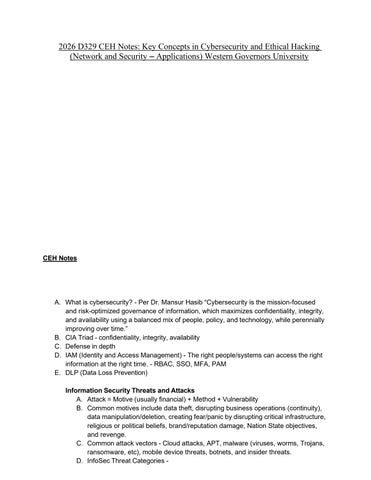
2026 D329 CEH Notes: Key Concepts in Cybersecurity and Ethical Hacking (Network and Security – Applications) Western Governors University
CEH Notes
A. What is cybersecurity? - Per Dr. Mansur Hasib “Cybersecurity is the mission-focused and risk-optimized governance of information, which maximizes confidentiality, integrity, and availability using a balanced mix of people, policy, and technology, while perennially improving over time.” B. CIA Triad - confidentiality, integrity, availability C. Defense in depth D. IAM (Identity and Access Management) - The right people/systems can access the right information at the right time. - RBAC, SSO, MFA, PAM E. DLP (Data Loss Prevention) Information Security Threats and Attacks A. Attack = Motive (usually financial) + Method + Vulnerability B. Common motives include data theft, disrupting business operations (continuity), data manipulation/deletion, creating fear/panic by disrupting critical infrastructure, religious or political beliefs, brand/reputation damage, Nation State objectives, and revenge. C. Common attack vectors - Cloud attacks, APT, malware (viruses, worms, Trojans, ransomware, etc), mobile device threats, botnets, and insider threats. D. InfoSec Threat Categories -