




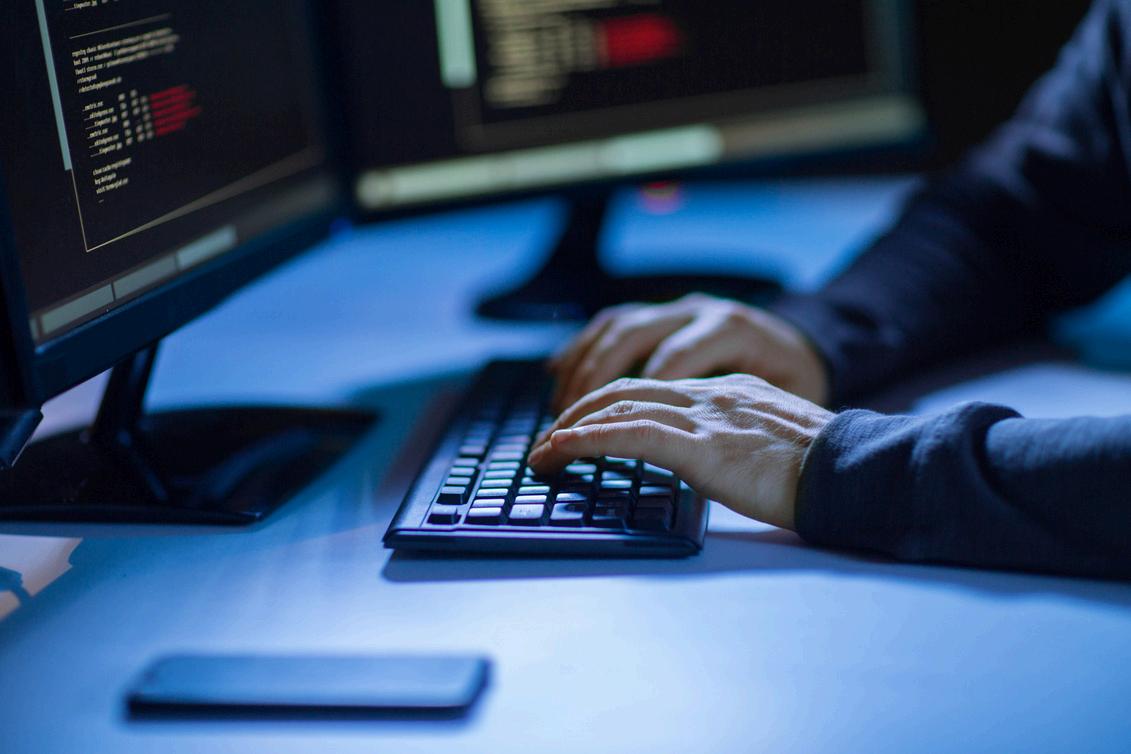
Threat Detection Services help organizations find and report suspicious activities within their IT systems. They continuously monitor servers, networks, and endpoints to detect malware, unauthorized logins, or abnormal data movement. These services are essential for keeping business operations secure and stable.
Example: A retail brand uses a Threat Detection Service to identify fake website traffic that tried to steal customer card details.

Businesses depend on these services to prevent security incidents and reduce downtime. They detect early signs of phishing, ransomware, and internal misuse before issues spread across the system. Such services also help meet compliance standards for industries handling sensitive data.

Example:
A bank’s security team detected a login attempt from an unknown location using its threat detection software, stopping data theft instantly.
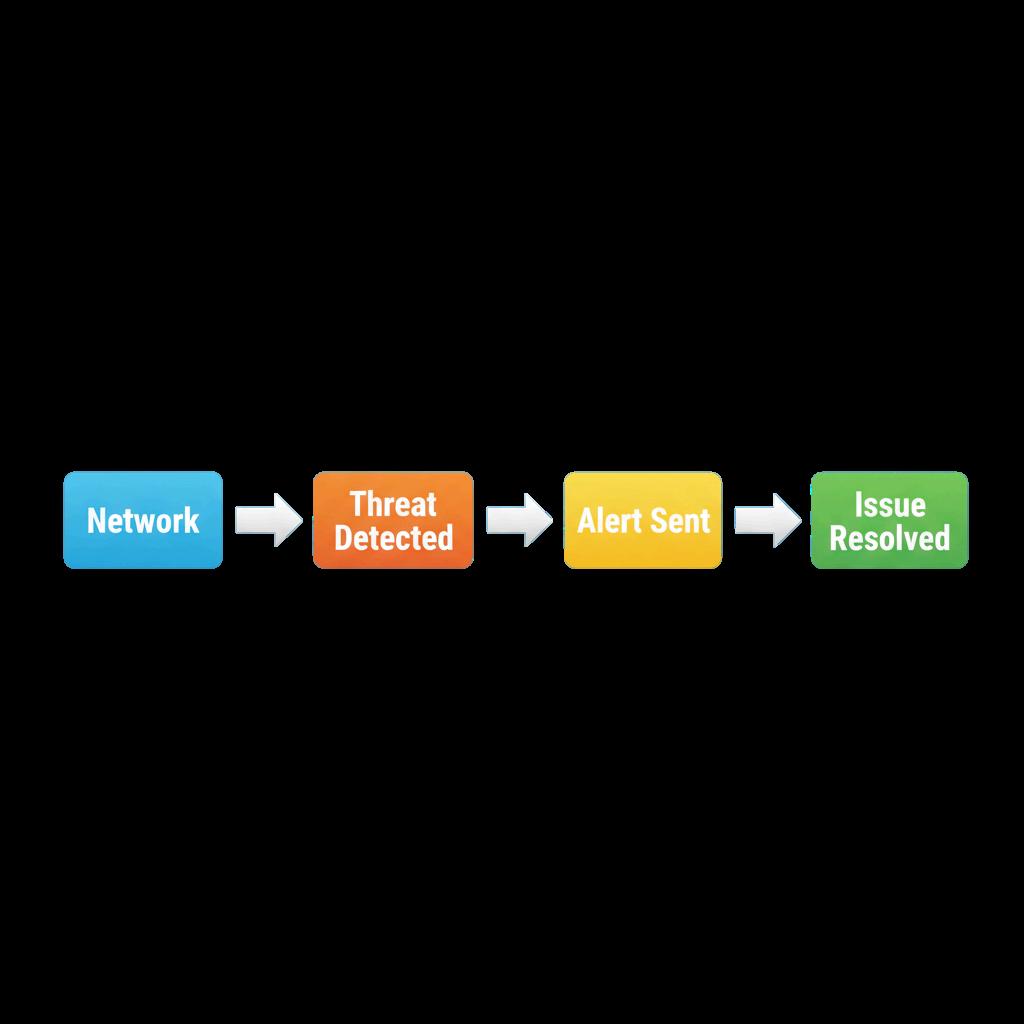



24/7 System Monitoring: Tracks every activity in real time.
Detailed Reports: Summarizes incidents for quick action.s IT teams through email or dashboard.
Anomaly Detection: Spots unexpected patterns or logins.
Instant Alerts: Notifies IT teams through email or dashboard.
Integration Options: Works with other cybersecurity tools seamlessly.
Example: A hospital network uses these services to track unauthorized access to patient files during non-working hours.

Select a service that offers clear reports, userfriendly dashboards, and quick alert responses. Ensure it fits your company’s IT setup and supports both on-site and cloud environments. Communication with your staff about these tools keeps everyone aware and responsible.



Example: A logistics company chose a cloudbased Threat Detection Service that sends weekly summaries to managers, helping them stay updated on potential risks.

