Neighbor Spoofing in Voice Fraud
A Trust-Amplification Layer in Modern Phone-Based Attacks
Research by Infosprint Technologies



A Trust-Amplification Layer in Modern Phone-Based Attacks
Research by Infosprint Technologies


Neighbour spoofing is often dismissed as a minor scam tactic4 a simple trick used by low-level fraudsters.
In reality, it operates as a sophisticated delivery layer that enables fraud at scale. This isn't about individual scams4it's about systematic infrastructure that amplifies the effectiveness of every downstream attack.
Understanding this distinction is critical to building effective defenses.



Doesn't pretend to be someone specific
Doesn't rely on social engineering scripts
Designed to increase answer rates and suppress early suspicion
Neighbour spoofing functions as a trust-amplification layer4creating the conditions for fraud to succeed before any conversation begins. It's infrastructure, not content.



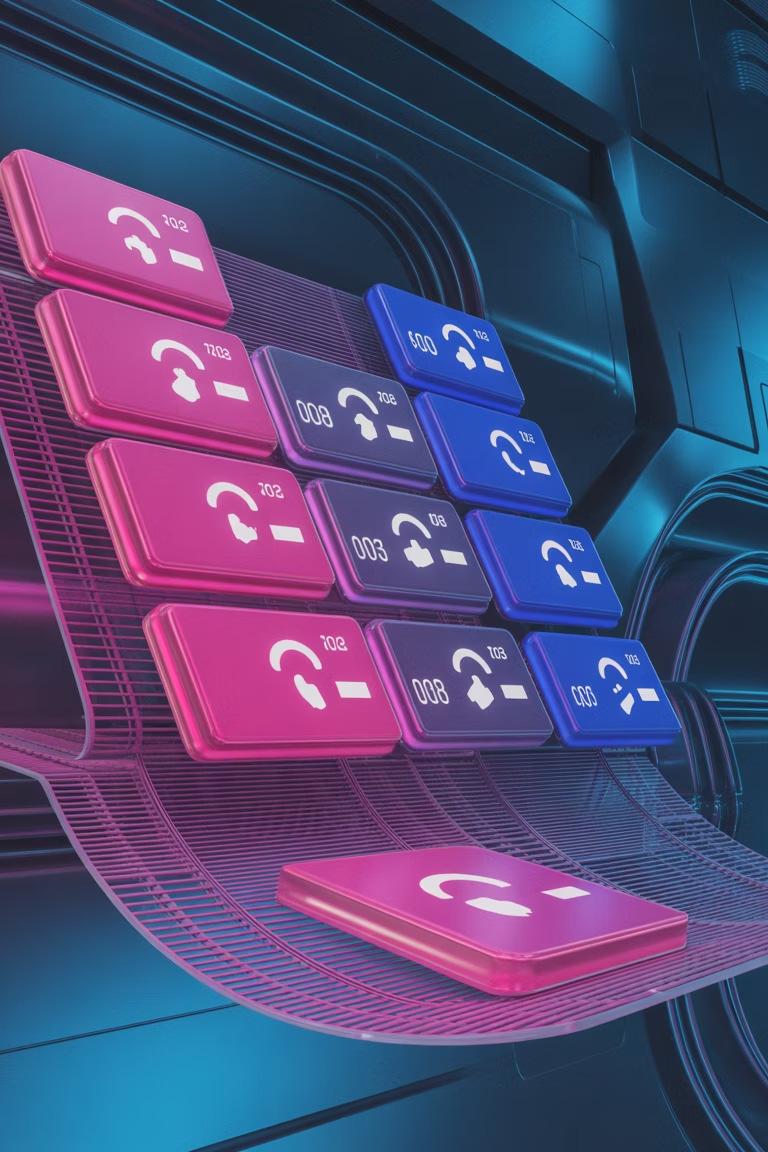
Attackers deliberately mirror local area codes and exchanges to create geographic plausibility. The strategy is precise and calculated.
Target Selection
Identify victim's area code and exchange pattern
Number Matching
Spoof caller ID to mirror local geographic markers
Identity Rotation
Cycle numbers before detection systems trigger
Critically, attackers avoid reusing identities long enough to trigger detection. The rotation happens based on performance metrics, not complaints4making traditional tracking methods ineffective.



During initial contact, a local number often generates more trust than a recognized brand. Why? Because local calls carry implicit legitimacy4they could be your doctor, your child's school, a neighbor, or a local business.
Ambiguity drives engagement before trust is challenged. By the time the recipient realizes something is wrong, the conversation has already begun and psychological commitment has set in.




The fundamental vulnerability lies in how phone systems were designed. Understanding these constraints explains why neighbour spoofing remains so effective.
The number you see is transmitted data, not verified identity. It was designed for convenience, not security.
These frameworks confirm a call came from a legitimate carrier4but they cannot determine whether that carrier's customer is a fraudster.
Unlike email authentication or HTTPS, voice networks lack a standardized mechanism to verify caller legitimacy at scale.


Neighbour spoofing operates early in the attack chain, absorbing risk and enabling downstream fraud techniques to function more reliably. It's the foundation that makes everything else possible4by securing the initial connection, it dramatically increases the success rate of subsequent manipulation tactics.
Discuss Voice Fraud Exposure


Traditional blocking relies on identifying and flagging specific numbers. But when attackers rotate through thousands of numbers, blocklists become obsolete before they're even deployed.

Awareness campaigns tell people to "be suspicious of unknown numbers." But neighbour spoofing exploits the opposite4numbers that appear known and local, triggering automatic trust responses.

Unlike email or text, voice calls demand immediate response and lack visual verification cues. The medium itself works against rational decisionmaking.


Neighbour spoofing should be treated as infrastructure-level risk, not an isolated incident. This isn't a problem that can be solved with user education or simple blocklists. It requires systemic changes to how we authenticate voice communications4treating caller identity verification with the same rigor we apply to digital authentication.
Organizations must shift from reactive incident response to proactive infrastructure defense, recognizing that neighbour spoofing is the foundation enabling a much larger fraud ecosystem.
Implement carrier-level authentication
Deploy behavioral analysis systems
Advocate for regulatory frameworks
Treat voice fraud as infrastructure risk
Read the Full Analysis