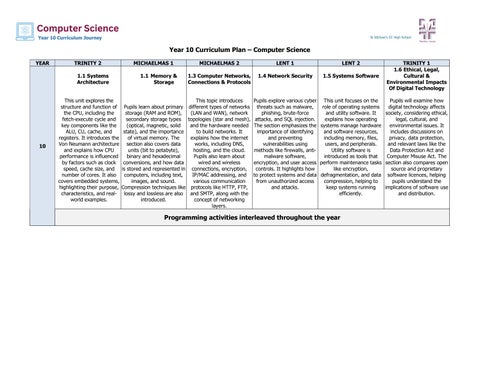
Year 10 Curriculum Plan – Computer Science YEAR
TRINITY 2 1.1 Systems Architecture
10
MICHAELMAS 1 1.1 Memory & Storage
MICHAELMAS 2
LENT 1
LENT 2
1.3 Computer Networks, Connections & Protocols
1.4 Network Security
1.5 Systems Software
TRINITY 1 1.6 Ethical, Legal, Cultural & Environmental Impacts Of Digital Technology
This unit explores the This topic introduces Pupils explore various cyber This unit focuses on the Pupils will examine how structure and function of Pupils learn about primary different types of networks threats such as malware, role of operating systems digital technology affects the CPU, including the storage (RAM and ROM), (LAN and WAN), network phishing, brute-force and utility software. It society, considering ethical, fetch-execute cycle and secondary storage types topologies (star and mesh), attacks, and SQL injection. explains how operating legal, cultural, and key components like the (optical, magnetic, solid and the hardware needed The section emphasizes the systems manage hardware environmental issues. It ALU, CU, cache, and state), and the importance to build networks. It importance of identifying and software resources, includes discussions on registers. It introduces the of virtual memory. The explains how the internet and preventing including memory, files, privacy, data protection, Von Neumann architecture section also covers data works, including DNS, vulnerabilities using users, and peripherals. and relevant laws like the and explains how CPU units (bit to petabyte), hosting, and the cloud. methods like firewalls, antiUtility software is Data Protection Act and performance is influenced binary and hexadecimal Pupils also learn about malware software, introduced as tools that Computer Misuse Act. The by factors such as clock conversions, and how data wired and wireless encryption, and user access perform maintenance tasks section also compares open speed, cache size, and is stored and represented in connections, encryption, controls. It highlights how like encryption, source and proprietary number of cores. It also computers, including text, IP/MAC addressing, and to protect systems and data defragmentation, and data software licences, helping covers embedded systems, images, and sound. various communication from unauthorized access compression, helping to pupils understand the highlighting their purpose, Compression techniques like protocols like HTTP, FTP, and attacks. keep systems running implications of software use characteristics, and real- lossy and lossless are also and SMTP, along with the efficiently. and distribution. world examples. introduced. concept of networking layers.
Programming activities interleaved throughout the year