


Analog Devices’ commercial off-the-shelf (COTS) software-defined radio (SDR) system-on-module (SOM) digitizers enable customers to deploy high performance distributed sensing techniques at the tactical edge, as quickly as possible.
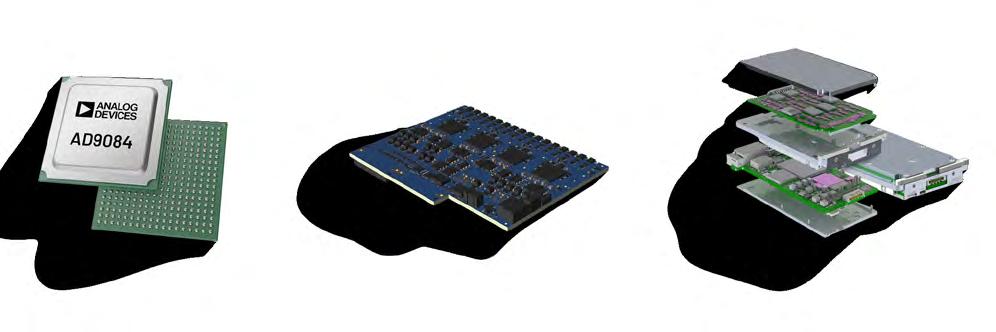





LCR is at the forefront of COTS open standards chassis and custom system designs for VPX, CMOSS, and SOSA architectures in accordance with MOSA directives. Intelligently engineered designs that bring operational advantage to the battlefield.
Find out how we can help you achieve mission success.
SERVING CRITICAL DEFENSE PROGRAMS FOR OVER 35 YEARS


Editor’s
7 MOSA and acquisition speed
By John M. McHale III
with


WEB RESOURCES
Subscribe to the magazine or E-letter
Live industry news | Submit new products http://submit.opensystemsmedia.com
WHITE PAPERS – Read: https://militaryembedded.com/whitepapers
WHITE PAPERS – Submit: http://submit.opensystemsmedia.com


SPECIAL REPORT: Counter-UAS technology
8 How small business and the war on terror supercharged autonomy By Bryan
Bockmon,
AimLock
10 Engineering resilience: Multi-layer conflict avoidance for military and commercial drones in shared airspace By Dawn Zoldi, P3 Tech Consulting
MIL TECH TRENDS: Enabling AI capability in autonomous systems
12 COTS edge AI accelerators – an enabler for military autonomous systems in all domains, including space By Stanley Crow, EdgeCortix
16 Autonomous AI acceleration requires hardware design to evolve By Drew Thompson, Sealevel Systems
INDUSTRY SPOTLIGHT: MOSA solutions for autonomous systems: SBCs, RTOS, connectors, backplanes, etc.
20 Why autonomy upgrades stall at integration – and how MOSA fixes it By Dan Taylor, Technology Editor
24 From single-band fragility to adaptive spectrum control By Ashish Parikh, Doodle Labs
28 The future of autonomy will integrate aerial and ground systems By Dr. James Crowell, Crow Industries
©
To unsubscribe, email your name, address, and subscription number as it appears on the label to: subscriptions@opensysmedia.com
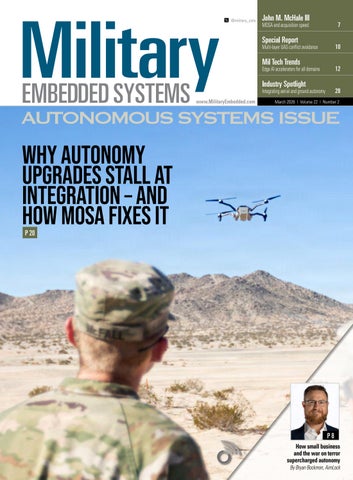
ON THE COVER:
A drone operator with 1st Battalion, 8th Cavalry Regiment, flies a Black Widow small uncrewed aerial system (UAS) in preparation for a National Training Center rotation at Fort Irwin, California. The rotation – a rigorous 21-to-30-day, large-scale training exercise for U.S. Army brigade combat teams – provides troops with realistic training scenarios to enhance unit readiness and interoperability. U.S. Army photo by 1st Lt. Tyler Williams.



Sea-Air-Space 2026
April 19-22, 2026
National Harbor, MD
https://seaairspace.org/
AUVSI Xponential 2026
May 11-14, 2026 Detroit, MI
https://xponential.org
SOF Week 2026
May 18-21, 2026 Tampa, FL
https://sofweek.org/
IEEE International MTT Symposia (IMS)
June 7-12, 2026
Boston, MA
https://ims-ieee.org/ims2026-boston
GROUP EDITORIAL DIRECTOR John McHale john.mchale@opensysmedia.com
ASSISTANT MANAGING EDITOR Lisa Daigle lisa.daigle@opensysmedia.com
TECHNOLOGY EDITOR – WASHINGTON BUREAU Dan Taylor dan.taylor@opensysmedia.com
CREATIVE DIRECTOR Stephanie Sweet stephanie.sweet@opensysmedia.com
WEB DEVELOPER Paul Nelson paul.nelson@opensysmedia.com
EMAIL MARKETING SPECIALIST Drew Kaufman drew.kaufman@opensysmedia.com
WEBCAST MANAGER Marvin Augustyn marvin.augustyn@opensysmedia.com
VITA EDITORIAL DIRECTOR Jerry Gipper jerry.gipper@opensysmedia.com
DIRECTOR OF SALES Tom Varcie tom.varcie@opensysmedia.com (734) 748-9660
STRATEGIC ACCOUNT MANAGER Bill Barron bill.barron@opensysmedia.com (516) 376-9838
EAST COAST SALES MANAGER Bill Baumann bill.baumann@opensysmedia.com (609) 610-5400
SOUTHERN CAL REGIONAL SALES MANAGER Len Pettek len.pettek@opensysmedia.com (805) 231-9582
DIRECTOR OF SALES ENABLEMENT Barbara Quinlan barbara.quinlan@opensysmedia.com AND PRODUCT MARKETING (480) 236-8818
INSIDE SALES Amy Russell amy.russell@opensysmedia.com
STRATEGIC ACCOUNT MANAGER Lesley Harmoning lesley.harmoning@opensysmedia.com
EUROPEAN ACCOUNT MANAGER Jill Thibert jill.thibert@opensysmedia.com
EUROPEAN ACCOUNT MANAGER Michael O'Kane michael.okane@opensysmedia.com
TAIWAN SALES ACCOUNT MANAGER Patty Wu patty.wu@opensysmedia.com
CHINA SALES ACCOUNT MANAGER Judy Wang judywang2000@vip.126.com
CO-PRESIDENT Patrick Hopper patrick.hopper@opensysmedia.com
CO-PRESIDENT John McHale john.mchale@opensysmedia.com
DIRECTOR OF OPERATIONS AND CUSTOMER SUCCESS Gina Peter gina.peter@opensysmedia.com
GRAPHIC DESIGN MANAGER Kaitlyn Bellerson kaitlyn.bellerson@opensysmedia.com
FINANCIAL ASSISTANT Emily Verhoeks emily.verhoeks@opensysmedia.com
By John M. McHale III
The term “fast-moving” can describe many of the actions under the Trump Pentagon, whether you find them good or bad. Either way, they are happening quickly. Those shifts in Washington aligned with speeding up acquisition make me – and those who read this column – happy. That increase in momentum is starting with autonomous systems and is enabled by modular open systems approach (MOSA) strategies.
But is it fast enough? Technological advancement is moving incredibly fast, both in industry and with U.S. adversaries.
“We’re seeing it in in real life, I’ll say in Ukraine and in other areas around the world, where the technology changes on the battlefield on a monthly basis,” said Jacob Glassman, Deputy Assistant Secretary of War for Science & Technology, during our keynote session chat for our MOSA Virtual Summit, held February 26. “Things have only gotten exponentially faster and also the innovative capability of industry is absolutely staggering.”
Acquisition of autonomous systems, which have been force multipliers in Ukraine, is the first application area U.S. military leaders are looking at to speed up and remove bureaucratic barriers.
U.S. Department of Defense (DoD) Secretary Pete Hegseth said during summer 2025 that he wants to enable drone dominance by bolstering the “U.S. drone manufacturing base by approving hundreds of American products for purchase by our military.” In that memo, he also called for a new procurement strategy that speeds up small drone acquisition.
A big part of speeding up acquisition of drones and other technology will be the DoD being a better partner to industry, Glassman told me. “That’s not a political
John.McHale@opensysmedia.com
statement. It’s a philosophical push to understand that we need to be better customers. We have not been good customers.
“We want to be partners in all of this, which means proactive collaboration, not just with us, but with each other,” he added. “Business is cutthroat. I get it. That’s the nature of how we do things, and it’s actually not necessarily a bad thing. It’s healthy. However, for us to succeed as a department and really [as] an industry, we need to go faster. We need to be able to leverage the best from every corner of this innovation ecosystem, and the way to do that is to collaborate on consensus-based standards.”
MOSA will help the U.S. military move faster and get technology to the warfighter more quickly, Glassman asserted. “What I keep saying to my teams is you don’t win when you demonstrate something in a lab. You win when it’s in a warfighter’s hands. It’s either on a submarine, it’s on an aircraft, it’s on a spacecraft, it’s in cyberspace, wherever the application is, that’s when you win. So how do you bridge that gap –that’s where MOSA really comes in.
“In the private and commercial world, if you’re two or three years to market, you’re a dinosaur, you’re gone, you’re dead,” Glassman told me. “Well, unfortunately, the same thing works for us, except the stakes are significantly higher, not Chapter 11. MOSA is where we are able to actually have rapid and affordable modernization of our Department of War systems. We are using interchangeable components, enabling that flexibility to do the rapid tech refresh and also give the opportunity to industry to solve our problems.
“The only way I know how to do that, how to unlock that, that the innovation ecosystem that is out there – as well as private equity and nontraditionals – is open architecture.”
MOSA is also enabling faster development of autonomous payloads, which need to be independent of their platform; such platforms can last for years.
“MOSA increases flexibility and accelerates capability growth, but it requires disciplined systems engineering, clear interface ownership, and strong configuration management to ensure the full system performs reliably and remains upgradable over time,” says Mitch McDonald, president of Red Cat subsidiary Teal Drones (South Salt Lake, Utah), which produces the Red Cat small autonomous craft pictured on this issue’s cover. “Our drones and maritime platforms are treated as durable baselines. The airframe or hull remains stable, while compute, sensors, autonomy software, and communications modules integrate through controlled interface boundaries.”
For more from McDonald and on MOSA and autonomous systems, please see the feature by Technology Editor Dan Taylor on page 20 titled “Why autonomy upgrades stall at integration – and how MOSA fixes it.”
To see my full conversation with Jacob Glassman, watch our 2026 MOSA Virtual Summit on demand at https://tinyurl.com/5zjphh7u. Other sessions in the summit include “Leveraging MOSA for Electronic Warfare, Radar, and C5ISR Applications”; “MOSA at the Edge Across Multiple Domains: Air, Land, Sea, Space, Spectrum”; and “Making the Business Case for MOSA.”

By Bryan Bockmon
Autonomy has gone from being a controversial idea in the defense industry to becoming one of the most important technologies for the future of warfare. The growing proliferation of battlefield threats around the world – with a particular emphasis on the Russia-Ukraine War – has helped to drive the growth of autonomous technologies. Two factors have been crucial in this growth: the visionary approach of smaller players in the defense industry and the real-time feedback loop formed during decades of counterterrorism operations.
Today, warfighters face ever-evolving asymmetric threats and terrorist tactics on the battlefield, and demand for autonomous technologies to keep personnel safe has never been higher. Autonomy is now becoming a vital part of everything from counter-unmanned aerial systems (C-UAS) and broader force-protection measures, to emerging maritime applications. Technologies that can identify, engage and destroy targets with little human intervention (or even no human intervention) are growing in importance.
Autonomous targeting technologies are also improving the performance of human operators across every military domain, enhancing the speed and accuracy of any engagement. These tools and technologies improve safety for personnel, platforms,
and infrastructure. But without small businesses and the grueling lessons learned in the ongoing war on terrorism, today’s warfighters would be less well-equipped to face the threats seen on the battlefields of today and the ones that will crop up tomorrow.
Small businesses got to work innovating Engineering teams at small businesses in the defense industry and policymakers had been keenly aware for many years that it was vital to build autonomy to defend forces against the growing threat of adversarial nations. However, that same awareness was lacking in defense program offices, where leaders were still debating the ethics of the technology. It would take years before they accepted what small defense businesses and so many people in Washington had been saying all along.

Backed by initiatives like the Small Business Innovation Research (SBIR) and Small Business Technology Transfer (STTR) programs, early efforts by these small businesses pushed forward, developing enabling and niche technologies such as artificial intelligence (AI)-based perception, autonomous navigation, and mission-specific payloads. While think tanks and boardrooms debated policy, small firms focused on capability – driven by real-life, warfighter needs.
Accelerators linked to the U.S. Department of Defense (DoD), such as the Defense Innovation Unit (DIU) and SOFWERX, were also key in giving emerging companies an avenue to prototype and deploy real-world solutions rapidly. In fact, many autonomy first-adopters cut their teeth building niche systems for military units, such as drone swarms; low size, weight and power (SWaP) intelligence, surveillance, and reconnaissance (ISR) platforms; or edge-computing payloads. No matter what they specialized in and no matter what the immediate payout of their work, many small businesses dabbling in the autonomy space in its earliest iterations knew that when the wider world woke up to autonomy, their technology would be at the heart of keeping the warfighter safe from new and emerging threats.
The practical lessons of how autonomous technology should work have come through working closely with soldiers on the ground through the decades of the war on terror. Like many military technologies, autonomous technology has been developed with the close involvement of forces, helping leaders in the sector to work out which formats of the technology are going to be successful.
The war on terror saw warfighters facing adversaries who used unconventional tactics and often blended in with the civilian population. In Iraq and Afghanistan, for example, this approach was highlighted by the use of improvised explosive devices (IEDs), makeshift drones, and tactics that exploited complex urban environments that housed a high volume of civilian bystanders. Autonomous systems began to show their value here, enabling round-the-clock surveillance, reducing the risk to personnel in route clearance operations, supporting a more rapid response to burgeoning aerial threats, and reducing the overall danger of working around IEDs.
As noted by the Centre for Emerging Technology and Security in its study several years ago, counterterrorism efforts showed that operations required capabilities that legacy systems simply couldn’t deliver fast enough. This realization helped drive a need for technology to minimize the risk to personnel, by offering persistent surveillance and precision targeting.
Terrorist groups have also rapidly adopted technologies such as drones and asymmetric tactics. The unpredictability of such groups has driven a need for technological innovation. The increased use of drones by both sides has no doubt driven acceptance of autonomous technologies, paving the way for wider adoption worldwide. (Figure 1.)
Driving success in autonomous weapons in a world reshaped by the war on terror requires input from innovative small businesses that helped shape today’s autonomous technology. Leaders in the procurement industry widely believe an open approach to autonomy is key to saving the lives of warfighters on the ground and to enhancing battlefield effectiveness.
Systems need to take a modular open systems approach (MOSA) to work effectively with many battlefield-management systems and standards for command and control. Designing and building using MOSA means that legacy systems can easily be upgraded to include autonomous targeting and engagement solutions that are ready for the modern battlefield. Standardized, modular components also mean that autonomy can be delivered in a highly cost-effective way and deployed rapidly by units in the field.
Acceptance of autonomy as a force multiplier: Going forward
Once seen as almost unthinkable technology, autonomy will continue to reshape the battlefield of tomorrow. Small businesses, working closely with forces from around the world, have helped to shape the form of autonomous technology we see on the battlefield today, as soldiers adapted to the changing threats of the war on terror. Those same small businesses will be vital to driving the wider adoption of this life-saving technology, using a modular approach to protect warfighters on the ground with cost-effective and rapidly deployable autonomous solutions. MES

Bryan Bockmon is the CEO of AimLock, a company that develops autonomous systems for defense applications. He has over two decades of experience across R&D, engineering, and leadership in autonomy and weapons systems development and is responsible for driving AimLock’s business strategy, critical partnerships, and product roadmap. AimLock is advancing autonomous and aided target recognition systems powered by the company’s core targeting modules (CTMs) that are purpose-built with a modular open systems approach (MOSA).
AimLock
https://aim-lock.com/

The MQ-9 Reaper is a medium-altitude/long-endurance remotely
intelligence, surveillance, reconnaissance
and
By Dawn Zoldi
Military drones, much like their commercial counterparts, are on the verge of routinely traversing domestic airspace for logistics and other critical missions. Project ULTRA [UAS logistics, traffic, response, autonomy] – a public/private collaboration in North Dakota – stands as a testbed for this future, demonstrating the necessity for seamless National Airspace System (NAS) integration of both military and commercial uncrewed aircraft. However, current FAA [Federal Aviation Administration] proposals for Part 108 beyond visual line of sight (BVLOS) operations, which lean heavily on ADS-B [Automatic Dependent Surveillance–Broadcast] and GPS, are inadequate alone. Engineers and decision-makers must grapple with the operational and security vulnerabilities of relying on cooperative, GPS-based systems, especially as military organizations will increasingly leverage commercial off-the-shelf (COTS) drones. The solution may very well lie in integrating robust, independent surveillance with secure radar-based conflict detection.
North Dakota’s Project ULTRA [UAS logistics, traffic, response, autonomy] represents a major change in unmanned logistics: For the first time, military cargo drones will be routinely flown between major installations, such as Grand Forks Air Force Base and Cavalier Space Force Station, through active civilian airspace.
This multi-entity collaboration project, and ones like it which will surely follow, underscores both the appetite for, and the challenges of, routine military UAS beyond visual line of sight (BVLOS) operations in the National Airspace System (NAS). Even so, the airspace density there is nothing like what operations will encounter in major U.S. corridors, such as near Liberty International in Newark; what works in North Dakota may not work in New Jersey. Each concept of operations (CONOPS) must be carefully reviewed in terms of mission, location, aircraft, and related technologies.
The FAA’s [Federal Aviation Administration’s] draft Part 108 rule aims to unlock scalable BVLOS operations. The FAA placed ADS-B and other GPS-derived systems as a centerpiece requirement for drones to broadcast their positions. But ADS-B, at its core, is a cooperative surveillance technology, meaning that it works only if each aircraft voluntarily and accurately broadcasts its location. However, GPS, as such a method, remains susceptible to spoofing, jamming, and operational denial.
“In civilian operations, GPS and ADS-B are fragile. An enemy or even a clueless operator probably won’t broadcast anything at all,” explains Ray Adams, CEO of airspace integration company Trajectrix (Egg Harbor Township, New Jersey) and a 31-year air traffic control (ATC) veteran. ADS-B’s dependence on GPS further amplifies the risk. GPS disruption, whether accidental
or malicious, immediately degrades the integrity of separation and collision avoidance for all airspace users.
This situation is a nonstarter for defense applications, where mission assurance depends on resilient, layered navigation and surveillance architectures. The military, Adams notes, already assumes that adversaries will not cooperate, hence their robust investment in networked, secure radar.
Security, autonomy and the limits of embedded conflict avoidance
The debate intensifies when considering military aircraft, especially commercial off-the-shelf (COTS) drones reconfigured for defense logistics or intelligence missions. As in Project ULTRA, many military UAS operations may leverage commercially available platforms with the same vulnerabilities as commercial drones.
“GPS is good most of the time, but it’s also incredibly fragile. For the size and weight of logistics drones, you really need three things: INS [inertial navigation system] backup, optical correlation, and – critically – a ground-based mechanism for independently tracking the aircraft outside what it broadcasts,” Adams emphasizes.
Most military drones are designed for contested, GPS-denied environments and are equipped with multilayered navigation backups such as INS, optical terrain reference, and magnetic field mapping.
According to Adams, even standalone detect-and-avoid (DAA) solutions embedded in the aircraft are imperfect, especially in the area of detecting noncooperative threats like a lost pilot, a wayward general aviation plane or an aircraft with disabled transponders. “You can’t deconflict from things you can’t see, and you can’t see everything from a UAS, even with top-tier sensors,” Adams says.
Military UAS in the NAS: same vulnerabilities, aame solutions
As military UASs transition to routine NAS operations for missions such as logistics, persistent surveillance, and supply delivery, many are being built as COTS drones or developed in partnership with industry. While U.S. Department of Defense (DoD) platforms may enjoy additional onboard security layers, their use in low-altitude, high-traffic airspace exposes the same collision and security risks as any large commercial drone.
“Any aircraft depending solely on GPS-based systems is risking both the mission and the safety of everyone in shared airspace,” Adams cautions. Mandating ADS-B or remote ID without backup independent surveillance is a “Swiss cheese” model where one failure mode can cascade into disaster, he said.
Military procedures historically favor redundancy and operational security. But in NAS airspace, especially above urban or infrastructure-rich corridors, the defense community needs integration protocols that mirror commercial best practices and address decentralized threat vectors. Neither embedded sensors nor broadcast-only mechanisms can ensure complete situational awareness.
The case for independent surveillance and secure radar integration
One path forward would be to integrate ground-based, radardriven independent surveillance as a complementary layer to cooperative systems. This is the essence of what Trajectrix advocates with its patented and proprietary Secure GroundBased Detection and Alert (S-GBDAA) system.
S-GBDAA leverages existing FAA and U.S. Department of Defense (DoD) radar infrastructure to securely process surveillance data within protected government enclaves. It does not transmit raw radar data, which would be a security risk, but instead generates precise, actionable alerts only for atrisk aircraft operators. This method ensures both operational effectiveness and cyber resilience. By extending the conflict detection range far beyond what airborne sensors can see, S-GBDAA “buys time,” Adams asserts, for both autonomous and piloted systems to deconflict safely.
“This architecture means military and commercial operators alike get the benefit of the nation’s surveillance network without risking classified movements or exposing sensitive patterns in the open,” Adams explains. The architecture is NISTand CMMC 2.0-compliant, minimizing attack surfaces and aligning with both FAA and military data-protection standards.
Adopting secure, ground-based and federated DAA systems also fully aligns with the FAA’s own safety objectives and ICAO’s air traffic management principles. To this end, Trajectrix is working cooperatively with both the FAA and the DoD on its S-GBDAA. The tool complements operator-based separation without shifting ATC responsibilities, while its scalable, federated architecture enables expansion as NAS traffic density grows, thereby supporting both commercial innovation and the mission-assurance imperative of the DoD.
As Project ULTRA in North Dakota sets the benchmark for integrated military drone logistics in the NAS, these demonstrations are only just the opening act. The long-term vision is a national airspace ecosystem in which both civilian and military drones can operate efficiently and safely beyond visual line of sight, in all types of airspace, at any scale.
For engineers, the task is to integrate multilayered surveillance: an ecosystem where every airspace user, regardless of origin, benefits from secure, independent, and resilient collision avoidance.
As the FAA finalizes Part 108 and the DoD continues to leverage COTS innovation in the NAS, embedded systems engineers must advocate for architectures that do not rely solely on GPS and ADS-B. The security of the nation’s airspace and the success of military autonomy will depend on it. MES
Dawn M.K. Zoldi (Colonel, United States Air Force, Retired) is a licensed attorney, an U.S. Air Force veteran, and the founder and chief executive officer of P3 Tech Consulting.
Enabling AI capability in autonomous systems
By Stanley Crow
Military autonomous systems increasingly depend on real-time perception, decision-making, and adaptation under extreme constraints of resilience and demands for ever-smaller size, weight, and power (SWaP). Traditional CPU-centric embedded architectures alone cannot meet the computational demands of modern machine learning (ML) inference without exceeding feasible power envelopes or introducing unacceptable latency. Commercial off-the-shelf (COTS) edge artificial intelligence (AI) accelerators are reshaping autonomous military systems, with particular attention to space as an operational domain. Recent NASA proton and heavy-ion test results demonstrate that selected commercial AI accelerators can exhibit radiation resilience compatible with mission-critical autonomy, signaling a potential shift in how defense and space programs approach onboard AI.
Autonomous military platforms – ranging from uncrewed aerial vehicles and autonomous ground systems to maritime and space assets – are increasingly expected to operate with minimal human oversight. These systems rely on deep neural networks for tasks such as object detection, sensor fusion, navigation, and adaptive mission planning. The computational profile of these workloads is dominated by matrix-intensive operations that scale poorly on general-purpose embedded CPUs.
The operation problem is fundamentally quantitative: A modern convolutional neural network for real-time object detection can require tens of trillions of operations per
second (TOPS) to sustain inference at tactically relevant frame rates. Historically, embedded CPUs capable of meeting such throughput typically exceeded acceptable power budgets or often required aggressive duty cycling that would degrade responsiveness. Conversely, GPUs can provide the necessary compute density, but can consume power in excess of
30 to 40 watts and are often incompatible with size, weight, power, and cost (SWaP-C) constraints required in military platform deployments.
Latency is an equally critical constraint. Autonomy demands deterministic response under degraded or denied communications. Reliance on off-board processing or cloud-based inference introduces vulnerability to jamming, cyberattack, and contested spectrum environments. As a result, the computational bottleneck at the edge has emerged as one of the most limiting factors for meaningful autonomy across multiple military domains.
In many autonomous military applications, latency budgets are measured in milliseconds (ms) rather than seconds. Guidance, navigation, and control loops for autonomous vehicles typically require end-toend perception-to-action latencies below 100 ms to maintain stability margins, with latencies of 20 ms to 50 ms desired.
When inference workloads exceed available onboard compute resources systems are forced to reduce model complexity, frame rate, or autonomy level – directly constraining mission performance.
Space amplifies the autonomy challenge
Space systems represent the most extreme instantiation of the autonomy problem. Satellites, spacecraft, and future cislunar platforms must operate with long communication delays, intermittent contact, and limited opportunities for human intervention. Onboard autonomy is not optional; rather, it is mission-enabling.
From a computational perspective, space platforms combine severe size, weight, and power (SWaP) constraints with an unforgiving radiation environment. High-energy protons and heavy ions can induce single-event effects (SEEs) that corrupt data, interrupt functionality, or permanently damage electronics. Historically, this environment drove reliance on radiation-hardened processors that trade performance for reliability, but such processors often lagged commercial technology by multiple generations and cost orders of magnitude more.
Radiation-hardened processors typically deliver performance in the range of singledigit to low-tens of giga floating-point operations per second (GFLOPS) at power levels of 5 W to 15 W, while unit costs can exceed upwards of $50,000 to $200,000 per device depending on qualification level and production volume. This cost and performance disparity has unfortunately made high-performance onboard autonomy economically impractical for many space and defense programs, particularly for proliferated constellations.

When embedded systems and critical I/O fail, the cost isn’t just repair or replacement. It’s missed missions. Lost data. Broken trust.
Reliability isn’t just about what you buy. It’s about what you never have to face.
Rugged embedded computing and industrial I/O for aerospace and defense platforms. Engineered for when failure isn’t an option.
The result has been a capability gap. Advanced autonomy algorithms – particularly those based on deep learning – have been difficult to deploy in space due to insufficient onboard compute power. This limitation constrains applications such as autonomous rendezvous and proximity operations, onboard target recognition, adaptive payload management, and resilient space situational awareness.
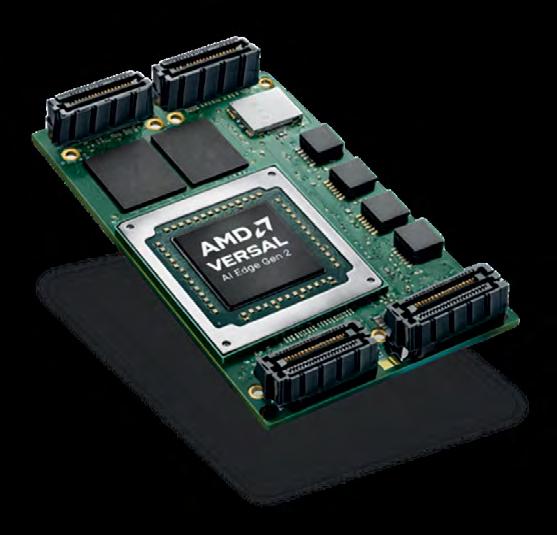
COTS edge AI accelerators as a viable solution path
Recent advancements in commercial edge artificial intelligence (AI) accelerators point to a fundamentally different approach. Defense and space programs are increasingly evaluating commercial off-the-shelf (COTS) accelerators originally designed for terrestrial edge inference. These devices leverage advanced semiconductor process nodes, specialized data flows, and memory architectures optimized for neural networks, achieving orders-of-magnitude improvements in performance per watt. These improvements reduce compute requirements on the CPU, enabling greater overall system performance at lower cost and power.
From a system-level perspective, the solution involves careful selection and validation rather than wholesale substitution. COTS accelerators enable compelling advantages, such as performance density measured in tens of TOPS within single-digit watt envelopes, reduced unit cost through commercial volumes, and mature software ecosystems that accelerate integration and updates.
A remaining concern has been radiation resilience. Unlike traditional space-qualified parts, most COTS AI accelerators are not designed explicitly for radiation environments. This gap must be addressed empirically through test and evaluation rather than assumption.
A recent NASA report provides quantitative insight into the radiation-resilience question. Under the NASA Electronic Parts and Packaging (NEPP) Program, a modern edge AI accelerator (the EdgeCortix SAKURA-II) was subjected to both proton and heavy-ion irradiation to characterize its susceptibility to single-event effects. Testing was conducted at the Texas A&M University K500 cyclotron using linear energy transfers (LETs) up to approximately 40.9 MeV·cm²/mg. (Figures 1 & 2.)
The device demonstrated no destructive single-event latchup events across the tested LET range. Observed effects were primarily single-event functional interrupts (SEFIs), often associated with PCIe interface disruptions, and single-event upsets (SEUs)


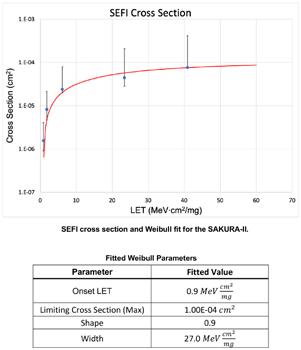
Figure 3 | Fitted Weibull analysis indicated an onset LET of approximately 0.9 MeV·cm²/mg and a limiting SEFI cross-section on the order of 1×10-4 cm². These parameters indicate suitability for many missions in low Earth orbit, geosynchronous orbit, and cislunar regimes.
Source: NASA.
manifesting as transient changes in neural network confidence scores. Many SEUs were self-recovering on subsequent inference iterations due to refresh from off-chip memory outside the irradiation zone.
Quantitatively, fitted Weibull analysis indicated an onset LET of approximately 0.9 MeV·cm²/mg and a limiting SEFI cross-section on the order of 1×10-4 cm². These parameters indicate suitability for many missions in low Earth orbit, geosynchronous orbit, and cislunar regimes. (Figure 3.)
Implications for space-ready AI processing
The significance of these results extends beyond a single device. Radiation tolerance is not a binary property limited to radiation-hardened parts, but is in fact a spectrum that can be quantified and mitigated at the system level. For AI accelerators, where performance per watt (and per dollar) is paramount, this answer opens a new design space.
From a reliability standpoint, typical single-event upset rates for advanced microelectronics in low Earth orbit are often on the order of 10-6 to 10-4 upsets per device-day, depending on shielding, orbit, and solar conditions. Importantly, not all upsets are mission-terminating.
System-level architectures that tolerate transient faults – through watchdog timers, task-level redundancy, memory refresh, or periodic health checks – can achieve high effective availability even when individual components experience recoverable events. This mindset shifts the design philosophy from eliminating all faults to bounding and managing them, enabling the use of higher-performance processors without compromising mission assurance.
By combining COTS edge AI accelerators with architectural mitigations, such as checkpointing, model reloads, redundancy at the task level, and autonomous recovery, space systems can field substantially more capable onboard autonomy without prohibitive mass or power penalties or exorbitant costs. This approach aligns with broader defense trends toward resilient, distributed, and software-defined systems.
The emerging evidence suggests that carefully selected and validated COTS edge AI accelerators can form the computational backbone of next-generation autonomous systems, including space platforms.
Military autonomy is no longer constrained by algorithms, but by the availability of reliable compute at the edge. Space represents the most demanding test case for this challenge, combining autonomy, power limits, and radiation exposure in a single domain.
The emerging evidence suggests that carefully selected and validated COTS edge AI accelerators can form the computational backbone of next-generation autonomous systems, including space platforms. As defense programs move to field adaptive, resilient autonomy at scale, commercial edge AI accelerators are well suited to play an increasingly central role. MES

Stanley Crow is EdgeCortix’s Vice President of Defense & Space Technology. He previously served for 15 years in Northrop Grumman in roles including CTO and VP Technology, Engineering and Manufacturing for the company’s Defense Systems sector and Chief Executive for Northrop Grumman Japan. Prior to joining Northrop Grumman, Mr. Crow was an Associate Principal at McKinsey and Company, serving technology, aerospace, and defense clients globally. Additionally, he served almost three decades in the U.S. Air Force, including both active-duty and reserve assignments focused on space, intelligence, and advanced capability needs in the IndoPacific.
EdgeCortix https://www.edgecortix.com/en/

NASA first selected our chip resistors for a mission to Jupiter and Saturn that launched in 1977 and is still operating in interstellar space. Our chip resistors continue to be selected for high reliability applications on Earth and in space. On Earth, our resistors are selected for mission critical applications in military weapon and defense systems. In space, our chips are found in weather and communications satellites and on missions to Mars, Jupiter, and Pluto.
Choose State of the Art resistors.
RESISTIVE PRODUCTS

Made in the USA.
Enabling AI capability in autonomous systems

By Drew Thompson
Across defense programs, autonomous artificial intelligence (AI) systems frequently stall between successful prototyping and field deployment. The limiting factor is rarely the software itself. Instead, progress slows when the underlying hardware platform was not engineered to evolve alongside rapidly changing AI workloads, sensors, and operational requirements. As the U.S. Department of Defense (DoD) accelerates its adoption of AI, platform-level engineering decisions are increasingly determining whether autonomous AI platforms can transition from experiment to operational reality.
Over the past several years, the deployment of autonomous artificial intelligence (AI) systems has become a strategic priority for the U.S. Department of Defense (DoD). Autonomous platforms are expected to sense, decide, and act independently, often in contested environments. While advances in AI algorithms and software models receive much of the attention, the practical challenge facing many programs is not whether autonomy can be achieved, but rather if it can be deployed, sustained, and iterated at operational speed.
While the DoD and other U.S. entities have used AI on an ad hoc basis over the past 60 years, in 2018 there was a shift towards more formalized processes with the release of the “2018 DoD Artificial Intelligence Strategy.” The document outlining the
2018 strategy emphasized the need to build a centralized infrastructure for AI development, to bridge AI technology developments from the DoD’s research and engineering communities, and to exert international leadership in military ethics and AI safety.
Subsequent DoD strategies, such as the “2020 DoD Data Strategy” and the creation of the Chief Digital and Artificial Intelligence Office (CDAO), further em-
phasized the importance of data-centric approaches and the optimization of AI capabilities across the DoD.
The “2023 DoD Data, Analytics, and AI Adoption Strategy,” placed a major focus on speed, agility, learning, and responsibility. It emphasized decentralized authority and the creation of tight feedback loops between developers and end users, all of it aimed at enhancing the decision-making processes within the DoD. The 2023 strategy outlined a foundational, guiding approach to AI rather than a step-by-step guide.
On January 12, 2026, the U.S. Secretary of Defense issued a memo outlining the AI Strategy for the DoD. The 2026 policy represents a significant shift in both the tone and the approach to the DoD’s use of AI. The earlier policy documents set broad, top-level goals like improving access to data across the entire department, cultivating a leading AI workforce,
and the responsible development of AI applications. In contrast, the 2026 policy places a major emphasis on speed and “identifying and eliminating bureaucratic barriers to deeper integration, which are vestiges of legacy information technology and modes of warfare.”
In more practical terms, the 2026 DoD AI Strategy goes further than its predecessors in that it establishes seven what it calls Pace-Setting Projects (PSPs) to be initially administered by the CDAO. These PSPs will “serve as tangible, outcome-oriented vehicles for rapidly completing our buildout of the foundational AI enablers needed to accelerate AI integration across the entire Department.” For the DoD, these PSPs are also meant to establish a new execution standard for AI implementation: “single accountable leaders, aggressive timelines, measurable outcomes, and rapid iteration where failure accelerates learning and improvement.”
The 2026 DoD AI Strategy reframes speed of deployment as a requirement rather than a vague aspiration. This speed is, perhaps, most consequential for autonomous systems, where AI must operate onboard, in real time, and often without reliance on cloud connectivity or centralized compute resources.
For hardware designers and manufacturers, accelerating the speed of development and iteration introduces a fundamental tension. AI software stacks evolve rapidly as the models grow, while hardware platforms are expected to remain stable, certifiable, and deployable over long service lives. When platforms are engineered around fixed assumptions, the end product often requires redesigns, requalification cycles, and delays that ultimately contradict the acceleration goals.

Many autonomous AI prototypes are built to prove feasibility under controlled conditions. Power budgets are tightly sized, thermal solutions are optimized for known workloads, and I/O configurations are selected for a specific sensor suite. These designs may succeed in demonstrations, but they often lack the flexibility needed for deployment.
As AI software stacks mature, new requirements and operational conditions often emerge. These include things such as higher inference rates or more complex models, the addition of more or different sensors and data sources, an expanded mission scope, new accelerators or compute architectures, or increased environmental and reliability constraints.
When the hardware platform cannot adapt to integrate these changes, programs stall. Redesigns consume schedule and budget and AI software progress outpaces hardware readiness. The result: A widening gap between the capability of autonomous AI platforms and the reality of which hardware can actually be fielded.
Power and thermal headroom as enablers of speed
Designing platforms around average power consumption is insufficient for autonomous AI hardware. For one thing, AI workloads are inherently dynamic. In addition, inference patterns are not uniform and can cause compute demands to spike unexpectedly. Another factor: It is assumed that the power profiles of AI accelerators evolve with each new generation.
Conscious design decisions in the early stages of product development to increase both the power and thermal headroom of a hardware platform can provide the flexibility to meet many of the challenges to the AI acceleration outlined by the DoD. This hardware flexibility enables new models or accelerators to be introduced without redesign. Further, these buffers are able to handle the variable compute load spikes of the AI workflow without throttling performance. Perhaps, most crucially, building in
this headroom from the earliest design stages reduces the need for late-stage thermal requalification or recertification.
Thermal margins in particular play a significant role: Edge systems are subjected to extreme temperatures, limited airflow, shock, vibration, and size constraints, all of which place unique demands on system design. Because external thermal conditions cannot be controlled, engineers must focus on minimizing internal heat production and maximizing heat dissipation. Localized heating from hardware accelerators can destabilize decision loops if not anticipated. Platforms that are engineered with sufficient margins from the earliest stages can evolve without sacrificing either reliability or flexibility.
Modularity has become a critical design principle for accelerating the iterative design and development of autonomous AI platforms. Modular compute, I/O, and subsystem architectures enable platforms to rapidly adapt to hardware, software, or environmental changes.

The use of modular architectures dramatically simplify aspects like sensor upgrades or compute changes without redesign or requalification.
Rather than treating integration as a onetime event, designs that use modular platforms are better able to support continuous iteration, ultimately aligning hardware development with the rapid, feedback-driven execution model emphasized in the PSPs. (Figure 1.)
Rapid experimentation to production repeatability
As noted previously, autonomous AI platforms often stall in the transition period between experimentation and production. Lab platforms optimized for flexibility often lack the consistency and robustness required for field deployment, while production hardware may arrive too late to influence AI development.
To this end, the PSPs will benefit from platforms that support early experimentation with production hardware that uses standardized interfaces that persist from lab to field and manufacturable designs that scale without major revisions.
Ruggedization and flexibility as acceleration tools
Ruggedization decisions made early in the design process can substantially accelerate deployment. Early attention to features like shock, vibration, and temperature extremes; power quality and signal integrity; and mechanical and thermal robustness has the effect of reducing downstream delays caused by redesigns, recertifications, and field failures.
The DoD’s AI Acceleration Strategy sets the primary goal as speed, saying that AI capabilities must move faster between the concept and design phase and operational deployment. Ultimately, the iterative speed depends much more on the capability and flexibility of underlying hardware platform than on the AI software stack. Hardware systems built with careful attention to flexibility and modularity are much better able to evolve at the pace outlined in the DoD policy.
True speed in deploying autonomous AI systems does not come from moving faster at the software layer alone. It comes from designing platforms deliberately engineered to change, scale, and survive the transition from experimentation to operational deployment. MES

Drew Thompson is a technical writer and content specialist for Sealevel Systems. He holds an M.S. in global studies and international affairs from Northeastern University. Thompson can be reached at drew.thompson@sealevel.com.
Sealevel Systems https://www.sealevel.com/


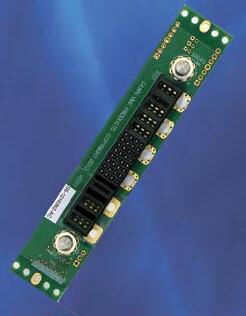






The Dawn family of one-slot OpenVPX test station and development backplanes gives engineers the ability to perform compatibility tests and easily reconfigure payload module profiles and slot interoperability to meet custom requirements.



Highly useful as stand alone or in combination with other backplanes, with or without RTM connectors. Multiple units can be topology wired using MERITEC VPX Plus cables.


Rugged, Reliable and Ready. You need it right. You want Dawn.

Available 3U and 6U in VITA 65, VITA 67.1, VITA 67.2, VITA 67.3, Nano-RF, SOSA-aligned and Power Supply slot profiles. Custom configurations available. (510) 657-4444

MOSA solutions for autonomous systems: SBCs, RTOS, connectors, backplanes, etc.

By Dan Taylor
Autonomous operations can range from small drones to autonomous surface vessels, with the real competitive edge shifting from who builds the best platform to who can upgrade it fastest. Open architectures promise plug-and-play tech insertion –with the hard part being the “glue”: the interfaces, timing, thermal and power behaviors, and configuration control that decide whether a new payload, compute card, or comms module drops in cleanly or triggers months of requalification. Designs that take a modular open systems approach (MOSA) help solve those interconnect challenges.
Defense teams want a simple outcome: Keep the platform in service, then insert better technology as it becomes available – which is where a modular open systems approach (MOSA) comes in and why it was mandated by the U.S. Department of Defense (DoD). But many upgrade plans fail during integration. A module may meet a standard on paper, yet still cause timing issues, thermal stress, data mismatch, or power conflicts once installed.
That is the central challenge in autonomous systems. Airframes and hulls can stay in service for years, while compute components, software, and sensors can change every year. If an architecture cannot absorb fast subsystem change, programs lose time, money, and relevance.
This is why MOSA choices now shape every layer of design: single-board computers (SBCs), real-time operating systems (RTOS) platforms, connectors, and backplanes.
Starting with a stable platform
Mitch McDonald, president of Red Cat subsidiary Teal Drones (South Salt Lake, Utah), says that the Teal/Red Cat process begins with fixed interface boundaries.
“We design autonomous systems around stable, well-defined mechanical, electrical, and data interfaces so capabilities can evolve without redesigning the core platform,” McDonald says. “That discipline applies across our portfolio, from small UASs [uncrewed aerial systems] to maritime USVs [uncrewed surface vessels].”

Figure 1 | LCR Embedded Systems’ VE02 packs two 4-slot VPX/SOSA aligned payload sections into a single SAVE envelope for Army ground vehicles, with separate cooling paths and dual conduction-cooling/forced-air assist to support high-power size/weight/power (SWaP)-constrained applications. Courtesy of LCR Embedded Systems.
He says that Red Cat treats the vehicle as the long-life baseline and updates mission technology inside controlled boundaries. “Our drones and maritime platforms are treated as durable baselines. The airframe or hull remains stable, while compute, sensors, autonomy software, and communications modules integrate through controlled interface boundaries.”
That model supports backward-compatible upgrades: McDonald points to new payload work that integrates with existing systems, so that users can improve capability without replacing the aircraft. He says the same approach extends to flight control, navigation, communications, and internal compute; these aspects also apply to the company’s Blue Ops maritime systems.
This kind of technology implementation depends on concrete standards, says William J. Pilaud, chief solutions architect at LCR Embedded Systems (Audubon, Pennsylvania).
“For autonomous defense systems, the application of MOSA principles points to the SOSA [Sensor Open Systems Architecture, or SOSA, Technical Standard] and VITA 46/ VPX architectures, open Ethernet-based data fabrics, and modular, container-friendly software frameworks,” he says.
Pilaud notes that standards also drive hardware selection decisions. “They directly influence hardware selection – driving the use of SOSA conformant single board computers; high-speed backplanes with deterministic, low-latency fabrics; and ruggedized connectors capable of supporting high bandwidth and harsh environments.”
RTOS design is changing Hardware can be modular, but if software is tightly locked to one platform, upgrade speed still suffers. This design aspect, Pilaud says, means that open architecture changes how teams design real-time software stacks.
“An open systems approach fundamentally shifts RTOS design from tightly coupled, platform-specific implementations to modular, standards-based architectures,” he explains. “Instead of hardwiring applications to proprietary hardware, modern RTOS environments must support portable middleware, containerized services, and well-defined APIs that allow autonomy stacks to evolve independently of the underlying compute.”
Hard real-time behavior is still mandatory, he adds: “Deterministic performance remains nonnegotiable, but it’s now paired with partitioning, secure boot, and realtime virtualization. This enables mixedcriticality workloads – AI inference, sensor fusion, and control loops – to run concurrently while preserving timing guarantees and rapid upgradeability.” (Figure 1.)
The upshot? RTOS selection is now both a performance choice and a life cycle choice. In short, MOSA is not only a policy objective. It is a component-selection framework that helps keep future upgrade options open.
Why integration still breaks
Even with robust standards and modern RTOS design, integration failures still happen. McDonald notes that the risk is concentrated where subsystems meet.
“Integration challenges typically appear at system boundaries,” McDonald says. “Even when components align to open standards, differences in timing, data formats, synchronization, thermal behavior, or fault management can affect system performance.”
He stresses the operational impact in autonomy programs. “Those boundary conditions directly impact perception accuracy, navigation stability, and command-and-control reliability.”
Pilaud describes the same issue from a VPX/SOSA perspective. “Even when SOSA/VPX modules and backplanes comply with MOSA principles, differences in firmware maturity, timing assumptions, thermal profiles, and power management can introduce subtle instability in tightly coupled autonomous systems,” he says.
Both Pilaud and McDonald call for strong integration discipline, with Pilaud recommending “rigorous interface control, conformance testing, and system-level validation,” and McDonald emphasizing “disciplined integration testing and configuration control” across power, thermal, software, and mission-data paths.
McDonald also points to IP-ownership risk at integration layers. “If interface
definitions or integration layers are owned externally, iteration cycles can become dependent on third-party development timelines, which increases integration complexity and slows capability evolution.”
Connectors and backplanes are strategic choices
This boundary challenge leads directly to interconnect decisions. Rodney Doss, industry standards manager for Samtec (New Albany, Indiana), says connector choices are often set early because they define what the system can carry.
“Work groups often begin with connectors to understand the signal between module and backplane, then work their way back from there,” Doss says.
He says groups usually focus on three things: “performance, ruggedness, and availability.” In autonomy programs, that can quickly become a bottleneck.
“The complex and smart features of these systems require the highest performances available such as PCIe Gen 6, with as many pin counts as they can fit into the small spaces they have available,” Doss says.
He says open-standard connector definitions make module interchange possible across vendors. By designing in connectors, these standard definitions help in three ways.
“First, it defines the footprint and placement requirements of the board assembly so module designers know how much room they have to work with to design their widget,” Doss says. “Next, it solves the connectivity needs, so that a system integrator can trust a module will plug into their system regardless of vendor. Finally, it allows the groups
MOSA solutions for autonomous systems: SBCs, RTOS, connectors, backplanes, etc.

2 |
AcceleRate
Evaluation Kit gives system designers and signal-integrity engineers a standalone, robust test platform for characterizing AcceleRate HD high-density 4-row strip connectors in highspeed, high-cycle applications. Courtesy of Samtec.
to define the pin maps of the connector so that all modules will communicate the same within the system, even if their module works completely different internally.” (Figure 2.)
Sponsored by Perforce
As artificial intelligence (AI) becomes increasingly integrated into software development, its presence in safety-critical applications is raising new challenges for functional safety and regulatory compliance. Attendees will gain insights into the limitations of current functional safety standards when applied to AI; AI’s role in safety validation; emerging standards and requirements for AI system design and verification; and international regulatory efforts including the EU AI Act. (This is an archived event.)
Watch this webcast: https://tinyurl.com/43t9jtcy

Once interconnects and interfaces are stable, MOSA can support another major need: controlling size, weight, and power (SWaP). Autonomous platforms cannot absorb unlimited SWaP growth, and Teal’s McDonald says that MOSA helps teams avoid that trap.
“MOSA helps prevent overbuilding and uncontrolled growth,” he says. “Not every drone or USV needs to carry every capability, and not every improvement should require structural redesign.”
He describes, for example, battery upgrades that improve performance while preserving the existing interface, or maintaining payload modularity across multiple airframes through common boundaries.
Pilaud makes the same point at system scale. “MOSA principles help manage SWaP constraints by enabling modular scaling rather than overdesign. Instead of building monolithic systems sized for peak future requirements, open architectures allow designers to rightsize compute, I/O, and acceleration at the module level.”
When upgrades stay inside defined subsystem boundaries, programs can add capability without triggering platformwide redesign. For program offices, life cycle value is often the strongest MOSA argument.
“Life cycle management is central,” McDonald says. “Airframes and maritime vessels may remain in service for many years. Sensors, compute hardware, autonomy software, and communications systems evolve much faster.”
He says that stable interfaces support incremental modernization, which can reduce recertification scope and limit operational disruption.
Pilaud adds that an open systems approach “keeps autonomous systems relevant by decoupling platform life cycles from technology-refresh cycles.” He says that this approach supports
module-level insertion of new processors, artificial intelligence (AI) accelerators, and networking technologies without the need for full redesign.
Today’s defense industry recognizes that standards are essential, but they are not enough by themselves. Programs also need clear interface ownership, strong configuration management, and disciplined validation.
“MOSA increases flexibility and accelerates capability growth, but it requires disciplined systems engineering, clear interface ownership, and strong configuration management to ensure the full system performs reliably and remains upgradeable over time,” McDonald says. MES







As the leader in Open Standards-based Solutions, Elma can take you rapidly from development to deployment. Find out how we work with our customers through every stage in the process.

MOSA solutions for autonomous systems: SBCs, RTOS, connectors, backplanes, etc.

By Ashish Parikh
Battlefield autonomy and distributed platforms demand communications architectures that respond at machine timescales, where conditions unfold. Every design choice that fails to embrace this reality reflects yesterday’s battlefield, not today’s.
Missions fail when links fail. Across air, land, sea, space, and cyber domains, operational outcomes hinge on whether communications systems can sustain connectivity in contested, dynamic environments. Autonomous and distributed platforms routinely demonstrate impressive performance in clear conditions, but in pressurized conditions, communications collapse becomes a key factor that limits mission success.
This trend reflects a deeper structural shift in the operating environment, where congested and contested spectrum has become the norm instead of the exception. Military, commercial, and civilian radio frequency (RF) activity all converge across the same frequency bands, often unpredictably.
In this environment, systems that preserve the ability for humans and machines to communicate enable freedom of action, while systems that lack it surrender tempo and coherence.
The strategic transition now underway in defense communications centers on adaptability, with a primary focus on enabling real-time spectrum control at the edge, including for autonomous systems.
For decades, communications architectures were built around the assumption that spectrum access could be predicted, allocated, and largely preserved through planning. Frequency plans, static allocations, and pre-mission deconfliction reflected environments in which spectrum access remained orderly and enforceable. That operating context has changed.
Contemporary missions unfold amid dense and overlapping emissions – urban terrain introduces commercial broadband saturation, coalition operations bring incompatible equipment, and satellite proliferation adds persistent overhead
activity. Even sparsely populated regions host sensors, relays, and unmanned platforms competing for access. Moreover, spectrum conditions vary by geography, mission phase, and operational tempo, often within minutes.
Defense leadership has recognized this reality. The DoD Strategic Management Plan (FY 2022-2026) emphasizes increasing the resiliency of command, control, and communications capabilities, noting the need to operate effectively in the electromagnetic spectrum and ensure resilient position, navigation, and timing (PNT) information to protect against disruption and exploitation. Spectrum has shifted from a fixed resource to a variable operating environment, which has exposed the fragility of architectures built on static assumptions. Systems that depend on preplanned frequencies carry increased risk in every mission, whereas adaptable systems are more likely to survive.
Electronic warfare as a persistent
functions as a constant operational pressure. Recent conflicts demonstrate continuous spectrum engagement shaping maneuver, sustainment, and command effectiveness. Jamming, spoofing, and denial blend together, stressing communications architectures over extended durations.
Rigid RF designs reveal their limits under these conditions. Once their operating channel degrades, single-band systems exhibit predictable failure patterns: performance falls sharply, recovery options narrow, and coordination breaks down across dependent systems. These outcomes arise from architectural constraints rather than execution errors.
Systems that adapt can sustain function under pressure, while systems that rely on fixed configurations exhaust their margins early. Post-conflict analysis continues to show that communications resilience flows from design choices made years before in-theater deployment.
Autonomy elevates communications to a mission-critical dependency
Autonomous and semi-autonomous systems amplify the consequences of communications instability. Distributed sensing, collaborative targeting, swarm behaviors, and shared situational awareness all depend on continuous information exchange. Connectivity supports coherence across machines operating at speed and distance, and a single node losing communications can breed uncertainty across the system.
When links degrade, autonomy fragments and slows coordination. Human-in-the-loop mitigation, which has usually been able to compensate for brittle communications, is often too slow for these environments. Spectrum conditions can change on subsecond timescales, and waiting for an operator to diagnose or retune is impractical. Autonomous operations require machine-speed response directly at the radio and network layers.






Single-band architectures struggle in this context because they lack degrees of freedom. Historically, bands were selected for reasons like regulatory access, interoperability mandates, or integration simplicity. While these drivers remain valid, they also constrain behavior. Once a single band is denied, the system has nowhere to go. Loss of degrees of freedom translates directly into loss of mission.
Multiband radios are often presented as a solution to spectrum volatility, but capability and behavior aren’t the same thing. Many systems are technically capable of operating across multiple bands, yet still rely on manual or static selection. In these cases, multiband support functions as a logistics feature, not as a strategic advantage. It may enable the same hardware to be configured differently for different missions, but it doesn’t increase operational resilience under stress.
The distinction that matters is between multiband-capable and multiband-adaptive systems: Without intelligence and real-time control, additional bands simply increase configuration complexity. True spectrum resilience emerges in multiband adaptive systems when radios manage their own access dynamically, aligned with mission intent and network needs.
Adaptive communications requires rapid interference detection, seamless band transition, and preservation of the control plane during switching. Each function reinforces the others. If radios only recognize interference after significant throughput loss, they have already ceded initiative. Likewise, seamless transitions matter because even brief outages can destabilize autonomous behaviors.
Most critically, adaptation must preserve network context. Systems that drop state or require reinitialization during band changes introduce disruptions indistinguishable from failure. Real-time adaptation at the edge reduces reliance on centralized controllers or human intervention in the tight loops where autonomy must make decisions.
Treating multiband operation as a radio feature misses its broader networking implications. When radios can operate across diverse spectrum in real time, the network itself gains new degrees of freedom. Nodes can bridge between frequencies, relay traffic across dissimilar links, and balance load based on current conditions rather than static plans. This setup enables redundancy and graceful degradation under denial. Instead of failing catastrophically when a primary band is disrupted, multiband networks can reconfigure to preserve partial connectivity and mission-critical flows. (Figure 1.)
Over time, this structure moves design emphasis from peak throughput to sustaining acceptable performance under stress. Modern defense networking discussions increasingly emphasize adaptive, self-healing networks as foundational to Combined Joint All-Domain Command and Control (CJADC2), even as formal definitions of resilience in contested environments continue to mature.
The defense acquisition community has long valued clean-lab peak performance metrics, but peak throughput or efficiency in benign settings is not predictive of behavior under contested spectrum. Instead, modern systems demand evaluation criteria that reflect contested reality: performance under interference, transition latency, and stability of connectivity during spectrum disruption.
A system’s capacity to sustain operational continuity in degraded spectrum (known as architectural resilience) is emerging as a procurement differentiator, primarily because systems designed around adaptive behavior are less likely to require costly retrofits as spectrum conditions evolve.
MOSA solutions for autonomous systems: SBCs, RTOS, connectors, backplanes, etc.

An urgent mandate for system teams
Spectrum volatility defines contemporary operations. Single-band systems don’t fail in contested environments because they’re poorly engineered, but because their assumptions no longer match reality. The value of multiband architectures depends entirely on real-time adaptability. Without it, additional bands add complexity without resilience.
Treating spectrum as a maneuver space reframes communications from a fragile dependency to an active operational enabler. A recent influx of private capital should help provide necessary innovation momentum. According to a recent study by McKinsey, global venture- capital investments in defense-related companies jumped by 33% year-over-year, to $31 billion in 2024. Among those investments, around $8 billion went towards next-generation communications networks and autonomous systems.
The systems fielded today will shape operational relevance for decades, and adaptability will determine whether autonomy thrives or falters in the environments where it matters most. MES

Ashish Parikh is the co-CEO of Doodle Labs. In addition to leading the global Doodle Labs team, Ashish oversees product management and operations at the company. Before joining Doodle Labs, Ashish worked at McKinsey & Co. leading strategy and growth projects, and later worked as a product manager at Google and at several startups. He earned a BSc in electrical engineering from Northwestern University.
Doodle Labs • www.doodlelabs.com

When the mission calls for a 3-phase 3U power supply that can stand up to the most rugged environments, the military chooses VPXtra 704™ from Behlman – the only VPX solution of its kind built to operate seamlessly from MIL-STD-704F power for mission-critical airborne, shipboard, ground and mobile applications.
> 3-phase AC or 270V DC input; high-power DC output
> Available holdup cards store 700W of DC power for up to 80 msec
> Overvoltage, short circuit, over-current and thermal protection
> Provides full output performance during both normal and abnormal transients


MOSA solutions for autonomous systems: SBCs, RTOS, connectors, backplanes, etc.

By Dr. James Crowell
The defense sector is saturated with aerial drone warfare, yet far less attention is paid to the ground domain. While air autonomy has dominated recent operational narratives, but the next advantage in autonomy will come from tightly integrating unmanned aerial systems (UAS) with unmanned ground vehicles (UGVs). Together, these systems address tactical blind spots that aerial platforms alone cannot solve, combining reach and speed with endurance, logistics capacity, and terrain control to enable more resilient, scalable, and survivable operations.
Autonomy is a dominant focus in today’s military, but the conversation is heavily focused on air power. Small unmanned aerial systems (sUASs) have become synonymous with autonomous warfare, especially in Ukraine, where commanders describe hundreds of thousands of drone missions flown in a single month. That larger-scale use of UASs underscores how critical air autonomy has become, but it also exposes a growing gap. Air-only autonomy struggles with the realities of deployment: terrain, sustainment, and electronic warfare (EW) at the tactical edge are all factors as well.
The next major leap in autonomy will not come from deploying more drones, but will come from integrating aerial systems with unmanned ground vehicles (UGVs) to create a coordinated, multidomain autonomous force that reduces blind spots, increases endurance, and maintains effectiveness when conditions make air assets less effective.
The blind spots at the tactical edge
While it’s true that sUASs excel at speed, reach, and wide-area sensing, their effectiveness drops sharply at close range. Environments like dense foliage, urban clutter, subterranean spaces, bridges, and interiors all create occlusion zones where overhead sensors lose their ability to gather accurate information. Even after a target is found, the last 50 to 100 meters often require confirmation angles that drones cannot maintain safely or continuously.
This limitation is not theoretical. Reports from the Ukraine conflict have described extended “kill zones” where drone density is high, yet ground maneuver and concealment still dictate outcomes. Persistent aerial presence does not eliminate terrain complexity, but actually amplifies the need for complementary systems that can operate within it.
UGVs address this gap by providing reliable information at the ground level. Positioned forward, they can conduct close-range inspection, validate detections, inspect routes, deploy sensors, and provide confirmation from angles unavailable to airborne platforms. When integrated properly, sUASs enable rapid cueing while UGVs deliver confirmation, with the pairing resulting in reduced false positives, shortened decision cycles, and limited redundant sorties.
Endurance and logistics: the constraints autonomy ignores
The use of drones enables more activity, but maintaining them is often more challenging than people think. High sortie rates mean more batteries to recharge, airframes to recover, parts to repair, and vehicles to replace. At scale, autonomy becomes less about sensing and more about logistics throughput.
A force flying thousands of sUAS missions per month is also moving and managing thousands of batteries, payloads, and spare components. Without automation on the ground, that burden falls on personnel, slowing operations and increasing exposure. UGVs can absorb much of this load: Autonomous ground platforms can perform resupply runs, transport batteries and payloads forward, reposition launch and recovery points, and move sensors or communications relays without putting soldiers at risk. In integrated operations, UGVs function as mobile sustainment nodes while sUASs focus on reconnaissance, targeting, and rapid retasking.
This division of labor increases overall endurance. While sUASs rotate through shorter missions, UGVs maintain a persistent presence, enabling longer time-on-station coverage with fewer airborne assets.
Resilience under electronic warfare
Air autonomy often breaks first under EW. Many sUASs depend on radio-frequency links and global navigation satellite systems (GNSS) for navigation and control, making them vulnerable in challenging environments. Public analyses from Ukraine suggest that a large majority of sUAS losses are attributable to jamming or spoofing rather than to kinetic interception. Precision-guided munitions have also shown dramatic performance degradation during periods of heavy GNSS interception.
An autonomy strategy that relies exclusively on airborne platforms inherits this fragility. When links degrade, aerial assets are forced to abort, loiter ineffectively, or fail outright.
Integrated sUAS-UGV systems can suggest a path to graceful degradation. Ground vehicles can host persistent sensors, alternative communications paths, and localized navigation references that remain effective when aerial links are disrupted. They can maintain mission continuity, provide line-of-sight relay points, and support retasking once conditions improve. Rather than collapsing under EW pressure, the system adapts.
Three integration playbooks that matter
When aerial and ground autonomy are treated as a single system, several repeatable operational patterns emerge:
1. Cue-confirm loops: Aerial detections trigger rapid ground verification. sUASs identify potential targets; UGVs confirm at close range. The payoff is faster confirmation and fewer false alarms.
2. Distributed persistence: UGVs hold terrain, sensors, and logistics while sUASs cycle through shorter missions. The result is extended coverage duration without proportionally increasing sortie counts.
3. Layered response: sUASs provide overwatch and rapid assessment while UGVs handle proximity tasks such as inspection, delivery of effects, and emplacement. This approach reduces risk to personnel and increases operational tempo.
Each pattern shifts autonomy from disparate platforms to integrated capability.
To prove that integrated autonomy works, metrics must go beyond platform performance. Relevant measures include time-to-detect, time-to-confirm, and timeto-respond; hours of continuous coverage per sector; operator-to-asset ratios; mission completion rates under EW conditions; and logistics throughput achieved without human involvement. These metrics capture system-level effectiveness rather than isolated capability.
Drones will continue to dominate coverage of modern warfare, but air autonomy alone cannot solve the realities of terrain, endurance, and contested environments. The future of battlefield autonomy lies in tightly integrating sUASs and UGVs into cohesive multidomain systems that close blind spots, sustain operations at scale, and remain resilient under pressure. The broader lesson applies across the autonomy ecosystem: Victory will belong to forces that treat autonomy as a combined-domain capability, not solely an airborne one. MES

Dr. James Crowell is the founder and CEO of Crow Industries. Before starting Crow Industries in 2018, he specialized in the development and deployment of polar, maritime, volcanic, and space systems at NASA.
By Editorial Staff

Each issue, the editorial staff of Military Embedded Systems will highlight a different organization that benefits the military, veterans, and their families. We are honored to cover the technology that protects those who protect us every day.
This issue we are highlighting the Frontline Healing Foundation, a 501(c)(3) organization dedicated to supporting active-duty military, veterans, and first responders by removing financial barriers to critical care. The foundation helps service members and veterans with cost and access as they navigate mental- and behavioral-health services as they seek to overcome addiction, PTSD, and traumatic brain injury.
According to information from the foundation, donations help in a number of ways, including subsidizing funding for chemical dependency and PTSD treatment that includes detox, inpatient residential treatment services, intensive outpatient program (IOP), one-on-one therapy, and sober living; funding service dogs for personnel; funding sober living housing for warriors who need structured, continued support after treatment while returning to school, volunteering, and/or receiving outpatient treatment; providing funding for treatment that aims to improve the synchrony of brain waves and cognitive health; and promoting behavioral-health education for veterans and law enforcement on how to help comrades and how to spot those struggling with chemical dependencies and PTSD.
The Frontline Healing Foundation is associated with Warriors Heart, a private, licensed, and accredited healing center with physical locations in Texas and Virginia. Its treatment courses provide care including detox, residential and day treatment, sober living, and intensive counseling. The foundation also partners with other veteran-owned and -focused companies and charities. The executive director of the Frontline Healing Foundation – and a Warriors Heart alumnus in long-term recovery – is former Green Beret and U.S. Army Veteran Ted Lanier.
For more information, visit https://frontlinehealingfoundation.org/.
Sponsored by Acromag, New Wave Design, and Samtec
Rugged computing platforms in applications including commercial space, medical, automation, and military need small, modular, high-performance solutions that can operate in extreme environments.
The VITA 93 QMC standard, developed by the VITA Standards Organization, will help solve many of these challenges and enable interoperability across multiple applications.
In this webcast of industry experts, learn how the modular, stackable mezzanine architecture introduced by the VITA 93 QMC standard presents a rugged alternative to M.2 and Mini-PCI Express modules and enables solutions from basic serial I/O to high-performance signal-processing applications across multiple applications. (This is an archived event.)
View this webcast at https://tinyurl.com/mrysuf7b.
View more webcasts at https://militaryembedded.com/webcasts.
By Epiq Solutions
The proliferation of small, low-cost uncrewed aerial systems (UASs) has transformed the threat land scape for military and civilian infrastructure worldwide. From the lessons learned in Ukraine to emerging threats at critical facilities like airports, the challenge of detecting and neutralizing small drones operating in complex RF environments has become increasingly complex. Unlike traditional air-defense systems designed for larger aircraft, counter-UAS (C-UAS) operations require sophisticated RF detection capabilities that can identify “needles in a haystack” or individual threatening drones amid dense civilian RF backgrounds cluttered with Wi-Fi access points, cellphones, and broadcast towers.

In this white paper, learn how software-defined radio (SDR) technology enables spectrum dominance in C-UAS operations and how new applications – from 2-watt ultracompact systems to 8-channel rackmount platforms – provide the technological foundation for next-generation C-UAS capabilities.
To view this white paper: https://tinyurl.com/yuzknru3.
To view more white papers: https://militaryembedded.com/whitepapers.
VNAs are foundational instruments in modern counter-UAS systems, where RF performance directly determines the effectiveness of detection, tracking, and electronic attack. Antennas, feed networks, filters, and RF paths must operate predictably across wide frequency ranges, often in challenging environments. The Select Series from Copper Mountain Technologies combine a 25 µs per point speed with high stability and included time domain measurement to validate, optimize, and sustain RF systems across the full counter-UAS lifecycle.
Broadband Antenna Characterization
Counter-UAS platforms rely on multiband and wideband antennas spanning common UAV control and navigation frequencies such as 433 MHz, 868/915 MHz, 1.2-1.6 GHz, 2.4 GHz, and 5.8 GHz. VNAs measure return loss, impedance stability, and bandwidth to ensure jammer power is efficiently radiated and not lost to mismatch. Feedline loss, matching networks, and combiner performance can also be verified to maximize effective radiated power and operational range.
Isolation and Coexistence Validation
High-power transmit antennas often operate alongside sensitive receivers used for detection, direction finding, or GNSS monitoring. Excessive coupling can degrade receiver sensitivity or create false signals. VNAs measure antenna-to-antenna isolation across sub-GHz through microwave bands, supporting optimization of antenna placement, shielding, filtering, and absorber use.
Wideband Electronic Attack Readiness
Modern UAV links frequently use spread spectrum, frequency hopping, or multi-band redundancy to resist interference. Counter systems must maintain consistent RF performance across wide spectral regions. VNAs provide continuous impedance and transmission measurements across hundreds of MHz to several GHz, identifying spectral weak points and ensuring broadband jammer effectiveness.
Development
Using scattering measurement configurations, VNAs support Radar Cross Section evaluation across L, S, C, and X bands (approximately 1–12 GHz). These measurements assist in optimizing detection strategies, calibrating sensing systems, and understanding how structural features, payloads, and materials influence UAV observability.
Field Diagnostics and Sustainment
VNAs detect cable faults, connector degradation, filter drift, and passive component failures caused by vibration, temperature, and operational stress. Time-domain transformation allows rapid localization of impedance discontinuities, supporting fast maintenance and sustained operational readiness.
Select Series Instruments
















› SC0402 – 4.5 GHz coverage for sub-GHz through microwave RF validation
› SC0602 – 6.5 GHz coverage for wideband electronic attack and isolation measurement
› SC0902 – 9 coverage for microwave sensing, RCS, and advanced RF characterization
› SN090X – 9 GHz coverage with 6-16 ports for phasedarray radar antenna development
› S5180B – 18 GHz coverage with pulse modulation capabilities
These instruments support secure, PC-controlled operation with no internal data storage, aligning with modern defense and classified deployment requirements.
Operational and Security Advantages
› License-Free Software for Windows and Linux
› Time Domain measurement at no additional cost
› Portable rugged design suitable for field deployment and harsh environments
› Fully software-defined architecture for automation and remote operation
Performance and Cost Efficiency
› Metrology-grade, with performance verified in an ISO17025/Z540 accredited lab
› 9 kHz to 18 GHz coverage supporting counter-UAS RF bands from sub-GHz through microwave
› High measurement stability for repeatable, defensible RF validation
› Supports wideband, frequency-agile, and multi-antenna
› Low unit cost with volume discount opportunities
Program and Lifecycle Value
› Identifies EMC, coupling, and antenna performance issues early
› Supports development, production test, and field sustainment
› Premier factory-direct customer support from RF measurement specialists at no additional cost
Mission Impact
The Select Series VNA provides unified RF measurement capability across the counter-UAS lifecycle. It ensures jammer antenna efficiency, preserves receiver sensitivity, validates broadband performance for frequency-agile engagements, supports RCS and sensing development, and verifies subsystem integrity. This directly improves detection reliability, electronic attack effectiveness, electromagnetic compatibility, and mission readiness in modern counter-UAS systems.
www.coppermountaintech.com