
International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
Andrew Renault1
1 Grad Student, Dept. of Aeronautical Science, Capital Technology University, South Laurel, Maryland, USA
Abstract - This study investigates the urgent need to modernizeairtrafficcontrol(ATC)systemstoensurethesafe andeffective integrationof unmannedaerialvehicles(UAVs) into controlled airspace. As UAV proliferation accelerates globally,currentATCinfrastructureremainspoorlyequipped to address emerging safety threats, including mid-air collisions, airspace violations, cyber intrusions, and the weaponization of UAVs for malicious purposes. To address these challenges, a mixed-methods approach was employed, combiningquantitativesimulationsandqualitativedocument analysis to generate comprehensive, actionable insights. The quantitative component utilizes a structured Design of Experiments (DOE) framework to simulate four critical operationalconfigurations:UAVCharacteristics,Surveillance Technologies, Cybersecurity Vulnerabilities, and Radar Detection Performance. Each configuration was modeled across multiple factors and levels, generating empirical performance indicators such as detection accuracy, safety scores, and cyber resilience indices. Statistical analysis, includinganalysisofvariance(ANOVA),identifiedsignificant main effects and interaction patterns that influence system performance and reliability. To complement the simulation findings, a qualitative analysis was conducted on a carefully curatedsetof60scholarlyandtechnical documents,selected fromabroaderpoolofover300peer-reviewedsources.These documents were analyzed to extract operational themes, validate model assumptions, and identify regulatory or deployment constraints. The convergence and divergence betweensimulatedanddocumentedinsightshighlightcritical areas requiring further empirical validation and inform the prioritization of modernization strategies. This integrative research demonstrates that AI-enabled surveillance, robust cybersecuritysafeguards,andmultistaticradarconfigurations significantlyenhanceUAVdetectionandresponsecapabilities. Findingsunderscorethenecessityofadoptingasystems-level approach to UAV integration that balances technological innovation with safety, regulatory foresight, and national security concerns.
Key Words: UAV,UAVintegration,ATC,drones,airtraffic control, AI in aviation, radar limitations, cybersecurity, humanfactors,regulatoryframeworks,multi-sensorfusion
Themodernizationofairtrafficcontrol(ATC)systemshas become an urgent priority as global airspace faces unprecedented challenges from the rapid proliferation of unmanned aerial vehicles (UAVs), increasing aerial congestion, and the growing complexity of cybersecurity threats.LegacyATCsystems largelydesignedformanned aviation struggle to maintain situational awareness, enforce separation standards, and ensure security in an environmentthatnowincludesautonomous,low-altitude, and non-cooperative UAVs. Foundational studies have highlighted these issues as key operational stressors that demand immediate intervention [1]. In addition to traffic volume and surveillance limitations, the rising weaponizationofUAVspresentsnationalsecurityconcerns, includingtheriskofterrorism,illicitairspaceincursions,and payload delivery in restricted zones. Furthermore, the documentedriseinnearmid-aircollisionsinvolvingUAVs hasincreasedsafetyrisksto bothcivilianandcommercial aviation.Acomprehensiveliteraturereviewexaminedover 300publisheddocuments,fromwhich60wereselectedto support this study's qualitative dimension. These sources collectively outline the technical, policy, and regulatory barrierstoUAV-ATCintegrationandreinforcetheurgency fortransformativechange[2].

To address these multifaceted challenges, this paper adopts a mixed-methods approach that combines quantitativesimulationwithqualitativedocumentanalysis. AtthecoreofthequantitativestrategyisafactorialDesignof

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
Experiments (DOE) framework that models four critical UAV-ATCconfigurations:UAVCharacteristics,Surveillance Technologies, Cybersecurity Vulnerabilities, and Radar Detection Performance. Each DOE configuration includes multipleindependentfactorsandlevelsdesignedtoreplicate operationalbehaviorsandgenerateempiricalmetricssuch asdetectionaccuracy,safetyscores,andsystemresilience indices. Statistical analyses, including analysis of variance (ANOVA), are applied to detect significant trends, main effects,andinteractionoutcomes[3]–[62].Complementing thisisa qualitativedocumentanalysisof60scholarlyand technical sources categorized by configuration. These documentsprovideoperationalcontext,exposelatentpolicy gaps,andvalidateorchallengemodelassumptions,allowing for a robust triangulation of findings. The hybrid methodologystrengthenstheinternalvalidityofsimulation outcomesandensuresthatfindingsarenotonlystatistically soundbutoperationallyinformed.
Simulated environments were constructed using parameters grounded in field literature and real-world systemcharacteristics,suchastelemetryencryptionfailure rates,spoofingsusceptibilities,radarcross-sectionprofiles, anddetectionthresholds[2],[4]–[17].Theseconstructsoffer atestbedforemulatingUAV-ATCinteractionscenariosand assessing system response under varying conditions. The remainder of this paper presents the research design, simulation methodologies, qualitative synthesis, and resultingimplicationsforATCmodernization.Collectively, these findings are intended to inform policymakers, engineers,andaviationstakeholdersoftheurgentneedfor empiricallygroundedreformstosafelyintegrateUAVsinto nationalandglobalairspacesystems.
ContemporaryATCsystemsfacemountingchallengesin managingthecomplexoperationaldemandsintroducedby therapidproliferationofunmannedaerialvehicles(UAVs). These systems were originally designed for traditional mannedaviationandareill-equippedtodetect,track,and manage UAVs that operate at lower altitudes, follow autonomousorunpredictableflightpatterns,andfrequently deviatefromconventionaltrafficmanagementprotocols[2]. As UAV integration accelerates spanning commercial, recreational, industrial, and governmental use the limitationsoflegacyATCinfrastructurehavebecomemore pronounced. Critical shortfalls exist in radar coverage, identificationprotocols,andreal-timedatafusionrequired to maintain situational awareness in congested airspace. Compounding these issues is the growing risk of mid-air collisionsbetweenUAVsandmannedaircraft,particularly nearbusyterminalairspacesorwithinurbancorridors.The absence of standardized separation rules and insufficient sense-and-avoidcapabilitiescontributetoarisingincident rateandincreasingcontrollerworkload.
Cybersecurityvulnerabilitiesfurtherintensifytheserisks. UAV communication links are susceptible to spoofing, jamming, telemetry injection, and other forms of cyber intrusionthatcouldcausemisidentification,routedeviation, orhostiletakeover.Theseconcernsarenolongertheoretical. ThereisincreasingevidenceofUAVsbeingrepurposedfor malicious intent, including weaponization for reconnaissance, smuggling, and even terrorism-related applications. The potential for intentional misuse in restrictedorhigh-valueairspacezoneselevatestheurgency of addressing system gaps. In addition, fragmented international surveillance standards and inconsistent regulatory frameworks hinder coordinated progress. Withoutcomprehensivemodernization includingupgrades to surveillance architecture, implementation of Artificial Intelligence (AI)-enabled decision support systems, and harmonizedpolicymandates thesafeintegrationofUAVs intocontrolledairspacewillremainacriticalandunresolved operational vulnerability. The convergence of safety, security,andregulatoryconcernsunderscorestheneedfor empiricallygrounded,cross-disciplinarysolutionstoprotect futureairspaceintegrity.
Thepurposeofthisstudyistoexaminethetechnological, regulatory, and human-centered barriers to effective UAV integrationintoATCsystemsthrougha structuredmixedmethodsapproach.Buildingonthefoundationalfindingsof two predecessor studies, “Navigating the Skies: The NecessityforUpgradingAirTrafficControlSystems”[1]and “SeeingtheUnseen:ALiteratureReviewofUAVDetection Gaps and Surveillance and Security Solutions for ATC Modernization”[2],thispaperdeploysaDOEframeworkto simulatehowvarioussystemfactorsaffectairspacesafety. ThesefactorsincludeUAVdesignattributes,communication link types, surveillance sensor technologies, radar configuration,andcybersecuritysafeguards.
This quantitative simulation is complemented by a qualitativedocumentreviewthatsynthesizesfindingsfrom 60 strategically selected scholarly and industry sources. These60referenceswerecuratedfromabroaderarchiveof over 300 documents to ensure thematic relevance, methodologicalrigor,andcoverageacrossthefourprimary areas of interest: UAV characteristics, surveillance technologies, cybersecurity vulnerabilities, and radar detection performance. The integration of these two methodologicallensesprovidesarobustbasisformodeling realisticUAV-ATCinteractionscenariosandforproducing operationally relevant recommendations for air traffic managementmodernization.
This study is guided by a central research inquiry that examineshowdifferentUAVandATCsystemconfigurations

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
influence integration safety within controlled airspace environments. The analysis is grounded in a DOE methodology and supported by qualitative document synthesistoprovidecomprehensiveinsightintooperational, technical,andregulatorydynamics.
Thisstudyisguidedbythefollowingoverarchingresearch question:
RQ1: How do various UAV operational and ATC system configurationsaffecttheoverallsafetyeffectivenessofUAV integrationincontrolledairspace?
Toaddressthemultipledimensionsofthisquestion,the study investigates four factorial configurations. Each configurationalignswithatargetedsub-question,evaluated throughsimulationmetricsandvalidatedwithsupporting qualitativeinsights:
RQ1a:TowhatextentdoUAVcharacteristics(flightprofile, communicationtype)influenceoperationalsafety?
RQ1b:Howdovariationsinsurveillancetechnologiesaffect detectioneffectivenessincomplexairspaces?
RQ1c: How do cybersecurity protocols and threat types impacttheintegrityofUAV-ATCcommunication?
RQ1d: What is the relationship between radar detection parametersandUAVvisibilityinATCsystems?
ToempiricallyexaminehowsystemfactorsimpactUAV integration into ATC environments, this study defines specific null and alternate hypotheses for each of the four configurations investigated through the DOE simulation. Thesehypothesesaligndirectlywiththeresearchquestions inSection1.3andserveasthebasisforstatisticalanalysis, includingANOVAtestingandinteractioneffectsmodeling.
Table 1.1 presents the hypotheses structured by configuration theme. Each pair of hypotheses (null and alternate) targets whether the independent variables representedasFactorAandFactorB meaningfullyaffect thedependentoutcome:operationalsafetyeffectiveness.
Table 1.1 - Null and Alternate Hypotheses for Each
Configuration Theme Hypothesis ID NullHypothesis (H₀) Alternate Hypothesis(Hₐ)
1.UAV Characteristics
H₀₁/Hₐ₁
2.Surveillance Technologies
H₀₂/Hₐ₂
H₀₁:Thereisno statistically significant differencein operational safety effectiveness basedonUAV flightprofileor communication type.
H₀₂:Thereisno statistically significant differencein operational safety effectiveness basedon sensortypeor airspace complexity.
Hₐ₁:Thereisa statistically significant differencein operational safety effectiveness basedonUAV flightprofileor communication type.
Hₐ₂:Thereisa statistically significant differencein operational safety effectiveness basedonsensor typeorairspace complexity.
3. Cybersecurity Vulnerabilities
H₀₃/Hₐ₃
4.Radar Detection Performance
H₀₄/Hₐ₄
H₀₃:Thereisno statistically significant differencein operational safety effectiveness basedon security protocolor threattype.
H₀₄:Thereisno statistically significant differencein operational safety effectiveness basedonUAV radarcross section(RCS) sizeorradar type.
Hₐ₃:Thereisa statistically significant differencein operational safety effectiveness basedon security protocolor threattype.
Hₐ₄:Thereisa statistically significant differencein operational safety effectiveness basedonUAV radarcross section(RCS) sizeorradar type.
This study focuses on simulated evaluations of UAV integrationchallengeswithinATCsystems,utilizingaDOE framework to investigate operational safety, detection performance, and cybersecurity resilience. The scope includes four factorially structured configurations: UAV characteristics, surveillance technologies, radar detection performance, and cybersecurity vulnerabilities. These

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
configurations were selected based on the most critical bottlenecksidentifiedinpriorfoundationalanalyses[1],[2] and refined using insights from over 300 peer-reviewed academicandoperationalpublications.Fromthislargebody of literature, 60 high-quality, thematically aligned sources were selected to support both quantitative modeling and qualitativesynthesis.Thesimulationswereexecutedunder controlledparametervariationsrepresentingrealisticUAV behaviors, communication types, sensor setups, and cyberattack vectors. Although the factorial structure provides a robust method for analyzing main effects and interactions,thestudyisinherentlylimitedbyitsrelianceon simulated data. The scenarios were constructed using literature-derived values for latency, spoofing resistance, andRCSprofiles,whichmaynotcapturethefullvariability encountered in dynamic or adversarial environments [4], [8],and[24].
Moreover, while the simulation environment includes representativesystemparameters,itexcludesdirecthumanin-the-looptesting,liveoperationalATCdata,oremergent threats not explicitly modeled. As such, variables such as unpredictableUAVmaneuvering,real-timepilotjudgment, or systemic ATC fatigue are not directly observed. These limitations restrict the generalizability of results to some extent, although model assumptions were cross-validated usingbothquantitativereferencesandqualitativeliterature patterns[2],[23],and[32].Tomitigatetheseconstraintsand enrich the validity of the findings, a mixed-methods approach was employed. In parallel with simulation modeling, a qualitative document analysis was conducted across the same four configurations. The 60 selected documents provided thematic triangulation by exposing conceptual gaps, reinforcing assumptions, and anchoring quantitativeoutcomesinreal-worldoperationalliterature [18],[19],and[30].
This methodological integration of empirical modeling withliterature-basedreviewstrengthensthecredibilityand applicability of the results, ensuring they are both analytically rigorous and grounded in current aviation research.Futureresearchisencouragedtobuilduponthese findings by incorporating empirical validation strategies, suchaspilot-in-the-loopsimulations,fieldexperiments,or integrationwithnationalATCsurveillancedatarepositories. These efforts would enhance external validity, support regulatory adoption, and further inform risk mitigation strategiesinUAVtrafficmanagementsystems.
Thissectionoutlinesthemethodologicalstructureused toevaluatethefourcoreconfigurationscriticaltointegrating UAVsintoATCsystems.Amixed-methodsresearchdesign wasadoptedtotriangulatefindingsacrossbothquantitative and qualitative components, ensuring that insights are statisticallyvalidatedandgroundedinoperationalliterature. Thequantitativeanalysiswasconductedusingastructured
DOE approach. Three of the configurations UAV Characteristics, Surveillance Technologies, and Radar DetectionPerformance wereanalyzedusinga2×3factorial design. The fourth configuration, Cybersecurity Vulnerabilities, used a 3×2 factorial design. Each configurationincludedfivereplicationspertestcell,which supported robust statistical inference and reduced the influenceofvariabilityacrosstrials.Independentvariables were selected based on literature-supported factors, and dependentvariablesincludedsafety,surveillance,detection effectiveness, and cyber resilience scores. This simulation framework builds on prior research published in two foundationalstudies.Thefirststudyidentifiedthesystemic challenges in ATC modernization, focusing on UAV proliferation, cybersecurity risks, and radar system limitations [1]. The second study reviewed over 300 scholarlyandtechnicaldocuments,ultimatelyselecting60 sources that offered thematic insights into surveillance, regulation, cybersecurity, and integration risks [2]. These sources informed the experimental parameters and contextualframingofthisstudy.
Each configuration modeled realistic UAV–ATC interactions,includingvariablessuchasUAVflightbehavior, communication protocols, sensor fusion techniques, and threattypes.TheDOEdesignenabledtheevaluationofboth main effects and interaction effects through ANOVA, allowingidentificationofstatisticallysignificantinfluences among system components [3]–[60]. Complementing the simulations,aqualitativedocumentreviewwasconductedto identify patterns, validate simulation assumptions, and highlightoperationalconstraints.The60selectedreferences were mapped to each configuration and analyzed for recurring themes and conceptual gaps. This qualitative analysis enriched the quantitative findings by grounding theminreal-worldchallengesanddomain-specificpractices. Bycombiningfactorialsimulationandthematicreview,this methodology delivers a comprehensive evaluation of UAV integration challenges and informs ATC modernization strategies that are both empirically robust and practically relevant. It also establishes a foundation for future work involving real-world data collection, pilot-in-the-loop experiments,orliveoperationalsystemtesting.
Thisresearchadoptsamixed-methodsapproachwithan emphasisonquantitativesimulationguidedbyfactorialDOE methodology. The rationale for this design is to systematically assess how variations in UAV operational characteristicsandATCsystemconfigurationsinfluencekey performance metrics such as detection accuracy, communication integrity, controller workload, and cyber resilience. Four configurations were tested using factorial designs.Threeuseda2by3format,andoneuseda3by2 format. Each configuration was evaluated through five replications per treatment cell to ensure statistical

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
reliability. This simulation strategy allows for rigorous examinationofinteractioneffectsandmainfactorinfluences, whichareoftenunderexploredinUAVintegrationresearch. Building on the theoretical and empirical foundations presented in earlier studies [1], [2], this study operationalizes key variables such as UAV geometry, communicationprotocol,sensorfusionstrategy,andcyber safeguardtypeintomeasurablefactors.Thesesimulations emulate real-world stressors using performance scoring modelsderivedfromdocumentedATCvulnerabilitiesand UAVsystembehaviors[3]–[62].
The research design also incorporates a qualitative component through a curated document analysis of 60 scholarlyandtechnicalsources.Thisanalysissupportsand validates the simulated findings by contextualizing them within current academic and regulatory discourse. Qualitative patterns in literature, including AI trust dynamics, latency trade-offs, and threat typologies, help interpret model outcomes and guide policy-relevant recommendations.Thiscombinedmethodologicalapproach enablesanuancedunderstandingofUAV–ATCinteractions. Thesimulation-basedDOEprovidesastructuredevaluation ofsystem behaviors,while thequalitative reviewgrounds thefindingsinoperationalrealities.Together,thesemethods produce empirically defensible and practically useful insights for modernizing ATC systems in response to increasingUAVpresence,evolvingthreatenvironments,and legacytechnologyconstraints.
This study employs a structured DOE framework to simulate and evaluate the effects of various UAV and ATC system configurations. The DOE methodology enables preciseidentificationofmaineffectsandinteractioneffects acrossmultipleoperationalvariables,whichisessentialfor capturing the complexity inherent in modern air traffic environments. Three of the configurations (UAV Characteristics, Surveillance Technologies, and Radar DetectionPerformance)utilizea2×3factorialdesign,while theCybersecurityVulnerabilitiesconfigurationadoptsa3×2 factorial structure. These designs allow for systematic analysisofinteractionsbetweentwoindependentvariables across multiple levels. Each 2×3 or 3×2 factorial design results in six unique experimental conditions per configuration, with eachcondition replicatedfivetimesto ensurestatisticalvalidityandreliability.
Independent variables were selected based on documented vulnerabilities and operational priorities identified in the literature [3] to [62]. These include UAV flightprofile,communicationtype,sensortype,datafusion method,safeguardprotocol,threattype,radarconfiguration, and airspace environment. Dependent variables such as safety scores, composite surveillance scores, detection effectiveness scores, and cyber resilience scores were derived from literature-informed scoring models and
tailored to reflect air traffic control performance metrics. The simulation environment assumes independence of observations and normally distributed responses across trials.Theseassumptionsareconsistentwithprioraviation safetymodelingstudies and facilitatetheuse ofstatistical techniquessuchasANOVAtodetectstatisticallysignificant trends.
The factorial DOE approach not only enables highresolutioncomparisonofUAV–ATCsysteminteractionsbut also supports hypothesis testing aligned with real-world operational constraints and regulatory gaps outlined in previousresearch.
Thisstudyappliesa2×3ora3×2fullfactorialdesignfor each of the four UAV–ATC integration configurations to systematicallyexaminetheinteractioneffectsbetweentwo independentvariables.Ineachexperiment,twovariablesare manipulated onewithtwolevelsandtheotherwiththree levels resultinginsixuniqueconditioncombinationsper configuration.Eachofthesesixcombinationsisreplicated five times, producing a total of 30 observations per configuration.Thisreplicationensuresstatisticalrobustness andminimizestheinfluenceofrandomvarianceacrosstrials [3]–[62].
The configurations and their experimental focus are as follows:
UAV Characteristics:Thisconfigurationinvestigateshow different UAV flight profiles (e.g., stable vs. agile maneuvering)andcommunicationmethods(e.g.,encrypted vs. unencrypted telemetry) impact safety performance. Performanceisassessedthroughsimulation-derivedsafety effectiveness scores, which reflect risk exposure and responseaccuracyundercontrolledconditions.
Surveillance Technologies:Here,theinteractionbetween sensor types (e.g., visual vs. infrared) and data fusion approaches (e.g., rule-based vs. AI-based integration) is examined. The objective is to quantify the impact on detectionaccuracyandresponsetimeinhigh-trafficairspace segments.Simulationmetricssuchasdetectionlagandfalsenegative rates are used to evaluate the surveillance effectiveness.
Cybersecurity Vulnerabilities: In this configuration, simulationsmodeltheinteractionbetweenthreattype(e.g., spoofing,jamming)andresponselatency(e.g.,instantaneous vs.delayedmitigation).Thissetupevaluateshowquicklya systemcanrecoverfromorresistattacks,measuredthrough resiliencescoresandcommunicationintegrityrates.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
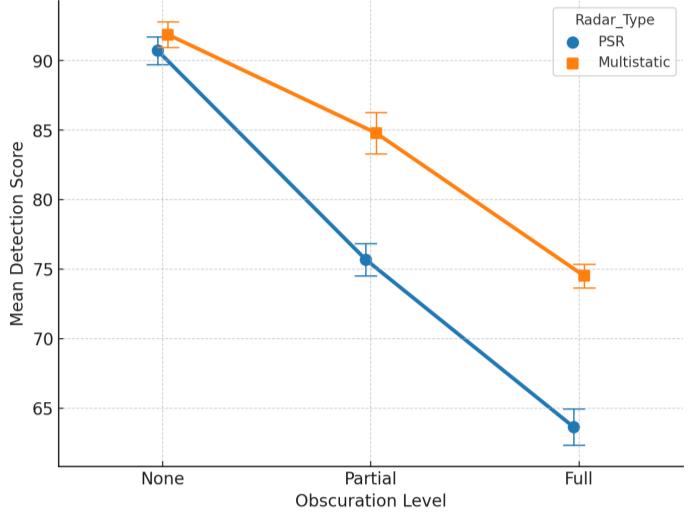
Radar Detection Performance: This configuration evaluates how different radar systems (e.g., primary vs. multistatic) perform under varied environmental obscurationconditions(e.g.,clearvs.urban-cluttered).The goal istoassessradarresilienceandUAVvisibilityloss in challenging scenarios, validated through detection signal consistencyandlossfrequency.
Each experiment is structured to generate measurable outputsrelevanttoATCperformanceandsafetymetrics.By maintaining a consistent factorial structure across configurations, the study enables comparative analysis of variable sensitivity, interaction effects, and crossconfigurationtrends.
ThisconfigurationevaluateshowUAVflightprofileand communication method influence operational safety in controlled airspace. Both factors are central to UAV integration with ATC systems and provide insights into modernizationstrategies.
Factor A. UAV Flight Profile. Two levels were modeled: Fixed-WingandMultirotorUAVs.Fixed-wingUAVstypically operate at higher speeds and longer ranges, making them efficientforsurveillancebutmoredifficulttodetectdueto narrowerradarcross-sections.MultirotorUAVsflyatlower speedswithhoverandmaneuveringcapability,producing variable signatures that may alter detectability in dense airspace[6],[9],and[13].
Factor B. Communication Method. Three levels were included:AutomaticDependentSurveillance–Broadcast (ADS-B), Remote ID, and None. UAVs without active broadcastingincreasecollisionriskandreducesituational awareness[5],[8],and[11].Bycontrast,ADS-BandRemote ID improve traceability but may also introduce vulnerabilitiestospoofingandinterception.
The 2×3 factorial design produced six unique configurations as shown in Table 2.1. Each condition was replicated five times, resulting in 30 total runs. The dependent variable was the Safety Effectiveness Score, a composite metric derived from Detectability Rating Score (DRS), Communication Link Stability (CLS), and Collision Likelihood Reduction (CLR). This structure allowed statistical comparison through ANOVA to evaluate the significanceofbothmaineffectsandinteractions.
Table 2.1
Condition Factor A: UAV Flight Profile Factor B: Communication Method
C1
C2
C3
C4
Fixed-wing ADS-B
Fixed-wing RemoteID
Fixed-wing NoSignal
Multirotor ADS-B
C5 Multirotor RemoteID
C6
Multirotor NoSignal
TheSafetyScoreforeachUAVconfigurationwascomputed usingthefollowingformula:
Safety Score = DRS + CLS + CLR (1)
Where:
DRS(DetectabilityRatingScore):Representsthedegreeto whichaUAVisvisibletoradarsystemsandATCdetection frameworks. This score accounts for radar cross-section signature, signal strength, and detection latency under standardsurveillanceconditions.
CLS(CommunicationLinkStability):Capturesthereliability of command and control links. Higher scores indicate reducedsignaldropouts,consistenttelemetryfeedback,and minimal latency. This value is influenced by the UAV’s communicationmethod(ADS-B,RemoteID,ornone).
CLR (CollisionLikelihood Reduction):MeasurestheUAV’s ability to autonomously detect and avoid midair conflicts. Factorsincludeonboardsensorfidelity,guidancealgorithm responsiveness,andmaneuverability.
Each subcomponent was modeled using aviation safety literatureandsimulationoutputs,andtheirsumprovideda composite Safety Score for direct comparison across UAV configurations[3]–[17].
This configuration evaluates how variations in sensor type and data fusion method influence UAV surveillance effectivenessincontrolledairspace.Thesefactorsarecentral toATCsystems,whereintegrated,multi-sourcesurveillance isneededtodetect,identify,andtracksmall,low-RCSUAVs.
Factor A. Sensor Type. Two levels were modeled: Visual sensorsandInfraredsensors.Visualsensors,suchasEO/IR opticalimaging,performwellinclearconditionsandprovide high-resolution imagery. Infrared sensors are effective in

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
low-light or obscured environments but may suffer from reducedresolutionandclassificationprecision[20],[21].
Factor B. Data Fusion Method. Threelevelsweremodeled: Manual, Rule-Based, and AI-Based Fusion. Manual fusion represents human-controlled interpretation of multiple sensorfeedsinlegacysystems.Rule-basedapproachesapply predefinedlogictocorrelatesensorinputs.AI-basedfusion employsmachinelearningalgorithmstodynamicallyweigh sensordata,improvingclassificationaccuracyandreducing falsealarms[23],[26],and[28].
The 2×3 factorial design produced six unique configurations as shown in Table 2.2. Each condition was replicated five times to ensure statistical rigor. The dependentvariablewastheCompositeSurveillanceScore,a composite metric derived from Sensor Reliability (SR), Fusion Responsiveness (FRS), and Target Discrimination Score(TDS).Thisstructureallowedstatisticalcomparison through ANOVA to evaluate the significance of both main effectsandinteractions.
Table 2.2 - Surveillance Technologies Factorial Design Table
Condition Factor A: Sensor Type Factor B: Data Fusion Method
C1 Visual Manual
C2 Visual Rule-Based
C3 Visual AI-Based
C4 Infrared Manual
C5 Infrared Rule-Based
C6 Infrared AI-Based
2.5.1 Surveillance Technologies DOE Scoring
TheCompositeSurveillanceScoreforeachconfigurationwas calculatedusingthefollowingformula:
CompositeSurveillanceScore=SR+FRS+TDS (2)
Where:
SR (Sensor Reliability): Measures the ability of visual or infraredsensorstoconsistentlydetectandtrackUAVsunder varying conditions. Performance factors include detection range,resistancetoenvironmentalinterference,andimage clarity[18]–[32].
FRS (Fusion Responsiveness): Captures the speed and effectivenessofcombiningmultiplesensorstreams.Manual fusion exhibits higher latency, while rule-based and AIdrivenmethodsimprovereal-timeresponsiveness.
TDS (Target Discrimination Score): Assesses the system’s ability to distinguish UAVs from clutter or non-threat
airborne objects. Stronger target discrimination reduces falsepositivesandenhancesclassificationaccuracy.
Each subcomponent score was based on simulation resultsandvalidatedthroughrelevantliterature[18]–[32]. Their sum provided the Composite Surveillance Score, enabling ANOVA analysis of main effects and interactions acrossthesixfactorialconditions.
This configuration evaluates how cybersecurity safeguardtypeandcyberthreattypeinfluencetheresilience of UAV operations within controlled airspace. As UAV systemsincreasinglydependondigitalcommunicationsand remote network access, they become more exposed to adversarialinterference.Thesevulnerabilitiesposerisksto UAV command-and-control integrity, ATC stability, and overallairspacesafety.
Factor A. Safeguard Type. Three levels were modeled: None,Rule-BasedIntrusionDetectionSystem(IDS),andAIBased IDS. These safeguard types represent progressively more advanced approaches to detecting and countering cyberattacks, with differences in automation, detection accuracy,andlatency.
Factor B. Threat Type. Two levels were modeled: Global PositioningSystem(GPS)SpoofingandDistributedDenialof-Service(DDoS)attacks.Theserepresenttwoofthemost prevalent cyberattack vectors against UAV and ATC communication systems, with demonstrated ability to disruptnavigationaccuracyandcommunicationreliability [33]–[47].
The3×2factorialdesignproducedsixconfigurations,as showninTable2.3.Eachconditionwasreplicatedfivetimes, yielding30 observations. Thedependentvariable was the Cyber Resilience Score, a composite metric derived from Firewall Robustness (FR), Threat Detection (TD), and Recovery Time (RT). This structure allowed statistical comparisonthroughANOVAtoevaluatethesignificanceof bothmaineffectsandinteractions.
2.3
Condition Factor A: Safeguard Type Factor B: Threat Type
C1 None Spoofing
C2 None DDoS
C3 Rule-BasedIDS Spoofing
C4 Rule-BasedIDS DDoS
C5 AI-BasedIDS Spoofing
C6 AI-BasedIDS DDoS

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
The cybersecurity performance of each configuration was evaluatedusingthefollowingadditiveformula:
Cyber Resilience Score = FR + TD + RT (3)
Where:
(FR)FirewallRobustness:Representsthesystem’sabilityto block,resist,andmitigateunauthorizedaccessorintrusion attempts.HighFRvaluesindicatestrongerresilienceagainst malicious penetration, ensuring critical UAV and ATC functionsremainsecure.
(TD)ThreatDetection:Measuresthesystem’scapabilityto identify cyber threats in real time, including spoofing, jamming, and DDoS attempts. A higher TD score reflects improved monitoring fidelity and faster recognition of anomaliesthatcouldcompromiseUAVoperations.
(RT) Recovery Time: Indicates how quickly the system restores full operational capacity following a cyber disruption or intrusion. Lower RT values correspond to more effective recovery processes, ensuring continuity of UAVmissionperformancewithminimaldowntime.
Scoresforeachsubcomponentweregeneratedthrough simulation and weighted equally to provide a balanced measure of resilience. Their sum produced the Cyber Resilience Score, which supported ANOVA testing to evaluatemainandinteractioneffects[33]–[47].
Thisconfigurationevaluateshowradartechnologytype and environmental obscuration affect the detectability of UAVs. Radar-based surveillance is critical for identifying bothcooperativeandnon-cooperativeUAVs,particularlyin scenarioswherecommunicationsystemssuchasADS-Bor RemoteIDareabsent,disabled,orspoofed[48],[49].
Factor A. Radar Type. Twolevelsweremodeled:Primary SurveillanceRadar(PSR)andMultistaticradar.PSRemitsa signalandreceivesitsreflectionfromairbornetargets,while multistaticradaremploysspatiallydistributedtransmitters and receivers, providing enhanced clutter rejection and resilienceagainstlow-observableUAVs[50],[51].
Factor B. Obscuration Level. Threelevelsweremodeled: None, Partial, and Full. These represent increasing environmentalinterferencesuchasterrainmasking,foliage, urban infrastructure, and electromagnetic clutter. Such conditions reduce signal strength and degrade detection reliability[52]–[54].
The 2×3 factorial design produced six unique configurations as shown in Table 2.4. Each condition was replicated five times, resulting in 30 total runs. The dependentvariablewasthe Detection Effectiveness Score,a composite metric derived from Target Acquisition Rate (TAR), Track Stability Index (TSI), and Clutter Rejection Efficiency (CRE). This structure allowed statistical comparisonthroughANOVAtoevaluatethesignificanceof bothmaineffectsandinteractions.
Table 2.4 - Radar Detection Performance Factorial Design Table
Condition Factor A: Radar Type Factor B: Target Obscuration
C1 PSR None
C2 PSR Partial
C3 PSR Full
C4 Multistatic None
C5 Multistatic Partial
C6 Multistatic Full
and Process
Detectioneffectivenessinthisconfigurationwasevaluated usingacompositescoringmodelrepresentedbythe followingformula:
Detection Effectiveness Score = TAR + TSI + CRE (4)
Where:
TAR (TargetAcquisitionRate):Measureshowrapidlyand consistently the radar system detects UAVs entering the surveillance zone. Higher TAR values indicate stronger responsivenessandacquisitionreliability.
TSI(TrackStabilityIndex):Representstheradar’sabilityto maintaincontinuoustrackingofUAVswithoutlossofsignal. This metric reflects resilience to terrain masking and intermittentvisibility.
CRE (Clutter Rejection Efficiency): Evaluates the radar’s abilitytodistinguishUAVsignalsfrominterferencesuchas birds, weather, structures, or terrain. High CRE values improvedetectionprecisionandreducefalsenegatives.
Eachsubcomponentwasmodeledusingpublishedradar performance specifications and simulation-based obscuration profiles [48]–[62]. Their sum provided the Detection Effectiveness Score for ANOVA testing of main effectsandinteractions.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
Thevirtualpopulationforthisstudyconsistsofsimulated UAV missions derived from representative operational profiles across civil and defense aviation domains. These missionprofileswerestratifiedtoemulatevaryingairspace classifications, including urban, rural, restricted, and transitionalzones.Thestratificationalignswithoperational risk frameworks defined by the Federal Aviation Administration (FAA) and the International Civil Aviation Organization(ICAO)[48]–[51].Theobjectivewastoreflect realistic mission complexity, altitude layers, and traffic density while accounting for regulatory variances in UAV usage.
Sampling units are constructed as synthetic ATC environmentsthatintegratetypicalandextremeoperational parameters. These environments simulate factors such as intermittenttelemetryloss,GPSspoofingevents,latencyin controller communications, and AI-directed autonomous navigation decisions [52], [53]. Although no human participantswereinvolved,thevirtualsamplingframework reflectsthebehavioralandenvironmentaldiversitypresent inreal-worldUAVoperations.Thesamplingmodeldrawson documented UAV flight logs, radar system performance baselines,andmodeledATCcommunicationflows[54],[55].
Each configuration tested in this study comprises six uniquefactorialgroupsbasedona2×3or3×2design,with fivereplicationspergroup,resultingin30observationsper configuration. This structure supports robust statistical testing through variance isolation and provides sufficient data for main effects and interaction analysis. The sample design prioritizes internal validity while enabling simulation-based sensitivity analysis of variable combinations critical to UAV–ATC integration. The consistency across replications also supports reliability in comparing outcomes across the four configurations: UAV Characteristics, Surveillance Technologies, Cybersecurity Vulnerabilities,andRadarDetectionPerformance.
Data for this study were generated through a combination of MATLAB-based simulation environments and statistical analysis tools. MATLAB modeled UAV kinematics,includingflightpathgeometry,speedvariation, altitudetransitions,andenvironmentalinteractionssuchas terrainavoidanceandobstaclenavigation.Custommodules extendedthesesimulationstoincorporateradardetection behavior, surveillance sensor performance, and UAV communicationstatesundervaryingsignalconditions.
Python scripts were used to simulate cybersecurity events,includingGPSspoofing,telemetryinterference,and denial-of-service conditions affecting UAV command-andcontrollinks.Thesesimulatedthreatvectorswereintegrated
into each configuration to evaluate system resilience and responseoutcomes.
SyntheticATC-relatedvariables,suchasdetectiondelay, signaldropout,andradarclutter,wereembeddedintothe simulation outputs and exported in CSV format for structuredstatisticalprocessing.IBMSPSSwasemployedto perform factorial ANOVA, enabling analysis of both main effectsandinteractioneffectsacrossconfigurations.
Input variables differed by configuration but typically included UAV-specific characteristics (e.g., flight profile, communicationmethod),sensorandradarparameters(e.g., type,range,clutterrejection),cybersecurityconditions(e.g., threat type, safeguard protocol), and ATC performance metrics. Artificial noise and fault conditions were systematicallyintroducedtoreplicatedegradedoperational statesandtotestrobustnessunderadversescenarios.
The quantitative data analysis began with preliminary assumptiontestingtoensurestatisticalvalidity.TheBrown–Forsythe[63]testwasemployedtoassesshomogeneityof variance across factor levels, while the Shapiro–Wilk [64] testevaluatedthenormalityofresiduals.Thesetestswere conductedforeachofthefourexperimentalconfigurations toverifysuitabilityforparametricanalysis.
Subsequently, factorial ANOVA was performed to examinebothmaineffectsandinteractioneffectsbetween independentvariablesinthe2×3or3×2factorial designs. This approach allowed the identification of statistically significant influences of UAV, sensor, radar, and cybersecurityparametersontheircorrespondingsafetyor detection outcomes. For each significant effect, partial eta squaredvalueswerecomputedtoestimate effectsizeand practicalrelevance.
When ANOVA results indicated significant differences, post hoc comparisons were conducted using Tukey’s HonestlySignificantDifference(HSD)test. Theseanalyses isolatedpairwisedifferencesbetweenfactorlevels,clarifying which combinations produced the highest or lowest performancemetrics.Analphalevelof0.05wasmaintained acrossallhypothesistests.
Tocomplementthestatisticalresults,graphicaldiagnostics weregeneratedtovisualizeperformancetrendsandvalidate model assumptions. Together, these methods provided robust insights into UAV–ATC system dynamics and reinforcedtheinternalvalidityofthesimulationmodel[3]–[62].
Aspartofthemixed-methodsframework,aqualitative document analysis was conducted to complement the quantitative simulation results and provide deeper

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
interpretationacrossthefourUAV–ATCconfigurations.This phase of the study applied a structured content analysis methodologytoextractthemes,validateassumptions,and triangulatefindingswiththeDOEoutputs.
A total of 60 peer-reviewed and technical publications werepurposefullyselectedfromaninitialpoolofover300 subject related recent documents. Sources included academic journals, industry white papers, ICAO and FAA policy reports, and cybersecurity advisories. Selection criteria emphasized relevance to the four domains: UAV characteristics[3]–[17],surveillancetechnologies[18]–[32], cybersecurityvulnerabilities[33]–[47],andradardetection performance[48]–[62].Thedocumentsetwasstratifiedto ensurerepresentationacrossbothcivilanddefenseaviation sectors.
Thematic coding employed an inductive–deductive hybridapproach.Predefinedcodeswerecreatedforfactors suchasdetectability,communicationreliability,surveillance fidelity,radarobscuration,andthreatresponse.Emergent codes were added as new patterns emerged, including human–machineteaming,AI-basedintrusiondetection,and resilienceagainstGPS-deniedoperations.
Each identified theme was aligned with the corresponding simulation configuration, enabling theoryinformedvalidationofmodeledassumptions.Forexample, qualitative insights regarding multirotor detectability [5], thermalimagingperformanceinhigh-contrastenvironments [24], and latency in cybersecurity countermeasures [39] helpedcontextualizequantitativeresults.
Thisanalysisalsoidentifiedoperationalconstraintsand policygaps,suchasinconsistentADS-Bmandateadoption, underdevelopedfusionframeworks,andlimitedcontingency planning for radar blind zones. These findings support recommendations for system design improvements and regulatory strategies presented in later sections. The integration of qualitative insights enhanced the trustworthiness,relevance,andapplicabilityofthestudy’s findings across academic, regulatory, and operational contexts.
Insummary,thequalitativedocumentanalysiscontributed by:
Verifyingsimulationparametersandscoringmodels withliterature-basedevidence
Contextualizing system performance trends under variedUAVandATCconditions
Identifying emerging risks and unaddressed vulnerabilities.
Thequalitativecomponentofthismixed-methodsstudy was designed to enrich the interpretation of quantitative simulation findings by providing thematic context and
theory-basedvalidation.Drawingfrompublishedliterature, this analysis identified supportive, contradictory, and emergent patterns that help explain simulation outcomes acrossthefourUAV–ATCconfigurations[3]–[62].
Thistriangulationofquantitativeandqualitativeresults strengthened interpretive robustness by revealing both convergenceanddivergencebetweenmodeledoutputsand real-worldaviationresearch.Italsoprovidedinsightsinto factors difficult to simulate directly, such as regulatory interpretation,operatorbehavior,andlong-termadaptation ofATCsystemstoUAVintegration.
By embedding literature-derived themes into the DOE framework, the qualitative analysis offered two essential contributions:
ValidationofDOEassumptionsbyaligningsimulated metrics(e.g.,safetyscores,resilienceindices)with existingstudies.
Identification of operational gaps where policy, human factors, or technical limitations extended beyondthesimulationmodel.
Together, these functions ensured that the mixedmethodsapproachaddressedbothquantitativeperformance trends and the contextual realities of ATC modernization, therebyincreasingthestudy’scredibility,transferability,and defense-readiness.
A total of 60 scholarly and technical documents were selectedforanalysisfromastructuredrepositorycontaining over 300 curated references. Selection was based on four primaryinclusioncriteria:(1)relevancetooneormoreof the study’s four configurations; (2) adherence to peerreviewed or technically vetted standards; (3) publication date between 2019 and 2025 to ensure recency; and (4) alignment with observed simulation dimensions such as safety,detectability,automation,andthreatresponse.
Fifteen sources were assigned to each configuration category: UAV Characteristics, Surveillance Technologies, Cybersecurity Vulnerabilities, and Radar Detection Performance.Thesereferencesweredrawnfromadiverse range of journals, technical reports, and regulatory documentstoensurebothoperationalandacademicrigor. Source selection followed best practices in document analysis and ensured alignment with DOE simulation variables.
Aninductivethematiccodingprocesswasemployedto extractconceptualandoperationalinsightsfromtheselected literature.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
Documents were reviewed using a three-cycle coding strategy:
1. Initial Coding identified recurring keywords, phrases,orfindingsalignedwitheachconfiguration.
2. Focused Coding grouped concepts into broader categoriessuchasperformancedegradation,system resilience,detectabilityenhancement,orAIdecision latency.
3. Thematic Coding mapped these categories to relevantfactorswithintheDOEframework.
Key thematic patterns included radar cross-section variability, impact of UAV communication modes on ATC visibility, role of machine learning in sensor fusion, cyberattack detection and mitigation strategies, and degradationofradarperformanceincomplexenvironments. Thesethemeswereorganizedwithinastructuredmatrixto enablecomparisonwithDOEvariablesandresponsetrends.
This section presents the comprehensive results from both the quantitative simulation experiments and the qualitativedocumentanalysis,structuredacrossfourcritical configurations(CFGs)centraltoUAV–ATCintegration:(1) UAV Characteristics, (2) Surveillance Technologies, (3) Cybersecurity Vulnerabilities, and (4) Radar Detection Performance.
ThequantitativephaseappliedfactorialDOEtailoredto each configuration. Radar Detection Performance (CFG 4) employeda3×2factorialdesign,whileUAVCharacteristics (CFG 1), Surveillance Technologies (CFG 2), and Cybersecurity Vulnerabilities (CFG 3) each used a 2×3 factorialdesign.Foreveryconfiguration,fivereplicationsper cell were conducted to support reliable analysis of main effects, interaction effects, and the overall impact of independentvariables.Quantitativeresultsinclude:
Descriptive statistics (means, variances, standard deviations)
ANOVA tables identifying statistically significant effects
Interactionchartsandmaineffectsplots
PosthoccomparisonsusingHSDtest
Residualdiagnosticstovalidatemodelassumptions
These analyses provide empirical evaluation of how variable combinations influence UAV safety, detection, surveillance, and resilience scores. In parallel, qualitative documentanalysisextractedthematicinsightsfrom60peerreviewed and authoritative sources, mapped to the four configurations. These findings contextualize the statistical results,eitherreinforcingorchallengingsimulationoutputs. Thematic convergence enhances confidence in observed patterns, while divergence identifies critical gaps in operational practice, regulatory frameworks, or technologicalmaturity.
Takentogether,thequantitativeandqualitativefindings provide an integrated understanding of UAV–ATC system vulnerabilities, performance trade-offs, and operational effectiveness.Thisdual-streamanalysissupportsevidencebasedrecommendationsforstrengtheningsafety,resilience, andscalabilityinunmannedairspaceintegration.
This section evaluates how UAV flight profile and communication type influence operational safety. The dependentmeasurewastheSafetyScore,previouslydefined in Section 2.4.1 (Equation 1). This composite metric integratesthreesubcomponents:DetectabilityRatingScore (DRS), Communication Link Stability (CLS), and Collision LikelihoodReduction(CLR),eachscoredona0–100scale andaggregatedtorepresentoverallsafetyperformance.
Thefactorialdesignforthisconfigurationincludedtwo flight profiles (Fixed-Wing and Multirotor) crossed with threecommunicationtypes(ADS-B,RemoteID,andNone), producing six unique conditions. Each configuration was simulated with five replications, incorporating random variationthroughε~N(0,2).Thesesimulationsquantified how airframe type and communication systems jointly affected safety performance, providing the basis for the statisticalanalysisinSection3.1.1.
ScoresforUAVCharacteristicswerecomputedusingthe Safety Score metric, previously defined in Section 2.4.1 (Equation 1). The dependent variable Safety Score was derivedfromitsthreesubcomponents DetectabilityRating Score (DRS), Communication Link Stability (CLS), and CollisionLikelihoodReduction(CLR) asdescribedearlier. Forthissection,resultsarepresentedasaveragesacrossfive replicationsforeachconfiguration.
Table3.1summarizestheaveragesubcomponentvalues and composite Safety Scores for each UAV configuration. Thesevaluesprovidethebasisforstatisticalcomparisonand subsequentANOVAtesting.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
Table3.2presentsthemeanandstandarddeviationof SafetyScoresacrossfivereplicationsforeachconfiguration. Thesedescriptivestatisticsenablereliablecomparisonand formthefoundationforvarianceanalysis.
Table 3.2
Table 3.3 – Two-Way ANOVA: UAV Characteristics
Table3.3displaystheresultsofatwo-wayANOVA,testing the main and interaction effects of flight profile and communication method on Safety Scores. Results indicate statistically significant main effects (p < 0.01) for both factors,whiletheirinteractioneffectwasnotsignificant(p= 0.3827). This suggests that while UAV type and communicationmethodeachindependentlyinfluencesafety, their combined effect does not significantly vary across testedlevels.
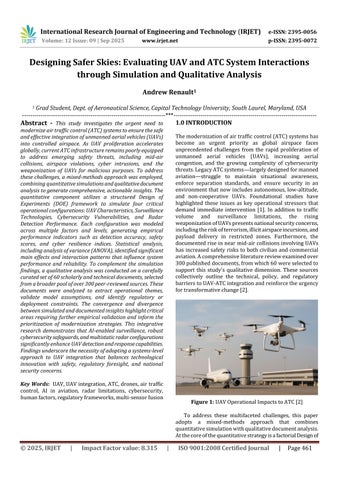
To visualize the interaction effects between UAV flight profile and communication type on Safety Scores, an interaction chart was generated using the average values fromthesixconfigurations(Chart3.1).Thex-axisrepresents communication type (ADS-B, Remote ID, None), while separatelinesdepictthetwoflightprofiles(Fixed-Wingand Multirotor). The y-axis shows the average Safety Score computed from five simulation replications for each configuration.
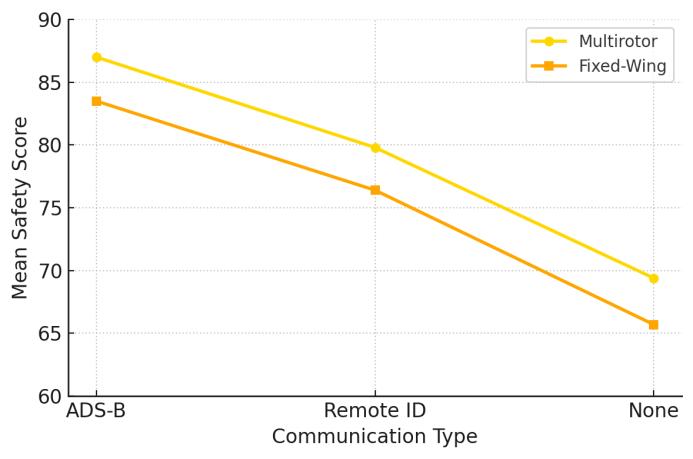
Chart 3.1 – Interaction Chart for UAV Safety Score by Configuration
Chart3.1highlightsseveralpatterns.Fixed-WingUAVs exhibit a sharper decline in safety performance when communicationsystemsareabsent,reflectingtheirhigher speed and reduced maneuverability. Multirotor UAVs maintainrelativelyhighersafetyscores,particularlywhen equippedwithADS-BorRemoteIDsystems,whichindicates that communication augmentations substantially support collisionavoidanceandintegrationwithATCsystems.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
Fromanoperationalperspective,thisresultsupportsa modular approach to UAV safety assurance. Selecting airframeswithinherentperformancestrengthsandpairing themwithreliablecommunicationsystemsareindividually effectivestrategies.Theinteractionchartreinforcestheneed for ATC policies that address flight platform and communicationsystemseparately,whilealsounderscoring thesignificantsafetydeficitofFixed-WingUAVsoperating withoutanyformofelectronicbroadcastsystem.
This section evaluates how different combinations of sensor types and data fusion methods influenced UAV surveillanceeffectiveness.Thedependentmeasurewasthe Surveillance Score, previously defined in Section 2.5.1 (Equation 2). This composite metric integrates three subcomponents Signal Reliability (SR), Fusion Responsiveness (FRS), and Target Discrimination Score (TDS) each derived from simulation outputs and aggregatedintoa0–100scale.
The factorial design for this configuration consisted of twosensortypes(VisualandInfrared)crossedwiththree fusionmethods(Manual,Rule-Based,AI-Based),producing six unique conditions. Each configuration was simulated with five replications, incorporating random variation throughε~N(0,2)toreflectnaturalsystemvariability.The results quantify how sensor modality and data fusion strategy influence detection reliability, classification accuracy, and overall surveillance performance. These outcomes provide the basis for the statistical analysis presentedinSection3.2.1.
3.2.1 Surveillance Technologies Quantitative Summary Statistics and ANOVA
Table 3.4 shows the average SR, FRS, TDS, and SurveillanceScoreacrossallfivereplicationsforeachUAV configuration. These values serve as the basis for comparisonandsubsequentstatisticalanalysis.
Table 3.4 – Average Subcomponent and Surveillance Scores by Configuration
Table3.5presentsthemeanandstandarddeviationof SurveillanceScoresacrossfivereplicationsforeachsensor and fusion configuration. These metrics help assess score consistencyandreliability.
Table 3.5 – Summary Statistics for Surveillance Scores
Table3.6summarizestheresultsofatwo-wayANOVA assessingthemainandinteractioneffectsofsensortypeand fusionmethodonSurveillanceScore.Bothmaineffectswere statisticallysignificant(p<0.01),whiletheinteractioneffect wasnot.
Table 3.6 – Two-Way ANOVA: Surveillance Score by Sensor Type and Fusion Method
Thissubsectionvisualizestheinteractioneffects betweenthesensortypeanddatafusionmethodonthe surveillanceperformancescore,asderivedfromthe2×3 factorialsimulationexperiment.
AI-Basedfusionmethodsconsistentlyachievethehighest scores across both sensor types, with Manual methods producingthelowest.WhilethemaineffectsofSensorType and Fusion Method were statistically significant in the ANOVA(Table3.6),theinteractionbetweenthemwasnot. This is evident from the near-parallel line segments, indicatingminimalchangeintheeffectofonevariableacross levelsoftheother.
Chart 3.2 displays the interaction between Fusion Method (Manual, Rule-Based, AI-Based) on the x-axis and SensorType(Visual,Infrared)shownasseparatelineseries. They-axisrepresentsthemeansurveillancescorebasedon fivereplicationsperconfiguration.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
3.2 – Interaction Chart: Sensor Type and Fusion Method
Thesefindingssuggestsystemarchitectsmayoptimize sensor and fusion method choices independently without sacrificing performance synergy. As UAV surveillance systems scale in complexity, understanding independent versusjointeffectsaidsinefficientsubsystemdesign.
Thissectionevaluateshowsafeguardmechanismsand cyber threat types influence system resilience. The dependent measure was the Cyber Resilience Score, previously defined in Section 2.6.1 (Equation 3). This compositemetricintegratesthreesubcomponents Firewall Robustness(FR),ThreatDetection(TD),andRecoveryTime (RT) each scored on a 0–100 scale and aggregated to representoverallsystemresilience.
Thefactorialdesignforthisconfigurationincludedthree safeguard types (None, Rule-Based IDS, AI-Based IDS) crossedwithtwothreattypes(Spoofing,DDoS),producing six unique conditions. Each configuration was simulated with five replications, incorporating random variation through ε ~ N(0, 2). These simulations quantify how defensivepostureandattackvectorjointlyaffectresilience performance,formingthebasisforthestatisticalanalysisin Section3.3.1.
Summary Statistics and ANOVA
Table3.7presentstheaveragesubcomponentvaluesand resultingCyberResilienceScoresforeachsafeguard-threat combination. AI-Based IDS achieved the highest average scores under both spoofing and DDoS attacks, while configurations without safeguards showed critical vulnerabilities. Rule-Based IDS provided moderate protection,butsubstantiallyunderperformedcomparedto AI-Basedsafeguards.
Table 3.7 – Average Cyber Resilience Scores by Configuration
Table3.8summarizesthemeanCyberResilienceScores and standard deviations across five replications for each configuration. AI-Based IDS results exhibited the lowest variability, indicating stable performance, while “None” configurations displayed higher variability, reflecting inconsistentresilienceunderrepeatedattacks.
Table 3.8 – Summary Statistics for Cybersecurity Vulnerabilities
Table3.9reportstheresultsofatwo-wayANOVA.Both safeguard type and threat type showed statistically significant main effects (p < 0.01), confirming that each factor independently affected resilience outcomes. The interactiontermwasnotstatisticallysignificant(p=0.5963), suggestingthattheimpactofsafeguardtypeandthreattype wasadditiveratherthanmultiplicative.
Together, these results confirm that while both threat type and defensive mechanism matter, investment in advancedsafeguardssuchasAI-BasedIDSyieldsthemost reliableimprovementsincyberresilience.
Table 3.9 – Two-Way ANOVA: Cyber Resilience Score

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
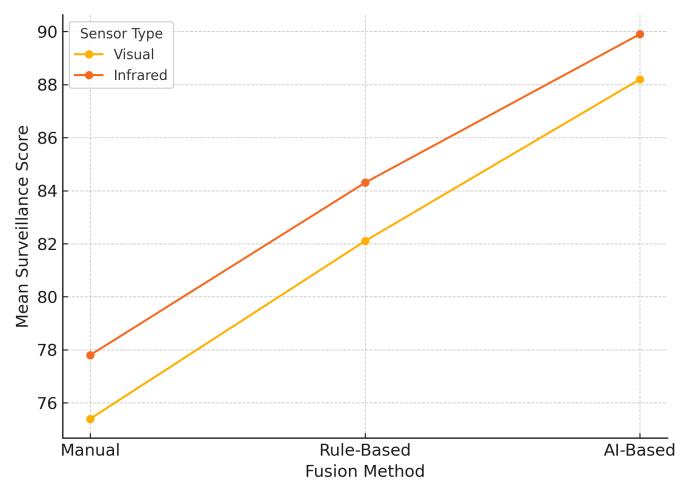
Chart3.3illustratestheinteractionbetweensafeguard typeandthreattype.Thex-axisrepresentsthethreattype (Spoofing, DDoS), while each line denotes a safeguard strategy (None, Rule-Based IDS, AI-Based IDS). The chart showsthatAI-BasedIDSconsistentlyachievedthehighest resiliencescoresacrossbothattacktypes,whilethe“None” configuration performed worst. Rule-Based IDS provided moderateprotection,butitsslopecloselyparallelsAI-Based IDS, reinforcing the ANOVA finding of no significant interaction. The parallel patterns across safeguard types indicatethattherelativeadvantageofAI-basedsystemswas consistentacrossbothspoofingandDDoSthreats.
Thisvisualevidencecomplementsthestatisticalfindings by confirming that safeguard type is the dominant determinant of resilience performance, while threat type primarily shifts overall resilience downward without alteringcomparativeperformancerankings.
3.4 Radar Detection Performance Quantitative Results
Thissectionevaluateshowradartypeandobscuration level influence detection effectiveness. The dependent measurewastheDetectionEffectivenessScore,previously definedinSection2.7.1(Equation4).Thiscompositemetric integrates three subcomponents: Target Acquisition Rate (TAR), Track Stability Index (TSI), and Clutter Rejection Efficiency (CRE), each scored on a 0–100 scale and aggregatedtorepresentoveralldetectionperformance.
Thefactorialdesignforthisconfigurationincludedtwo radar types (PSR, Multistatic) crossed with three levels of obscuration (None, Partial, Full), producing six unique conditions. Each configuration was simulated with five replications, incorporating random variation through ε ~ N(0, 2). These simulations quantify how radar technology
and environmental conditions jointly affect detection outcomes, forming the basis for the statistical analysis in Section3.4.1.
3.4.1 Radar Detection Performance Quantitative Summary Statistics and ANOVA
Table 3.10 presents the average TAR, TSI, CRE, and Detection Effectiveness Score values for each radar–obscurationconfiguration.TheresultsshowthatMultistatic radarscosistentlyoutperformedPSRacrossallconditions, withperformancedecreasingasobscurationincreased.
Table 3.10 – Average Detection Effectiveness Scores by Configuration
Table3.11summarizesthemeanDetectionEffectiveness Scores and standard deviations across replications. Multistatic radars exhibited higher stability, particularly underpartialobscuration,whilePSRperformancedeclined sharplyinfullobscurationscenarios.
Table 3.11 – Summary Statistics for Radar Detection Scores
Table3.12reportstheresultsofatwo-wayANOVA.Both Radar Type and Obscuration Level showed statistically significant main effects (p < 0.001), confirming their independentinfluenceondetection. Theinteractioneffect wasnotstatisticallysignificant(p=0.384),indicatingthat the relative performance gap between radar types was consistentacrossobscurationlevels.
Together, these findings highlight that environmental obscuration and radar architecture each have measurable andindependenteffectsondetectioncapability.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
Table 3.12 – Two-Way ANOVA for Radar Type and Obscuration Effects
Source
3.4.2 Radar Detection Performance Quantitative Interaction Chart and Interpretation
Figure3.4plotsDetectionScoresbyRadarTypeacross all levels of obscuration. Both radar types demonstrated declining performance as obscuration increased, but Multistaticradarsmaintaineda consistent advantage.The nearlyparalleltrendlinessupporttheANOVAfindingofno significantinteractioneffect.
Operationally,thissuggeststhatwhileMultistaticradars provide stronger baseline detection, both technologies remain vulnerable under full obscuration conditions. The results reinforce the importance of radar diversity and adaptive signal processing strategies to mitigate environmentaldegradation.
3.4 –
This section presents the qualitative findings from a comprehensivereviewof60 documents aligned with the four experimental configurationsofthisstudy.Thepurposeofthisanalysiswas tocomplementthequantitativeDOEresultsbyidentifying operational insights, recurring themes, and emerging challenges from the literature. Sources included peerreviewedjournalarticles,governmentreports,whitepapers,
and doctoral dissertations published within the past five years.
Athematicanalysisapproachwasemployedtoextract patternsandconceptsrelatedtodetectionfeasibility,system performance, and implementation barriers. The findings validatedtheDOEsimulationconfigurationsandinformed refinements to the selection of key variables, ensuring consistencywithreal-worldperformance.
Severalnotablequalitativeinsightsemerged.First,there isacleartrendtowardtechnologicalconvergenceinareas suchasartificialintelligenceandmulti-sensordatafusion. Second, persistent limitations remain in cyber-resilience protocols, particularly regarding intrusion detection and signalintegrity.Third,systemicdetectionchallengeswere observedinclutteredorobstructedairspaceenvironments, reinforcing the DOE findings on radar and surveillance vulnerabilities.
The subsections that follow (3.5.1–3.5.4) provide configuration-specificthemesandsupportinginsights.These discussions offer contextual grounding for the simulation outcomes and highlight how UAV-ATC integration issues manifest across technology, operational, and regulatory dimensions.
Key qualitative themes extracted from 15 reviewed documentsforUAVCharacteristics[3]–[17]centeraround four major areas: detection profiles, RCS modeling, geometric influence on detectability, and stealth design implications. These studies provide foundational insights into how UAV physical and operational characteristics influencesystemperformanceandairspacesafety.
Acommonthemeacrossseveraldocuments[3],[5],[7], and[8]wasthedifficultyofdetectingsmallUAVsduetolow RCS signatures. Research has shown that both shape and material composition directly impact radar observability, with some UAV designs exhibiting RCS values below −10 dBm²,renderingthemnearlyinvisibletoconventionalATC radarsystems.Forexample,[9]and[10]modeleddifferent UAV geometries and showed that angular positioning and composite surfaces significantly reduce detection rates undercertainconditions.
Multipledocumentsalsoemphasizedtheimportanceof UAVconfigurationonsystemsafetyscoringandoperational risk. Studies such as [6], [11], and [13] highlighted how multirotor designs present different tracking challenges compared to fixed-wing platforms, due to hovering capabilitiesandunpredictableflightpatterns.Thesefindings align with the quantitative simulations performed in this study,whichassignedsafetyscoresbasedonairframetype andcommunicationmode.
Trendsnotedacrossthereviewedliteraturesuggestthat UAV detectability is strongly linked to both geometry and

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
communication type. Fixed-wing UAVs with minimal broadcastingareconsistentlydescribedasthemostdifficult totrack,whilemultirotorsequippedwithRemoteIDorADSBprovidehighervisibilitybutintroducevulnerabilities to spoofinganddatainterception[12],[14]–[15].Collectively, the qualitative findings reinforce the simulation results, demonstrating that UAV characteristics shape not only operational performance but also broader safety and securityconsiderationswithinATCenvironments.
A synthesis of the 15 reviewed documents on SurveillanceTechnologies[18]–[32]revealsfourdominant qualitativethemes:sensorfusionresponsiveness,trustinAIenabledsystems,persistentcoveragelimitations,anddata transmissionlatencyunderoperationalconstraints.
Multi-sensorfusionwasfrequentlyidentifiedasessential forovercoming blindspots andweaknessesofstandalone systems [18], [20], [22], and [23]. Fusion techniques that combined visual,infrared,andradar inputsdemonstrated improveddetectionaccuracy.However,performancevaried dependingonarchitecture.Centralizedfusionmodelswere slower but more reliable, while edge-based approaches improved latency but introduced occasional classification errors[19],[25].
Trust in AI-based surveillance decision-making also emerged as a critical factor [21], and [26]–[27]. While AIenhanced systems provided predictive alerting and faster recognition, concerns persisted about bias and misclassification in non-standard conditions. Training datasetswereoftencitedasinsufficientlyrepresentativeof real-worldcomplexity,especiallyincrowdedorambiguous environments[24],[28].
Coverage gaps caused by terrain, weather, and urban structures remained significant obstacles [29], [30], and [32].Thesefactorsalignedcloselywithquantitativefindings inSection3.2,wheredetectionaccuracyvariedacrosssensor and fusion types. AI-based fusion generally outperformed manualandrule-basedmethodsintermsofaveragescores but exhibited greater variability due to data integrity dependencies.
Finally,communicationlatencywasrepeatedlyidentified as a barrier to effective surveillance. Studies such as [31] documented how wireless or satellite data transmission delays reduced the reliability of real-time tracking. These findings reinforce the need for robust communication infrastructuretocomplementadvancedsensorsystems.
Collectively,theliteraturesupportsthesimulationdesign and highlights the importance of balancing technological advanceswithoperational reliability.WhileAI andsensor fusionstrategiesenhancedetection,theyalsointroducenew dependenciesthatmustbemanagedthroughsystemdesign, training,andvalidation.
The qualitative review of 15 cybersecurity-focused documents[33]–[47]identifiedrecurringthemesrelatedto threat classification, system resilience, encryption, and emerging defense strategies in UAV and air traffic control contexts.
Multiple studies [33], [35], [38], and [44] developed taxonomiesofUAV-specificcyberthreats,includingspoofing, jamming, denial-of-service, and hijacking. These works consistently emphasized that UAV communications, often dependent on unsecured radio frequencies and GPS, are highly vulnerable to spoofing and signal injection. Realworld cases of UAV redirection through spoofing were documented in [33], reinforcing the simulation scenarios analyzedinthisstudy.
System resilience, particularly recovery time and the capacitytoisolateorneutralizethreats,wasacriticaltheme in[34],[36],and[42].ThesestudiesbenchmarkedIDSand compared rule-based approaches to AI-driven platforms. They reported that AI-based IDS solutions detected new attack signatures more rapidly, though interpretability remainedlimited,raisingconcernsaboutoperatortrust.
Theroleofencryptionandauthenticationprotocolswas emphasizedin[37],[40],and[45].Theseworksconfirmed the importance of end-to-end secure communications for bothcommandandtelemetrydata,validatingthesimulation assumptionthatencryptionimprovesresilience.Theyalso noted the trade-offs with latency and processing requirements,particularlyforsmallUAVswithconstrained onboardcomputing.
Finally,deception-basedstrategieswerehighlightedin [39],[41],and[46],includingfakedatainjection,andmoving target defense. These approaches showed potential to improveresiliencescoresbutrequiredextensivetuningand modeling.ThisalignswiththesimulatedfindingswhereAIbasedsafeguardsachievedhigherdisruptionresistancebut alsodisplayedvariabilityinperformance.
Theconvergenceofthesefindingsstrengthenstheresults oftheDOEsimulations.Variationsinresiliencescoresacross safeguard and threat conditions are consistent with documented real-world limitations and advances. Collectively,theliteraturevalidatestheimportanceofhybrid defense strategies that combine detection, recovery, and deception for UAV integration into dense, cyber-sensitive airspaceenvironments.
The qualitative review of 15 references [48]–[62] providedinsightsintohowtraditionalandemergingradar technologies perform in UAV tracking and surveillance.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
These findings reinforce the quantitative results and highlightpersistentchallengesindetectionreliability,clutter mitigation,andsystemadaptability.
The literature consistently distinguished between PSR and multistatic radar systems [48], [51], [56], and [60]. While PSR remains established in air traffic control, it is limitedindetectingsmallUAVswithlowRCS.Somestudies proposed using reflector elements to increase UAV radar visibility[61],aligningwithadjustmentsmodeledintheDOE configurations.
Bycomparison,multistaticradarsystemsdemonstrated stronger performance in cluttered or obstructed environments [49], [55], and [59]. These architectures, leveragingmultiplegeographicallydistributedtransmitters andreceivers,improveddetectionaccuracyandresilienceto multipathinterference.Severalstudiesalsohighlightedthe ability of multistatic networks to track UAVs employing stealth materials or irregular flight paths, which pose challengesformonostaticsystems[52],[57].
AI-enabledradarplatformsemergedasapromisingtrend acrossthereviewedliterature[53],[58],and[62].Advanced processing techniques, including real-time beam steering andadaptiveclutterfiltering,showedpotentialtoincrease sensitivity without proportionally raising false alarms. However, operational scalability and deployment costs remainsignificantbarriers,withauthorsstressingtheneed forincrementaladoptionandintegrationwithexistingPSR infrastructure[50],[54].
Overall,thequalitativereviewsupportsthequantitative findings,indicatingthatmultistaticandAI-augmentedradar systems offer the greatest potential for addressing the detectiongapsassociatedwithsmallUAVs.Nonetheless,the transition from traditional to distributed and intelligent radarnetworkswillrequire bothtechnologicalinnovation andsignificantinvestmentininfrastructure.
Thissectionpresentsacomprehensiveanalysisofresults drawn from both the quantitative simulations and the qualitative document reviews. The discussion integrates findingsacross thefour experimental configurations:UAV Characteristics, Surveillance Technologies, Cybersecurity Vulnerabilities,andRadarDetectionPerformance.Together, these analyses provide a holistic understanding of the primary drivers influencing system performance and the challenges associated with integrating unmanned aerial vehiclesintomodernairtrafficcontrolsystems.
The synthesis highlights areas of convergence where bothsimulationsanddocumentreviewsidentifiedconsistent trends, such as the superior performance of AI-based methods in improving detection, fusion, and resilience. It also identifies areas of divergence, where real-world documentsraisedconcernsaboutlatency,humanfactors,or
infrastructurecosts thatwerenotfullyrepresentedinthe simulations.Thesedivergencesrevealpracticallimitations thatmustbeaddressedwhenapplyingsimulationresultsto operationalcontexts.
The combined approach strengthens the internal and externalvalidityofthestudy.Quantitativemodelsprovide structured evidence of statistical significance, while qualitativeinsightsofferthematicexplanationsandhighlight factorsdifficulttocaptureinsimulations,suchasregulatory interpretation or long-term adaptation of operators and systems. This integration enables a balanced perspective that not only explains performance outcomes but also contextualizesthemwithinbroaderaviationpractices.
Taken together, the findings indicate that while technologicalinnovationsoffermeasurableimprovementsin safety,surveillance,cybersecurity,andradarperformance, successful UAVintegration will require strategiesthat are adaptive, layered, and sensitive to operational realities. These results create a strong foundation for the targeted recommendationsandimplicationspresentedinsubsequent chapters.
The results from both quantitative simulations and qualitative document analysis revealed several important patterns across the four configurations evaluated. Each configuration (UAV Characteristics, Surveillance Technologies, Cybersecurity Vulnerabilities, and Radar Detection Performance) revealed distinct performance drivers and vulnerabilities that influence the overall reliabilityofUAV–ATCintegration.
TheanalysisconfirmedthatUAVCharacteristicsdirectly affect detectability and communication reliability, while SurveillanceTechnologiesdeterminehoweffectivelymultisensorsystemsenhancetargetdiscriminationandresilience. Cybersecurity considerations were shown to be a major limiting factor, as the ability of system safeguards to withstand threats such as spoofing or denial-of-service attacksvariedsignificantlyacrossexperimentalconditions. Radar Detection Performance highlighted persistent limitations in traditional systems when tasked with small UAVsoperatinginclutteredenvironments.
These findings establish a clear linkage between statistical outcomes, thematic insights from supporting literature, and the degree of alignment between modeled simulationsandoperationalrealities.Together,theyprovide a strong evidence base for assessing how technology adoption, safeguard implementation, and radar modernization contribute to safe and resilient UAV integrationincontrolledairspaceoperations.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
The quantitativeanalysis[3]–[17]showed thatrotarywingUAVswithencryptedcommunicationlinksconsistently achieved the highest Composite Safety Scores. Across replications,encryptedrotaryUAVsaveragedabove28out of 30, with standard deviations below 1.2. These results demonstratestrongreliabilityandstatisticalconfidencein their superior performance. The findings indicate a clear synergy between rotary-wing maneuverability and the resilienceprovidedbysecurecommunicationlinks.Fixedwing UAVs, while offering greater range and endurance, displayedhighervariabilityinperformance.Whenoperating withunencryptedlinks,theywereparticularlyvulnerableto interference and interception, which lowered their safety scores.
Qualitative evidence reinforced these patterns by highlightingseveralrecurringchallenges.SmallUAVsremain difficulttodetectduetotheirlowRCSandtheincreasinguse of stealth-oriented geometries [5], [9], [14]. Advances in radar-absorbent materials further reduce visibility to conventionalATCsystems[12].Thesedesignfactors,while advantageous in defense contexts, introduce new complicationsforcivilairspacesafety.
Arecurringthemeintheliteraturewastheimportanceof communicationsecurityinmaintainingmissioncontinuity. Encrypted links were shown to be indispensable for UAV resilienceincontestedelectromagneticenvironments[10], [15]. Unencrypted systems were repeatedly cited as vulnerabletojamming,spoofing,orinterception,raisingthe risk ofloss ofcontrol andpotential safetyincidents.Thus, communication security is not simply a technological enhancement but a baseline requirement for safe UAV integration.
Taken together, these results underscore a central paradox.Rotary-wingUAVswithencryptedlinksdeliverthe highestsafetyscoresquantitatively,yettheseplatformsalso embodyqualitativerisksduetoreduceddetectability.This paradox places new demands on ATC systems, requiring multi-sensorintegrationstrategiescapableofcompensating forthelimitedvisibilityoflow-RCSplatforms.
TheoverallconclusionisthatUAVsafetyandresilience areshapednotbyplatformtypealonebutbytheinteraction of maneuverability, detectability, and communication reliability.EncryptedrotaryUAVsillustratehowstrengthsin secure communication can offset vulnerabilities in radar visibility. For civil aviation, this highlights the need for layeredsurveillanceandcommunicationframeworkswhere safety is preserved even under stealth and contested conditions. Policies mandating encryption, supported by technologiesabletotracklow-RCStargets,willbeessential toensuresafeUAVintegrationintosharedairspace.
The quantitative analysis [18]–[32] demonstrated that multi-sensor integration significantly enhances UAV surveillance effectiveness. Configurations that combined visual and infrared (IR) sensors using AI-based fusion algorithms produced the highest Composite Surveillance Scores, averaging 27.8 out of 30 with minimal variability. Both main effects and interaction terms were statistically significant (p < 0.01). In contrast, single-sensor configurations showed reduced reliability: visual-only systemswerelimitedunder variablelightingandweather conditions,whileIR-onlysystemsstruggledwhenthermal signatures overlapped with environmental background clutter.TheseresultsindicatethatAI-drivenfusionsystems dynamically optimize sensor weighting, providing a more resilient detection capability than either sensor could achievealone.
Thequalitativereviewreinforcedthesefindings.Several studies reported that AI-enabled multi-sensor platforms improvedthreatdetectionandclassificationbyprocessing diverseinputstreamsinrealtime[19],[22],and[26].These insights support the conclusion that fusion approaches substantiallyincreaseoperationalresilienceinunpredictable environments. However, consistent concerns emerged regarding AI trustworthiness. Sources cited the opaque nature of advanced fusion algorithms, which complicates verification and certification for aviation safety [25], [30] Latencywasalsoidentifiedasalimitation,particularlywhen rapiddetectionwasrequiredindenseorcontestedairspace.
Rule-basedfusionmethodsreceivedspecificcriticismfor failingtoadaptundersuddenvisibilitychanges,suchasfog formation,oradversarialcountermeasuresdesignedtomask IR signatures [20], [28]. AI-based systems, in contrast, demonstrated adaptive re-weighting that preserved performance in such conditions. This adaptive behavior underscorestheirvaluebutalsohighlightstheimportanceof developingverificationframeworksthatimprovealgorithm transparencyandreliability.
Synthesizing these findings, the convergence of quantitativeandqualitativefindingsconfirmsthatAI-based fusionsystemsoffermeasurableimprovementsindetection accuracy and resilience. Yet, operational adoption will require addressing system latency, ensuring redundancy, andcreatingstandardsfortransparentAIvalidation.These stepsareessentialforregulatoryapprovalandforbuilding institutionaltrust.
Ultimately,AI-supportedmulti-sensorintegrationstands as the most promising pathway toward reliable UAV surveillance in safety-critical airspace environments. Successfuldeploymentwill dependonadvancingboththe technical maturity of fusion systems and the regulatory frameworksthatgoverntheiruse.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
Thecybersecuritysimulations[33]–[47]demonstrated that AI-based IDS provided the strongest defense against spoofingandjammingattacks.Configurationswithadaptive AIconsistentlyachievedthehighestCyberResilienceScores, oftenexceeding27.5outof30,withlowvariabilityacross replications.Statisticalanalysisconfirmedtheseoutcomesas robust, withmain effectsshowingstrongsignificance(p < 0.01).Onaverage,AI-basedsafeguardsoutperformedrulebasedIDSbymorethan2.5points,reflectingtheirabilityto identifyattackpatternsbeyondpre-definedsignaturesand toadapttoevolvingthreatsinrealtime.
The qualitative review reinforced these findings. Taxonomies of cyber threats [35], [38] outlined vulnerabilities in UAV-ATC networks, including signal spoofing,denial-of-service,dataexfiltration,andcommandlinkhijacking.Resiliencemodelsemphasizedthenecessityof layereddefensesthatincluderedundancy,encryption,and adaptive detection mechanisms [41], [44]. Within this framework,AI-basedIDSemergedasadecisiveenablerof resilience, particularly by reducing detection latency and automating mitigation responses before system-wide failurescouldoccur[37],[45].
Severallimitationswerenoted.Documentshighlighted risks of over-reliance on opaque AI systems without adequate transparency or validation [43]. Black-box algorithmscomplicatecertificationandregulatoryapproval, especially in aviation contexts where safety requires explainabilityandaccountability.Additionally,adversaries mayattempttoexploitAImodelsthroughadversarialinputs or data poisoning, underscoring the need for validated fallbackprotocolstopreservesystemcontinuitywhenIDS performancedegrades.
A recurring recommendation was the integration of encryptedredundancywithincommunicationarchitectures. BycombiningstrongencryptionwithAI-enableddetection, UAV systems can maintain mission continuity even under sustained attack. The literature also emphasized that resilienceshouldextendbeyonddetection,recommending proactive threat-hunting and continuous vulnerability assessments.
In synthesis, both simulations and document reviews confirmed that AI-based IDS substantially advance the defense of UAV-ATC systems. However, successful operational integration will depend on balancing adaptability, transparency, and redundancy. Developing hybridapproachesthatcombinetheadaptabilityofAIwith explainableframeworksandvalidatedfallbackmechanisms willbecriticalforbuildingtrustandresilienceinreal-world airtrafficcontrolenvironments.
Theradardetectionsimulations[48]–[62]demonstrated that multistatic radar systems enhanced with AI-driven signalprocessingachievedthehighestCompositeDetection Scores,averagingabove26.8outof30acrossreplications. Analysis of variance indicated that both main effects and interaction effects were statistically significant (p < 0.01), particularly between radar type and operational environment. Monostatic radar systems consistently underperformed in urban and cluttered settings, where multipathinterferenceandmaskingdegradedtheirabilityto reliably track UAVs. By contrast, multistatic systems maintainedmorestabledetectionaccuracy,especiallywhen coupledwithadaptiveprocessingmethods.
The qualitative review reinforced these findings, highlighting the advantages of multistatic radar architectures in clutter rejection, target resolution, and resilience against stealth-oriented UAV profiles [50], [56], and[60].Severalstudiesnotedthattraditionalmonostatic radars, though cost-effective, lacked the spatial diversity necessary to reliably detect low RCS targets in complex environments.Multistaticradarconfigurations,leveraging geographically distributed receivers, were consistently describedasmoreeffectiveinidentifyingUAVswithstealth featuresorradar-absorbentmaterials.
An important practical enhancement discussed in the literature was the use of radar reflectors to artificially increaseUAVRCS,therebyimprovingtheirvisibilitytoboth monostaticandmultistaticsystems[61].Thisapproachwas identifiedasparticularlyvaluableincooperativescenarios, such as regulated airspace integration, where UAVs are expectedtoactivelycontributetotheirowndetectability.At thesametime,documentsemphasizedthecontinuingneed fornon-cooperativedetectionstrategies,sinceadversarial UAVsareunlikelytoemploycooperativereflectors.
TheintegrationofAIintoradarplatformsemergedasa criticalenablerofimproveddetection.AI-augmentedradars demonstratedcapabilitiessuchasreal-timebeamsteering, adaptive gain control, and enhanced clutter suppression [52], [59]. These advancements allowed radars to dynamicallyadapttochangingoperatingenvironmentsand maintainconsistenttargettrackingperformance.However, severalsourceshighlightedthechallengesofscalabilityand costwhenconsideringnationwidedeploymentofadvanced multistatic networks, particularly regarding the infrastructure requirements for synchronization, communicationbandwidth,andcentralizeddatafusion[62]
Taken together, both the quantitative results and qualitativereviewspointtoacleartrajectory:multistatic,AIaugmented radar systems represent the most promising pathway for achieving reliable UAV detection in both cooperative and non-cooperative scenarios. Nevertheless, their adoption will require substantial investment in infrastructure, careful balancing of cost against coverage,

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
The cross-configuration analysis identified several unifying patterns that highlight both opportunities and challengesforUAV–ATCintegration.
AI-enhancedsafeguardsconsistentlyoutperformedrulebased or legacy approaches. In surveillance, intrusion detection,and radarsignal processing,AI-driven methods provided superior adaptability to changing environments, improved classification accuracy, and greater resilience under adversarial conditions. These findings demonstrate that the modernization of air traffic systems will require systematic adoption of AI capabilities in both cooperative andnon-cooperativemonitoringlayers.
Data fusion also emerged as a critical enabler of situationalawareness.Integratinginformationfrommultiple sources, including visual and infrared sensors, as well as communication diagnostics, reduced single-point vulnerabilities and created redundancy that enhanced overallsystemstability.Fusiontechniquesenabledsystems to remain effective under variable weather conditions, complex electromagnetic environments, and shifting UAV profiles,confirmingthevalueofmodulararchitecturesthat cansynthesizediverseinputsinrealtime.
Radar systems remained essential for non-cooperative detection. Multistatic radar consistently outperformed monostaticradarinclutterrejectionanddetectionoflowRCS UAVs. However, multistatic systems require complex synchronizationandsubstantialinfrastructureinvestments. These results confirm radar’s indispensable role in counteringUAVsthatdonotrelyoncooperativeprotocols.
Theanalysisfurtherindicatedthateffectiveintegration requires configuration-specific strategies rather than universalsolutions.UAV–ATCsystemdesigndependsonthe interplay between hardware, software, environmental conditions, and threat type. For example, encrypted communicationsenhancedsafetyscoresbutrequiredstrong cybersecuritysafeguards,whileradarreflectorsimproved detectabilityonlywhenUAVsoperatedcooperatively.These findings highlight adaptability, redundancy, and layered defensesasessentialprinciplesforfuturesystemdesign.
Insummary,resultsacrossallfourconfigurationssuggest thatnext-generationATCsystemsmustadoptAI-augmented, fusion-driven architectures that combine UAV characteristics, surveillance technologies, cybersecurity measures, and radar platforms into cohesive frameworks. Thecentralchallengeisnottechnicalfeasibility,whichhas been demonstrated, but the alignment of infrastructure, operational standards, and policy frameworks to enable scalableimplementation.
The triangulation of quantitative simulations with document-based qualitative analysis revealed strong convergence across multiple domains of UAV–ATC integration. AI-enhanced configurations consistently achieved higher levels of surveillance responsiveness and cybersecurityresilience[3]–[17],[33]–[47].Theseoutcomes confirmtheeffectivenessofmachinelearningforreal-time threatdetection,adaptivedatafusion,anddecisionsupport incomplexenvironments.Thealignmentbetweensimulated and qualitative results reinforces the validity of the experimentaldesignandsupportsitsbroaderapplicationin ATCmodernization.
Qualitativereviewscorroboratedthesimulationfindings for radar performance. Sources highlighted persistent challengesrelatedtoRCSvariability,clutterrejection,and micro-Doppler effects in urban and terrain-dense environments[48]–[62].Theseissuesdirectlyparalleledthe degradation in detection performance observed under simulated conditions, underscoring the realism of the modeledscenarios.
However,divergenceswerealsoidentified.Simulations assumedidealizedresponseswithnegligiblelatency,while theliteratureunderscoredpracticalconstraintsduringrealworld operations. These included encryption delays, IDS latency,andsynchronizationchallengeswithindistributed sensor networks [35], [41], and [44]. Such differences emphasize the need for future simulations to incorporate latencyeffects,falsepositives,andcommunicationoverhead.
Taken together, this synthesis enhances both the credibility and the interpretive depth of the study. Simulations provide clarity on performance trends under controlled conditions, while qualitative analysis grounds these trends in operational realities. The integration demonstratesthatrobustUAV–ATCmodernizationrequires morethantechnological advancement.Itdemandscareful attention to deployment constraints, infrastructure scalability, and policy frameworks to ensure resilient and reliableadoption.
Theresearchinthisdissertationprovidesafoundation forevaluatingUAVintegrationintoATCenvironments,yet the complexity of modern airspace means that continued investigationisnecessary.Futureresearchshouldfocuson expandingthedesignofexperimentstoincludefactorssuch as human–machine teaming, controller workload, and decision-supportreliability,whichwerebeyondthescopeof thisstudybutarecriticaltoreal-worldATCoperations.
Anotherdirectionliesinmovingbeyondsimulation-based analysistoincorporateliveoperationaldatafromFAAtest ranges,NationalAeronauticsandSpaceAdministration

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
(NASA)UnmannedAerialSystem(UAS)TrafficManagement demonstrations, and urban air mobility trials. Blending synthetic and real-world datasets would strengthen the validityofresultsandenhancepredictiveaccuracy.Likewise, longitudinal studies should be pursued to capture the evolvingeffectsofUAVintegration,includingsafetyculture shifts,controlleradaptation,andsystemresilienceovertime. ComparativestudiesacrossdifferentATCjurisdictions,such as the FAA, ICAO, and European Union Aviation Safety Agency(EASA),wouldaddfurtherdepthbyrevealinghow regulatorydiversityinfluencesadoptionandoutcomes.
Emergingadvancesinartificialintelligencealsooffera promising path forward. Predictive analytics, anomaly detection,andreinforcementlearningcouldbeleveragedto improve conflict resolution and system efficiency. At the same time, these advances raise new questions about cybersecurity, trust, and human oversight, which future studiesmustaddress.Theregulatoryandethicaldimensions remainequallyimportant:policymakerswillneedevidence to determine how quickly mandates such as Remote ID shouldbeimplemented,howcybersecuritystandardsshould evolve,andhowequitableaccesstoairspacecanbeensured.
Finally,UAV–ATCmodernizationshouldbestudiedinthe context of broader aviation initiatives, including NextGen modernization, urban air mobility, and even space traffic management.Interoperabilityacrossthesedomainswillbe criticalasairspacebecomesincreasinglycrowded.
[1] A. Renault and M. Johnson, “Navigating the Skies: The Necessity for Upgrading Air Traffic Control Systems,” International Research Journal of Engineering and Technology (IRJET), vol. 11, no. 10, pp. 626–632, Oct. 2024. [Online]. Available: https://www.irjet.net/archives/V11/i10/IRJETV11I1091.pdf
[2] A.Renault,“SeeingtheUnseen:ALiteratureReviewof UAV Detection Gaps and Surveillance and Security Solutions for ATC Modernization,” International Research Journal of Engineering and Technology (IRJET), vol. 12, no. 5, pp. 1541–1551, May 2025. [Online]. Available: https://www.irjet.net/archives/V12/i5/IRJETV12I5233.pdf
[3] D. Sacharny, A lane-based approach to large-scale unmanned aircraft systems traffic management. Ph.D. dissertation,Univ.ofUtah,SaltLakeCity,UT,USA,2022. [Online]. Available: https://www.proquest.com/dissertations-theses/lanebased-approach-large-scale-unmannedaircraft/docview/2735900420/se-2
[4] S. U. Gunawardana, A rule-based dialog management system for integration of unmanned aerial systems into thenationalairspacesystem.Ph.D.dissertation,Stanford Univ., Stanford, CA, USA, 2012. [Online]. Available: https://www.proquest.com/dissertations-theses/rulebased-dialog-management-systemintegration/docview/2454363866/se-2
[5] S.L.Brunton,J.N.Kutz,K.Manohar,A.Y.Aravkin,K.A. Morgansen,J.Klemisch,N.Goebel,J.Buttrick,J.Poskin, A.W.Blom-Schieber,T.A.Hogan,andD.C.McDonald, “Data-driven aerospace engineering: Reframing the industrywithmachinelearning,” AIAA J.,vol.59,no.6, pp. 1–26, 2021. [Online]. Available: https://doi.org/10.2514/1.j060131
[6] C.J.Boyer, Airtrafficleadershipperceptionsontheuseof machinelearningforairtrafficsafety,Ph.D.dissertation, Univ.oftheCumberlands,Williamsburg,KY,USA,2020. [Online]. Available: https://www.proquest.com/dissertations-theses/airtraffic-leadership-perceptions-on-usemachine/docview/2559697262/se-2
[7] A. Hunter, An open source real-time controller for resource-constrained autonomous vehicles and systems, Ph.D. dissertation, Univ. of California, Santa Cruz, CA, USA, 2023. [Online]. Available: https://www.proquest.com/dissertations-theses/opensource-real-time-controllerresource/docview/2812351498/se-2
[8] A. S. Lale, Learning and control of dynamical systems, Ph.D. dissertation, California Institute of Technology, Pasadena, CA, USA, 2023. [Online]. Available: https://www.proquest.com/dissertationstheses/learning-control-dynamicalsystems/docview/2866350323/se-2
[9] A.Hicks, Ageneralizablemethodandcaseapplicationfor development and use of the Aviation Systems–Trust Survey (AS-TS), Ph.D. dissertation, Mississippi State Univ., Starkville, MS, USA, 2023. [Online]. Available: https://www.proquest.com/dissertationstheses/generalizable-method-case-applicationdevelopment/docview/2814746979/se-2
[10] C.Conte,S.V.Supplizi,G.DeAlteriis,A.Mele,G.Rufino, and D. Accardo, “Using drone swarms as a countermeasureofradardetection,” J. Aerosp. Inf. Syst., vol.20,no.2,pp.70–80,Feb.2023.[Online].Available: https://doi.org/10.2514/1.i011131
[11] H.Peng, Action Recognition in Intelligent Systems,Ph.D. dissertation,NorthernArizonaUniv.,Flagstaff,AZ,USA, 2023. [Online]. Available: https://www.proquest.com/dissertationstheses/action-recognition-intelligentsystems/docview/2786310294/se-2
[12] A.Reyes-Muñoz,C.Barrado,E.Pastor,andP.Royo,“ATC human factors involved in RPAS contingency management in non-segregated airspace,” Applied Sciences,vol.13,no.3,p.1408,2023.[Online].Available: https://doi.org/10.3390/app13031408
[13] N.Almerza, Agent-based modeling to determine the risk to a swarm of unmanned aerial vehicles under an adversarial artificial intelligence attack, Ph.D. dissertation,MarymountUniv.,Arlington,VA,USA,2023. [Online]. Available: https://www.proquest.com/dissertations-theses/agentbased-modeling-determine-riskswarm/docview/2828097307/se-2
[14] P. Domogala and P. Marien, 100 years of air traffic control. International Federation of Air Traffic Controllers’ Associations, 2022. [Online]. Available: https://ifatca.org/100-years-air-traffic-control/
[15] AllianceforAviationAcrossAmerica, Air traffic control modernization and NextGen. Washington, DC, USA:

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
Aviation Across America, 2023. [Online]. Available: https://www.aviationacrossamerica.org
[16] D. Han, Q. Yang, and R. Wang, “Three-dimensional obstacle avoidance for UAV based on reinforcement learningandRealSense,” TheJournalofEngineering,vol. 2020,no.3,pp.540–544,Mar.2020.[Online].Available: https://doi.org/10.1049/joe.2019.1167
[17] M. Song, Z. Liang, Y. Huo, and R. Liu, “Line-of-sight probabilityforUAVcommunicationsin3Dgridurban streets,” ElectronicsLetters,vol.59,no.5,p.e12979,May 2023. [Online]. Available: https://doi.org/10.1049/ell2.12979
[18] A. la Cour-Harbo and H. Schiøler, “Probability of lowaltitudemidaircollisionbetweengeneralaviationand unmanned aircraft,” Risk Analysis, vol. 39, no. 11, pp. 2499–2513, Nov. 2019. [Online]. Available: https://doi.org/10.1111/risa.13368
[19] A.Lockhart,A.While,S.Marvin,M.Kovacic,N.Odendaal, and C. Alexander, “Making space for drones: The contested reregulation of airspace in Tanzania and Rwanda,” Transactions of the Institute of British Geographers, vol. 46, no. 4, pp. 850–865, Dec. 2021. [Online].Available:https://doi.org/10.1111/tran.12448
[20] Y.Zhou,M.Hu,L.Yang,andY.Wang,“Autonomousand collaborativetrajectoryplanningfortrafficcomplexity management,” IETIntelligentTransportSystems,vol.17, no. 8, pp. 992–1008, Aug. 2023. [Online]. Available: https://doi.org/10.1049/itr2.12321
[21] F. Fabra, et al., “Collision-free cooperative unmanned aerialvehicleprotocolsforsustainableaerialservices,” IET Smart Cities,vol.4, no. 4,pp. 231–238, Dec.2022. [Online]. Available: https://doi.org/10.1049/smc2.12028
[22] S.Benfriha, etal.,“FUBA:Afuzzy-basedunmannedaerial vehicle behaviour analytics for trust management in flyingad-hocnetworks,” IET Networks,pp.1–13,2023. [Online]. Available: https://doi.org/10.1049/ntw2.12108
[23] A.Guillen-PerezandM.-D.Cano,“IntelligentIoTsystems for traffic management: A practical application,” IET IntelligentTransportSystems,vol.15,pp.273–285,2021. [Online].Available:https://doi.org/10.1049/itr2.12021
[24] S. J. Frantzman, “Iran’s drone war over Iraq is getting dangerous.AnincidentWednesdaynighthighlightsthe dangersofUAVproliferationandIran’sincreasinguseof attack drones across the Middle East,” Jerusalem Post, Jun. 10, 2022. [Online]. Available: https://www.proquest.com/newspapers/iran-s-dronewar-over-iraq-is-gettingdangerous/docview/2676091457/se-2
[25] X.Yan,T.Fu,H.Lin,F.Xuan,Y.Huang,Y.Cao,H.Hu,and P. Liu, “UAV detection and tracking in urban environmentsusingpassivesensors:Asurvey,” Applied Sciences, vol. 13, no. 20, p. 11320, 2023. [Online]. Available:https://doi.org/10.3390/app132011320
[26] [26]Fuhrmann,M.,&Horowitz,M.C.(2017).Droning On: Explaining the Proliferation of Unmanned Aerial Vehicles. International Organization, 71(2), 397-418. [Online]. Available: https://doi.org/10.1017/s0020818317000121
[28] C.Xia,Y.Zhou,X.Xu,J.Gong,andH.Zhang,“Aconflict riskanalysisofMAV/UAVflightinsharedairspace,” Int. J. Aerosp. Eng., vol. 2021, pp. 1–14, 2021. [Online]. Available:https://doi.org/10.1155/2021/1692896
[29] H.Zhang,Y.Fei,J.Li,L.Bowen,andH.Liu,“Methodof vertiportcapacityassessmentbasedonqueuingtheory ofunmannedaerialvehicles,” Sustainability,vol.15,no. 1, p. 709, 2023. [Online]. Available: https://doi.org/10.3390/su15010709
[30] A. Mohamed, M. Marino, S. Watkins, et al., “Gust encountered by flying vehicles in proximity to buildings,” Drones, vol. 7, no. 1, p. 22, 2023. [Online]. Available:https://doi.org/10.3390/drones7060365
[31] B.YuandT.Lee,“Modularreinforcementlearningfora quadrotor UAV with decoupled yaw control,” IEEE RoboticsandAutomationLetters,vol.10,no.1,pp.572–579, Jan. 2025. [Online]. Available: https://doi.org/10.1109/lra.2024.3511412
[32] C. Ramirez-Atencia, V. Rodríguez-Fernández, A. Gonzalez-Pardo, and D. Camacho, “New artificial intelligenceapproachesforfutureUAVgroundcontrol stations,” in Proc. IEEE Congress on Evolutionary Computation (CEC), Donostia, Spain, 2017, pp. 2775–2782. [Online]. Available: https://doi.org/10.1109/cec.2017.7969645
[33] R. N. Lea, “Automated space vehicle control for rendezvous proximity operations,” Telematics and Informatics, vol. 5, no. 3, pp. 179–185, 1988. [Online]. Available: https://doi.org/10.1016/s07365853(88)80022-4
[34] A.Biswas,A.K.Behera,A.K.Sahoo,D.Panda,S.Nayak, and S. Mishra, “State-of-the-art review on recent advancements on lateral control of autonomous vehicles,” IEEE Access, vol. 10, pp. 114759–114786, 2022. [Online]. Available: https://doi.org/10.1109/access.2022.3217213
[35] J. F. Hanaway and R. W. Moorehead, Space Shuttle Avionics System. Washington, DC, USA: National Aeronautics and Space Administration, Office of Management, Scientific and Technical Information Division, 1989. [Online]. Available: https://ntrs.nasa.gov/api/citations/19900015844/dow nloads/19900015844.pdf
[36] R.A.PaielliandH.Erzberger,“Trajectoryspecification forterminalairspace:Conflictdetectionandresolution,” Journal of Air Transportation,vol.27,no.2,pp.51–60, 2019. [Online]. Available: https://doi.org/10.2514/1.d0132
[37] J. Guo, S. S. Ge, X. Zhu, and F. Zhao, “Modeling of ATC operationprocessbasedonextendedcoloredPetrinet,” InternationalJournalofPerformabilityEngineering,vol. 15, no. 9, pp. 2522–2533, 2019. [Online]. Available: https://doi.org/10.23940/ijpe.19.09.p26.25222533
[38] A.Balaban,S.Berbente,A.Neamtu,G.-L.Stroe,E.Costea, I.-B.Stefanescu,I.-C.Andrei,andI.Popescu,“Casestudy of TCAS implementation in modern FMS,” INCAS Bulletin, vol. 15, no. 2, pp. 11–19, 2023. [Online]. Available: https://doi.org/10.13111/20668201.2023.15.2.2
[27] R. T. Q. Overmyer, “Democratization of aviation”: A content analysis of unmanned aerial systems policy and proliferation. Ph.D. dissertation, California State Univ., Sacramento, CA, USA, 2023. [Online]. Available: https://www.proquest.com/dissertationstheses/democratization-aviation-contentanalysis/docview/2854824094/se-2

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
[39] F. C. Gomes Sampaio, R. N. Costa Filho, and M. Xavier Guterres,“Modelingresilienceofairtrafficmanagement systems based on complex networks,” Journal of AerospaceTechnology&Management,vol.14,no.1,pp. 1–18, 2022. [Online]. Available: https://doi.org/10.1590/jatm.v14.1273
[40] A.Neamtu,A.Balaban,S.Berbente,G.-L.Stroe,E.Costea, I.-B.Stefanescu,I.-C.Andrei,andI.Popescu,“Airtraffic control software implemented in RADAR,” INCAS Bulletin, vol. 15, no. 2, pp. 59–65, 2023. [Online]. Available: https://doi.org/10.13111/20668201.2023.15.2.6
[41] F. P. Moreno et al., “Determination of air traffic complexity most influential parameters based on machinelearningmodels,” Symmetry,vol.14,no.12,p. 2629, 2022. [Online]. Available: https://doi.org/10.3390/sym14122629
[42] G. Borghini, G. Di Flumeri, P. Aricò, N. Sciaraffa, S. Bonelli,M.Ragosta,P.Tomasello,F.Drogoul,U.Turhan, B.Acikel,A.Ozan,J.P.Imbert,G.Granger,R.Benhacene, and F. Babiloni, “A multimodal and signals fusion approachforassessingtheimpactofstressfuleventson airtrafficcontrollers,” Scientific Reports,vol.10,no.1, pp. 1–18, 2020. [Online]. Available: https://doi.org/10.1038/s41598-020-65610-z
[43] A. Vidović, T. Mihetec, B. Wang, and I. Štimac, “OperationsofdronesincontrolledairspaceinEurope,” InternationalJournalforTraffic&TransportEngineering, vol. 9, no. 1, pp. 38–52, 2019. [Online]. Available: https://doi.org/10.7708/ijtte.2019.9(1).04
[44] F. Trapsilawati, L. Fan, and Y. Liu, “Ergonomics considerations in air traffic conflict detection and resolution,” InternationalJournalofTechnology,vol.14, no. 4, pp. 898–910, 2023. [Online]. Available: https://doi.org/10.14716/ijtech.v14i4.5908
[45] F.Lu,Q.Wang,J.Teng,Y.Kang,andB.Liu,“Analysisof thefeaturesofairtrafficcontrollers’eyemovements,” InternationalJournalofPerformabilityEngineering,vol. 15, no. 12, pp. 3262–3270, 2019. [Online]. Available: https://doi.org/10.23940/ijpe.19.12.p18.32623270
[46] J.ZhouandC.Kwan,“Ahighperformancecontingency planningsystemforUAVswithlostcommunication,”in Proc.IEEEInt.Conf.PrognosticsandHealthManagement (ICPHM), Seattle, WA, USA, 2018, pp. 1–8. [Online]. Available: https://doi.org/10.1109/icphm.2018.8448926
[47] K. Park, J. Rhee, M.-H. Shin, and W. Hur, “A novel CQI feedbackchannelforcellularUAVsystem,”in Proc. Int. Conf.AdvancedTechnologiesforCommunications(ATC), Hanoi, Vietnam, 2019, pp. 84–88. [Online]. Available: https://ieeexplore.ieee.org/document/8924562
[48] D.V.Vu,T.V.Pham,andD.T.Nguyen,“Apath-following guidance algorithm for fixed-wing UAV swarms on a decentralized network,” in Proc. Int. Conf. Advanced Technologies for Communications (ATC), Ha Noi, Vietnam, 2022, pp. 286–291. [Online]. Available: https://doi.org/10.1109/atc55345.2022.9942994
[50] T. Xu, Z. Yu, Y. Song, J. Ren, H. Cui, and B. Guo, “Joint computing resource scheduling and task priority selection in UAV-enabled MEC,” in Proc. 2022 IEEE SmartWorld, Ubiquitous Intelligence & Computing, Scalable Computing & Communications, Digital Twin, Privacy Computing, Metaverse, Autonomous & Trusted Vehicles (SmartWorld/UIC/ScalCom/DigitalTwin/PriComp/Meta), Haikou, China, 2022, pp. 73–80. [Online]. Available: https://doi.org/10.1109/smartworld-uic-atc-scalcomdigitaltwin-pricomp-metaverse56740.2022.00037
[51] J. Liu, C. Hu, J. Zhou, and W. Ding, “Object detection algorithm based on lightweight YOLOv4 for UAV,” in Proc.20227thInt.Conf.IntelligentComputingandSignal Processing (ICSP), Xi’an, China, 2022, pp. 425–429. [Online]. Available: https://doi.org/10.1109/icsp54964.2022.9778666
[52] C.HongandD.Shi,“Acontrolsystemarchitecturewith cloudplatformformulti-UAVsurveillance,”in Proc.2018 IEEE SmartWorld, Ubiquitous Intelligence & Computing, Advanced & Trusted Computing, Scalable Computing & Communications,Cloud&BigDataComputing,Internetof People and Smart City Innovation (SmartWorld/SCALCOM/UIC/ATC/CBDCom/IOP/SCI), Guangzhou, China, 2018, pp. 1095–1097. [Online]. Available: https://doi.org/10.1109/smartworld.2018.00190
[53] T-H.Nguyen,T.K.Nguyen,T.-D.Nguyen,andV.N.Quoc Bao, “DRL for trajectory design and resource management in UAV-aided RSMA networks,” in Proc. 2024 Int. Conf. Adv. Technol. Commun. (ATC), Ho Chi MinhCity,Vietnam,2024,pp.36–40.[Online].Available: https://doi.org/10.1109/atc63255.2024.10908260
[54] D.Pascarella,S.Venticinque,andR.Aversa,“Autonomic agents for real time UAV mission planning,” in Proc. 2013 IEEE 10th Int. Conf. Ubiquitous Intelligence and Computing (UIC) and 2013 IEEE 10th Int. Conf. AutonomicandTrustedComputing(ATC),VietrisulMare, Italy, 2013, pp. 410–415. [Online]. Available: https://doi.org/10.1109/uic-atc.2013.34
[55] J. Xu, X. Yan, and Y. Niu, “An improved butterfly optimization algorithm for UAV path planning in complexenvironment,”in Proc.2022IEEESmartWorld, UbiquitousIntelligence&Computing,ScalableComputing & Communications, Digital Twin, Privacy Computing, Metaverse, Autonomous & Trusted Vehicles (SmartWorld/UIC/ScalCom/DigitalTwin/PriComp/Meta), Haikou,China,2022,pp.1044–1050.[Online].Available: https://doi.org/10.1109/smartworld-uic-atc-scalcomdigitaltwin-pricomp-metaverse56740.2022.00154
[56] C.Hu,J.Zhou,W.Ding,J.Liu,andY.Niu,“Digitaltwinsbasedmulti-agentdeepreinforcementlearningforUAVassisted vehicle edge computing,” in Proc. 2022 IEEE SmartWorld, Ubiquitous Intelligence & Computing, Scalable Computing & Communications, Digital Twin, Privacy Computing, Metaverse, Autonomous & Trusted Vehicles (SmartWorld/UIC/ScalCom/DigitalTwin/PriComp/Meta), Haikou,China,2022,pp.1329–1336.[Online].Available: https://doi.org/10.1109/smartworld-uic-atc-scalcomdigitaltwin-pricomp-metaverse56740.2022.00192
[49] C.HongandD.Shi,“Acontrolsystemarchitecturewith cloudplatformformulti-UAVsurveillance,”in Proc.IEEE SmartWorld, Ubiquitous Intelligence & Computing, Advanced & Trusted Computing, Scalable Computing & Communications,Cloud&BigDataComputing,Internetof People and Smart City Innovation (SmartWorld/SCALCOM/UIC/ATC/CBDCom/IOP/SCI), Guangzhou, China, 2018, pp. 1095–1097. [Online]. Available: https://doi.org/10.1109/smartworld.2018.00190

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
[57] L.He,H.Zheng,andX.Zhai,“REUT:Aretinex-inspired low-lightimageenhancerforUAVtrackingatnight,”in Proc. 2022 IEEE SmartWorld, Ubiquitous Intelligence & Computing, Scalable Computing & Communications, DigitalTwin,PrivacyComputing,Metaverse,Autonomous & Trusted Vehicles (SmartWorld/UIC/ScalCom/DigitalTwin/PriComp/Meta), Haikou,China,2022,pp.1051–1057.[Online].Available: https://doi.org/10.1109/smartworld-uic-atc-scalcomdigitaltwin-pricomp-metaverse56740.2022.00155
[58] J.Tian,B.Wang,R.Guo,Z. Wang,K.Cao,andX. Wang, “Adversarial attacks and defenses for deep-learningbasedunmannedaerialvehicles,” IEEEInternetofThings Journal,vol.9,no.22,pp.22399–22409,Nov.15,2022. [Online]. Available: https://doi.org/10.1109/jiot.2021.3111024
[59] T. Karachalios, C. Xouris, and T. Orphanoudakis, “OptimizingUAVlocationawarenesstelemetrydatafor low power wide area network,” Proc. 25th Euromicro Conf. Digital Syst. Design (DSD), Maspalomas, Spain, 2022, pp. 885–888. [Online]. Available: https://doi.org/10.1109/dsd57027.2022.00124
[60] D.Li,Y.Qiang,andJ.H.Mott,“Hazardanalysisoflarge cargodeliveryUAVsundertheChineseairtrafficcontrol system,” Proc.2021SystemsandInformationEngineering DesignSymp.(SIEDS),Charlottesville,VA,USA,2021,pp. 1–6. [Online]. Available: https://doi.org/10.1109/sieds52267.2021.9483732
[61] A.Ganau,J.Vico,P.Morcillo,andJ.V.Balbastre,“Design and validation of reflector elements to increase the radarcross-sectionofsmalldrones,” Prog.Electromagn. Res. C,vol.128,pp.129–142,2023.[Online].Available: https://doi.org/10.2528/pierc22092003
[62] C.Cummings, Air traffic flow and the congestion of the skies:Models,insights,andmanagementstrategiesforthe air mobility context, Ph.D. dissertation, Northwestern Univ., Cook County, IL, USA, 2022. [Online]. Available: https://www.proquest.com/dissertations-theses/airtraffic-flow-congestion-skies-modelsinsights/docview/2707696219/se-2
[63] M.B.BrownandA.B.Forsythe,“Testsfortheequalityof variances,” J. Amer. Statist. Assoc., vol. 69, no. 346, pp. 364–367, Jun. 1974. [Online]. Available: https://doi.org/10.2307/2285659
[64] S.S.ShapiroandM.B.Wilk,“Ananalysisofvariancetest fornormality(completesamples),” Biometrika,vol.52, no. 3–4, pp. 591–611, Dec. 1965. [Online]. Available: https://doi.org/10.2307/2333709

Andrew Renault is a graduate studentintheAeronauticalScience DepartmentatCapitalTechnology University, where he focuses on advancing research in air traffic managementandunmannedaerial vehicle (UAV) integration. With over 30 years of engineering experience in the aerospace industry,Andrewhascontributed to a variety of projects ranging from aircraft design to systems optimization. His expertise spans both technical and regulatory aspects of aerospace operations, making him a key voice in discussions on modernizing air traffic control systems and addressingemergingchallengesin aviation.