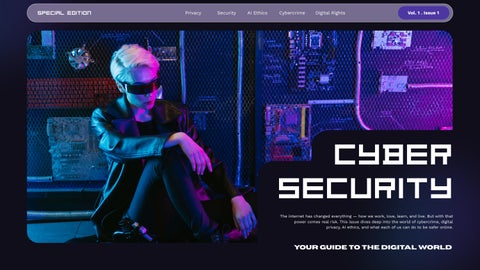
Cyber Security
The internet has changed everything — how we work, love, learn, and live. But with that power comes real risk. This issue dives deep into the world of cybercrime, digital privacy, AI ethics, and what each of us can do to be safer online. Your guide to the digital world

The World Changed. Did Our Habits?

Think about the last time you picked up a pencil and wrote a letter by hand. Or walked to a library to look something up. Or called a friend on a landline phone. For many of us, these feel like distant memories — relics of a slower, quieter world. In just two decades, the internet has quietly rewritten every rule about how human beings communicate, work, shop, fall in love, and make sense of the world around them.
Today, over 5.4 billion people use the internet that is nearly 67% of the entire world population, according to the International Telecommunication Union's 2023 report. We scroll before we sleep. We Google before we decide. We share before we think. And in this hyper-connected world, a single click can change your life sometimes for the better, sometimes in ways you never imagined.
But here is the uncomfortable truth: while we have become extraordinarily good at using technology, most of us have not learned to use it safely or wisely. We protect our homes with locks and our cars with insurance, yet we leave our digital doors wide open — using the same password on every website, clicking suspicious links, oversharing personal details, and ignoring the invisible trail of data we leave behind every day.
5.4B
Internet users worldwide as of 2023 — 67% of the global population
Source: International Telecommunication Union (ITU), 2023
$8T
Estimated global cost of cybercrime in 2023, projected to reach $10.5 trillion by 2025
Source: Cybersecurity Ventures, 2023 Cybercrime Report
95%
Of cybersecurity breaches are caused by human error — not technical failures
Source: IBM Security, Cost of a Data Breach Report, 2023
The $8 Trillion Shadow: Understanding Cybercrime
$12.5B
Total cybercrime losses reported to the FBI's Internet Crime Complaint Center (IC3) in 2023 — the highest ever recorded.
Source: FBI Internet Crime Report, 2023
It is the largest transfer of economic wealth in history. Cybercrime does not look like what the movies show — it's not always a hoodie-wearing hacker in a dark basement. More often, it's an email that looks perfectly normal. A link that seems safe. A moment of trust that someone exploits.
Written by Arjun Sinha Investigative Editor
880,418
Complaints received by IC3 in 2023 alone — averaging over 2,400 complaints every single day.
Source: FBI IC3 Annual Report, 2023 300%
Increase in reported cybercrimes since the COVID-19 pandemic began in 2020, as more life moved online.
Source: Interpol, Cybercrime COVID Impact Report
By the Numbers: The Global Cyber Crisis

What Is Cybercrime, Really?
The Human Element: Why We Get Fooled Cybercrime and India: A Growing Crisis
The word "cybercrime" sounds technical and distant. But at its heart, it is simply crime that uses computers and the internet as tools the same old human impulses of greed, manipulation, and cruelty, just wearing a digital mask. Cybercrime comes in many forms. Phishing is when criminals send you emails or messages that look like they're from your bank, your boss, or a government office tricking you into giving up your passwords or clicking malicious links. According to the Anti-Phishing Working Group (APWG), there were over 4.9 million phishing attacks reported in 2022, the worst year on record.
Ransomware is when hackers break into your computer system and lock all your files then demand a payment (ransom) to unlock them. In 2021, the Colonial Pipeline ransomware attack in the United States caused fuel shortages across the eastern seaboard, showing how a single hack can impact millions of ordinary people.
Why do these attacks work? Because they exploit something very human: trust. A well-crafted phishing email is not full of obvious spelling mistakes anymore. Modern cybercriminals use social engineering psychological tricks that exploit our emotions like fear, urgency, and authority.
Imagine receiving an email that says: "Your bank account has been compromised. Click here immediately to secure your funds." Your heart rate spikes. You panic. You click and that is exactly what the criminal was counting on. IBM's 2023 Cost of a Data Breach Report found that phishing was the most common initial attack vector, responsible for 16% of all data breaches, with an average cost of $4.76 million per breach.
Identity theft is another massive problem. When criminals steal your personal information your Social Security number, bank details, or even just your name and address — they can open credit cards in your name, take out loans, file fake tax returns, or sell your data on the dark web. The U.S. Federal Trade Commission received 5.7 million reports of fraud and identity theft in 2022.
India is the world's largest democracy and one of the fastest-growing digital economies — and that growth comes with risk.
According to the Indian Computer Emergency Response Team (CERT-In), over 1.39 million cybersecurity incidents were reported in India in 2022. That is roughly 3,800 cases per day.
The rise of UPI (Unified Payments Interface) has brought millions of Indians into the digital economy but it has also brought new fraud. Fake customer care numbers, QR code scams, and vishing (voice phishing) calls posing as bank representatives have become epidemic. The National Cybercrime Reporting Portal (cybercrime.gov.in) received over 940,000 complaints in 2023 alone.
India's National Crime Records Bureau (NCRB) data shows that cybercrimes increased by 24.4% in 2022 compared to 2021. Young people between the ages of 18 and 30 are among the most targeted and the most vulnerable, because they are highly active online.
"Cybercrime doesn't
discriminate. It targets governments, hospitals, schools, businesses, and individuals with equal enthusiasm. Anyone connected to the internet is a potential target."
"Your
Password Is Your Weakest Link"
A conversation with Dr. Anjali Krishnamurthy, Cybersecurity Researcher at IIT Delhi and former consultant to CERT-In
Dr. Krishnamurthy, most people think hackers target big companies, not individuals. Is that still true?
That is one of the most dangerous myths in cybersecurity. Yes, big breaches make the news — but criminals are opportunists. They use automated tools that scan millions of devices simultaneously, looking for any easy entry point. A teenager with a weak password on their social media account is just as attractive a target as a corporation, because that account can be sold, used for fraud, or used to access their family's banking information. Everyone is a target. The question is whether you make yourself an easy target or a difficult one.
What are the most common mistakes ordinary people make online?
Number one, without question, is password hygiene. People use the same password everywhere, or use incredibly simple passwords like their name, birthday, or "123456". According to NordPass's 2023 report, "123456" was still the most common password in the world, used by 4.5 million accounts. Criminals have massive lists of common passwords and they try them automatically. It takes less than one second to crack a 6-character password. The second mistake is not enabling two-factor authentication (2FA). Even if someone gets your password, 2FA means they still can't get in. It is free, it takes two minutes to set up, and it stops the majority of account takeover attacks cold. The third mistake is clicking links without thinking. You receive an urgent email, you panic, you click. Always verify before you click hover over links to see where they actually lead, or go directly to the website yourself.
Quick Security Checklist
1) Use a password manager (Bitwarden, 1Password) and create unique passwords for every account
2) Enable two-factor authentication on every account that offers it, especially email and banking
3) Keep your phone, laptop, and apps updated. Updates patch security holes that criminals exploit
4) Never click links in unexpected emails or messages. Go directly to the website by typing the address
5) Your bank will NEVER ask for your OTP, CVV, or full card number over a phone call or message
6) Avoid using public Wi-Fi for banking or shopping. If you must, use a VPN service
Privacy Violation Facebook–Cambridge Analytica: The Data That Changed Elections (2018)
87M
Users affected $5B FTC fine 2 elections Potentially influenced
This case changed how the world thinks about data privacy. Cambridge Analytica, a British political consulting firm, harvested the personal data of up to 87 million Facebook users without their explicit consent, using a personality quiz app that collected not just the quiz-taker's data but all of their friends' data as well.
This data was allegedly used to build psychological profiles of American voters and micro-target them with political advertising during the 2016 US Presidential Election and the Brexit referendum. The scandal revealed how social media platforms were allowing third parties to harvest massive amounts of personal data through loopholes in their privacy policies.
Facebook was fined $5 billion by the US Federal Trade Commission — the largest privacy fine in history at the time. The scandal led to widespread calls for data protection legislation and prompted the European Union's General Data Protection Regulation (GDPR) to be enforced in May 2018.
The Six Pillars of Ethical Technology Use
1) Honesty & Authenticity
Do not pretend to be someone you are not. Do not spread information you have not verified. Do not manipulate others through fake profiles, bots, or deceptive content.
2) Respect for Privacy
Treat other people's personal information as you would want yours treated. Do not share private messages, photos, or data without explicit permission from the people involved.
3) Intellectual Property Rights
Respect the work of creators. Piracy harms individuals musicians, writers, filmmakers not faceless corporations. Credit sources and creators when sharing their work.
4) Kindness & Non-Harm
Online anonymity does not make hurtful words harmless. Cyberbullying causes real psychological harm. Think carefully before posting anything that could demean or hurt another person.
5) Accountability
Take responsibility for your digital actions. If you spread misinformation, correct it. If you hurt someone online, apologize. Own your digital footprint.
6) Environmental Consciousness
Technology has a physical footprint. Data centers consume enormous energy. Unnecessary emails, cloud storage, and device waste have real environmental costs. Use technology mindfully.
What the Experts Are Saying

“The biggest vulnerability in any system is not the software — it's the human being using it. You can spend millions on security technology and still be breached because one employee clicked a phishing link. Security culture is more important than security technology.”
Bruce Schneier
Security Technologist · Author of "Click Here to Kill Everybody" · Fellow, Harvard Kennedy School
“AI is neither good nor bad — it is a tool. But tools can be used for liberation or oppression. The question we must always ask about any AI system is: who built it, what data did they use, whose interests does it serve, and who bears the cost when it fails?”
Timnit Gebru
AI Ethics Researcher · Founder, DAIR Institute · Former Google AI Lead
“Children do not understand the permanence of the internet. They post something in a moment of excitement or pain, not realising it may follow them for life. We need to teach digital literacy as seriously as we teach reading — because in the 21st century, they are the same thing.”
Kailash Satyarthi
Nobel Peace Prize Laureate · Child Rights Activist · Founder, Bachpan Bachao Andolan
“Cybersecurity is a shared responsibility. It is not something you delegate to your IT department or your government. Every person who uses a computer or a smartphone is a participant in the digital ecosystem — and every one of us has a role to play in keeping it safe and ethical.”
Dr. Sanjay Bahl
Director General, CERT-In (Indian Computer Emergency Response Team)