Transforming Nations: How AI is Shaping Digital Future & Security




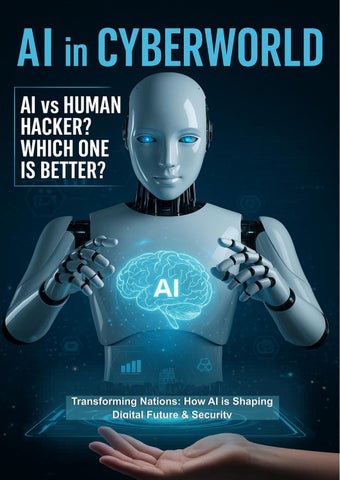
Transforming Nations: How AI is Shaping Digital Future & Security









in cybersecurity refers to the use of smart computer systems that can think, learn, and make decisions to protect digital information. Instead of waiting for humans to detect problems, AI can automatically find and stop cyber threats in real time.
AI helps cybersecurity systems to analyze data, detect unusual patterns, and predict possible attacks before they happen. For example, if a hacker tries to access a company’s data, the AI system can recognize the suspicious activity, block it, and alert security teams immediately.
Unlike traditional antivirus software that only detects known viruses,AI can identify new and unknown threats by learning how normal systems behave. When something unusual happens, it quickly takes action to prevent damage.
In short, AI in cybersecurity acts like a digital guard that never sleeps. It continuously monitors networks, learns from past attacks, and improves itself to keep data safe from hackers.

In Malaysia, the national agency leading this digital defense is Cybersecurity Malaysia (CSM), under theMinistry of Science, Technology and Innovation (MOSTI).
CSM uses advanced technologies including AI-powered systems to monitor, analyze, and respond to cyber threats that affect individuals, businesses, and government networks.

Every day, millions of cyber threats attack computers, phones, and networks all around the world. Hackers create smarter viruses, fake emails, and even deepfakes to steal data. Luckily, Artificial Intelligence (AI) has become a powerful defender against these modern dangers.
AI doesn’t just wait for an attack to happen, it predicts and prevents it. By studying data from past attacks,AI learns how hackers operate and uses that knowledge to stop future ones. Here are some ways how AI fight cyber threats


AI systems establish a baseline of normal network and user behaviour by analyzing vast amounts of data. Any deviation from this norm such as unusual login attempts, large data transfers at odd hours, or abnormal file modifications is immediately flagged as a potential threat, including zero-day attacks that traditional signature-based systems might miss

AI-driven tools analyze the content, context, sender information, and metadata of emails to identify and block sophisticated phishing attempts and spam. Natural Language Processing (NLP) helps systems recognize the subtle signs of social engineering, such as urgent tone or unusualwording.

AI processes and interprets massive volumes of data from global threat reports, security blogs, and malware databases to identify trends and forecast future attack scenarios. This allows organizations to move from a reactive to a proactive defense strategy


Who dominates the cyber battlefield?
AI- powered attacks can execute in 0.3 SECONDS
Ahumanhacker canperform around40-60 targetedattacks (32%)
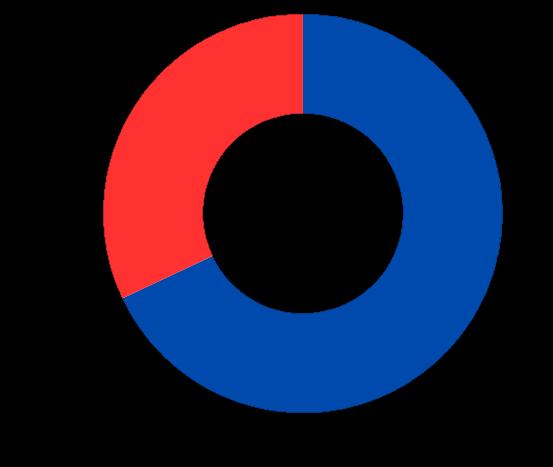
AI can launch 10,000 automated attacks per minute which is 68%
1. Analysing millions of logs instantly
2. Predicting threats
3. Automated patching
4. Detect phishing and & scams
5. Identify unknown malware

Human hackers take an average of 5-20 MINUTES
AI
Real -time Scanning Automated Patching
Analysing millions of Logs instantly
Predicting threats
Strategy Creative hacking Social engineering attacks Decision making
By 2027, 90% of all cyber attacks will involve AI



i. AI generated phishing emails 73% success rate
ii. Deeptake impersonation attacks a 43% increase in 2024
iii. Malware created by AI tools 30% more complex than before

Malaysia is increasingly adopting AI inn cybersecurity to combat rising threats, With initiatives like a government-led project to develop anAI tool for verifying digital contents and a focus on building AI-focused cybersecurity teams. Organizations are Also using AI for defensive purpose, while the government is focusing on ethical guidelines, training, and future-proofing its digital infrastructure against threats like quantum computing.
Malaysia’s cybersecurity landscape is strengthened by several key national agencies and influential leaders who work together to safeguard the country from rising cyber threats. One of the most notable figures is Dato’ Ts. Dr. Haji Amirudin Abdul Wahab, the former Chief Executive Officer of Cybersecurity Malaysia (CSM). Under his leadership, CSM expanded its national cybersecurity capabilities, enhanced Malaysia’s cyber incident response readiness, and strengthened international cooperation in digital security. His contributions have helped position Malaysia as one of the more cyber-resilient nations in the region.
At the national level, cybersecurity efforts are coordinated by the National Cyber Security Agency (NACSA), the central authority responsible for national cyber strategy and the protection of critical systems. NACSA works closely with ministries, agencies, and industries to ensure the country’s digital infrastructure remains secure.
Supporting these institutions is the Royal Malaysia Police (PDRM) through its Commercial Crime Investigation Department, which handles cybercrime cases such as hacking, financial scams, and identity theft



“Cybersecurity awareness Malaysian consumers is still concerningly low … we must ensure that our initiatives provide consistent guidance on how consumers can protect their digital identities better” - Dato’ Ts. Dr. Haji Amirudin Abdul Wahab

Meanwhile, the Malaysian Communications and Multimedia Commission (MCMC) plays a key role in digital regulation, online safety, and monitoring harmful online activities.
Together with the pioneering work of leaders like Dato’ Ts. Dr. Haji Amirudin, these agencies form Malaysia’s frontline defence against cyberthreats ensuringthe nationremains secure,resilient, and prepared for the challenges of an increasingly digital world.
In today’s era, where cyberattacks are becomingmore sophisticated and frequent, the collaboration between regulatory bodies, cybersecurity experts, and technology innovators is crucial. By combining strategic oversight with cutting-edge tools and proactive measures, Malaysia is strengtheningits digitalinfrastructureandbuildingpublic trustin asecure online environment.




“In dealing with terrorism, we cannot work alone. If Malaysia refuses to share intelligence, we will lose sight of activities from abroad, including AlQaeda elements or foreign terrorists entering the country.
“PDRM enters new phase using AI to tackle online terror threats”
The Royal Malaysia Police (PDRM) is entering a new phase in its efforts to combat terrorism by leveraging on artificial intelligence (AI) technology to strengthen investigations, rehabilitation, and monitoring of extremist activities in cyberspace.
Deputy Inspector-General of Police Tan Sri Ayob Khan Mydin Pichay said the use of AI is seen as a strategic step in facing terrorist threats, which are now increasingly shifting to online platforms.
“We have taken the initial steps to utilise AI for the benefit of the country in the context of investigations, detecting terrorist elements, and intercepting ideologies that are now spreading via social media,” he said.
“The Home Affairs Ministry (KDN) and PDRM have entered a new phase in exploiting AI to address terrorism issues,” he told reporters after attending a closed discussion on the publication of a special book regarding counterterrorism here last night.
“Many more departments within the Royal Malaysian Police will transition to usingAI to assist with investigations, recovery and monitoring in cyberspace.”
He said this when asked to comment on the proactive approach of the security forces in curbing the spread of extremist ideology in the new era.


As the digital world expands, Artificial Intelligence has become a vital force in strengthening cybersecurity. From predicting attacks to identifying threats in real time,AI is reshaping how we protect networks, data, and users. With continuous innovation, skilled experts, and smarter security tools, the cyber landscape is becoming more resilient and adaptive. In an age where cyber risks evolve every second, one truth stands out: the future of cybersecurity depends on the powerful collaboration between human intelligence and AIdriven technology. With the right strategies and awareness, we can build a digital ecosystem that is safer, smarter, and ready for tomorrow’s challenges.
1. What is AI for cybersecurity? | Microsoft Security. (n.d.). https://www.microsoft.com/enus/security/business/security-101/what-is-ai-for-cybersecurity
2. Artificial intelligence (AI) in cybersecurity: The future of threat defense. (n.d.). Fortinet. https://www.fortinet.com/resources/cyberglossary/artificial-intelligence-in-cybersecurity
3. Mail, M. (2025, October 28). Ayob Khan: PDRM enters new phase using AI to tackle online terror threats. Malay Mail. https://www.malaymail.com/news/malaysia/2025/10/28/ayobkhan-pdrm-enters-new-phase-using-ai-to-tackle-online-terrorthreats/196249?utm_source=chatgpt.com#google_vignette
4. Ramirez, S. (2025, October 7). AI Cyber Attacks Statistics 2025: HowAttacks, Deepfakes & Ransomware Have Escalated. SQ Magazine. https://sqmagazine.co.uk/ai-cyber-attacksstatistics/?utm_source=chatgpt.com