
0. Implementation Resources
1. Firewalls
2. Secure Configuration
3. Security update management
4. User access control
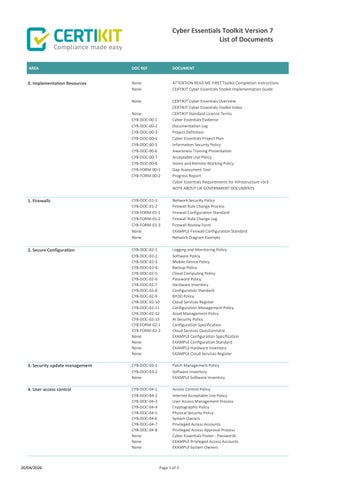

0. Implementation Resources
1. Firewalls
2. Secure Configuration
3. Security update management
4. User access control
None
ATTENTION READ ME FIRST Toolkit Completion Instructions
None CERTIKIT Cyber Essentials Toolkit Implementation Guide
None
CERTIKIT Cyber Essentials Overview
CERTIKIT Cyber Essentials Toolkit Index
None CERTIKIT Standard Licence Terms
CYB-DOC-00-1 Cyber Essentials Evidence
CYB-DOC-00-2 Documentation Log
CYB-DOC-00-3 Project Definition
CYB-DOC-00-4 Cyber Essentials Project Plan
CYB-DOC-00-5 Information Security Policy
CYB-DOC-00-6 Awareness Training Presentation
CYB-DOC-00-7
Acceptable Use Policy
CYB-DOC-00-8 Home and Remote Working Policy
CYB-FORM-00-1 Gap Assessment Tool
CYB-FORM-00-2 Progress Report
Cyber Essentials Requirements for Infrastructure v3r3
NOTE ABOUT UK GOVERNMENT DOCUMENTS
CYB-DOC-01-1
Network Security Policy
CYB-DOC-01-2 Firewall Rule Change Process
CYB-FORM-01-1 Firewall Configuration Standard
CYB-FORM-01-2 Firewall Rule Change Log
CYB-FORM-01-3
None
None
CYB-DOC-02-1
CYB-DOC-02-2
Firewall Review Form
EXAMPLE Firewall Configuration Standard
Network Diagram Example
Logging and Monitoring Policy
Software Policy
CYB-DOC-02-3 Mobile Device Policy
CYB-DOC-02-4
Backup Policy
CYB-DOC-02-5 Cloud Computing Policy
CYB-DOC-02-6 Password Policy
CYB-DOC-02-7 Hardware Inventory
CYB-DOC-02-8
Configuration Standard
CYB-DOC-02-9 BYOD Policy
CYB-DOC-02-10 Cloud Services Register
CYB-DOC-02-11
Configuration Management Policy
CYB-DOC-02-12 Asset Management Policy
CYB-DOC-02-13 AI Security Policy
CYB-FORM-02-1
Configuration Specification
CYB-FORM-02-2 Cloud Services Questionnaire
None
None
None
None
CYB-DOC-03-1
CYB-DOC-03-2
None
CYB-DOC-04-1
CYB-DOC-04-2
CYB-DOC-04-3
EXAMPLE Configuration Specification
EXAMPLE Configuration Standard
EXAMPLE Hardware Inventory
EXAMPLE Cloud Services Register
Patch Management Policy
Software Inventory
EXAMPLE Software Inventory
Access Control Policy
Internet Acceptable Use Policy
User Access Management Process
CYB-DOC-04-4 Cryptographic Policy
CYB-DOC-04-5 Physical Security Policy
CYB-DOC-04-6 System Owners
CYB-DOC-04-7
CYB-DOC-04-8
None
None
Privileged Access Accounts
Privileged Access Approval Process
Cyber Essentials Poster - Passwords
EXAMPLE Privileged Access Accounts
None EXAMPLE System Owners
CYB-DOC-05-1
CYB-DOC-05-2
CYB-DOC-05-3
CYB-DOC-05-4
CYB-DOC-05-5
CYB-DOC-05-6
CYB-DOC-05-7
None
Anti-Malware Policy
Electronic Messaging Policy
Incident Response Plan Ransomware
Threat Intelligence Policy
Incident Response Plan Data Breach
Incident Management Policy
Privacy and Personal Data Protection Policy
Cyber Essentials Poster - Phishing