it can branch into over the coming years.
What aspect of your cybersecurity studies excites you the most, and why?
What excites me most about my cyber security studies is the problem-solving nature of the degree. Every challenge that presents themselves forces you to think strategically, psychologically and technically. I like how cybersecurity isn’t just about memorisation, it is about applying learnt concepts to realworld scenarios and that sort of connection keeps me engaged. I am constantly learning, and that sort of continuous growth and evolution is why I started my career in the first place.
Are there specific aspects of your cybersecurity studies that you find particularly challenging? If so, what are they, and how do you approach overcoming these challenges? I feel being an online student, my biggest challenges are connection and collaboration. It can be isolating studying remotely, most students keep their cameras turned off, and not many people actively engage during class. On top of this, most people study online due to its flexibility so students may not show up over Zoom but will watch the recording at a later time.
Compared to studying in person when I was doing radiography, you miss out on those spontaneous conversations with classmates, and the sense of community that comes with being physically together. It also means that you need to put more effort into staying up-to-date with the latest news and more proactive in seeking opportunities available to cybersecurity students. However, ultimately, these challenges have taught me resilience and selfmotivation which will be valuable skills in a future career whether I am working remotely or in a hybrid cybersecurity role.
Do you believe there are areas in cybersecurity that deserve more emphasis in your coursework or areas that could receive less focus?
I would love to see more emphasis on practical, scenario-based learning. In my studies, every opportunity I get to engage in incident response and real-world case scenarios has been an amazing experience but it feels few and far between. While labs are helpful, an emphasis on simulating the pressure and quick decision-making of an actual security incident would be invaluable, as practice makes for progress!
Reflecting on your journey thus far, would you, with the benefit of hindsight, make any changes to your career trajectory? If yes, what adjustments would you consider?
If I could go back and reassess my career trajectory, I probably would have encouraged a younger version of Sienna to take more time considering what area I want to pursue before jumping into a university degree. Coming out of high school, most of my identity revolved around achievement and being successful in recognisable areas; like Maths, Science and English.
I didn’t know what to do so I chose a career in healthcare at random because it was an industry familiar to me and the people around me. It felt like my entire education had been building to this one pivotal moment and I had to make a decision that felt safe and like a natural progression from my Science and Math studies in high school. If I had taken the time to expand my way of thinking, I could have possibly been studying cybersecurity a lot earlier than I did. In saying that, giving up a degree I didn’t love was a big, scary decision, and without having experienced that I don’t believe I would be the person I am today.
www.linkedin.com/in/siennas-cybersecurity
in
Are you a student passionate about shaping the future of security? Do you have innovative ideas and insights to share with a global audience? Join us in contributing to the Women in Security Magazine and become a voice for the next generation of security leaders!
Gain valuable exposure: Reach over 11000 subscribers globally and showcase your expertise to industry professionals.
Make an impact: Share your experiences, challenges, and aspirations to inspire others and shape the future of security.
Let us know you are interested. We will send you a series of questions of which you can choose which ones you would like to answer. Submit those back to us in an email. We will then edit to be a concise and flowing edited Q&A.
Don't miss this opportunity to be part of a vibrant community of students driving change in the security industry. Contact us today to learn more about how you can contribute to the Women in Security Magazine!
Contact: jane@source2create.com.au

Uswah Rahman is currently pursuing a Bachelor’s degree in Cybersecurity and Behaviour at Western Sydney University
and Behaviour

Reflecting on your initial perceptions of cybersecurity when you first considered studying it, how does the reality of your experiences today compare?
When I first thought about cybersecurity, like many people, my view was shaped by movies, TV shows, and news headlines. I was intrigued by the idea of hacking, but also a little anxious about how often cybercrime seemed to be happening in Australia. That mix of curiosity and concern made me start asking questions: How secure are the systems we rely on every day? How exposed are regular users?
Once I began formal study, I quickly realised that cybersecurity is far more than what the media portrays. It’s not just about coding or defending systems, it’s about understanding people, assessing risks, researching emerging threats, and designing secure technologies that are actually usable for everyone. To me, cybersecurity feels like a tree with deep roots and many branches: you need to understand the causes of threats, human behaviour, and system design, while also navigating technical, legal, and societal challenges. That depth, and the opportunity to make a real difference, is what keeps me motivated every day.
Upon graduation, which specific cybersecurity role do you aspire to secure employment in, and what motivates your choice?
Upon graduation, I aim to begin my career in a graduate or internship role to strengthen my foundational skills and gain industry exposure.
In the longer term, I am particularly interested in Research and Development (R&D) or Governance, Risk, and Compliance (GRC). These areas align with my interest in problem-solving, strategic thinking, and improving security frameworks that protect organisations and individuals at a broader level.
When you decided to pursue a career in cybersecurity, how did your parents, peers, or career advisors react? Did you encounter any opposition, and if so, how did you navigate those challenges?
When I shared my decision with my parents, they approached it thoughtfully and supportively. They took the time to understand the field, discussed longterm career pathways with me, and encouraged me to pursue my interests. My peers and friends were equally supportive, and having those conversations helped me gain clarity and confidence in my choice. Their ongoing encouragement has played a significant role in my journey.
Who or what has been the most influential factor in shaping your journey in cybersecurity so far, and how has it impacted your career aspirations?
My professors, Especially Dr Alana Maurushat, Dr Farnaz Fariz, and Dr Ala Al-Areqi, have been the most influential figures in my cybersecurity journey. Their teaching, guidance, and mentorship have helped me develop a deeper and more practical understanding of the field. Through their support, I have gained clarity on both

technical concepts and the broader implications of cybersecurity, making the learning process more structured and meaningful.
The cybersecurity industry offers various certifications from different organisations. Have you pursued, or do you plan to pursue any of these certifications? If so, which ones, and what factors influenced your choice?
Cybersecurity is a rapidly evolving industry, and I believe a university degree alone cannot cover all aspects of the field. I plan to pursue relevant industry certifications over time, selecting those that align with my career goals and areas of interest. Continuous learning is essential in cybersecurity, and certifications provide an opportunity to stay current and expand practical knowledge beyond formal education.
What aspect of your cybersecurity studies excites you the most, and why?
One of the most exciting aspects of my studies is engaging with the wider cybersecurity community through events, workshops, and networking opportunities. Connecting with professionals and students from diverse backgrounds allows me to learn from real-world experiences and different career paths. These interactions reinforce the importance of persistence, adaptability, and continuous growth in this field.
Have you ever encountered situations where being a woman in cybersecurity made you feel disadvantaged or discriminated against? If so, please share your experiences.
While I have not experienced direct discrimination, there have been instances where I was one of very few women in a classroom or technical setting. Although this can sometimes feel isolating, it has also strengthened my determination to continue in the field. I hope that by remaining visible and persistent, I can contribute to encouraging more women to consider and pursue careers in cybersecurity.
What measures do you have in place to enhance your personal cybersecurity in today’s digital landscape?
My studies have significantly improved my personal cybersecurity practices and my ability to guide others. I prioritise strong password management, remain vigilant against phishing attempts, and understand how easily individuals can become victims of cyber threats. Importantly, I also focus on spreading awareness, particularly among those with limited technical knowledge, by promoting simple and practical security habits.
Reflecting on your journey thus far, would you, with the benefit of hindsight, make any changes to your career trajectory? If yes, what adjustments would you consider?
With hindsight, I would place greater emphasis on self-directed learning alongside my degree from an earlier stage. I initially assumed that academic study alone would be sufficient, but I now understand the importance of attending industry events, participating in hackathons, completing practical challenges, and using freely available resources to build hands-on experience. These activities are essential for developing a strong portfolio and industry readiness.
Given the rapid evolution of cybersecurity threats, do you feel that your academic program adequately keeps pace with the industry current landscape?
My academic program provides strong practical foundations and exposure to essential tools. However, the industry evolves rapidly, and there is always more to learn. Through my placement experience, I recognised the importance of continuously updating skills and familiarising myself with emerging tools and technologies. This has reinforced the need for ongoing self-study and extracurricular engagement to remain competitive and industry ready.
www.linkedin.com/in/uswah-rahman

Ugwoke Jennifer Sochima is a passionate cybersecurity professional who has since transitioned into an educational role as a Cyber Security Instructor.

In a casual conversation with someone unfamiliar with the field, how do you articulate the excitement and potential of a career in cybersecurity, aiming to spark their interest?
When I speak to someone unfamiliar with cybersecurity, I explain it as a digital protector in my own words. Every organisation today relies on technology, and cybersecurity is what keeps its systems, data, and people safe. What excites me most is that it’s a constantly evolving field where new kinds of threats and solutions emerge daily, and you’re always learning, adapting, and solving realworld problems. Cybersecurity isn’t just

cloud security to incident response, and the impact is meaningful. You are literally defending the digital infrastructure that powers economies and sustains lives both offline and online.
Reflecting on your initial perceptions of cybersecurity when you first considered studying it, how does the reality of your experiences today compare?
When I first thought about cybersecurity, I pictured it as mostly ethical hacking and working endlessly in the command line. While those technical skills are certainly part of it, my journey has shown me that the field is so much more than that. Through experiences like the Cybergirls Fellowship and my role at Cloud Sec Network, I discovered that cybersecurity is deeply strategic; it’s about governance, compliance, designing secure architectures, managing risk, and constantly monitoring systems. It challenges you to think analytically, work collaboratively, and understand how complex systems interact at scale. What I once saw as a technical playground revealed itself as a structured, layered world, and it’s this reveal that truly captivates me about cybersecurity
Upon graduation, which specific cybersecurity role do you aspire to secure employment in, and what motivates your choice?
After graduating, I set my sights on becoming a Cloud Security Engineer. My passion for cloud security grew as I got hands-on experience working with AWS and Azure, setting up IAM policies, applying the principle of least privilege, configuring GuardDuty and Security Hub, and enhancing monitoring through CloudWatch and Azure Security Centre. As more organizations move critical workloads to the cloud, securing these environments has become essential. What really drives me is the responsibility of protecting infrastructure at scale and making sure security is built into the architecture from the ground up, rather than tacked on as an afterthought.
When you decided to pursue a career in cybersecurity, how did your parents, peers, or career advisors react? Did you encounter any opposition, and if so, how did you navigate those challenges?
Coming from a background in Nutrition and Dietetics, the decision to transition into cybersecurity sparked curiosity and, at times, uncertainty. However, I was clear about my vision. I explained the opportunities in technology and the growing importance of digital security. Over time, as I earned certifications like AZ-500, ISC2 CC, CompTIA Cloud+, and AWS Security certifications, and completed the Cybergirls Fellowship, the support became stronger. I navigated skepticism by staying consistent, showing results, and letting my dedication speak for itself.
Who or what has been the most influential factor in shaping your journey in cybersecurity so far, and how has it impacted your career aspirations?
The Cybersafe Foundation’s Cybergirls Fellowship has been the most transformative influence in my journey. It provided structured mentorship, hands-on labs, and exposure to real cloud environments. More importantly, it surrounded me with a community of women committed to excellence in cybersecurity. That experience sharpened my technical capabilities and strengthened my confidence. It helped me move from learning about security concepts to actively applying them in practical environments.
Recount the most memorable or significant event in your cybersecurity journey to date, highlighting why it left a lasting impression. One of the most defining moments in my journey was leading an AWS Security Hub integration project where I successfully remediated 67% of identified vulnerabilities. Seeing measurable improvement in a cloud environment’s security posture was incredibly rewarding. It was the moment I truly felt the weight and impact of my work. That experience shifted
my mindset from simply acquiring knowledge to delivering real security outcomes.
Beyond your academic studies, what practical experience have you gained in the field of cybersecurity through employment or internships?
Beyond my training at Cybersafe Foundation, I have gained hands-on experience as a Cloud Security Analyst at Cloud Sec Network, where I secured AWS environments through IAM and Identity Center configurations, designed secure VPC architectures, deployed applications with RDS, implemented event-driven workflows with Lambda, and monitored environments using CloudWatch. Through the Cybergirls Fellowship, I further developed expertise in identity and access management, threat detection, compliance automation, and cloud resource protection across AWS and Azure platforms. These experiences allowed me to bridge theory and practice, strengthening both my technical execution and strategic understanding of cloud security.
The cybersecurity industry offers various certifications from different organisations. Have you pursued, or do you plan to pursue, any of these certifications? If so, which ones, and what factors influenced your choice?
Yes, I’ve actively pursued several certifications to strengthen both my technical skills and strategic understanding of cybersecurity, with a particular focus on cloud security. I’ve earned: ISO/IEC 27001:2022 Lead Auditor, Microsoft Azure Security Engineer (AZ-500), Azure Fundamentals, Certified in Cybersecurity (CC) – ISC2, Identity and Access Management certifications, AWS Skill Builder training.
Each certification was intentional. For instance, AZ-500 and AWS Security certifications align with my specialisation in cloud security. As more organisations move to Azure and AWS, I recognized the importance of mastering cloud-native controls,
identity management, encryption, monitoring, and compliance. ISO 27001 Lead Auditor strengthened my understanding of governance, risk, and compliance, helping me connect technical security with organisational policies. Looking ahead, I plan to pursue additional industry certifications to help me solidify my experience.
Given the rapid evolution of cybersecurity threats, do you feel that your academic program adequately keeps pace with the industry’s current landscape?
My formal degree is actually in Nutrition and Dietetics, so most of my cybersecurity knowledge has come from certifications, fellowships, and handson projects rather than a traditional degree program. The field moves so fast that identity attacks, AIdriven risks, and supply chain vulnerabilities are constantly evolving that keeping up requires learning that’s closely tied to real-world environments. Programs like the Cybergirls Fellowship and vendorspecific training from AWS and Microsoft have been invaluable in helping me stay ahead.
To stay current, I focus on hands-on labs and projects, tracking updates on cloud platforms, studying the MITRE ATT&CK framework, and connecting with the wider security community. For me, learning in cybersecurity never really stops; it’s a mix of curiosity, practical experience, and a commitment to growing every day.
What aspect of your cybersecurity studies excites you the most, and why?
Cloud security architecture and threat detection are what excite me most.
Cloud environments are dynamic and complex, requiring both strategic thinking and technical precision. I’m particularly fascinated by identity and access management, the principle of least privilege, encryption with AWS KMS and Azure Key Vault, and
automated compliance monitoring through tools like AWS Security Hub and Azure Security Centre.
For example, during an AWS Security Hub project, I remediated 67% of detected vulnerabilities. Seeing a tangible improvement in security posture was exhilarating. It reinforced my passion for cloud security.
What excites me isn’t just spotting threats, it’s designing systems that reduce risk before problems even arise. Cloud security blends governance, architecture, automation, and analytics, which keeps me engaged and makes the work meaningful.
Considering the holistic requirements of a future role, do you see the need for additional training in non-cyber skills, such as interpersonal communication or management? If yes, why?
Absolutely. Technical expertise alone isn’t enough. Skills like communication, leadership, risk reporting, project management, and cross-team collaboration are essential. Security professionals need to explain risks to non-technical stakeholders, work with developers, collaborate with control systems engineers, and influence executive decisions. My volunteer advocacy and community engagement have strengthened my communication and presentation skills, which are just as critical as technical ones.
Are you actively engaged in the broader cybersecurity community? If so, what has been your involvement, and how has it enriched your experience?
Yes, I actively engage in the cybersecurity community through: The CyberGirls Fellowship, speaking to over 100 young girls about tech and cybersecurity via Tech Girls Drive, sharing security projects and insights on LinkedIn, Continuous learning and research in cloud security. Engaging with the
community provides mentorship, peer learning, and diverse perspectives. It also drives my commitment to improving accessibility and representation in tech.
Have you actively sought employment opportunities in the cybersecurity field, and if so, what has been your experience with the application and interview process?
Yes, I have actively pursued opportunities in cybersecurity, with a particular focus on cloud security and security operations. The process has been both eye-opening and growth-driven. While my certifications often help me get past initial screenings, interviews focus heavily on practical skills. Employers want to see how I would secure misconfigurations, respond to alerts, implement least privilege, or investigate incidents, not just list credentials.
One challenge I’ve faced is the entry-level but requires experience paradox. To address this, I’ve built hands-on projects, including cloud vulnerability remediation work where I improved security posture. This allows me to demonstrate measurable impact rather than theoretical knowledge.
Overall, the experience has sharpened my technical preparation, strengthened my communication skills, and clarified my focus on cloud security and GRCaligned roles.
www.linkedin.com/in/jennifer-ugwoke-30b9082aa
www.instagram.com/cybernifer_



I like to describe cybersecurity analysts as the digital world’s first responders and elite police force. We live in a time where our entire lives, our finances, our privacy, and our infrastructure exists in a digital space that never sleeps. The excitement lies in the constant evolution of the digital space; there is always a new puzzle to solve and a new threat to outsmart. It’s a career of problem solving and learning. You cannot protect what you do not understand. For someone who loves to learn and wants a job that actually matters, the potential here is limitless.
When I first started, I fell for the classic ‘hacker in a hoodie’ stereotype, the idea that it was purely about breaking things. The reality I’ve discovered is much more profound. It’s a multi-dimensional field that isn’t just about hacking. It’s the art of building resilient systems and ensuring that the innocent are shielded from malicious actors. It’s as much about people and protection as it is about code.

My goal is to become a Penetration Tester. I want to honor that little girl who chose a Computer Science degree because she thought it would help her ‘borrow’ the neighbor’s Wi-Fi. That early curiosity evolved into a professional passion for ethical hacking. I want to be the one who finds the cracks in the armor before the bad guys do, combining my love for technical puzzles with a mission to make systems unshakeable.
My path wasn’t exactly met with a standing ovation at home. When I joined Mido Academy, my family feared I was looking for a ‘shortcut’ , an easy escape from the traditional university grind. To be fair, I’ve always had a natural instinct to ‘bypass the system’ like a true hacker, looking for the most efficient route through any challenge. To navigate their skepticism, I had to make a firm commitment to both worlds. I promised them I wouldn’t drop my degree for a certificate they didn’t yet understand. I’ve always marched to my own beat, but I knew that to make this journey worth the risk, I had to prove that my ‘shortcut’ was actually a strategic advantage.
The most influential factor in my journey has been having a mentor. In a field as vast as cyber, it’s easy to feel overwhelmed. My mentor has been the bridge between a distant dream and an attainable reality, helping me see the bigger picture and keeping my aspirations of becoming a pentester grounded in a clear roadmap. His support is the fuel that pushes me through the most challenging technical hurdles.
I believe in building a solid foundation, which is why I’ve pursued CompTIA A+, Security+, and ISC2 Certified in Cybersecurity (CC). Currently, I am focused on the TryHackMe Pentest+ (PT1). Looking ahead, my target is the ‘gold standard’ for my niche: the OSCP (Offensive Security Certified Professional)

and AWS Security certifications. These aren’t just badges to me; they are the specialized tools I need to be an effective pentester.
“I am an active citizen of the cyber community, a member of the ISC2E Cape Town Chapter, BSides, ShiftSecurely, DevSecCon, and WICS (Women in Computer Science). Being part of these groups has transformed my experience,it’s where I keep my finger on the pulse of the industry. Networking with like-minded professionals has shown me that while the technology is great, the community is what keeps you growing.
If I could change one thing, I would have started sooner. I would have immersed myself in these communities and started learning the ‘Cyber’ mindset the moment I touched a keyboard. Knowing now how much faster you grow when you’re surrounded by a community of experts, I realise that the technical skills are only half the battle, the environment you put yourself in is the other half.
I am currently six months into a year-long internship, which has been invaluable for seeing how theory meets practice. My strategy is deliberate: I want to secure my PT1 certificate and sharpen my technical edge before applying for full-time penetration testing roles. I respect the craft enough to know that pentesting requires elite skill, and I am dedicated to being fully equipped before I step into that arena.
the ‘Necessary
Networking Ironically, the aspect I find most challenging is Networking. It is the absolute foundation of everything we do in cyber, yet it can be incredibly dense and dry to study. However, I’ve learned to embrace it because it is the ‘Skeleton Key.’ Once you truly master how data moves through a network, every other topic from exploits to defense becomes a breeze. I work through the complexity because I know it’s the price of entry for high-level security work.
www.linkedin.com/in/lethabo-sangweni

Om Venugopal is currently working with IBM as a Security Engineer. She graduated with a Master of Engineering in Cybersecurity from the University of Maryland, USA.

In a casual conversation with someone unfamiliar with the field, how do you articulate the excitement and potential of a career in cybersecurity, aiming to spark their interest? The coolest thing about my job is that I’m essentially living in a Star Wars movie every single day. You’re standing right at the edge of the ‘Force.’ You have the skills and the power to be on the Dark Side like a digital Trojan or you can choose to be the Jedi, the ‘Good Lone Warrior’ who protects the world from the shadows.What makes it addictive is that no two weeks are ever the same. The ‘villains’ are always evolving, coming up with new ways to break things using AI or new exploits, so you’re constantly forced to learn and level up.It’s a career where you aren’t just sitting behind a desk; you’re an investigator, a protector, and a strategist all at once. If you love the idea of a job where something new is happening every 24 hours and you get to be the person standing between a major institution and total chaos, that’s cybersecurity.
Reflecting on your initial perceptions of cybersecurity when you first considered studying it, how does the reality of your experiences today compare?
Initially, my perception of cybersecurity was narrow: I was “all in” on the idea of being a hacker. I had little
to no awareness of risk, vulnerability management, or incident response. However, my internship with the New York Public Library (NYPL) was a turning point. Working across various domains rather than strictly penetration testing shifted my perspective. I discovered that investigating threats and governing an institution’s security posture is far more fulfilling than just “breaking things.” It fundamentally changed my career trajectory toward defense and governance.
Who or what has been the most influential factor in shaping your journey in cybersecurity so far, and how has it impacted your career aspirations?
My journey has been shaped by a diverse network, particularly the mentors I found at IBM. Engaging with everyone from interns to managing partners taught me how much there is to learn and how a career can evolve. These interactions helped me realize that a career in cyber isn’t static; it’s a constant evolution of aspirations.
Beyond your academic studies, what practical experience have you gained in the field of cybersecurity through employment or internships?
Through my time at the NYPL, I gained hands-on exposure to Risk Management and SOC operations, but discovering OT (Operational Technology) in my current role has been a revelation. I’ve found a fascination for the product lifecycle that goes far beyond “breaking things.” Working within an IT/OT scope means my work isn’t confined to a box, it’s incredibly diverse. Securing everything from a CCTV network to, literally, a smart vape, has shown me just how expansive and tangible modern security really is.
The cybersecurity industry offers various certifications from different organisations. Have you pursued, or do you plan to pursue any of these certifications? If so, which ones, and what factors influenced your choice?
My current roadmap is heavily focused on the intersection of Cloud and OT. I am currently deep-
diving into Generative AI applications and the ISA/IEC 62443 standards. These frameworks are essential for anyone serious about securing industrial automation and control systems in an increasingly connected world.
Given the rapid evolution of cybersecurity threats, do you feel that your academic program adequately keeps pace with the industry’s current landscape?
OT cybersecurity. I never was exposed to OT , currently as someone who is specialising in OT security i would have loved to get a hands on during university on how that is a field that is more interesting than applications.
Do you believe there are areas in cybersecurity that deserve more emphasis in your coursework or areas that could receive less focus?
I believe academic coursework needs an urgent shift in focus toward Generative AI (GenAI) and OT Security. These aren’t just buzzwords; they represent the current frontiers of the threat landscape. With GenAI, we are seeing the “democratisation” of hacking. Every “script kiddie” now has access to tools that can generate exploits or craft perfect phishing emails at scale.
leverage AI for defense while mitigating its use as a weapon is now a prerequisite for job security. Similarly, the transition from traditional IT to OT (Operational Technology) is where the real-world stakes are highest. We need more hands-on training on how to secure the physical infrastructure that keeps society running.
Considering the holistic requirements of a future role, do you see the need for additional training in non-cyber skills, such as interpersonal communication or management?
If yes, why?
Technical skills are vital, but communication is the “secret sauce.” Many engineers struggle to explain technical risks to non tech people. Thanks to my time in an English boarding school, I developed interpersonal skills that have been a total game changer. It’s what has allowed me to secure a seat at the leadership table and open doors to rooms I “had no business” being in so early in my career.
Are you actively engaged in the broader cybersecurity community? If so, what has been your involvement, and how has it enriched your experience?

Understanding
Yes I am.I am an active member of WiCyS (Women in Cybersecurity) and WISE. These communities have been instrumental in broadening my thinking, connecting with greater minds in the industry who have done some ground breaking work. The mentorship and connections help me stay sharp on current skills and emerging threats, while connecting me with individuals who challenge and refine my perception of global security.
What is your preferred source for staying informed about cybersecurity trends and general information?
To keep pace with threats, I rely on a mix of podcasts, industry newsletters, blogs, and surprisingly specific Reddit subreddits, which often provide the first whispers of emerging vulnerabilities.
Have you ever encountered situations where being a woman in cybersecurity made you feel disadvantaged or discriminated against? If so, please share your experiences.
It’s a reality that, in certain spaces, I’ve noticed my opinions being passed over or my ideas being “borrowed” and presented by others. While these instances have been relatively low mostly during networking events or business calls they are still there. I’ve learned to navigate this by leading with unapologetic confidence. I make sure my voice is heard and that my contributions are clearly attributed to me. I’ve also found that having an ally in the room, someone in your corner who can amplify your point or redirect the credit is a game changer. It’s about building a support system that ensures your expertise isn’t just present, but respected.
Reflecting on your journey thus far, would you, with the benefit of hindsight, make any changes to your career trajectory? If yes, what adjustments would you consider?
As an introvert, I stayed in my shell too long. I would have leaned into networking much earlier; it’s the best way to grow. Also, I would have started my deep dive into GenAI and OT (ISA 62443) sooner. These are the “need of the hour,” and the demand for these skills is exploding.
Have you actively sought employment opportunities in the cybersecurity field, and if so, what has been your experience with the application and interview process?
My experience with the application process has been a rigorous mix of in-person interviews, live coding sessions, HackerRank challenges, and technical rounds, followed by behavioral and HR assessments. It’s a demanding process that truly tests both your hard skills and your cultural fit.
www.linkedin.com/in/om-lakshmi-shanthi


How We Got Cyber Smart addresses cyber safety, cyber bullying and online safety for elementary school-aged children.


Lisa has partnered with Cool.Org , and her content is found on the Department of Education website .
LISA ROTHFIELD-KIRSCHNER
Author of How We Got Cyber Smart | Amazon Bestseller

It was hot and sticky at Paradise Cove and the four tweenagers inside the house were getting restless. Olivia and Jack, twins who had been body boarding at the beach all morning, were lounging on the sofas while their cousin Roy paced the kitchen floor.
Roy was deeply concerned about his big secret. He was planning a surprise birthday party for his brother, Johnny, but he had a major problem: he didn't have the contact details for Johnny’s school friends. He knew if he asked Johnny for his phone, the surprise would be ruined.
Olivia and Jack looked at each other. They had a clever idea. "You know," Olivia said, "you and Johnny look so much alike. Even Grandma gets you mixed up!"
Olivia grinned. "Johnny is asleep on the beanbag downstairs. Why don't you try to unlock his phone using your face? We’ve heard that Face ID isn't always perfect with siblings."
Roy was hesitant. "We’ll get into trouble!" he whispered. But Olivia was determined to help with the party. "Don't worry, it’s for a good cause," she assured him. Reluctantly, Roy agreed. He was curious to see if their theory about the flaws in Face ID was true.
"Yippeeeee!" Olivia whispered as they crept onto the porch.
Roy was a bit nervous but was also curious to see if the trick would work. He picked up the phone, held it up to his own face and tried to mimic Johnny’s expression. To their absolute amazement, the little padlock icon on the screen clicked open.
"I can’t believe we did it!" Roy whispered, feeling very satisfied, but also somewhat shocked.
They quickly used their sleuthing skills to find the ‘basketball crew’ and ‘tennis mates’ in Johnny’s contacts. They jotted down the numbers and felt very clever for having bypassed the phone's security. However, as they watched Johnny sleep, they started to feel rather uncomfortable. If Roy could get in so easily, anyone who looked like him, or Johnny, could access Johnny’s private messages and photos.
That evening after a BBQ dinner, Olivia, Jack and Roy decided to confess. They told Johnny and their parents about their afternoon experiment.
"We need to tell you that we found a flaw in the phone's security," Olivia explained. They showed everyone how Roy’s face had unlocked his brother Johnny’s device.
Their parents listened attentively. "We understand why you did it for the party," their father said, "but this shows why we
have to be so careful with our technology. Biometrics like Face ID are convenient, but they aren't a perfect shield."
Johnny admitted, "I thought my phone was unhackable, but it wasn't. It’s a bit scary to think how easily someone could see my private things."
The cousins soon realised that, while their trick had helped the party, it was a serious reminder about digital safety. Their parents helped Johnny update his settings to be more secure.
"And remember," their mother added, "technology is a wonderful tool, but we must always use it safely and respect each other's privacy."
Olivia, Jack, Roy and Johnny all felt more secure knowing they understood the risks better. They enjoyed the rest of their summer holiday, but with a newfound understanding of the need for strong passwords and extra protection.
Using your face to unlock your device is fast, but it’s important to use it wisely to keep your information private.
• Turn on ‘Require Attention’. Always make sure this setting is enabled. It ensures the phone only unlocks if your eyes are open and looking at the screen. This stops people from unlocking it while you are asleep.
• Sibling caution. If you have a twin or a sibling who looks very much like you, be

aware that Face ID might struggle to tell you apart. In these cases, using a strong passcode is much safer.
• Use a strong backup passcode. Don't use numbers like 1234 or your birthday that are easy to guess. If Face ID fails or is bypassed, your passcode is your final line of defence.
• The quick lockdown. On most phones pressing the power button five times quickly will disable Face ID and force the phone to ask for a passcode. Use this if you feel you are in an unsecure area.
• Keep sensors clean. Dust or smudges on the camera can make the face recognition less accurate. Wipe the top of your screen regularly with a soft cloth.
• Update your software. Companies constantly release security updates to make Face ID harder to trick. Always install the latest updates on your device.
www.linkedin.com/in/lisarothfield-kirschner
howwegotcybersmart.com














1. JAIMEE MULLINS
Technical Consultant, Saepio Information Security
2. AMANDA-JANE TURNER
Author of the Demystifying Cybercrime series and Women in Tech books. Conference Speaker and Cybercrime specialist
3. JACKIE ORCHARD
Head of Information and Data Security Advisory, Team Global Express
4. MEEGAN BRYANT
Defence Security Consultant
5. NADIA VEERAN-PATEL
LRMG as the CISO
6. HAJAR NACHATE
Chief Information Security Officer (CISO IT/OT)
7. KOKETSO RIHLAMPFU
Senior Manager: Lead Information Security Officer
8. LAURA JONES
CISO at Transdev Australasia
9. ERIN BLANCHARD
Technology Risk Consulting Vacationer
10. CLEO FAUL
Consultant (KPMG)
11. CRAIG FORD
Head Unicorn – Cofounder and Executive Director, Cyber Unicorns. Australian Best Selling Author of A Hacker I Am, Foresight and The Shadow World book series. vCISO – Hungry Jacks, Wesley Mission, PCYC and Baidam Solutions
12. ADRIANA JONES
Engineer, Cybersecurity Advocate and founder of The Innocent Souls Project (TISP)
13. JO STEWART-RATTRAY
Oceania Ambassador, ISACA
14. LISA VENTURA MBE FCIIS
Chief Executive and Founder, Unity Group Solutions Limited/AI and Cyber Security Association












15. SIMON CARABETTA
National Cyber Security Training Advisor
16. DEARNE MCWHIRTER
Associate Director (KPMG)
17. JAY HIRA
Cyber Director – Financial Services, KPMG
18. KAREN STEPHENS
CEO and co-founder of BCyber
19. MARINA AZAR TOAILOA
Founder of the Mummy Safety Security Project
20. MADHURI NANDI
Madhuri Nandi, Head of security at Nuvei, AWSN Board Chair, author of Cyber Smart
21. SIENNA SMITH
Bachelor of Information Technology with a major in Cybersecurity student at Charles Sturt University
22. USWAH RAHMAN
Cybersecurity and Behaviour student at Western Sydney University
23. UGWOKE JENNIFER SOCHIMA
Cyber Security Instructor
24. OM VENUGOPAL
Master of Engineering in Cybersecurity graduate at the University of Maryland, USA
25. LETHABO SANGWENI
Computer Science Student at the University of Western Cape
26. LISA ROTHFIELD-KIRSCHNER
Author of How We Got Cyber Smart | Amazon Bestseller
CYBER MANAGEMENT ALLIANCE BLOG
By Cyber Management Alliance Blog
Cyber Security blog features articles, surveys, research and all things related to information security and data privacy including methods, technology and resources.

By Bleeping Computer
The latest Technology and Security News to help you stay informed and protected on the Net. BleepingComputer is a premier destination for computer users of all skill levels to learn how to use and receive support for their computers.

UNDERSTANDING VULNERABILITIES
ACROSS MODERN CYBERPHYSICAL SYSTEMS
By Claroty Blog
Vulnerability management of cyberphysical systems (CPS) is one of the most frustrating challenges for enterprise security and networking teams, whose CPS protection efforts are often hampered on several fronts:

ENTERPRISE WI-FI: THE MOST TRUSTED ATTACK SURFACE YOU’RE NOT TESTING (AND HOW TO FIX THAT)
By Hack The Box Blog
Some security teams out there like to believe that the perimeter is gone. That everything important lives tucked behind identity controls, conditional access, and layers of cloud-native defense. The assumption is that if credentials are protected and endpoints are hardened, the rest will follow.

By Cloudbric
Cloudbric provides free website security for everyone. Cloudbric aims to bring mainstream enterprise level website security to small and medium businesses. Cloubric's blog aims to provide readers with the latest company news and trending infosec topics.

2026 SCAM
WHAT’S CHANGED, WHAT’S THE SAME & HOW TO STAY SAFE
By CyberCX Blog
Scams have become the reality we can’t ignore with every Australian likely receiving one in some form. As cyber criminals grow more sophisticated, leveraging generative AI and cutting-edge tech, spotting scams has become trickier than ever.
AN OPEN LETTER ON SECURITY, SOVEREIGNTY, AND THE RIGHT TO CHOOSE
By LogPoint' Blog
For security leaders, service providers, and public sector organizations, this is no longer theoretical. It shows up in audits, procurement processes, customer contracts, and board-level risk discussions. At Logpoint, we see this every day.

HOW DOES IDENTITY THEFT MONITORING WORK?
By IdentityIQ
In broad terms, identity theft monitoring is a service provided by private companies to help protect you from identity theft. While the details vary between services, they involve monitoring your identity in several different areas to identify risks and look for signs of fraud.

RANSOMWARE ENTRY POINTS ARE CHANGING. HERE IS WHAT TO DO ABOUT IT?
By CyberHoot Blog
Ransomware groups are not breaking in organizations the same way they did five years ago. The entry methods have shifted, and understanding that shift is one of the most useful things you can do to protect your organization right now.

LYING TO YOURSELF)
By CodeLivly
It’s either intimidating technical jargon from experts who forgot what being a beginner feels like, or empty hype from influencers selling you a dream. You’re told to “just learn to hack” while job postings demand 3 years of experience for entry-level roles.

CYBER SCHOLARSHIPFOR-SERVICE STUDENTS SAY GOVERNMENT HAS PULLED RUG ON THEM, POTENTIALLY BURDENING THEM WITH DEBT
By CyberScoop
A landmark program that offers scholarships in exchange for federal service is threatening to saddle students with hundreds of thousands of dollars worth of debt amid hiring freezes and budget cuts, raising questions about the future of an initiative proponents say has helped close the government’s cyber workforce gap.

INTRODUCING "AI
UNLOCKED: DECODING
PROMPT INJECTION," A NEW INTERACTIVE CHALLENGE
By CrowdStrike Blog
This immersive simulation is designed to help security teams better understand the prompt injection threat landscape by putting them in the attacker’s seat. Players are challenged to progress through three virtual rooms by using prompt injection techniques to convince the room’s supervisor, SAIGE, to reveal secret phrases that allow them to move forward.

With Dark Rhiino Security Security Confidential provides weekly interviews and insights into the world of cybersecurity. Produced entirely in-house by MSSP & global risk management firm Dark Rhiino Security.

With Laurens Jagt
The interview podcast for cyber security professionals and for those who aspire to become one. We interview industry experts about the latest trends, real life war stories and everything you need to know about this exciting industry.

With Jessica Hoffman SC Media and Saviynt are proud to present this month's CISO Stories program, where CISOs share tales from the trenches and unpack leadership lessons learned along the way. Hosted by Jessica Hoffman.

With Stephanie Itimi Seidea's Spotlight sheds light on the journeys of Black, Minority Ethnic women who are changing the face of cybersecurity. Through powerful interviews with bootcamp graduates and industry leaders, we explore the challenges and triumphs BME women face in this dynamic field. Join us as we uncover career advice, build a community of support, and celebrate the rise of a cyber sisterhood breaking down barriers and forging a brighter future in tech.

With Dani Middleton-Wren Cybersecurity Sessions is an insightful monthly podcast covering the latest cybersecurity news and hot topics, featuring security leaders from Netacea alongside other technology experts.At Netacea we are interested not just in the technology behind cyber-attacks, but also the intent. How do they affect different businesses, sectors, and even wider society? What stories are out there of cybersecurity woes and wins?
With Rachael Lyon, Vince Spina and Eric Trexler
Stay ahead in the dynamic world of cybersecurity with 'To the Point Cybersecurity.' This podcast offers in-depth discussions on the latest cyber threats, trends, and technologies impacting businesses, governments, and communities globally.Listeners will gain insights into how emerging technologies, such as AI and frameworks like data governance and expanded global cyber regulations, are shaping modern security practices

With Christopher Okpala
Most people are trying to break into cybersecurity the wrong way.
In this episode of Tech Woke, I sit down with Destini Simmons (Cyber Shorty), Solutions Engineer, to break down what it really takes to enter cybersecurity in 2026 with no experience.

With Alice Violet Humans are the weakest link in cybersecurity.' We disagree and we're here to change the narrative. Subscribe for monthly episodes.

With Holly Grace Williams
Hacked Off demystifies the world of cybersecurity. Hosted by Secarma's Managing Director, Holly Grace Williams, it features weekly interviews delving beneath the headlines of the latest hacks, breaches and vulnerabilities, providing expert advice on how to stay safe online. This podcast is brought to you by global cybersecurity and penetration testing company, Secarma.

With Karissa Breen
Unlike every other security podcast, we don't get stuck down in the technical weeds. Our remit is to speak with experts around the globe at the strategic level how security technology can improve the experience and risk optimisation for every organisation. The Voice of Cyber® - In Partnership with Vanta

With AUSCERT Anthony Caruana and Bek Cheb
AUSCERT is Australia's pioneer Cyber Emergency Response Team, proudly a part of The University of Queensland. We help our members prevent, detect, respond and mitigate cyber-based attacks.

With Momentum Media
Cyber Uncut brings you the key decision makers and cutting edge innovators shaping Australia's cyber revolution. From cyber security to artificial intelligence and information systems, discover how businesses and government are navigating the transition to a digital future.

Author // Lida
The Digital Battle Cyber Security attempts to assist consumers by suggesting cyber security measures to protect PII, intellectual property, and critical infrastructure from compromise. To prevent exploitation, consumers need vigilance paired with knowledge.
THE BOOK
Authors // Ira Winkler and Tracy Celaya Brown
Around the world, users cost organizations billions of dollars due to simple errors and malicious actions. They believe that there is some deficiency in the users. In response, organizations believe that they have to improve their awareness efforts and making more secure users. This is like saying that coalmines should get healthier canaries.

Authors // Dr Jessica Barker
Confident Cyber Security is here to help. From the human side to the technical and physical implications, this book takes you through the fundamentals: how to keep secrets safe, how to stop people being manipulated and how to protect people, businesses and countries from those who wish to do harm.
Author // Mindy Seu
Hackers, scholars, artists and activists of all regions, races and sexual orientations consider how humans might reconstruct themselves by way of technology. When learning about internet history, we are taught to focus on engineering, the militaryindustrial complex and the grandfathers who created the architecture and protocol.

Author // Jonathan Brill and Stephen Wunker
In AI and the Octopus Organization: Building the Superintelligent Firm, leading futurist Jonathan Brill and innovation expert Stephen Wunker unveil a groundbreaking vision for how organizations must evolve to survive and thrive in the age of artificial intelligence.
BUY THE BOOK
Author // Lance Hayden
People-Centric Security: Transforming Your Enterprise Security Culture addresses the urgent need for change at the intersection of people and security. Esentially a complete security culture toolkit, this comprehensive resource provides you with a blueprint for assessing, designing, building, and maintaining human firewalls.
BUY THE BOOK
Authors // Agathe Merle
Cyber Like a Girl is a powerful exploration of what it means to build a career in cybersecurity as a woman-against the odds and with purpose. Author Agathe Merle never planned to work in cybersecurity. Nearly a decade later, she's not only built deep technical expertise, particularly in Security Operations, but also observed the industry through the lens of a researcher, woman, and insider.
Author // Lyron Foster | Illustrator // Lauren Foster
This book is an action-packed adventure that takes readers on a journey through the world of technology and crime-solving. The story follows Alexis, a young girl hacker with a love for Japanese snacks, and her best friend Tania as they navigate the challenging world of cybercrime in their hometown of Hilo, Hawaii. Together, they solve a series of complex and thrilling cases that require their expertise in technology and quick thinking to unravel.
Author // Arthi Vasudevan | Illustrator // Jasmin Sorto
In this middle grade adventure book about cyber safety, Maya, Dave, and their AI animals are plunged back into the high-stakes cyberworld where digital dangers are all too real.
“I couldn’t put the book down. I read it in one day as it’s as good as Percy Jackson. I really liked Cyber Panda and Maya. An amazing book with a wonderful story.”
Authors // Nina Du Thaler
Lizzy’s Triumph Over Cyber-Bullying is a heartfelt and empowering story that helps children understand the emotional impact of cyberbullying—and how to overcome it. Told through the diary of Elle, a smart and caring 10-year-old, this book follows her best friend Lizzy as she navigates the pain of being bullied online and learns how to take back control with the help of trusted friends, family, and teachers.

Author // Dr Dheeraj Mehrotra
This is to provide further insight into the concerns about the same. It is more necessary; Kids should be educated about cyber security early because the skills they gain will help safeguard them as they age and experience more digital hazards. The main reason for this is because it is more required. I do not doubt that the book will serve as a manual for all parties investigating the concept.
Author // Christian Blake
What if your computer could be in two places at once?
The Magic Coin introduces children ages 8-12 to quantum computing using only everyday analogies they already understand. No math. No jargon. Just spinning coins, spooky best friends, and ice castles.

Get on the fast track to a career in cybersecurity. In this certificate program, you'll learn in-demand skills, and get AI training from Google experts. Learn at your own pace, no degree or experience required.


This program equips aspiring cybersecurity professionals, SOC analysts, network engineers, and system administrators with the foundational knowledge and practical skills required to understand, analyze, and defend against modern cyber threats in enterprise environments.


During the course, you’ll learn to identify common threats such as data theft, tampering, phishing, and malware. You’ll discover how cyberattacks unfold and explore the physical, environmental, and access control measures used to secure devices and facilities. Plus, you’ll develop strong digital hygiene habits using secure passwords, password management techniques, and multi-factor authentication, and understand the risks of password reuse, sharing, and default credentials.
Homeland security is about safeguarding the United States from domestic catastrophic destruction. Cybersecurity has emerged as a priority homeland security concern because a coordinated cyber attack against critical infrastructure could result in the worst catastrophe in the nation’s history.







Cybersecurity affects everyone, including in the delivery of basic products and services. If you or your organization want to better understand how to address your cybersecurity, this is the course for you and your colleagues to take -- from seasoned professionals to your nontechnical colleagues.
VISIT HERE
Each course includes a case study that will require students to put into practice the knowledge they have gained throughout each course. Successful completion of course projects will require the basic understanding of the topics covered and the ability to relate those topics to the real world. The objective of each project is to determine whether students have understood course concepts and are able to use them in a real world setting.
VISIT HERE
This specialization provides comprehensive training in cybersecurity operations, risk assessment, and strategic risk management, equipping learners with the skills to identify, analyze, and mitigate modern cyber threats.
VISIT HERE

This Specialization is designed for post-graduate students aiming to master AI applications in cybersecurity. Through three comprehensive courses, you will explore advanced techniques for detecting and mitigating various cyber threats. The curriculum covers essential topics such as AI-driven fraud prevention, malware analysis, and the implications of Generative Adversarial Networks (GANs).
VISIT HERE

The CompTIA Cybersecurity Analyst+ (CySA+) Specialization prepares you to detect, analyze, and respond to cybersecurity threats. Guided by industry expert Aamir Lakhani, this course covers essential topics such as attack methodologies, incident response, and vulnerability management.



This Specialization can be taken by students, IT professionals, IT managers, career changers, and anyone who seeks a cybersecurity career or aspires to advance their current role. This course is ideal for those entering the cybersecurity workforce, providing foundational, hands-on skills to solve the most common security issues organizations face today.
With this program, you can prepare for the Microsoft Cybersecurity Analyst SC-900 certification exam administered by Microsoft. Learners who complete this program will receive a 50% discount voucher to take the exam. Organizations rely on cybersecurity experts to protect themselves from threats, but nearly 60% of organizations report security talent shortages (1). Prepare for a new career in this high-demand field with professional training from Microsoft — an industry-recognized leader in cybersecurity. You'll also have the option to learn how generative AI tools and techniques are used in cybersecurity analysis.

Cybersecurity is an essential business skill for the evolving workplace. For-profit companies, government agencies, and not-for-profit organizations all need technologically proficient, business-savvy information technology security professionals.



Most organizations plan for routine operations, but what happens when unexpected events overtake the routine? This course examines contingency planning used to prepare for and manage non-normal operations, including cybersecurity incidents – like hacking attempts, web site defacement, denial of service attacks, information disclosures; a well as other natural and man-made cybersecurity disasters.
The no-cost curriculum includes all courses to support security-driven networking, adaptive cloud security, AI-driven security operations and zero-trust network access. Completion of these courses will help cybersecurity professionals defend their networks against the widest range of ever changing threats.
In the Secure Coding 101: JavaScript Module, you will learn how to improve the security of your JavaScript code through reverse engineering advanced JavaScript obfuscation functions and identifying hard to find vulnerabilities, and learning how to patch them properly.

In this course, you’ll learn key skills and tools for data analytics, including spreadsheets, structured query language (SQL), R programming, and Tableau. You will also understand the daily tasks of a data analyst and explore the kinds of jobs you could pursue after completing this program.


FULL TIME INDIA
RESPONSIBILITIES
• Monitor, triage, and respond to security incidents using alerts and incidents from Microsoft Defender products (MDE, MDI, MDO, MDA, MDC, Sentinel etc.)
• Perform proactive threat hunting using hypothesis, and telemetry from endpoints, identities, cloud and network.
• Develop hunting queries using Kusto Query Language (KQL) or similar to uncover suspicious patterns and behaviours.
• Investigate security incidents across hybrid environments and contribute to root cause analysis and containment strategies.



• Collaborate with internal teams (defender, threat intelligence, engineering) to enhance detection logic, develop automations, and improve incident response workflows.
• Contribute to incident documentation, detection playbooks, and operational runbooks.
• Stay current with evolving threat landscapes, cloud attack vectors, and advanced persistent threats (APT).
• Develop necessary automation (e.g. using Jupyter Notebooks) to scale Threat Hunting.
FULL TIME AUSTRALIA
YOUR KEY RESPONSIBILITIES

This is an exciting period in the adoption of the technology with incoming regulation set to provide certainty for companies who’ve been sitting on the sidelines. You will have the opportunity to build on your strong Risk and Control skills and enthusiasm for digital assets by working with some of the most innovative companies and vendors within Oceania and globally through EY’s global blockchain network. You will be given all the skills, knowledge, and exciting learning opportunities to build your career, and the chance to make a real impact.
FULL TIME NEW ZEALAND
POSITION SUMMARY & PRIMARY OBJECTIVES
• The Senior Consultant is an experienced cyber security professional capable of leading client meetings and producing high-quality deliverables with minimal supervision.
• There is the potential for this role to develop into a LEAD for our IR tabletop engagements if that was an avenue of interest.
KEY ROLES & RESPONSIBILITIES
• Lead discovery activities with client stakeholders to inform deliverables and shape client outcomes
• Support the development of cyber security strategies and solutions to protect clients and their customers
• Facilitate cyber security awareness amongst our clients’ leadership teams
• Produce high-quality proposals, reports, and presentations for senior client stakeholders

• Manage client expectations, communicate effectively, and develop professional relationships with clients
• Prepare clients for critical cyber security incidents through contributing to their cyber security strategic direction




PART TIME AUSTRALIA
ROLE RESPONSIBILITIES
• Evaluate and assess content for potential security concerns in a cutting-edge AI context.
• Review and analyze security patterns to enhance AI model security.
• Collaborate asynchronously with a team of experts to solve real-world cybersecurity problems.
• Utilize Python and other data analysis tools to interact with large databases.



• Work independently to improve AI model performance and security analysis.
FULL TIME CANADA
WHAT YOU’LL BE DOING
Reporting to the Senior Manager, Operational Threat Intelligence, the Analyst, Operational Threat Intelligence is responsible for tactical level information and intelligence collection, analysis, and production. This effort is geared predominantly towards protecting CIBC’s clients, assets, staff, and operations through the delivery of proactive intelligence across the cyber, financial, geopolitical, and physical security domains. The Analyst leverages knowledge and robust experience with intelligence methodologies to advance the Fusion Threat Intelligence program and deliver best in class intelligence products.

At CIBC we enable the work environment most optimal for you to thrive in your role. You'll have the flexibility to manage your work activities within a hybrid work arrangement where you’ll spend 1-3 days per week onsite, while other days will be remote.
FULL TIME SOUTH AFRICA
• Driving Product Innovation: Serve as the primary analytical counterpart to product teams, contributing critical insights that inform the development of cutting-edge features and help shape the future of our digital experience.
• Unlocking User Insights: Analyze user behavior and feedback to identify patterns, uncover friction points, and translate findings into actionable recommendations that improve product usability, engagement, and satisfaction.
• Defining Success: Design clear, scalable performance frameworks and KPIs that enable teams to track progress, evaluate product outcomes, and align efforts across disciplines.

• Scaling Experimentation: Build and champion experimentation frameworks, methodologies, and tools that empower product teams to test hypotheses rigorously and iterate with confidence.
• Fostering a Data-Centric Culture: Advocate for datainformed thinking across the organization, promoting best practices and ensuring that product decisions are consistently grounded in evidence and insight.
FULL TIME UNITED KINGDOM
We’re focused on the security of AI systems themselves, examining how modern models can be attacked, misused, or pushed beyond their intended boundaries. You will work with realistic scenarios to help ensure AI systems remain safe, reliable, and aligned with security best practices.
• Organization: Alignerr
• Position: AI / Emerging Tech Security Analyst Type: Contract / Task-Based
• Compensation: $40–$60 /hour
• Location: Remote Commitment: 10–40 hours/week



• Analyze AI and LLM security scenarios to understand how models behave under adversarial or unexpected conditions
• Review prompt injection, data leakage, model abuse, and system misuse cases
• Classify security issues and appropriate mitigations based on real-world impact and likelihood
• Help evaluate and improve AI system behavior so it remains safe, reliable, and aligned with security best practices
FULL TIME SOUTH KOREA
As a member of this dynamic team, you will dive deep into the world of advanced browser technologies, particularly Chromium. You'll play a critical role in modifying and extending Chromium modules to support the full suite of Netskope Enterprise Browser functionalities. Expect to work with cuttingedge technologies such as C++ and gRPC services, and to tackle complex challenges in distributed systems—ranging from performance optimization and scalability to high availability, containerization, and advanced analytics.
FULL TIME ITALY
• Digital Transformation: PwC Italy focuses on driving digital transformation for its clients through advisory and consulting services in areas such as deals, risk, analytics, and program management.
• Market Insights and Research: PwC Italy provides updated and informed macroeconomic insights and market reports, such as the Real Estate

• Modify and enhance the Chromium engine to support new features.
• Using advanced data structures and algorithms in C++
• Researching optimization algorithms and improving performance
• Solving problems with quick and elegant solutions APPLY

Healthcare Market Report, to help clients navigate economic conditions and investment dynamics.




FULL TIME NIGERIA
ROLE OVERVIEW
The Senior Transaction & Fraud Optimization Analyst will lead daily transaction monitoring, fraud risk optimization, routing strategy enhancement, and executive reporting development. This role requires hands-on expertise in Fraud.net, strong knowledge of payment routing logic, and advanced analytics capabilities within fin-tech or payment processing environments.



KEY RESPONSIBILITIES
Transaction Analysis and Monitoring
• Analyze daily transaction volumes, approval rates, declines, charge-backs, and fraud ratios.
• Identify patterns, anomalies, and performance gaps.
• Deliver actionable insights to increase authorization rates and reduce false declines.
FULL TIME SPAIN
ROLE OVERVIEW
You will engage in a service that is responsible for the coordination and execution of the Top Cyber Threat Assessment for all Allianz Entities (70+). This role is part of the Resilience as a Service division, acting within it as a micro-cluster performing cyber threat assessments and Cyber Risk Quantifications (CRQs).
WHAT YOU DO
• Manage and maintain the cyber risk quantification model in collaboration with the vendor
• Regularly analyze and validate input data and model results

• Support the delivery of cyber risk quantification services provided to clients globally
• Evaluation and presentation of model results
• Analysis and coordination of model changes in collaboration with the vendor
• Provide functional support for an internal platform, including conception and testing of functional requirements
• Conduct training sessions and provide functional support for tool user
• Prepare, revise, and maintain relevant documentation
FULL TIME UNITED ARAB EMIRATES
JOB SUMMARY
We are seeking a highly senior L3 Network Engineer / Network Architect with 8–10 years of hands-on enterprise experience to provide architecture-level support, lead complex network designvalidation,and drive network optimization, security posture, and availability improvements across enterprise and hybrid cloud environments.

The role requires CCIE-level expertise, deep Azure networking skills at L3 level, and strong leadership in critical escalations, Zero Trust implementation, and governance.
We need your support to continue this important initiative into its 8th year.

JOIN US IN MELBOURNE FOR 2026
The 2026 Awards will be hosted in Melbourne. To ensure this initiative continues, we invite you to partner with us as a sponsor.
Your sponsorship will help us continue to celebrate and elevate the achievements of women in security across Australia.
Packages available from $6,000 to $50,000 Custom packages tailored to your organisation’s needs
To discuss how you can support and sponsor next year’s awards, please reach out to Aby at Aby@source2create.com.au .
We look forward to partnering with you to make the 2026 Australian Women in Security Awards our best yet.