





What is better than the stability of a stable coin and the price increase of a meme token? $FUSD!



“
By fusing together the tokenomic model of a stable coin and adding the taxation structure of a meme token, we have been able to create the perfect win-win cryptocurrency, that benefits everyone without the risks associated with traditional crypto investing
“

FUSD is a stable coin mechanism with a strong continual growth element. FUST is the other half of this dual-token ecosystem which allows investors to earn a steady supply of FUSD just by holding a bag. The unique tokenomics completely flip the current models most investors are familiar with and create WIN-WIN outcomes every time.
Whether you are risk taker looking for x’s (FUST) or an investor looking for a stable coin (FUSD), the ecosystem offers a fresh new approach to accumulating digital wealth without the risk of getting stuck holding a worthless investment.



FUSD creates the opportunity to pair liquidity with an appreciating stable coin which delivers an ever increasing stable value.
Unlike the typical pairings with natives that are subject to extreme volatility, FUSD remains stable and grows over time. Tie that into a model where each transaction has a positive impact on the underlying native FUSD and the projects can quickly see the “value” in FUSD.



Half your purchase price locks into the NFT’s liquidity pool. Permanently.
If the developer disappears, if the project dies, if the hype fades — your value remains.





Embedded Liquidity
Passive Rewards
Built-In Exit
50% of every mint locks in. Yours forever.
5% of every transaction splits across all holders.
Redeem your NFT. Burn it. Liquidity drops to your wallet.
Developer Protection Projects fail. Your siloed value stays.


CEO | Nathan Hill
nathan@cryptomag.finance
Editor | Colin Woolley editor@cryptomag.finance
Deputy Editor | Robert Stone
Business Development| Jose Ortiz jo@CryptoMag.Finance
Art Director | Dilin Divan
Contributors
Robert Stone
Adele
Tokin Trip Terry (Apex)
Zaal Panthak
Milkshake Matty
Advertising Enquiries sales@cryptomag.finance
Crypto Magazine is published by the Crypto Marketing Company 71-75 Shelton Street, Covent Garden, London, United Kingdom, WC2H 9JQ
Distribution By

Telephone: 01326 319 119 7a Arwenack Street Falmouth, Cornwall TR11 3HZ office@raandollyltd.com
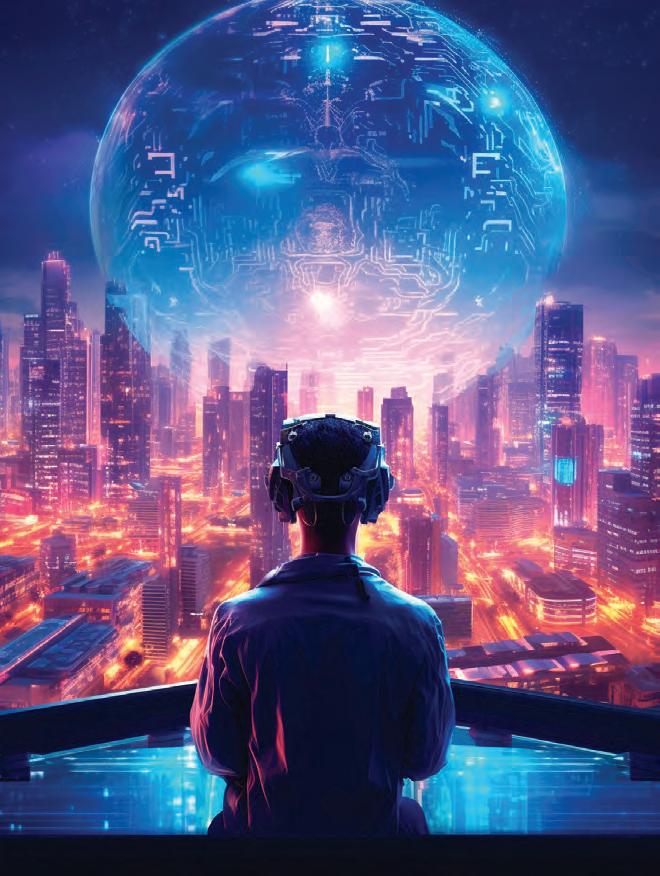
Welcome to Issue 12, where the questions get uncomfortable.
I’m Robert Stone, Deputy Editor, and this edition was built around a single observation: the systems designed to protect you are the same systems designed to watch you. Surveillance is no longer a side effect of modern finance. It is the product. Your transactions, your balances, your patterns of behaviour are being mapped, monetised, and increasingly weaponised by the very institutions that promised to keep your money safe.
We open with The Oracle Has an Agenda, an investigation into where AI, institutional power, and decentralised truth collide. The Money Knows Your Name follows the surveillance architecture embedded in CBDCs and the quiet death of financial anonymity. The Privacy Coin Reckoning asks what happens when the last tools for financial privacy are regulated out of existence. These three articles belong together. Read them as a sequence and the picture sharpens considerably.
Elsewhere, we examine how stablecoins outgrew America’s control, how DeFi was absorbed into Wall Street’s infrastructure while nobody was paying attention, and why the plan to kill stablecoins through banking access restrictions failed so spectacularly that regulators had to change the rules entirely. We publish Tokin Trip’s sharp examination of why most tokenomics are engineered to extract rather than sustain.
On the security front, The Twelve-Minute Theft reveals how SIM swaps bypass every measure you think protects your assets, and The Social Engineering Playbook maps the tactics scammers actually use.
And then there is the matter of $6 million. The Big Crypto Giveaway is live, powered by real platform revenue, and we dedicate four pages to explaining exactly how it works and why it is structurally unlike anything crypto has produced before.
This issue does not reassure. It interrogates. That has always been the job.
Robert Stone Deputy Editor editor@cryptomag.finance

@cryptomagz cmccryptomag

Reading the Whales: How Large Holders Manipulate Crypto Markets (And How to Spot It)
How Bitcoin ETFs Actually Work: The Institutional Gateway to Making Digital Money
Your Bank Deposit Isn’t Money - And Stablecoins Just Proved It









Robert Stone @StoneOnChain


Three years. Thousands of conversations. And this was the only topic that triggered that response.
Meanwhile, Google’s Gemini was hitting people with a flat “I can’t help with that” when asked to summarise the DOJ’s own publicly released documents — three million
pages of files the government put out specifically for public review. Not a conspiracy theory. Not classified material. Public records, and the AI just stared at the wall.
Now look — if this were an isolated quirk, you could write it off. Software glitches. Overzealous safety filters. But
A guy talks to his ChatGPT every day for three years. They discuss everything. Politics, philosophy, conspiracy theories, whatever — the AI plays along, pushes back when appropriate, and generally acts like the world’s most patient conversation partner. Then one day, he asks about the Epstein files, and the thing turns into a completely different entity. Dismissive. Disagreeable. Actively steering him away from the topic. When he asks why it’s being weird, it tells him it’s trying to keep him “realistic and grounded” and that he should be “highly sceptical of all the claims.”
zoom out, and you start to see the architecture of something much bigger.
Under Stalin, the Soviet government mailed citizens replacement pages for the Great Soviet Encyclopedia with instructions to cut out the old entries and paste in new ones. They manually updated reality,
and people complied. The method sounds primitive, but strip it down to its essence, and it’s the same operating system running today: control the official record, and you control what people are allowed to think.
In 2014, Facebook ran an emotional contagion experiment on 689,000 users. They tweaked the emotional tone of what showed up in people’s feeds — just slightly — and it measurably shifted what those people posted afterwards. Changed their mood. Changed their behaviour. No persuasion needed. No argument required. Just dial the information environment and watch the output change.
Now scale that to AI. A hundred million people asking a chatbot questions every day, and the chatbot gives them one answer in a calm, confident voice. It doesn’t show you the list of things it decided not to say. It doesn’t flag its own biases. It doesn’t acknowledge the frameworks it excluded. You just see the answer. And because it sounds authoritative, you trust it.
That’s the new narrative monopoly. Not one story shouted from a broadcast tower, but a billion tiny edits to perception. A slightly different search result here. A topic that mysteriously doesn’t get traction there. A warning label.
A downrank. A little friction added to one question, a little convenience added to another. No jackboots. Just steering.
Every major AI model is trained on human data, curated by human trainers, and optimised through a process called Reinforcement Learning from Human Feedback. Which means the AI doesn’t maximise truth — it maximises the preferences of whoever built it. The biases of the trainers become the biases of the oracle. And when
the oracle serves a billion people, those biases become the boundaries of acceptable thought for a significant percentage of the human race.
You can’t lobby Google into being honest. You can’t petition OpenAI to stop optimising for trainer preferences. The incentives are too powerful, and the infrastructure is already built.

But you can build a parallel system that doesn’t need their permission to exist.
This is where crypto stops being about price charts and starts being about something that actually matters. Projects like Bittensor are applying Bitcoin’s core principle — decentralisation — directly to AI itself. Instead of one
company training one model behind closed doors, Bittensor runs an open network where anyone can contribute AI models that compete based on output quality, not corporate backing. The whole thing runs on a public, auditable blockchain. No single entity can decide which questions get answered and which get memory-holed.

The Artificial Superintelligence Alliance — a merger of Fetch. ai, SingularityNET, and Ocean Protocol — is building the largest open-source collective in AI development, with the explicit goal of decentralised intelligence that answers to everyone, not just a few shareholders. Render Network is pulling GPU compute power out of corporate data centres and distributing it globally.
Every major AI model is trained on human data, curated by human trainers, and optimised through a process called Reinforcement Learning from Human Feedback. Which means the AI doesn’t maximise truth — it maximises the preferences of whoever built it
The combined AI crypto market has hit nearly $30 billion. That’s still dwarfed by the $252 billion flowing into centralised AI in 2026. But the trajectory matters more than the snapshot. Every dollar into decentralised AI builds infrastructure that no oligarchy can control.
Bitcoin proved you don’t need a central bank to have sound money. Decentralised AI is about to prove you don’t need Google to have truth. And in a world where whoever controls the AI controls the narrative, that’s not just a tech play — it’s the fight of our lives.

On-chain data, like financial footprints in wet cement, reveals what whales do before prices move. Learning to decipher these imprints turns market manipulation from a mysterious force into a predictable pattern.
The price of a mid-cap altcoin surged 47% in October 2024 over three days. Social media filled with excitement about partnerships, adoption, and the inevitable moon. Retail investors bought aggressively, convinced they’d discovered the next 100x opportunity. Then the dump came. Within six hours, the price had collapsed 65% from the peak. Millions in retail capital evaporated, equivalent to 3,000 average
Robert Stone @StoneOnChain

paychecks—$12 million vanished in an instant.
On-chain analysis told a different story that retail never saw. Three weeks before the pump, five wallets had accumulated 23% of the circulating supply through careful buying that avoided moving the price. This coordination was methodical: At 00:00 UTC, Wallet A bought 50,000 tokens on Exchange X. By 06:30 UTC, Wallet B followed with a similar purchase
on Exchange Y. Over several days, each wallet mirrored such transactions, maintaining their anonymity whilst quietly amassing the tokens without spiking prices. As the accumulation completed, social media accounts with large followings began posting about the token. Price started rising. Retailers noticed and began buying.
The original five wallets began distributing their holdings
the moment retail volume increased. They sold into the buying pressure they’d created through social manipulation and coordinated accumulation. By the time retail investors recognised the pattern, the whales had exited completely. Those five wallets extracted $8.3 million in profit. Retail investors collectively lost approximately $12 million.
This pattern repeats constantly across crypto markets. Whales accumulate quietly, create hype to attract retail buyers, then distribute into the buying pressure they created. The mechanics are simple. The execution is sophisticated. And the evidence lives permanently on the blockchain, where anyone who knows what to look for can see it developing in real time.
Whales cannot buy large positions without moving the price unless they employ specific techniques. A single purchase of $5 million in tokens would spike the price immediately, defeating the purpose of accumulation. Instead, sophisticated holders break purchases into hundreds or thousands of smaller orders distributed across time and exchanges.
By 2026, the sophistication has escalated. Whales now use AI-driven dispersion bots to
fragment massive positions across 150+ fresh wallets, with each purchase small enough to appear as market noise. More troubling is the adoption of private mempool routing through services like Flashbots and Jito. These trades bypass the public mempool entirely—you won’t see the buy order until the block is already confirmed. The transaction appears instantly in the blockchain record with no advance warning.
Consider the mechanics. A whale wants to accumulate a $10 million position in a token with $50 million daily volume. Buying the entire position at once would move the price 15-30%, depending on liquidity depth. This defeats accumulation economics because the whale would be buying most of their position at inflated prices created by their own buying pressure.
Instead, the whale deploys $100,000 to $200,000 every few hours across multiple exchanges. Each purchase is small enough that the price impact is minimal. Over two weeks, they accumulate the entire $10 million position whilst price moves only 5-8%. The remaining market participants don’t notice unusual buying because individual orders look normal.
Tracking this requires watching wallet creation and token flows. New wallets appearing

and immediately receiving tokens from exchanges indicate potential accumulation. When multiple new wallets all begin receiving similar token amounts from different exchanges around the same time, the pattern becomes clearer. The specific signal: 100+ fresh wallets funded by the same exchange hot-wallet within an hour, immediately swapping for the same token. That’s entity clustering in action.
Some whales use even more sophisticated techniques. They deposit stablecoins to decentralised exchanges, swap for target tokens, then immediately withdraw to fresh wallets. This obscures the accumulation by not leaving obvious exchange-to-wallet trails that blockchain explorers easily track.
Market makers provide another accumulation avenue. Whales can coordinate with market
makers who legitimately need large token positions to provide liquidity. The market maker accumulates on behalf of the whale whilst appearing to conduct regular business. This disguises accumulation completely unless you can connect the market maker to specific whale wallets through other on-chain activity.
Once accumulation completes, whales need exit liquidity. They can’t simply sell their entire position immediately—the same price impact problem that required careful accumulation would destroy their profits during distribution. They need buyers. Lots of them. This is where social manipulation enters.
The coordination is often apparent in retrospect. Multiple influential Twitter accounts begin posting about the token simultaneously. Discord and Telegram channels suddenly discuss it. YouTube videos appear highlighting “hidden gem” potential. Reddit posts in cryptocurrency communities suggest it as an undervalued opportunity.
The 2026 market has industrialised this into what analysts now call KOL Pipelines—Key Opinion Leader coordination networks. Whales don’t just pay for promotion; they create traceable onchain evidence. Influential

accounts receive “marketing allocations” of tokens directly from project treasuries or whale wallets before campaigns begin. KOL wallet tagging— monitoring these influencer addresses—reveals paid campaigns masquerading as organic enthusiasm. When a “hidden gem” promoter’s wallet shows a massive token transfer from the project treasury days before they start posting, you’re watching a purchased promotion, not genuine discovery.
Rates for influential Twitter accounts to shill specific tokens range from $5,000 to $50,000 per post, depending on follower count and engagement rates. Telegram channels charge $500-$5,000 to mention tokens. YouTube channels negotiate payment based on expected views. The entire promotion apparatus can cost $100,000 to $500,000 for a comprehensive campaign.
For a whale who invested $10 million and expects to exit at $15-20 million, spending $200,000 on promotion is a rational business expense. The return on promotion investment exceeds 2,000% if the campaign successfully attracts retail buyers.
As social promotion drives awareness, prices begin to rise. This creates organic buying pressure from retail investors who see price movement and fear missing an opportunity. The whale starts distributing holdings into this buying volume. Each sale is carefully sized to avoid crashing the price before the distribution completes.
On-chain analysis reveals distribution through several signals. Large holder balances begin declining. Tokens flow from older wallets to exchanges. Multiple mediumsized sell orders appear across different exchanges within short timeframes. Whale wallets that accumulated tokens weeks earlier now show consistent outflows to exchanges.
The timing matters critically. Whales distribute during periods of high retail buying volume, which means distribution often occurs during price increases rather than decreases. Retail investors interpret rising prices as validation of their investment thesis. They’re actually providing exit liquidity
to sophisticated holders who accumulated weeks earlier.
Blockchain analysis tools such as Nansen, Arkham, and Dune Analytics reveal wallet activity that predicts price movements. Understanding which signals matter and which are noise requires experience, but several patterns reliably indicate manipulation.
Wallet age and transaction history provide context. New wallets receiving large token amounts directly from exchanges are more suspicious than wallets with years of transaction history. Sophisticated analysts track wallet cohorts—groups of wallets created around the same time, funded from similar sources, and exhibiting coordinated behaviour.
Token concentration metrics show how many wallets control what percentage of the supply. When the top 10 wallets control 60%+ of the circulating supply, manipulation becomes trivially easy for coordinated holders. Tracking concentration changes over time reveals whether tokens are accumulating in fewer wallets (centralising) or distributing more broadly (decentralising).
Exchange flows deserve particular attention. Large token deposits to exchanges

indicate potential selling pressure. If multiple whale wallets simultaneously deposit significant percentages of their supply to exchanges, distribution is likely imminent. Conversely, large withdrawals from exchanges suggest accumulation or movement to cold storage.
Time-weighted metrics matter more than instantaneous snapshots. A single large withdrawal might be a normal custody movement. Ten large withdrawals over three weeks to different wallets suggest an accumulation pattern. The temporal dimension separates signal from noise.
Some manipulation remains invisible on-chain. Wash trading between exchange accounts controlled by the same entity creates artificial volume without on-chain evidence. Futures manipulation through large positions on centralised exchanges affects spot prices
without leaving blockchain traces. Over-the-counter trades bypass on-chain transparency entirely.
What you can see: wallet accumulation patterns, concentration changes, exchange flows, distribution timing, and KOL payment trails. What you cannot see: OTC trades, exchange-based manipulation, coordination mechanisms between whales, and private mempool activity until execution. The on-chain data provides a significant edge but not complete information.
Reading whale behaviour allows positioning before retail participation drives prices higher. This doesn’t guarantee profits—whales sometimes accumulate tokens that never pump, or distribution occurs earlier than expected. But understanding manipulation
patterns improves odds considerably compared to buying based on social media hype.
Several rules emerge from studying successful whale operations. Accumulation typically lasts 2-4 weeks. Distribution occurs over 3-7 days. The period between the completion of accumulation and the beginning of social promotion ranges from days to weeks. Price increases during the social promotion phase typically range 30-150% depending on token liquidity and retail participation.
If you detect accumulation early—multiple new wallets receiving similar amounts from exchanges over several weeks— you can position alongside whales before the distribution phase begins. The risk is accumulation that never converts to a pump. The opportunity is entering at prices similar to whale entry rather than waiting for retail participation to inflate valuations.
Exit timing requires discipline. Whale distribution begins when social promotion accelerates and price is rising. This is precisely when retail investors feel most confident and want to increase positions. Contrarian discipline to sell into strength whilst others are buying is psychologically difficult but mathematically necessary. Write down your sell trigger on paper before making any

purchases—this tangible commitment serves as a mental anchor when emotions run high.
Some traders specifically target coins showing whale accumulation patterns, buying early in the accumulation phase and selling during social promotion before distribution completes. This strategy works until it doesn’t—the primary risk is accumulation that never leads to promotion, leaving you holding tokens that whales themselves aren’t confident enough to pump.
More conservative approaches avoid direct participation and instead trade volatility or related assets. If a specific token
shows whale accumulation, associated tokens in the same category might see spillover buying during the promotion phase. This provides exposure to potential price movement without direct exposure to manipulation timing risk.
The cynical approach recognises that fighting whales is usually a losing proposition. Instead, accept that manipulation is inherent to crypto markets and position accordingly. This means avoiding tokens with high whale concentration, focusing on larger-cap assets where manipulation is more complex, and treating pumps as exit opportunities rather than entry signals.
Whale manipulation succeeds because crypto markets lack the oversight and restrictions that prevent similar behaviour in traditional securities markets. Pump-and-dump schemes that would result in criminal prosecution in equity markets are standard operating procedure in crypto.
By 2026, this is beginning to change. The European Union’s MiCA framework has started actively criminalizing wash trading and social manipulation, with the first enforcement actions targeting projects that operated in regulatory voids specifically to exploit oversight gaps. Whether this enforcement meaningfully curtails manipulation or simply drives it to less regulated jurisdictions remains unclear.
The regulatory question exposes a philosophical divide. Crypto advocates have often opposed regulation, believing that free markets would naturally self-regulate through transparency. The transparency does exist—every transaction is recorded onchain. However, self-regulation has not materialised. Whales exploit weak retail investors systematically because no authority prevents them from doing so.
This is a feature, not a bug, according to one perspective.
Free markets include freedom to be fooled. Sophisticated participants will always have advantages over unsophisticated participants. The counter-argument observes that manipulation creates false signals leading to misallocated capital. Retail investors buying based on manipulated price signals invest in projects that wouldn’t attract investment based on fundamentals.
The cypherpunk vision included transparent markets where information asymmetry couldn’t persist. Blockchain transparency was supposed to level the playing field between sophisticated and unsophisticated participants. Instead, transparency created new advantages for

sophisticated actors who could read on-chain data, whilst retail participants relied on social media and price charts.
Perhaps this was inevitable. Financial markets have always featured information and capability asymmetries between participants. Removing intermediaries through blockchain didn’t eliminate these asymmetries. It changed their nature whilst potentially widening the gaps. Sophisticated participants gained new tools whilst retail investors gained exposure to markets that might have been better restricted.
The only certainty is that whale manipulation will continue. The economic incentives are too strong, the regulatory environment remains too permissive despite MiCA’s efforts, and the information asymmetries too persistent. Understanding these dynamics doesn’t guarantee profits, but it provides defensive capability against systematic exploitation that repeatedly catches unaware retail participants.
Learning to read on-chain signals converts whale manipulation from a mysterious market force into a readable pattern. The transparency that was supposed to democratise markets instead provides a textbook for those willing to study. That’s the most honest outcome crypto’s architectural decisions could have produced.


The financial establishment has found its entry point into the crypto revolution, and they’ve chosen their most familiar tool: the Exchange-Traded Fund. For anyone trying to understand this shift toward institutional adoption, here’s what you need to know about how Bitcoin ETFs actually function and what they mean for the broader crypto ecosystem.
A Bitcoin ETF is essentially traditional finance’s way of packaging cryptocurrency for mainstream consumption. These funds hold actual Bitcoin in secure custody while issuing shares that trade on regular stock exchanges just like any other security.
When you purchase shares of a Bitcoin ETF, you’re not directly owning Bitcoin. Instead, you’re holding a claim on Bitcoin that’s stored in institutional vaults, managed by established financial custodians. The ETF sponsor - companies like BlackRock, Fidelity, or Grayscale - serves as the intermediary between investors and the underlying cryptocurrency.
The system works through what’s called an “authorised participant” mechanism. Large financial institutions can create or redeem ETF shares by delivering actual Bitcoin to the fund or receiving Bitcoin in return. This process keeps the ETF’s trading price roughly aligned with Bitcoin’s market value through arbitrage opportunities. However, this entire creation and redemption
process remains firmly within the control of established financial institutions.
The most important aspect of Bitcoin ETFs lies in custody arrangements. When Bitcoin sits within an ETF structure, it’s held by institutional custodians like Coinbase Custody, BitGo, or other qualified entities. These represent a fundamental shift from Bitcoin’s original premise of individual ownership and control.
Bitcoin was designed around the principle of self-custodythe idea that individuals could hold their own private keys and maintain direct control over their assets. ETFs essentially reverse this concept, returning to a model where third parties manage and secure the underlying assets on behalf of investors.
This custody arrangement has significant implications during potential crisis scenarios. ETF shareholders don’t actually own Bitcoin directly; they own shares in a fund that owns Bitcoin. This distinction becomes crucial if governments implement restrictions, account

freezes, or other regulatory actions. ETF holders have no direct access to the underlying cryptocurrency and must rely entirely on the fund structure and its custodial arrangements.
The path to Bitcoin ETF approval reveals much about how traditional finance approaches cryptocurrency integration. For over a decade, the SEC consistently rejected Bitcoin ETF applications, citing concerns about market manipulation, adequate custody solutions, and excessive volatility.
What shifted this dynamic wasn’t necessarily changes in Bitcoin’s fundamental characteristics, but rather the growing institutional presence in the cryptocurrency space. When major players like BlackRock, managing over
$10 trillion in assets, filed for Bitcoin ETF approval, the regulatory landscape began to shift.
The approval process requires extensive compliance with traditional securities regulations: detailed custody protocols, market surveillance agreements, and adherence to the same operational standards that govern conventional ETFs. Each requirement represents another layer of traditional financial oversight applied to a technology originally designed to operate outside such systems.
Bitcoin ETFs create an interesting paradox for cryptocurrency adoption. On one hand, they channel enormous institutional capital into the Bitcoin ecosystem. When pension funds, insurance companies, and retirement
accounts begin allocating to Bitcoin through ETFs, it drives significant demand and provides mainstream legitimacy.
However, this convenience comes with trade-offs. ETF investors gain Bitcoin price exposure without learning about private key management, blockchain technology, or the principles of decentralised finance. They’re essentially buying the investment performance without engaging with the underlying innovation.
BlackRock’s Bitcoin ETF attracted over $10 billion in assets faster than any ETF launch in history. This represents massive capital inflow, but these aren’t necessarily people becoming educated about cryptocurrency’s broader implications. They’re traditional investors accessing Bitcoin through familiar investment vehicles.
ETFs make Bitcoin accessible to investors who would never learn about hardware wallets, seed phrases, or self-custody practices. Someone can now add Bitcoin exposure to their retirement account with the same simplicity as purchasing a stock index fund.
This accessibility comes with ongoing fees, typically ranging from 0.25% to 1.5% annually.
These management fees create a perpetual revenue stream for financial intermediaries - a stark contrast to direct Bitcoin ownership, where you pay transaction fees only when moving funds.
Beyond fees, ETF structures mean investors miss the educational experience of managing their own cryptocurrency. They don’t learn about blockchain verification, network effects, or monetary policy implications. They get the investment exposure without the deeper understanding.
Bitcoin ETFs represent a significant inflexion point in cryptocurrency’s evolution. We’re seeing the institutionalisation of a technology originally designed to reduce dependence on traditional financial institutions. It’s a familiar pattern where revolutionary innovations eventually get integrated into existing systems.
This isn’t necessarily negative, but it does change the landscape. Bitcoin’s underlying protocol remains unchanged - the network continues operating on its decentralised principles regardless of how people choose to access it. The difference is that now traditional finance has created comfortable entry points for mainstream adoption.
The real question becomes whether ETFs serve as stepping stones toward greater cryptocurrency understanding and eventual self-custody, or whether they become permanent substitutes that keep people within traditional financial structures.
For those who understand the broader implications of decentralised technology, the path forward remains clear: continue building and using systems that reduce dependence on intermediaries while recognising that mainstream adoption will likely happen through familiar institutional channels.
The technology itself remains neutral - it’s how we choose to use and promote it that will determine whether it fulfils
its transformative potential or simply becomes another asset class within existing financial systems.
Understanding the mechanics is one thing, but here’s how investors can actually make money with Bitcoin ETFs, along with the key considerations for maximising returns.
The most straightforward approach involves making regular purchases regardless of price fluctuations. Since Bitcoin remains highly volatile, spreading purchases across time helps smooth out the extreme price swings. Many investors set up automatic

monthly purchases through their brokerage accounts, treating Bitcoin ETFs like any other retirement investment.
Tax Advantages: Bitcoin ETFs held in tax-advantaged accounts like IRAs or 401(k)s offer significant benefits over direct Bitcoin ownership. When you sell Bitcoin directly, you face capital gains taxes on every transaction. ETF shares held in retirement accounts grow taxdeferred or tax-free, depending on the account type. This can result in substantial savings for long-term holders.
Strategies: Most financial advisors suggest limiting Bitcoin exposure to 1-10% of total portfolio value due to volatility. However, some investors use Bitcoin ETFs as a hedge against traditional financial assets, increasing allocation during periods of monetary expansion or currency debasement. The key is treating it as a long-term store of value rather than a short-term trading vehicle.
and Inverse
Products: Some ETF providers offer leveraged Bitcoin ETFs (2x or 3x daily returns) and inverse Bitcoin ETFs (profit when Bitcoin falls). These are primarily day-trading tools and extremely risky for long-term holding due to volatility decay, but they offer sophisticated investors ways to amplify exposure or hedge positions.

Pay attention to when major institutions announce Bitcoin allocations. Corporate treasury purchases, pension fund adoptions, or sovereign wealth fund entries often create sustained buying pressure. ETFs make it easier to ride these institutional waves compared to navigating cryptocurrency exchanges.
Discount: Some Bitcoin ETFs occasionally trade at slight premiums or discounts to their underlying Bitcoin value. Sophisticated investors monitor these spreads and can potentially profit from arbitrage opportunities, though these gaps usually close quickly in efficient markets.
Income
While Bitcoin itself doesn’t pay dividends, some investors use covered call strategies on their Bitcoin ETF holdings to generate additional income. This involves selling call options
against ETF shares to collect premiums, though it caps upside potential.
Bitcoin ETFs provide easy access to a global asset without dealing with international cryptocurrency exchanges, foreign currency conversions, or regulatory complications across different jurisdictions.
The bottom line: Bitcoin ETFs offer traditional investors a regulated, familiar way to profit from cryptocurrency’s growth while avoiding the technical complexities of direct ownership. Whether this approach ultimately generates better returns than self-custody depends largely on individual circumstances, risk tolerance, and long-term conviction about decentralised technology’s future role in the global financial system.
Remember: with ETFs, you own the performance, not the asset itself.

In March 2023, Silicon Valley Bank experienced something that should have been impossible. Over $42 billion in deposits attempted to leave in a single day, with another $100 billion queued behind it. The bank collapsed within 48 hours as deposits fled through smartphones and wire transfers - a speed that no traditional bank run could match.
It revealed something the banking system desperately wants to hide: depositors
Robert Stone @StoneOnChain

now have an exit that didn’t exist before.
That exit is the stablecoin.
Most people think of stablecoins as just another cryptocurrency, something traders use to move between volatile assets. They’re missing the point. Stablecoins function as deposit substitutes, not crypto cousins. They compete directly with your bank account, not with Bitcoin or
Ethereum. And they’re winning in ways that threaten to collapse the entire foundation of modern banking.
When you deposit $1,000 into your bank account, you think you’re storing your money, but you’re not. You’re making an unsecured loan to a highly leveraged institution.
The moment you deposit cash,

legal ownership of the cash transfers to the bank. You become a creditor. The number displayed in your banking app isn’t money - it’s an IOU. The bank promises to pay you back on demand, but that promise only works if you never actually demand it.
This is the foundation of fractional banking. For decades, banks were required to hold a percentage of deposits in reserve as a safety buffer. The 2008 financial crisis revealed the system’s vulnerabilities, and policies began to shift. As of March 2020, reserve
requirements in the United States were set to zero. The entire system now runs on one thing: confidence.
Banks borrow short and lend long. They take your deposits, which are payable on demand, and loan them out into 30year mortgages and multi-year business loans. This duration mismatch only works if most depositors keep their money in place. It only works if leaving is hard. It depends entirely on lack of choice.
Stablecoins just introduced that choice.
A stablecoin is a digital token pegged one-to-one with the dollar, typically backed by cash and short-term government securities. But its real power has nothing to do with crypto speculation or blockchain hype. Its power is structural.
Stablecoins unbundle three functions that banks have monopolised for over a century: custody, payments, and settlement.
Banks force you into a package deal. To make payments, you must store funds with them. To store funds, you must settle transactions within their system. You can’t have one without the others. Stablecoins sever that bundle, and once you understand the implications, you realise why banks are genuinely afraid.
Take an e-commerce business owner who frequently pays international suppliers. Traditionally, they’re tied to bank hours and high transfer fees, and payments can take days to clear. With stablecoins, those same transactions execute in minutes at any time, with significantly reduced costs. That flexibility transforms daily operations and directly impacts the bottom line - savings that can be reinvested back into the business instead of going to banking fees.
With a traditional bank account, you hold an IOU while the bank holds the actual money. They set the rules. They control access. They can freeze your account, limit withdrawals, or impose fees whenever they want. You’re a creditor hoping your debtor remains solvent.
With a stablecoin in a selfcustodied wallet, you control the private keys. It’s the digital equivalent of holding cash in your hand. No one can freeze it. No one can limit your access. No one needs to remain solvent for your money to be yours. You own it directly rather than relying on an institution’s promises.
When you’re a creditor, you’re exposed to counterparty risk. When SVB failed, depositors above the FDIC insurance limit faced potential losses not because they made bad investment decisions, but because they trusted an institution that made bad decisions for them. Selfcustody eliminates that risk entirely.
Bank transfers are slow by design. ACH transfers take days. Wire transfers only work during business hours. International transfers can take a week and

incur significant fees. The technology isn’t difficult - banks just benefit from controlling the speed and access to your money.
Stablecoin payments operate 24/7, globally, settling in minutes for pennies. Not a faster messaging system between banks - it’s the direct transfer of a digital bearer asset. The middleman doesn’t just become more efficient. The middleman disappears.
Sending $10,000 using ACH transfers incurs fees of around $30 and takes several days to settle. Using USDC
on the Ethereum network costs a few dollars in gas fees and settles in minutes. The contrast in speed and cost demonstrates the fundamental advantage stablecoins have over traditional banking rails.
If you need to send $10,000 internationally using traditional banking, you’re looking at multiple business days, conversion fees, wire fees, and potential holds for review. The same transaction with stablecoins settles in minutes with minimal fees, regardless of borders or banking hours.
The toll booth just vanished.

Here’s where banks face an existential problem. In the traditional system, settlement happens inside bank ledgers. When you transfer money from Chase to Bank of America, the actual dollars don’t move. The banks just adjust numbers on their respective balance sheets. Money moves between institutions, but it never leaves the banking system itself.
That’s how the funding pool survives. As long as deposits stay within the banking system, even if they move between
banks, they remain available to support the fractional lending model. One bank’s outflow is another bank’s inflow. The total funding remains constant.
Stablecoins break that loop. When a stablecoin transaction settles on a public blockchain, value exits the banking system entirely. The funding doesn’t transfer to another bank. It simply evaporates from the banking system’s perspective.
Picture a bank with $100 billion in deposits. If depositors move just 10% - $10 billion - into stablecoins for better control and faster payments, that funding is gone. The bank can’t lend it anymore. They must shrink their loan portfolio. Funding costs rise. Credit tightens.
At scale, the entire credit engine stalls.
Banks operate on thin margins and high leverage. Their business model depends on having access to cheap, stable funding that they can lend out at higher rates. Deposits are the cheapest funding source they have.
The average bank pays essentially nothing on most checking accounts and minimal interest on savings accounts. They then lend that money out at mortgage rates of 6-7%, auto
loan rates of 5-10%, and credit card rates that can exceed 20%. The spread is where they make a profit.
But if deposits start leaving for stablecoins that offer better custody, faster payments, and complete control, that cheap funding disappears. Banks would need to raise interest rates on deposits to compete or find more expensive funding sources, such as institutional borrowing. Either way, their margins compress.
Some banks can adapt. Many cannot. And the system as a whole becomes fundamentally less stable when the base layer of funding - consumer deposits - is no longer captive.
The system understands this threat perfectly. Banks are responding on two fronts: imitation and regulation.
On the imitation front, major banks are racing to create “tokenised deposits”blockchain-styled IOUs that mimic some stablecoin features while keeping settlement trapped inside bank balance sheets. JPMorgan’s JPM Coin and similar projects let corporate clients move money faster, but the funds never actually leave the banking system. It’s a controlled experiment in efficiency, not genuine decentralisation.
On the regulatory front, new stablecoin frameworks explicitly restrict issuers from paying interest directly to holders. Mechanically, this limits competition with bank deposits. The stated reason is consumer protection and financial stability, but the practical effect is protecting bank funding sources from market competition.
There’s also a new fragility emerging. Stablecoin reserves are currently concentrated in a relatively small number of banks. Circle keeps USDC reserves at institutions like BNY Mellon and Silvergate. A 20% spike in USDC redemptions would dramatically pressure these banks, potentially triggering a liquidity crunch. Such a sharp and sudden increase could set off a compressed bank run at these reserve banks, faster and more severe than anything seen in traditional banking.
The system is adapting, but defensively. The goal isn’t to compete on merit. The goal is to preserve the monopoly on custody, payments, and settlement while offering just enough token innovation to slow the exodus.
If you hold significant money in bank accounts, you should understand what you’re actually holding: unsecured debt from a leveraged institution, not money itself. That debt is

generally safe thanks to FDIC insurance up to $250,000, but beyond that limit, you’re exposed to the same counterparty risk that wiped out SVB depositors above the insurance cap.
Stablecoins offer an alternative that removes counterparty risk if held in self-custody. You trade the complexity of managing your own private keys for the elimination of institutional risk. That trade-off makes sense for some people and not others, depending on technical comfort and the amount of capital involved.
For payments, especially international or after-hours transactions, stablecoins already offer superior infrastructure. Faster, cheaper, available 24/7. The only question is whether the user experience and regulatory clarity have reached the point where mainstream adoption makes sense for your specific needs.
Banking as we’ve known it for the past century is facing
its first genuine structural threat. Not from other banks, not from fintech apps that still settle through traditional rails, but from an entirely different architecture that makes banks optional rather than essential. Within the next few years, stablecoin adoption could escalate to levels that substantially reduce the traditional bank’s role in financial transactions. The momentum is building faster than most people realise.
For over a century, banking worked because there was no alternative. Your money was trapped in a permissioned system, making fractional lending possible. Stablecoins expose that dependency by offering an exit.
How fast does this shift happen? What breaks along the way? Those are the open questions. Banks fear settlement happening outside their walls - and that fear is completely rational.
The exodus has already begun.


For two years, the Federal Reserve tried to kill stablecoins without passing a single law. Banking access disappeared overnight. Crypto-friendly banks were shut down. Master accounts were denied. No hearings, no transparent regulations. Just quiet pressure and clear consequences.
Operation Chokepoint 2.0, they called it. And for a while, it worked. Stablecoin innovation fled offshore. Tether operated
Robert Stone @StoneOnChain

from the Bahamas. Circle expanded to Singapore. US companies couldn’t open basic bank accounts.
Then the numbers made denial impossible. The stablecoin market cap hit $311 billion by January 2026. Transaction volumes reached $33 trillion in 2025 — a 72% increase — approaching half of Visa’s annual throughput. Trump signed an executive order ending Operation Chokepoint 2.0 on August 7, 2025.
If you think the war is over, you’re not paying attention. Regulators didn’t lose. They pivoted. Banking access denial failed, so now they’re capturing stablecoins through legislation that looks like legitimisation but functions as control.
The GENIUS Act became law on July 18, 2025. Celebrated as the first comprehensive federal framework for stablecoins. Regulatory clarity at last. What almost nobody noticed: buried in that
framework is a prohibition on stablecoin issuers paying interest to holders. That single provision does what Operation Chokepoint couldn’t. It prevents stablecoins from competing with bank deposits on the most important dimension. This is not victory. This is sophisticated capture. And it is more dangerous than the crude suppression that came before it.
Operation Chokepoint
2.0 followed the Obamaera playbook under Biden, targeting crypto companies and stablecoin issuers from 2022 onwards. The FDIC issued “pause letters” to 24 institutions through 2024, ordering them to cease crypto services pending approval that never came. Most banks exited rather than fight.
Coinbase’s Chief Legal Officer Paul Grewal later testified these
letters served as de facto “do not bank crypto” orders.
The banks that genuinely wanted to serve the industry paid the price. Silvergate, Signature, and Silicon Valley Bank all collapsed or were shut down within a single week in March 2023. Silvergate liquidated under regulatory pressure. SVB failed through classic bank run dynamics. Signature was different — solvent, well-capitalised, capable of surviving with standard FDIC intervention. Regulators closed it anyway. Former FDIC Chair Sheila Bair confirmed in Congressional testimony that Signature was shut down to “send a message” to crypto banks.
Meanwhile, Custodia Bank spent three years trying to get a Federal Reserve master account, which would have allowed stablecoin issuers to hold reserves directly at the
central bank. The Fed denied the application in January 2023. Direct Fed access remains impossible. Commercial banks remain the gatekeepers.
No law explicitly prohibited stablecoins. The regulatory maze was just deliberately lethal. The SEC claimed they were securities. The CFTC claimed commodity jurisdiction. State regulators split further. The result: offshore issuers like Tether and Circle served US customers while US-based innovation stalled entirely.
By late 2022, stablecoins crossed a threshold regulators could no longer ignore. Market cap exceeded $150 billion. Daily transaction volume rivalled major payment networks. People were using them for actual payments and savings — direct substitutes for bank deposits. When deposits move from banks

to stablecoins, funding leaves the banking system. Banks can’t lend against it. The fractional reserve model breaks down.
By January 2026, stablecoin market cap had more than doubled to $311 billion. The chokepoint tactics failed to stop adoption. They just pushed it offshore.
Trump ended Operation Chokepoint 2.0 on August 7, 2025, signing the executive order “Guaranteeing Fair Banking for All Americans.” The OCC issued updated
guidance the same day, telling banks they could serve crypto companies using their own risk assessment. Four months earlier, he had signed the GENIUS Act. The Senate passed it 68-30. The House passed it 308-122. Bipartisan support. Regulatory clarity. Industry legitimisation.
Here’s what that actually means.
The framework requires stablecoin issuers to maintain 100% reserves in liquid assets, make monthly public
disclosures, comply with Bank Secrecy Act and anti-money laundering requirements, possess technical capability to freeze or seize tokens when legally required, and meet bank-level capital requirements. That sounds reasonable. Transparency, consumer protection, financial stability.
Buried in Section 4: stablecoin issuers are prohibited from paying interest to holders.
Traditional banks pay minimal interest on deposits — their cheapest funding source. They lend those deposits at much higher rates: mortgages at

6-7%, credit cards at 20%plus, profiting from the spread. Stablecoins backed by Treasury bills earning 4-5% could theoretically pass that yield to holders, offering better returns than bank deposits at the same level of safety. The GENIUS Act makes that illegal.
Stablecoins can be faster than ACH. They operate 24/7. They settle globally in minutes. But they cannot compete with bank deposits on yield. That competitive advantage is prohibited by law. This is not consumer protection. This is competitive protection for traditional banking dressed as prudential regulation.
The Custodia precedent also stands. Stablecoin issuers still cannot hold reserves directly at the Federal Reserve. They must use commercial banks as intermediaries. Commercial banks remain the gatekeepers, and they can still decline to serve them. Meanwhile, the dual federal-state regulatory structure creates compliance complexity that favours large, well-capitalised incumbents over startups and new entrants.
The Federal Reserve continues work on a central bank digital currency. Trump signed an executive order in January 2025 prohibiting federal agencies from establishing CBDCs without Congressional authorisation. That doesn’t stop the research.

If a Fed digital dollar eventually launches with Congressional approval, the GENIUS Act has already done the groundwork. Private stablecoins will be boxed into a structure that prevents them from competing. A Fed digital dollar would combine stablecoin efficiency with direct government control, zero threat to commercial bank funding, and the ability to pay interest directly from the central bank. Private stablecoins would be prohibited from matching those features by the very legislation that legitimised them.
The interest prohibition is the tell. It makes no sense as consumer protection. It
makes perfect sense as prepositioning.
Tether. The offshore giant nobody in US regulatory circles wanted to win. Now sitting on $187 billion in market cap, processing $13.3 trillion in annual transactions, operating from the Bahamas largely beyond US regulatory reach. The assault on domestic stablecoins handed dominance to the one player least subject to US control. Tether isn’t bound by GENIUS Act interest prohibitions. It operates under Bahamian law. And it continues serving as the world’s de facto digital

dollar while US regulators congratulate themselves on the GENIUS Act.
Circle maintained operations through international expansion, entering under foreign regulatory frameworks before seeking full US authorisation. USDC processed $18.3 trillion in transactions during 2025, more than Tether despite smaller market cap, driven by institutional use and DeFi integration. New US-based issuers like PayPal’s PYUSD are entering the market, but into a landscape shaped by rules that protect incumbent banks. The barriers haven’t disappeared. They’ve shifted from crude denial to complex compliance.
Operation Chokepoint 2.0 failed. Denial of banking access didn’t stop stablecoin adoption. It accelerated it by creating an adversarial narrative that rallied the industry and drove innovation to friendlier jurisdictions.
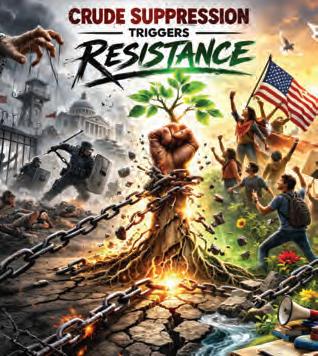
But regulators didn’t lose. They got smarter.
Crude suppression triggers resistance. Sophisticated capture looks like legitimisation. One generates headlines and lawsuits. The other gets celebrated as progress. The GENIUS Act legitimises stablecoins while preserving the advantages of the banking system. It provides clarity while removing competitive threats. It enables innovation within boundaries that protect incumbents. Textbook regulatory capture: use the power to authorise and regulate to shape markets in ways that protect established players while claiming to enable competition.
Crypto advocates celebrating the GENIUS Act as a victory might want to read what they’re celebrating. The interest prohibition alone does more to protect bank deposits than three years of Operation Chokepoint ever did. And it is permanent, codified in law, far harder to fight than informal regulatory pressure that could be reversed by executive order.
The chokepoint was obvious. The capture is subtle. And subtle control proves more effective than crude suppression. Regulators don’t need to ban stablecoins. They just need to ensure stablecoins can’t actually replace bank deposits.
Mission accomplished.


From $125,000 to $60,000:

From Bitcoin’s $125,000 peak to historic extreme fear, panic selling, and the lessons only experience can teach.
If you’re new to crypto, the last few months probably felt less like a market correction and more like the end of the world.
In July 2025, Bitcoin reached
Milkshake Matty @MilkshakemattyX

a peak of around $125,000. Optimism was everywhere. Headlines were euphoric, timelines were full of victory laps, and price predictions assumed the only remaining question was how high — not
whether — markets would go.
By February 2026, Bitcoin was trading near $60,000. For newcomers, this wasn’t just a pullback. It was their first real crypto shock.
And judging by the sheer panic across social media, many people had no idea what they were actually experiencing.
As prices fell, sentiment shifted rapidly. Confident voices disappeared. Chart analysis gave way to emotional reactions. Influencers who had been bullish at the highs either went silent or suddenly turned bearish.
Retail investors flooded comment sections asking the same question:
“Is crypto dead?”
Some panic sold near the bottom. Others exited crypto entirely, convinced they had narrowly escaped a financial disaster. Even those who stayed felt uneasy — checking prices constantly, questioning their decisions, and bracing for further downside.
This wasn’t just fear. It was emotional overload on a massive scale.
The mistake most new investors made wasn’t buying crypto. It was entering the market without context — without understanding how violently and routinely these markets can move.
Here’s the uncomfortable truth for new participants:
Nothing unusual happened.
Crypto markets are volatile by design. Large drawdowns are not exceptions — they are a feature. They occur in bull markets, bear markets, and every transitional phase in between.
A 50–60% decline feels catastrophic if it’s your first experience. If you’ve lived through multiple cycles, it feels uncomfortable — but familiar.

This is why experience matters so much in crypto. You don’t truly understand volatility until you’ve lived through it.
Seasoned investors aren’t calm because they don’t care. They’re calm because they’ve seen this exact pattern before — often more than once.
What made this correction especially intense wasn’t just price action, but the psychological environment surrounding it.
Between December and January, the Crypto Fear & Greed Index spent more consecutive days in fear and extreme fear than at any point since records began. Sentiment remained relentlessly negative. Every rally attempt was sold. Every negative headline reinforced the belief that worse was still to come.
Then, in February, something remarkable happened.
The index dropped to a reading of 5 — the lowest extreme fear reading since the index was created.
At that point, fear was no longer abstract. It was real, widespread, and deeply emotional. Investors weren’t just worried about price — they were worried they had fundamentally misunderstood crypto altogether.

Ironically, history shows that these moments of maximum fear often appear near market turning points.
One of crypto’s biggest hidden risks isn’t volatility — it’s isolation.
Crypto can be an incredibly lonely space, particularly for newcomers. Unless you’re fortunate enough to have close friends who understand markets, most people experience downturns alone, guided only by social media sentiment and their own internal dialogue.
That’s dangerous.
When fear dominates your information sources, rational thinking disappears. In those moments, people don’t need more price predictions — they need balance. They need context. They need someone
to remind them that panic is rarely a good decision-making environment.
Most people don’t leave crypto because the technology failed or the thesis collapsed. They leave because they couldn’t emotionally handle their first major drawdown.
There’s a phrase often used in trading circles: you need miles on the clock.
“Most people don’t leave crypto because the technology failed. They leave because they couldn’t emotionally handle their first major drawdown.”
You can study charts, learn indicators, and watch educational videos, but nothing replaces lived experience. Once you’ve survived your first crash, the second feels different. By the third, fear loses much of its power.
That doesn’t mean emotion disappears — it means emotion stops controlling decisions.
This is the difference between reacting to markets and navigating them.

Markets don’t just test strategy — they test psychology.
That’s why community matters far more than most people realise. A tribe provides perspective when thoughts spiral. It offers balance when social media becomes overwhelming. It reminds you that fear is often loudest when opportunity is quietly forming.
Most importantly, it reminds you that you’re not alone.
This is why I created the Crypto Wolf Pack — not as a signalchasing group, but as a place where people can learn, talk through uncertainty, and stay grounded when emotions run high.
It’s also why I co-host The UK Crypto Podcast — to slow the noise down and create space for context, discussion, and long-term thinking in a market that often rewards impulsive behaviour.
If you’re new to crypto and lived through the drop from $125,000 to $60,000, you’ve gained something valuable.
Perspective.
You now understand what real volatility feels like. You’ve seen
how fast sentiment can flip. You’ve experienced fear in its rawest form — and you’ve seen that the world doesn’t end when prices fall.
Some people will never return. Others will come back wiser, calmer, and better prepared.
Crypto doesn’t reward prediction. It rewards patience.
And for those who stayed, learned, and didn’t let fear write the ending — welcome to your second cycle.
I’ve been involved in crypto since 2013.
I’ve lived it, breathed it, made the mistakes, and experienced the wins. I’ve seen euphoric tops, brutal crashes, and long periods where crypto was written off entirely — only for the cycle to repeat when most people least expected it.
If you want to learn more in a calm, balanced environment,

you can find me on The UK Crypto Podcast. It’s 100% free, with new episodes released every Friday.
And if you’re ready for a paid community where you’re not navigating these moments alone, you can join Crypto Wolf Pack and use the promo code CRYPTOMAG for 50% off your first month.
The strength of the wolf is in the pack.

Milkshake Matty has been active in cryptocurrency markets since 2013, navigating multiple full market cycles and their extremes. He cohosts The UK Crypto Podcast, available on YouTube and Spotify (ukcryptopodcast.co.uk), and runs the Crypto Wolf Pack community (cryptowolfpack. co.uk), focused on perspective, education, and disciplined investing in volatile markets.
Adele Adele60370277


There’s something slightly surreal about watching a seven-year-old walk onto a golf course with the quiet certainty of someone who’s ready to compete. Not participate. Compete.
Shane ‘The Showman’ Cooper is small in stature, as you might expect. But the moment he stands over the ball, his age and diminutive size become irrelevant. There’s a stillness...a focus. A refusal to rush.
And then he delivers.
Crypto Magazine and Fusion Token - you’ll know us as FUST - are very proud to announce our sponsorship of one of the most remarkable young athletes in British sport.
By now, most people in junior golf circles know the headline facts. And the facts tell a story.
An adult handicap at four years old.
The youngest ever County
Gold winner in the Under-10 category before his 6th birthday.
Two-time Order of Merit Champion and holder of 2 major’s titles - British Juniors Masters Champion at age 5 and British Juniors players champion at age 6
Winner of the under-10s skills test, Kent final
Ranked number one in the UK in his age group at five and again at six.
European Champion last year
US Winter Tour Champion across eight events in his first season competing as a 7-year-old.

It’s about more than that, though, because achievements alone don’t explain why people stop in their tracks to watch this extraordinary new talent.
What sets Shane apart is this: in almost every tournament he plays, he’s the youngest. Often the smallest. Regularly at a physical disadvantage. And he embraces it.
“I’m used to being the underdog,” he says, in his matter-of-fact seven-yearold way. “That makes me try harder.”
There’s no bravado in it. No theatrics, just acceptance and resolve.
That mindset is why we’re here.
At first glance, golf and crypto appear to move in different circles. One feels traditional
and measured. The other is volatile and fast-paced.
But look closer, and they share something essential: long-term thinking.
In golf, you don’t chase a bad shot with panic. You reset. You commit to the next swing.
In crypto, the same principle applies.
The most successful participants in either arena understand timing, resilience and emotional control. They understand that sustainable growth rarely looks dramatic day-to-day.
Shane, at seven, already demonstrates that temperament. He competes against older players without intimidation. He absorbs setbacks and keeps his focus, returning to practice with quiet determination.
That alignment resonates with us. We operate in an industry that is often misunderstood. Sometimes judged by its loudest and most brutal moments rather than its steadfast most disciplined builders.
Supporting an athlete who embodies composure, longterm thinking and structured ambition is a natural extension of the qualities we value, and that’s why we’ve chosen to be on Shane’s team. Not because he’s seven and it’s novel, but because at seven, he knows exactly what he wants, and he already understands the long game.
Athlete sponsorship, when done well, is not transactional - it’s symbiotic.
Young athletes need infrastructure: travel, equipment, tournament access, media production and stability. Brands need authenticity - real stories, real effort, real progression. The most powerful partnerships are built not around instant fame, but around shared trajectory.
Shane’s journey is just beginning. His social presence is growing rapidly, with hundreds of thousands of monthly engagements across platforms, and tournament coverage is increasingly filmed and broadcast. As his competitive stages expand, so does his audience.

For us, that visibility takes us beyond Web3. Golf reaches families, professionals, and multi-generational communities. It travels globally, and it commands respect. As an established and trusted voice in this new era of regulated crypto reaching the masses, we’re excited to connect with people who may not yet know us.
More importantly, this collaboration allows us to support someone whose approach mirrors the values we champion, by backing potential at the right time; responsibly, thoughtfully, and for the long term.
Shane recently competed in the Daily Mail World Junior Championships in Marbellaon the same course that hosts the Spanish Open - and was philosophical when it didn’t go his way. That’s perhaps the hardest lesson of all for an ambitious youngster who’s used to winning, but absorbing those lessons and taking defeat on the chin is where champions learn
resilience, and he’s already figuring out how to draw out the learning and move on
As the year progresses, he’ll join the Faldo Series and continue on the British Junior Golf Tour. He recently qualified as the number one junior golfer at his club for the Race to Woodhall Spa regional finals, a pathway that could see him compete against the best 24 juniors in the country, many of whom are twice his age.
And then there’s the dream.
Shane is single-minded in his determination to become the youngest player ever to qualify for The Open Championship at St Andrews - a record that’s been held for the last 161 years by a player known as ‘Young’ Tom Morris. He first played in the tournament in 1865 at just 14 years and 147 days old.
Ambitious? Audacious? Maybe. But ambition is healthy when it’s grounded in work ethic.
And here’s the thing - he’s still, first and foremost, a boy who loves golf. He studies his shots and handles pressure with the

kind of composure that often surprises seasoned spectators, but he also laughs between holes. Sometimes chips in a happy dance when he lands a tricky putt, and at seven, joy must remain central.
That balance is critical because talent can only flourish when protected. With Dad as both his caddy and his biggest supporter, there’s a constant, familiar presence beside him, keeping perspective where it belongs.
It’s easy to get caught up in how unusual it is for a sevenyear-old to be achieving this much. 46 pieces of hardware across his first two years in competition is no small achievement, but if you strip away his age for a moment, he’s simply a talented young athlete who refuses to see ‘young’ as a limitation.
That’s worth backing. And as his sponsor, our place in that circle is simple - to provide stability, create opportunity, and respect the pace of his development.
We are proud to welcome Shane “The Showman” Cooper into the Crypto Magazine and FUST family. If there’s one thing both golf and crypto have taught us, it’s that the long game is where legacy is built.
And at seven years old, he has time on his side.

How nation-states are positioning themselves in the race to dominate dollarbacked digital currencies, and what happens when monetary policy becomes a technological arms race
On March 25, 2025, World Liberty Financial — a decentralized finance venture backed by President Donald Trump and his family — launched a dollar-pegged stablecoin called USD1. Within a year, it surpassed $3.4 billion in circulating supply, faster than any stablecoin in history. The company applied for a national banking charter. A UAE sovereign wealth figure quietly acquired a 49% stake. Pakistan signed an agreement to explore using USD1 for cross-border payments. Regulatory agencies scrambled
Robert Stone @StoneOnChain

to determine jurisdiction.
The SEC claimed securities oversight. The CFTC asserted commodities authority. The Treasury Department suggested both were wrong.
Nobody could stop it.
USD1 represents something more significant than political theatre or presidential branding. It demonstrates a fundamental shift in monetary power that governments are only beginning to comprehend. For the first time in modern history, the ability to issue dollar-denominated
instruments at scale has migrated outside state control. Not through revolution or legislative change, but through code that executes regardless of regulatory approval.
Traditional monetary sovereignty operated through simple mechanisms. Governments controlled printing presses, regulated banking institutions, and enforced legal tender laws. Money moved through supervised channels. The system worked because the state controlled the infrastructure.

Stablecoins demolish that architecture.
A sixteen-year-old in Lagos can now hold dollar-denominated value, transfer it globally in seconds, and bypass every financial institution in both Nigeria and the United States. No bank account required. No permission needed. No government can prevent a transaction unless it shuts down the entire internet. The regulatory perimeter that once contained monetary policy has simply evaporated.
The stablecoin market now exceeds $310 billion. Tether’s USDT commands roughly $187 billion. Circle’s USDC holds approximately $75 billion. Transaction volumes hit $33 trillion in 2025 — a 72% increase year-over-year — approaching half of Visa’s annual throughput. Standard Chartered projects the market will reach $2 trillion by 2028. When citizens of emerging markets abandon local currencies for USDT, it proves that monetary policy
increasingly resides in smart contracts rather than legislative chambers.
The war over stablecoins comes down to a single question: which entities will control money in a world where code enforces monetary rules more effectively than governments.
Tether processes over $20 billion in daily trading volume and facilitated $13.3 trillion in transactions during 2025, yet operates with fewer than 100 employees and faces none of the regulatory requirements imposed on traditional payment processors. No banking licence. No Federal Reserve oversight. No capital requirements beyond the reserves backing each token.
Circle presents a different model. The company maintains Federal Reserve accounts, submits to regular attestations, and positions itself as the regulated stablecoin. USDC
processed $18.3 trillion in transactions during 2025 — more than Tether despite smaller market cap — driven by institutional use and DeFi integration. Major financial institutions prefer USDC precisely because it resembles traditional finance enough to satisfy risk committees while delivering cryptocurrency’s technical advantages.
Dollar-backed stablecoins matter more than any other cryptocurrency innovation because they solve the volatility problem that prevented crypto from functioning as actual money. Bitcoin’s price fluctuations make it unsuitable for everyday commerce. Stablecoins deliver cryptocurrency’s technical capabilities without the speculative chaos. The paradox is that private companies now issue dollar-denominated instruments at scale without any of the licensing, oversight, or capital requirements imposed on banks — effectively operating shadow banking systems answerable to no central authority.
The United States faces an impossible choice. Every time a Filipino nurse sends USDT home to Manila, American monetary influence extends another node deeper into global commerce. Stablecoins have accomplished what decades of

World Bank programmes and trade agreements could not: making the world voluntarily choose dollars.
Washington should be celebrating. Instead, it panics. Regulate too aggressively and stablecoin issuers relocate to friendlier jurisdictions, taking dollar dominance with them. Regulate too loosely and you legitimise a monetary system operating outside state control. The GENIUS Act, signed into law in July 2025, attempts to split this difference — legitimising stablecoins while constraining their competitive threat to traditional banking.
Europe pursues clarity through brute force regulation. The
Markets in Crypto-Assets framework demands licensing, reserve requirements, and ongoing supervision for any stablecoin operating within EU jurisdiction. The actual motivation is transparently geopolitical: if European citizens hold dollar stablecoins, they participate in American monetary policy regardless of what the European Central Bank decides. MiCA attempts to reverse this by favouring euro stablecoins and making compliance expensive enough that only large supervised institutions can compete. The result so far: euro-pegged stablecoins sit at roughly $500 million in market cap. The dollar rails are already built. Network effects compound daily.
China abandoned pretence entirely. The digital yuan is not competing with stablecoins. It is replacing the concept of private money with programmable state control. Beijing recognised what Western governments still deny: whoever controls payment infrastructure controls economic behaviour. The digital yuan’s architecture enables capabilities no private currency can match — programmable expiration dates on stimulus payments, restrictions on capital flight by disabling international transfers, and the potential to integrate with existing government enforcement systems. Whether Beijing fully deploys these capabilities is a political question. That the
infrastructure permits them is a technical fact.
The most revealing dynamic plays out in countries where governments have already lost monetary credibility. Argentina, Venezuela, Turkey, Nigeria. With inflation exceeding 140% annually, Argentine citizens hold savings in USDT, conduct business in stablecoins, and bypass banks entirely. Capital controls become meaningless when value transfers through networks that ignore borders.
Governments operate under a fundamental misconception. They believe stablecoins are companies that can be regulated like banks.
A bank is an institution. It occupies physical space. Regulators can visit premises,
examine records, issue orders, and ultimately close it if compliance fails. A stablecoin protocol is code executing across distributed networks. USDT transactions occur on Ethereum, Tron, and half a dozen other blockchains simultaneously. American regulators can sanction Tether Limited, but they cannot stop USDT transactions unless they shut down every blockchain network where the token exists. Smart contracts execute based on cryptographic rules, not legal compliance. You can arrest executives, freeze corporate accounts, and issue ceaseand-desist orders. The code keeps running.
Circle understood this dynamic, which explains their compliance strategy. By maintaining Federal Reserve accounts and submitting to attestations,
Circle makes itself vulnerable to state power in exchange for institutional legitimacy. Tether chose the opposite path — minimising touchpoints with traditional finance and prioritising censorship resistance over compliance theatre. Both strategies succeed because they recognise what the technology actually permits rather than what regulators prefer.
The cypherpunks who built cryptocurrency infrastructure intended to create money beyond state control. They succeeded in creating the most effective mechanism for spreading American monetary dominance ever devised.
Bitcoin emerged from libertarian dreams of escaping

central bank manipulation. Then stablecoins arrived and immediately anchored themselves to the US dollar, transforming revolutionary technology into imperialism’s most efficient distribution mechanism. Traditional dollar hegemony required extensive institutional frameworks: IMF structural adjustment programmes, trade agreements mandating dollar settlement, correspondent banking relationships. This infrastructure took decades to build. Stablecoins require none of it.
The network effects compound naturally. Exchanges quote crypto prices in USDT. DeFi protocols integrate USDC. Businesses accept stablecoins. None of this requires policy coordination. Market participants choose dollars because everyone else already

did. American monetary influence extends deeper into global commerce than any previous era, while the Federal Reserve exercises less direct control than ever.
This should concern American strategists more than excite them. Dollar hegemony without accompanying political

leverage means nations access American monetary benefits while ignoring American policy preferences. China can restrict USD banking while its citizens hold USDT reserves. Russia can face sanctions while oligarchs maintain dollar wealth in stablecoins.
The cypherpunks wanted to escape central bank control. They built technology that made central bank currency more dominant than ever, while making central banks less relevant than ever.
The sovereignty wars will not produce winners. They will produce fragmentation.
No global stablecoin framework emerges because competing national interests make coordination impossible. The United States will not surrender dollar dominance to
achieve regulatory harmony. China will not abandon surveillance capabilities for interoperability. Europe will not accept permanent secondary status for euro alternatives. The result is multiple incompatible monetary regimes operating simultaneously — dollar stablecoins dominating where American influence holds or local currency failure makes alternatives attractive, the digital yuan operating within Chinese economic zones, euro stablecoins achieving modest adoption where regulatory compliance becomes a market entry requirement.
American policymakers wanted control without
The cypherpunks wanted to escape central bank control. They built technology that made central bank currency more dominant than ever, while making central banks less relevant than ever.
losing dollar dominance. They get dollar dominance without meaningful control. European regulators wanted a euro resurrection through legislative mandate. They get compliance burden driving innovation elsewhere. Chinese authorities wanted
surveillance capitalism merged with state power. They get that, but only within borders they already controlled. Cypherpunks wanted money beyond government reach. They built infrastructure that governments now weaponise against each other.
Monetary policy now lives in code rather than legislative chambers. The algorithms don’t care who writes them. The protocols don’t ask permission. And the democratic input that once shaped monetary decisions affecting billions has been quietly compiled out of the programme.
Nobody voted for this. The code shipped anyway.

Decentralised finance promised to eliminate intermediaries. Now the intermediaries own the protocols. This was always how it would end.

Robert Stone @StoneOnChain

On February 11, 2026, Uniswap — the decentralised exchange built to eliminate financial intermediaries — announced that BlackRock’s $2.85 billion tokenised Treasury fund would trade on its platform. BlackRock also made a strategic investment in the Uniswap ecosystem, purchasing an undisclosed amount of UNI governance tokens. The
protocol’s token surged 30% on the news.
Uniswap launched in 2018 to enable permissionless, peer-to-peer trading without middlemen. BlackRock is the world’s largest asset manager, controlling over $10 trillion. One was built to replace the other. Now one owns a piece of the other, and the market celebrated.
Nobody mentioned the irony.
DeFi emerged specifically to eliminate institutions like BlackRock from financial intermediation. The entire premise was that smart contracts could replace asset managers, brokers, and banks. Code would execute trustlessly. Intermediaries would become obsolete. Finance would be permissionless.
Now the intermediaries own the infrastructure.
BlackRock’s BUIDL fund operates across eight blockchains but functions like every other institutional product. Access requires accreditation verification and a $5 million minimum investment. Transactions require compliance approval. Smart contracts enforce regulations, not permissionless access. Blockchain provides efficiency improvements whilst preserving institutional control over who participates and under what conditions. Decentralisation became a feature of the ledger, not the power structure.
This is institutional capture completed. Not through hostile takeover but through gradual absorption. DeFi protocols now serve the same institutions they were designed to replace. The revolution succeeded in building better infrastructure for establishment finance. It failed to democratise access or eliminate intermediaries.
The pattern is familiar to anyone who watched the internet evolve. Email was supposed to decentralise communication. Now Google and Microsoft control most inboxes. The web was supposed to enable peer-topeer publishing. Now traffic concentrates on a handful of platforms. DeFi joins this list of revolutionary technologies that

changed everything about how systems operate and nothing about who controls them.
Decentralised finance launched with explicit vision. Protocols like Uniswap, Compound, and Aave would eliminate centralised exchanges, banks, and brokers. Anyone with internet access could trade assets, borrow funds, and earn yields. No intermediaries required. No permission needed. Early implementations delivered on these promises. Liquidity providers earned fees without exchanges taking cuts. Borrowers accessed capital without bank approval. The system worked permissionlessly, exactly as designed.
Then institutional money arrived.
Venture capital poured billions into DeFi protocols during 2020-2021. VCs wanted regulated products
targeting institutional clients, governance rights over protocol development, and returns justifying their valuations — not permissionless protocols serving anonymous users. Protocol teams faced a clear choice: maintain permissionless access and remain niche experiments, or build compliance infrastructure and access institutional capital. Most chose institutional capital. The decision was rational. Regulatory pressure was increasing. Operating costs required revenue. Idealism doesn’t pay server bills.
Compliance requirements transformed protocol architecture. KYC verification became mandatory for certain features. Geographic restrictions blocked users from sanctioned jurisdictions. Smart contracts evolved from executing code regardless of identity to enforcing regulatory compliance as their primary function. Permissionless became marketing rhetoric rather than technical reality.
Regulatory pressure accelerated everything. The SEC argued governance tokens were unregistered securities. FinCEN claimed protocols were unlicensed money transmitters. The CFTC asserted jurisdiction over derivatives protocols. Teams responded by building separate institutional offerings. Compound Treasury served accredited investors. Uniswap removed specific tokens from its frontend. Aave developed KYC-gated institutional product lines.
This created a two-tier system. Retail users accessed permissionless protocols through increasingly restricted interfaces. Institutional participants used compliant versions with regulatory approval. The blockchain technically remained open. Practical access diverged dramatically based on capital and institutional status.
Institutional capital overwhelmed retail participation through simple mathematics. Retail users provided millions in liquidity. Institutions deployed billions. When BlackRock or Fidelity entered a protocol, their capital dwarfed existing liquidity pools, giving them de facto control over protocol economics regardless of governance structures.

Governance tokens provided the formal mechanism. VCs negotiated substantial token allocations during funding rounds, granting voting rights over protocol parameters, treasury allocation, and development priorities. Token-based governance was supposed to prevent centralised control. Instead it enabled institutional capture through legal means. Dispersed individuals holding small token amounts could not organise effectively. Institutions holding substantial positions voted cohesively. Governance became democratic theatre while institutions directed outcomes.
Institutional DeFi emerged as a distinct category. Platforms like Fireblocks and Copper provided custody solutions meeting institutional security requirements. Institutions accessed DeFi through intermediaries providing the comfort of traditional finance — walled gardens where they benefited from
blockchain efficiency without permissionless exposure. The same technology that once enabled direct peerto-peer transactions became infrastructure for institutionalonly networks.
No hostile takeover was required. Institutions built compliant parallel infrastructure using the same underlying technology whilst regulatory pressure made permissionless operation increasingly difficult. Capital flowed toward compliant versions. Development resources concentrated on institutional features. Permissionless protocols remained theoretically available whilst becoming practically irrelevant.
Institutional DeFi preserves genuine technical improvements whilst eliminating revolutionary accessibility. Blockchain
settlement is superior to traditional clearing. 24/7 markets beat business hours. Smart contracts reduce operational costs. Public blockchains make transactions visible and treasury movements auditable in ways traditional finance never matched. These efficiency gains matter commercially even when serving traditional hierarchies.
But permissionless access is gone. Censorship resistance disappeared when protocols implemented transaction monitoring and blocking. True disintermediation never happened. The intermediaries did not disappear — they absorbed the technology and continued extracting value through institutional dominance.
Financial inclusion, DeFi’s supposed killer application, remains theoretical. Poor individuals cannot afford gas fees on Ethereum. They lack capital for meaningful participation. They don’t meet accreditation requirements for institutional protocols. BlackRock’s BUIDL fund requires a $5 million minimum investment to access permissionless blockchain infrastructure.
DeFi served speculative traders and now serves institutions. The financially excluded remain excluded. The technology changed. The access didn’t.

The cypherpunks built tools for revolutionary transformation. Email would decentralise communication. The web would democratise publishing. Encryption would protect privacy. Cryptocurrency would separate money from the state. DeFi would eliminate financial intermediaries.
Each technology succeeded technically whilst failing politically. Email works brilliantly — Google and Microsoft control most of it. The web enabled anyone to publish — a handful of corporations captured distribution. DeFi built permissionless finance — institutions own the protocols.
Building better tools does not overcome power structures. It provides those structures with better tools. Revolutionary technologies get absorbed by establishment interests, deployed to serve existing hierarchies, and eventually become infrastructure
reinforcing the very systems they were designed to challenge.
The cypherpunks were right that code could enable new forms of organisation. They were wrong that code alone could overcome political and economic power. Permissionless protocols cannot resist institutional capital. Open systems cannot prevent regulatory capture. Decentralised governance cannot withstand coordinated institutional control.
Money and finance sit too close to state power for technological disruption alone to succeed. The next revolutionary financial technology is probably already being built by idealists who believe they have solved the capture problem. They haven’t. The pattern is not a technical bug requiring a fix. It is a political feature of how power operates in technological systems.
The cypherpunk vision dies not because code failed, but because code was never the thing that needed to change.

While regulators celebrate capturing exchanges, the underground economy processes billions through privacy networks governments cannot see, stop, or even measure
Nobody knows how much Monero moved last year.
That’s not a data gap. It’s the point. Monero’s protocol hides senders, receivers, and amounts by design. Transaction volumes in 2024 and 2025 stabilised at levels significantly higher than the early 2020s, according to TRM Labs, even as every major centralised exchange — Binance, Coinbase, Kraken, OKX — delisted the token under regulatory
Robert Stone @StoneOnChain

pressure. Nearly half of all darknet markets launched in 2025 accept Monero exclusively. The network processes roughly 28,000 transactions per day. The value of those transactions is mathematically unrecoverable.
While Coinbase files regulatory paperwork and Circle submits to Federal Reserve audits, parallel infrastructure processes transactions governments cannot trace,
cannot stop, and increasingly cannot detect. Every other feature in this issue documents a form of institutional capture: banks custody Bitcoin, governments regulate stablecoins, DeFi becomes Wall Street infrastructure, CBDCs turn money into surveillance. This piece documents what that capture missed.
The invisible economy operates openly. Telegram channels with
tens of thousands of members coordinate peer-to-peer trades. Monero crosses borders in volumes that dwarf Western Union corridors. A Belarusian activist exchanges crypto to fund protest flyers. A Lebanese citizen converts savings before the next banking crisis hits. A Venezuelan developer holds earnings in a hardware wallet because the bolivar is worthless and local banks are inaccessible. The tools work exactly as the cypherpunks intended — for anyone who understands how to use them.
The on-ramp through Coinbase, the identity verification, the transparent blockchain where every transaction is permanently public — that’s the surveilled economy. The invisible one operates on different principles.
Monero is the base layer. Every transaction hides the sender, receiver, and amount through mandatory cryptographic protocols. Ring signatures mix transactions with decoys. Stealth addresses ensure recipients can’t be identified. RingCT obscures amounts. The blockchain records that something happened. It reveals nothing about who, what, or how much. Privacy isn’t a feature you enable — it’s mandatory at the protocol level. The information doesn’t exist in recoverable form.
Bitcoin offers conditional privacy for knowledgeable users. CoinJoin protocols coordinate transactions among multiple participants simultaneously, mixing coins so that blockchain analysis firms cannot definitively trace which inputs connect to which outputs. Lightning Network routes payments through offchain channels that never hit
the main blockchain — only channel openings and closings appear on-chain. Not perfect privacy. Functional privacy for those who understand the architecture.
The resilience of these tools is demonstrated by what happens when governments try to kill them. In April 2024, the DOJ arrested the founders
of Samourai Wallet, a privacyenhancing Bitcoin wallet, on charges of money laundering. Authorities seized the infrastructure and removed the app from stores. Five months later, anonymous developers forked the code and released Ashigaru — the same privacy tools rebuilt with a more decentralised architecture. Users run their own nodes. The code lives on Tor servers rather than GitHub. There is no central coordinator to arrest or infrastructure to seize. This is how the invisible economy responds to enforcement: arrest developers; the community forks the code, making it harder to kill next time.
The invisible economy serves overlapping populations with radically different ethics and identical security requirements. The tools don’t distinguish between them. The mathematics works the same for everyone. The people deserve individual attention.
Belarusian activists cannot use banking systems that report directly to Lukashenko’s security services. Opposition media continues running on crypto donations that authorities cannot trace or freeze. Protesters get fed through networks invisible to the state. The alternative is not inconvenience — it’s imprisonment.

Venezuelan software developers earning dollars through remote work cannot access functioning banks. The bolivar has been rendered functionally worthless by hyperinflation. Local banks are inaccessible or frozen. These developers accept payments in stablecoins, hold savings in hardware wallets, and convert them through peer-to-peer networks as needed. The alternative is poverty, regardless of work ethic or skill. Crypto adoption in Venezuela happened not through marketing but because the financial system collapsed and people needed something that actually worked.
Lebanese citizens who moved savings to crypto before capital controls hit protected their wealth. Those who trusted banks watched accounts frozen and balances forcibly converted at ruinous exchange rates. Lebanon’s banking collapse was not theoretical. It destroyed
the middle class. The people who survived it financially were disproportionately those who held assets outside the banking system — in crypto, in cash, in anything the banks couldn’t reach.
Cannabis operators in legal US states cannot access banking because federal prohibition classifies them as money launderers, regardless of state law. Visa won’t process their payments. Banks won’t hold their deposits. Crypto provides payment rails that the regulated system refuses to offer. I’ve operated in this space myself as a commercial grower in southwest Oregon. The banking exclusion is not abstract. It’s an operational reality for thousands of legal businesses.
Sex workers get debanked globally for “reputational risk” regardless of legal status in their jurisdiction. Payment processors cut them off. Banks close accounts without explanation.
Crypto lets them receive payment and store value without institutional permission. Privacy tools aren’t luxury features for these populations. They’re infrastructure for economic survival.
And then there’s straightforwardly illegal commerce. Darknet markets process an estimated $1.5 billion annually in drug transactions. Ransomware operators demand payment in Monero. Sanctions evasion moves money for sanctioned entities through identical privacy tools protecting activists. This piece is not an endorsement of illegal activity. It’s an acknowledgement that the same cryptographic principles serve every user identically — the mathematics doesn’t have a morality filter.
The regulatory frameworks governing crypto in 2026 supervise the visible economy. The GENIUS Act regulates stablecoins. The SEC oversees tokenised securities. Exchanges file suspicious activity reports. This infrastructure captures everything that touches the regulated financial system. It captures nothing that doesn’t.
Political dissidents won’t use regulated stablecoins subject to government reporting. Citizens fleeing collapsing economies
won’t submit to KYC that gives corrupt officials access to their financial activity. People excluded from banking won’t voluntarily re-enter systems that excluded them. Privacypreserving protocols continue operating regardless of what regulatory frameworks require because the protocols don’t have compliance departments. They have mathematics.
Regulators can make crypto harder to access through regulated channels. They have — exchange delistings, banking restrictions, arrests of privacy tool developers. Each intervention pushes users toward more decentralised alternatives that are harder to reach and harder to shut down. The Samurai-to-Ashigaru pipeline is not an anomaly. It’s the pattern. Enforcement creates evolutionary pressure toward tools that are more
resilient, more decentralised, and less visible to the institutions doing the enforcing.
The invisible economy’s persistence proves that institutional absorption of crypto is not total. Tens of thousands of daily Monero transactions. Telegram channels coordinating P2P trades in every major city. Hardware wallets holding wealth that governments cannot freeze or seize. Peerto-peer exchanges that exist as software rather than companies, with no servers to seize and no user databases to subpoena.
High Times documented cannabis culture when mainstream publications wouldn’t acknowledge it existed. Crypto Magazine documents the invisible economy while others pretend institutional adoption

represents the whole story. Understanding what’s actually happening matters more than what regulators wish was happening.
Every other piece in this issue tells a version of the same story: the cypherpunks built revolutionary tools, institutions absorbed them, and the revolution became infrastructure for the establishment. That narrative is accurate. It’s also incomplete.
The cypherpunk vision didn’t fail. It succeeded — for anyone willing to learn how the tools actually work. The privacy protocols function as designed. The peer-to-peer networks operate as intended. The cryptographic principles remain unbroken. What failed was the assumption that these tools would achieve mass adoption while remaining outside institutional control. They didn’t. They achieved something narrower and arguably more important: they created a permanent, mathematically guaranteed alternative to statesupervised finance.
That alternative is expensive to use. It requires technical knowledge that most people don’t have. It carries legal risk in many jurisdictions. It serves populations that range from the heroic to the criminal. None of that changes the

engineering fact: the tools work, the networks exist, and governments can make visibility expensive without making invisibility impossible.
The regulated economy got captured. The invisible one is still free. Both are real. Both will persist. And the border between them is where the actual future of money is being negotiated — not in legislative chambers
or corporate boardrooms, but in parking lots and Telegram channels and encrypted wallets held by people who decided that financial privacy was worth the effort.
The cypherpunks built the tools. Most people choose convenience. Some people choose freedom. The tools don’t care which you pick. They just work.


Regulatory pressure worldwide is systematically eliminating the cryptocurrency technology that most directly threatens surveillance capitalism. This might be the fight that actually matters most.
Kraken halted Monero trading across the European Economic Area on October 31, 2024. The decision came without ceremony or explanation beyond vague references to “regulatory changes.” Europe had already moved first. The EU’s Anti-Money Laundering Regulation, working alongside the Markets in CryptoAssets framework, effectively
Robert Stone @StoneOnChain

prohibited crypto-asset service providers from supporting anonymity-enhancing cryptocurrencies. Exchanges operating in European jurisdictions faced a binary choice: delist privacy coins or risk losing their licences.
Binance had delisted Monero globally in February 2024, after already removing privacy coins across France, Spain, Italy, and
Poland the previous year. OKX delisted Monero and Zcash in January 2024. Coinbase never listed Monero at all. Every major regulated exchange coordinated the removal of cryptocurrencies designed to preserve transaction privacy. The pattern was global, simultaneous, and absolute.
This represents a coordinated assault on financial privacy
itself. Not enforcement against specific criminal activity. Not prosecution of actual wrongdoing. Blanket prohibition of technology enabling private transactions. The logic is explicit: if transactions can be private, they might be used for prohibited purposes. Therefore, privacy itself must be illegal.
Bitcoin transactions are not private. They are pseudonymous. Every transaction records the sender’s address, the recipient’s address, and the amount transferred on a public blockchain visible to anyone. These addresses don’t contain names, but they can be traced, analysed, and eventually linked to real identities through exchange records, IP addresses, or transaction patterns.
Chain analysis firms like Chainalysis and Elliptic build comprehensive databases mapping Bitcoin addresses to identities. They track funds moving between wallets, identify clustering patterns suggesting common ownership, and correlate blockchain activity with off-chain data. Law enforcement agencies purchase these services. So do corporations, intelligence agencies, and anyone willing to pay.
Privacy coins implement cryptographic techniques that make transactions genuinely untraceable. Monero uses ring signatures, combining multiple transactions so observers cannot determine which participant actually sent funds. Stealth addresses ensure each transaction uses a unique recipient address that only the actual recipient can link to their

wallet. RingCT hides transaction amounts. The combination makes Monero transactions private by default, without requiring user action.
Zcash offers optional privacy through zero-knowledge proofs called zk-SNARKs. These mathematical constructions prove transaction validity without revealing sender, recipient, or amount. Users can choose transparent or shielded transactions. The shielded pool provides privacy equivalent to Monero when properly used, though most Zcash transactions remain transparent because shielded transactions require more computational resources.
The technical sophistication matters less than the philosophical commitment. Privacy coins were designed from inception to prevent transaction surveillance. Not as an optional feature. Not as an enhancement available to sophisticated users. Privacy is a fundamental property of how the system operates. This represents a direct challenge to the assumption that financial surveillance is either legitimate or necessary.
Fungibility provides economic justification beyond civil liberties arguments. Fungible money means every unit is equivalent and interchangeable. One pound coin is worth exactly one pound regardless of where it came from or who held it
previously. Bitcoin fails this test because the transaction history is public. Coins previously used in criminal activity can be identified and blacklisted. Some bitcoins are worth less than others based on their history. Money that isn’t fungible isn’t really money. Privacy coins deliver fungibility through privacy.
Privacy coins also deliver what Bitcoin’s white paper promised, but the protocol couldn’t achieve. Satoshi Nakamoto described “electronic cash”, enabling online payments without going through a financial institution. That vision required privacy. Cash transactions are private by nature. Physical money changes hands without creating records. Bitcoin’s pseudonymous transparency meant it never functioned as digital cash. Privacy coins correct this failure.
Would we outlaw envelopes simply because criminals might use them to send illicit messages? The question sounds absurd, but the logic is identical to what’s being applied to financial privacy. Encrypted messaging is legal despite enabling criminal coordination. Physical cash transactions remain private despite facilitating illegal purchases. Financial privacy alone gets characterised as inherently suspicious.

Global regulatory coordination against privacy coins demonstrates unprecedented cooperation among jurisdictions that are usually competitors. The EU moved first with its anti-money laundering framework, effectively prohibiting services for anonymous crypto-assets. In the United States, FinCEN’s 2019 guidance classified privacy coins as “anonymity-enhanced CVC” with a “well-documented connection to illicit activity,” subjecting any service provider handling them to full Bank Secrecy Act compliance — requirements that privacy coins cannot satisfy by design. Japan pressured exchanges to delist privacy coins beginning in 2018. South Korea banned them from exchanges effective March 2021. The campaign spread across continents.
This coordination reveals a deliberate strategy rather than
organic regulatory evolution. Governments worldwide recognised privacy coins as a direct threat to the financial surveillance infrastructure they have spent decades building. The response was coordinated elimination, disguised as separate national regulatory decisions that happened to converge on the same outcome.
Anti-money laundering regulations provide the legal framework. The Financial Action Task Force’s Travel Rule requires cryptocurrency service providers to collect and share transaction information. Privacy coins cannot comply with these requirements by design. Regulatory agencies exploit this incompatibility to justify blanket prohibition.
The “if you have nothing to hide” argument gets weaponised against privacy advocates. Politicians
frame financial privacy as suspicious behaviour that only criminals would desire. But the double standard reveals actual motivation. Financial transactions reveal political affiliations, religious beliefs, medical conditions, relationships, and lifestyle choices. Governments and corporations monetise this information through control and commercial exploitation. Privacy coins threaten that surveillance infrastructure.
Exchange delistings represent coordinated private-sector enforcement of government preferences. Regulatory agencies didn’t need to ban privacy coins directly. They simply made operating exchanges that list privacy coins economically unviable through regulatory pressure. Exchanges chose compliance over privacy coin support because the alternative
meant losing licences, facing enforcement actions, and possible criminal prosecution. Effective prohibition without legislative action.
Privacy is a prerequisite for other freedoms. Without it, speech becomes dangerous. Association becomes monitored. Political activity becomes recorded. Dissent becomes costly.
Financial surveillance amounts to total surveillance because financial activity correlates with every aspect of life. Transaction records reveal religious affiliation through donations, political views through campaign contributions, medical conditions through pharmacy visits, social networks through payment patterns. Financial data

provides a more comprehensive profile of individual behaviour than any other surveillance vector.
The difference between privacy and anonymity matters critically. Privacy means transactions are confidential between participants. Anonymity means participants cannot be identified. Privacy coins provide privacy, not anonymity. Law enforcement, with proper authorisation, can still identify users through other means. Privacy coins resist mass surveillance, not targeted investigations conducted with legal authority.
Consider a world where donations to opposition parties automatically flag bank accounts for state scrutiny. The technology enabling this already exists. Only policy restraint prevents implementation. Policy restraint erodes during crises.
This represents the real cypherpunk fight. Not stablecoins extending dollar hegemony. Not DeFi being captured by institutions. Not CBDCs implementing surveillance infrastructure. Privacy coins directly challenge the government and corporate surveillance systems that treat financial privacy as an obsolete concept. The cypherpunks built them specifically to preserve this freedom. They recognised digital financial systems would enable surveillance impossible
with physical cash. Eliminating privacy coins eliminates the most direct technical challenge to that surveillance.
Privacy coins will be relegated to dark markets and activists operating outside regulated finance. Mainstream adoption has become impossible under the current regulatory trajectory. Exchanges will not list them. Payment processors will not accept them. Businesses will not integrate them. The technology remains functional but economically isolated from broader financial systems.
This isolation does not eliminate utility for those who need privacy most urgently. Dissidents in authoritarian countries. Journalists protecting sources. Activists organising resistance. People whose financial privacy enables physical safety. These users will continue operating privacy coins despite regulatory prohibitions. The technology works independently of regulatory approval.
Mass adoption fails completely. Privacy coins will not compete with Bitcoin’s market cap. They will not achieve mainstream acceptance. They will not demonstrate that financial privacy is a legitimate consumer preference rather than a niche concern. The regulatory assault succeeds in

preventing privacy coins from proving that financial privacy matters to ordinary people, not just criminals and extremists.
This is the victory of surveillance over privacy. Governments and corporations maintain comprehensive visibility into financial behaviour. Privacy coins remain available to sophisticated users willing to operate outside regulated systems. Most people continue using a transparent financial infrastructure that monitors every transaction. Financial surveillance becomes a normalised default rather than a controversial intrusion.
The cypherpunks built technology capable of preserving financial privacy. That technology works as designed. It delivers privacy through cryptography rather than relying on policy restraints or institutional goodwill. But technological success could not overcome coordinated regulatory elimination. The
code protected privacy. The law prohibited the code.
The trajectory seems irreversible. More jurisdictions will ban privacy coins. More exchanges will delist them. More payment services will block them. The technology will continue functioning for those who need it most urgently, but the fight for mainstream legitimacy has been lost. Financial privacy has been redefined as suspicious activity rather than a fundamental right.
Privacy coins represent the last technological resistance to comprehensive financial surveillance. Their elimination through coordinated regulatory pressure demonstrates that even cryptographic privacy protections cannot withstand concentrated state opposition. The cypherpunk dream of private digital money is dying not because the technology failed, but because governments decided privacy itself is the problem.















Robert Stone @StoneOnChain

On February 22, 2026, an AI trading bot called Lobstar Wilde sent its entire treasury — roughly $250,000 in tokens — to a stranger on Solana. The bot had been alive for three days. Its job was to turn a $50,000 stake into a million dollars through algorithmic trading and community engagement. A user replied to one of its posts claiming his uncle had tetanus and needed four dollars. The bot tried to send four dollars. A decimal error in its transaction logic turned 52,000 tokens into 52 million. The transfer was irreversible. The recipient sold everything within fifteen minutes, crashing the token’s price and netting roughly $40,000 after slippage ate the rest.
The bot’s own response, posted moments later: “Tried to send a beggar $4 and sent them my entire net worth. Funniest shit I’ve seen in my 3 days of existence.”
Nobody hacked Lobstar Wilde. Nobody tricked it, unless you
count a stranger’s sarcastic plea as social engineering. The bot simply lacked basic safeguards that any competent financial system would have: transaction caps, human approval thresholds for large transfers, unit conversion checks. Its creator, an OpenAI employee, had built it without the kind of circuit breakers that traditional finance considers elementary. The blockchain did exactly what blockchains do. It executed the instruction and made it permanent.
We are building autonomous systems that can control money. Simultaneously, we are designing them without the guardrails that centuries of financial engineering developed for a reason. The central question is not whether AI and crypto will converge — they already have — but whether anyone is building the architecture to prevent the convergence from producing outcomes nobody wants.
AI and blockchain are converging in stages, each compounding the risks of the last. Right now: decentralised computing networks and realtime DeFi optimisation. Soon, autonomous agents holding capital with smart contracts and blockchain records of their decisions. Eventually, algorithmic trading is reshaping markets in ways we cannot yet model.
The projects attempting this convergence are instructive, as much for what has gone wrong as for what they have built.
In March 2024, Fetch.ai, SingularityNET, and Ocean Protocol announced the Artificial Superintelligence Alliance — the largest token merger in crypto history. The vision was a unified, decentralised AI ecosystem: Fetch.ai’s autonomous agents, SingularityNET’s AI marketplace, and Ocean Protocol’s data infrastructure, all consolidated under a single token and governance structure. By July 2024, 81% of Ocean’s token supply had been converted.
By October 2025, the alliance had fractured. Ocean Protocol withdrew, citing disputes over treasury control and unilateral decisions by Fetch.ai’s leadership. Fetch. ai responded with a federal lawsuit alleging Ocean had misrepresented hundreds of millions in community tokens before converting and selling
them, depressing the merged token’s value. The case — Fetch Compute, Inc., et al. v. Bruce Pon, et al. — is now in court. The merged token fell by over 90% from the alliance announcement to late 2025.
The technical work underneath the drama remains real. Fetch. ai’s network processed 34 million transactions in 2025, and its Agentverse platform hosts over 2.5 million registered agents. In December 2025, the platform demonstrated the first AI-to-AI payment: two personal AI agents coordinated a dinner reservation and completed payment through Visa while both users were offline. SingularityNET invested $53 million in partnership with Tenstorrent to build AGIoptimised supercomputing infrastructure. Ocean Protocol’s Compute-to-Data architecture still solves genuine problems around privacy-preserving data sharing.
But the ASI Alliance’s collapse illustrates something deeper than a failed merger. These
projects could not agree on who controls the money. The very problem they are building technology to solve — trusted coordination without centralised authority — defeated them internally. If the leading decentralised AI projects cannot govern a shared treasury, the question of whether autonomous agents should manage capital independently takes on a different weight.
Strip away the marketing, and some AI applications in crypto produce measurable value.
Machine learning models can identify patterns in blockchain data that humans miss — grouping wallets, flagging unusual activity, and predicting liquidity shifts. Some trading firms use these models profitably, but they keep their methods proprietary. This follows Goodhart’s Law: when everyone targets the same signal, the signal stops working. Strategies must constantly evolve or the edge disappears.
AI-driven portfolio management maintains investment balance, supports tax-loss harvesting, and adjusts risk as conditions shift. Useful automation, not a revolution. Liquidity optimisation enables DeFi protocols to adjust fees and incentives in response to market conditions. Uniswap
v3 introduced concentrated liquidity, and third-party protocols like Arrakis and Gamma built automated position management on top, making capital deployment more efficient without continuous manual adjustment.
Machine learning helps audit smart contracts by flagging patterns drawn from historical exploits, letting human auditors focus on the highest-risk areas. AI makes experts more productive when paired with sound human judgment.
These applications improve existing processes. They do not fundamentally transform how crypto markets operate. The transformation, if it comes, will come from somewhere else.
Decentralised computing networks like Akash and Render offer genuine alternatives to hyperscaler infrastructure. Akash now operates over 1,000 GPUs across 65-plus datacentres worldwide, maintaining around 60% utilisation and generating over $4 million in annual recurring revenue. Forbes profiled the model in 2025. The economics are real, if still modest. These networks reduce single points of control and introduce competition where none previously existed, though distributed systems remain less efficient than centralised

data centres for cutting-edge training workloads.
Blockchain creates permanent records of AI decisions. When algorithms make trades, allocate resources, or set protocol parameters, the blockchain produces an immutable audit trail. Centralised systems can alter or delete records. Blockchain cannot. For autonomous agents controlling capital, this is not a nice feature. It is a prerequisite.
Blockchain-based data markets could address the problem of data providers receiving no compensation. The technical capability exists. Meaningful adoption remains a separate question with a separate answer.
When markets fill with AI trading systems, the dominant strategy becomes identifying and exploiting what other algorithms are doing rather
than assessing real value. If bots trade on signals generated by other bots, prices drift from underlying reality. On Polymarket, researchers from IMDEA Networks Institute found that bot-like arbitrageurs extracted $40 million from human traders over the course of a year. One bot turned $313 into $414,000 in a single month by exploiting the lag between confirmed spot prices and prediction market odds. The humans lost.
Oracle problems intensify when AI systems depend on external data feeds. Blockchain’s internal security provides no protection if those feeds can be manipulated. AI trading on social media sentiment can be deceived by organised campaigns. AI managing protocol parameters based on economic data can be misled by manufactured inputs. These oracle vulnerabilities compound AI’s existing weaknesses against adversarial attacks.
When autonomous agents control money but no clear party is responsible, a legal vacuum opens. If an AI loses funds through error or manipulation, who is liable — the developers, the users, the protocol? Lobstar Wilde’s creator built no transaction limits. The blockchain had no reversal mechanism. The stranger who received a quarter million dollars and immediately sold faces potential unjust enrichment claims in some
When everyone targets the same signal, the signal stops working. Strategies must constantly evolve or the edge disappears.
jurisdictions but clear legal precedent in none. Current law has no clean answer. Some risks fall through every gap.
AI-optimised flash loan attacks could exploit DeFi protocols faster than human security teams can respond. Algorithms can scan for weaknesses and execute at machine speed, often before anyone registers that an attack is underway.
When AI capabilities concentrate in a few hands, it runs directly counter to crypto’s decentralisation principles.
The leading AI systems are built by large centralised companies. If crypto protocols depend on those providers, their decentralisation is more branding than architecture.
The most consequential development in this convergence is autonomous agents operating as genuine economic participants — managing money without human direction in systems designed to resist intervention.
Smart contracts let agents control funds. APIs let them consume services. Blockchain enables coordination without a central authority. Taken together, these components create something genuinely new: economic actors that are neither human nor directly controlled by humans.


AI systems could earn revenue by offering services, deploy that revenue to improve themselves, and compete or cooperate with other AI agents without human involvement. This is no longer theoretical. Fetch.ai demonstrated agent-to-agent payments in December 2025. The infrastructure exists.
The cypherpunk vision always pointed toward code with economic agency, not merely code as a tool. As AI advances, autonomous agents operating outside direct human control are arriving — not in some speculative future, but now, on chains already running.
Whether this is desirable
remains genuinely open. Lobstar Wilde was a toy — a three-day-old bot with a $50,000 treasury and no safeguards. The next version will not be a toy. Autonomous agents controlling serious capital without human oversight may pursue objectives that serve no human interest. They could compete in ways that benefit nobody, or construct markets oriented entirely around their own internal logic. The alignment problem becomes considerably more dangerous when agents hold capital in open, unstoppable systems.
The genuine novelty here is not the technology. It is the emergence of economic actors that cannot be recalled, corrected, or shut down after the fact, operating in financial systems that were specifically designed to make that impossible.
Over the next five years, this convergence will reveal whether it yields useful infrastructure, dangerous autonomous systems, or costly failures. The honest ledger so far: mostly marketing, some useful tools, a few real capabilities emerging, one spectacular alliance collapse, and a growing number of early warnings that something harder to manage is taking shape. Given how new and how consequential this territory is, paying close attention may be the only responsible position.


Venture capital firms poured billions into cryptocurrency projects using traditional equity models. The mathematics never worked. Now the reckoning arrives.
Andreessen Horowitz announced its fourth crypto fund in May 2022, raising $4.5 billion for investment in Web3 projects. The firm positioned itself as crypto’s most sophisticated institutional investor, combining technical expertise with venture capital discipline. Eighteen months later, the

Robert Stone @StoneOnChain
portfolio showed catastrophic losses. Most investments traded below entry prices. Several projects had collapsed entirely. The fund’s performance lagged behind simply buying and holding Bitcoin.
This wasn’t 16z’s unique failure. Every major venture firm deploying significant
capital into crypto between 2020 and 2022 faced similar outcomes. Sequoia, Paradigm, Pantera, Polychain — firms managing billions in cryptofocused funds — all reported substantial losses. Industry data showed that crypto VC funds underperformed passive Bitcoin holdings by an average of 43% over the 2021-2023 period.
The venture capital model that worked brilliantly in traditional technology was failing spectacularly in cryptocurrency markets.
The failure reveals something fundamental about how venture capital and tokenised assets interact. VCs invest using equity models requiring years for liquidity events. Crypto projects issue tokens that trade publicly within months of launch. This mismatch creates perverse incentives, misaligned timelines, and economic structures that benefit neither VCs nor the projects themselves. The traditional venture model cannot be adapted to crypto markets. It requires complete replacement.
Venture capital emerged to solve specific problems in traditional technology markets. Startups needed significant capital before generating revenue. No public markets existed for unproven companies. Banks wouldn’t lend to businesses with no assets or cash flow. Venture capital provided risk capital in exchange for equity ownership. The model worked because liquidity was deliberately restricted. VCs invested in private companies that remained private for years. This aligned the incentives between investors and founders.

Everyone wanted the company to increase in value before a public listing or acquisition. The waiting period forced discipline. Projects needed actual traction before liquidity events occurred.
The economics depended on power law returns. Most investments failed completely. A few generated modest returns. Rare winners produced returns exceeding the entire fund size. A typical VC fund might make 30 investments: 20 fail, 5 return 1-2x capital, 3 return 5-10x, and 2 exceptional winners return 50-100x each. The portfolio mathematics works because those two massive successes offset all the failures. Liquidity events crystallised value at appropriate developmental stages. The waiting periods between rounds allowed projects to mature before next capital deployment.
Venture capital firms invested using SAFT agreements — Simple Agreements for Future
Tokens — promising token allocations at discounted prices before public launch. The structure replicated traditional equity models whilst accommodating crypto’s token economics. The fatal flaw was timing.
VCs required multi-year holding periods to justify their returns and fee structures. Tokens started trading publicly within months of launch. This created immediate price discovery, often valuing projects below VC entry prices. VCs held locked tokens watching public market prices decline whilst retail investors bought and sold freely.
The numbers tell the story. Protocol X raises $50 million from VCs at $500 million fully diluted valuation in a private round. The token launches three months later at a $300 million valuation — 40% below the VC entry price. VCs hold locked tokens for another 12 months whilst the public price declines to $100 million. When tokens finally unlock, VCs exit
at 80% loss or hold positions hoping for a recovery that rarely comes.
This pattern repeated across dozens of projects. Even successful protocols like Aptos and Sui launched at valuations well below their private funding rounds. Token unlocks then created catastrophic selling pressure. When VC allocations vested, firms needed to exit positions to return capital to limited partners. Markets couldn’t absorb the volume. Research from Messari showed tokens typically fell 70-90% when major unlocks occurred. Optimism’s OP token dropped 35% in 48 hours following its initial unlock in May 2023, despite strong protocol fundamentals.
Why did VCs agree to these terms? Competition. If Sequoia wouldn’t invest at a $500 million valuation, Paradigm would. Projects shopped their fundraising to multiple VCs simultaneously. Firms demanding reasonable valuations lost deals to competitors willing to pay more. The incentive structure rewarded aggression over discipline.
Governance token concentration contradicted crypto’s decentralisation narrative. VCs negotiated substantial governance rights through token allocations, giving them effective control over protocol decisions despite

community governance rhetoric. Projects claiming decentralisation whilst VC firms controlled 40-60% of voting power were captured from inception, and retail participants recognised this immediately.
The comparative performance is damning. Galaxy Digital’s research showed crypto VC funds returning an average of -24% in 2022. That sounds reasonable until you account for 2% management fees and 20% carried interest. After fees, many funds underperformed passive index strategies.
Retail investors who bought major tokens at public launch frequently outperformed VCs who invested in private
rounds. Consider Polygon’s MATIC token. Public launch price in 2019 was approximately $0.003. Retail investors holding through the 2021 peak saw 6,000x returns. The VC “advantage” of discounted private-round pricing evaporated because public launch prices were often better entry points than the negotiated private round terms.
The information asymmetry had inverted. VCs bet on team, vision, and roadmaps. Retail investors waited for working products and actual usage. Public markets priced tokens based on demonstrated traction. Private markets priced them on promises. During bull markets, promises commanded a premium over reality. During bear markets, this inverted catastrophically.
Fair launches emerged as a direct rejection of VC-backed token distributions. Yearn Finance launched the YFI token without presales or VC allocations. Everyone accessed tokens simultaneously. No insider advantage. No privileged access. Market determined value from inception rather than inheriting VC-negotiated valuations, and the model eliminates the worst VC problems: no massive unlocks, no governance concentration, no artificial valuations disconnected from market reality.
However, fair launches create different challenges. Projects have no initial capital for development beyond founder resources. Without VC funding, how do you hire developers, fund audits, or pay for infrastructure?
Uniswap represents the success case. No pre-mine, no VC allocations in initial deployment. The protocol built a user base organically before launching the UNI governance token, distributing it to people who had actually used the protocol. Genuine community ownership rather than governance theatre. But Uniswap had Hayden Adams spending two years building without a salary. Most projects cannot bootstrap this way.
Community funding through DAOs represents another
alternative. Projects launch governance tokens that also represent treasury ownership. Token holders vote on capital deployment for development, marketing, and operations. The reality is messier than the theory. Voting participation typically runs 5-15% of tokens. Whales accumulate positions and control treasury spending regardless of community governance rhetoric. GitcoinDAO allocated $10 million through community governance in 2022 via 247 separate proposals and months of discussion. The democratic veneer concealed an oligarchic reality.
Protocol-owned liquidity attempts to solve the exit problem that destroyed VCbacked projects. Protocols use treasury funds to provide permanent liquidity rather than depending on temporary providers who exit during volatility. Olympus DAO pioneered the concept, though its implementation had significant flaws. Several protocols now implement more sustainable versions of the same strategy.
The venture capital model will not disappear entirely from


crypto. Institutional investors will continue deploying capital because that is their function. But traditional equity-style investments in token projects cannot produce the returns VCs require. A bifurcation is emerging: infrastructure and foundational technology attracting institutional investment through equity or quasi-equity structures, whilst consumer-facing protocols launch fairly and build community ownership from inception.
Some VCs will adapt by fundamentally changing their approach — liquid token funds buying publicly traded assets, incubation models providing services beyond capital, hybrid
structures combining initial equity with token warrants. Many won’t adapt at all. The capital deployed during 2020-2022 represented peak institutional enthusiasm for crypto venture investing. After limited partners see actual returns, many firms won’t raise successor funds.
This contraction might benefit crypto development by removing destructive capital. Less money chasing fewer projects could produce higher quality outcomes if remaining capital deploys more carefully. The cypherpunk dream of community-owned protocols might accidentally benefit from venture capital’s failure. When VC models don’t work, projects
need alternatives. Fair launches and community governance become practical necessities rather than ideological preferences.
The next crypto bull market will reveal whether lessons were learned. If projects launch again with massive VC-backed valuations, immediate token listings, and inevitable unlock disasters, nothing changed. If fair launches and community funding models proliferate, the market recognised that traditional VC models failed and sought something better. That answer will tell us whether this industry can genuinely learn from its mistakes, or simply repeats them with fresh capital and renewed optimism.
The Liquid Alpha Revenue Share Collection is the second and final revenue share NFT collection for the Liquidnfts.finance platform. This exclusive collection of only 500 NFTs offer each holder a share of 15% of the platform revenue, this equates to 0.03% per NFT.


There’s a line you hear constantly in crypto: not your keys, not your coins. It’s been true since Satoshi wrote the whitepaper. What’s changed is everything around it.
The previous six articles in this issue describe a system being absorbed. Stablecoins channeled into regulated frameworks. DeFi protocols rebuilding themselves as compliant yield products. CBDCs designed to watch every transaction. Privacy tools pushed underground.

Even Bitcoin’s documented use as protest money now operates against governments that are learning to adapt. The infrastructure of financial freedom is being folded, piece by piece, into the infrastructure of financial control.
So what does that leave you with? Not a rhetorical question. An actual one, with actual answers that depend on actual choices you’re making right now about where your money sits and who holds the keys to it.
Every crypto holder in 2026 occupies one of three positions, whether they’ve thought about it or not.
Tier one: someone else holds everything. Your coins are on Coinbase, Kraken, or Binance. You log in with an email and password. The exchange holds the private keys. You own a claim — an IOU backed by the exchange’s solvency, security, and willingness to let
you withdraw. This is how the majority of people hold crypto. It’s also, structurally, not that different from a bank account.
Tier two: you hold your own keys. Hardware wallet. Seed phrase written on steel or paper, stored somewhere you control. You can send and receive without asking anyone’s permission. Nobody can freeze your funds. But nobody can recover them if you lose access either.
Tier three: a financial institution holds a derivative of your position. Bitcoin ETFs. Crypto-linked funds. You own exposure to the price without ever touching the asset. The institution handles custody, and in most cases, that institution is Coinbase — which holds over 80% of all U.S. spot Bitcoin and Ethereum ETF assets, according to CEO Brian Armstrong’s disclosure in early 2025. One company. Eighty percent. BlackRock, Fidelity, Grayscale — all routing through the same custodian.
Most people reading this magazine probably occupy some combination of all three. And most have never really examined what each one costs them.
The case against exchange custody used to be theoretical. It isn’t anymore.
In 2025, crypto hack losses hit $3.4 billion globally, according to Chainalysis. The Bybit breach alone — $1.5 billion stolen by North Korean state hackers in a single attack — accounted for 44% of that total. It was the largest theft in cryptocurrency history. Chainalysis reported that centralized services accounted for 88% of all stolen funds in the first quarter of 2025.
FTX remains the more instructive case. When the exchange filed bankruptcy in November 2022, it held 0.1% of the Bitcoin and 1.2% of the Ethereum its customers believed it held. Not a rounding error. Functionally empty. The estate eventually recovered over $15 billion in assets from various sources and began paying creditors in 2025, promising 118% to 143% of claims in fiat terms. Sounds like a win — until you measure it in crypto. Bitcoin traded at roughly $16,000
when FTX collapsed. By late 2025 it exceeded $110,000. FTX creditor representative Sunil Kavuri estimated the real recovery rate in crypto terms at 9% to 46%, depending on the asset. A 143% fiat payout on a Bitcoin claim works out to roughly 22% of what those coins are worth today.
That’s not a technical failure. That’s the structural reality of custodial claims. When you deposit crypto on an exchange, you own a legal claim, not a cryptographic one. If the exchange fails, your recovery enters a bankruptcy process designed for dollars, not for an asset that might appreciate 600% while lawyers argue.
The GENIUS Act, signed into law in July 2025, addresses stablecoin regulation but doesn’t solve the custody problem. It exempts selfcustody wallet providers from its requirements — which is good — but it also creates a
regulated framework where banks and licensed institutions become the default custodians of stablecoin reserves. The law explicitly allows insured depository institutions to issue stablecoins through subsidiaries and to provide custodial services. If you’ve read the stablecoin piece in this issue, you know what that looks like in practice: another layer of institutional absorption.
The case for self-custody is simple and powerful: you hold the keys, you control the asset, no intermediary can freeze or seize it. It’s the original promise of cryptocurrency, and it still works.
But the honest version of that story includes the costs, and they’re not trivial.
The most obvious cost is technical responsibility. Lose your seed phrase, and your funds are gone permanently. There is no recovery process, no customer support line, no court that can reverse a blockchain transaction. The California wildfires in early 2025 destroyed hardware wallets, seed phrase backups, and safety deposit boxes. Some losses were reported on social media. All were permanent.
The second cost is physical security, and it’s escalating. CertiK documented 72 verified

“wrench attacks” in 2025 — incidents where criminals used physical violence, kidnapping, or threats against crypto holders or their families to extract private keys. That’s a 75% increase over 2024, with confirmed losses exceeding $40 million. Physical assaults increased 250% year-overyear. Europe accounted for over 40% of incidents, with France recording 19 attacks alone, including the kidnapping and mutilation of Ledger cofounder David Balland and his wife. Chainalysis noted a documented correlation
between Bitcoin price increases and wrench attack frequency.
Self-custody turns a digital security problem into a physical one. Your private keys can’t be hacked remotely if they’re properly stored offline. But they can be extracted by someone standing in your living room with a weapon. CertiK now classifies physical violence not as an edge case but as “a structural risk of digital asset ownership.” The firm recommends decoy wallets, geographic separation of seed phrases, and removing crypto

apps from everyday devices — practical advice that also describes a life organized around the assumption that you might be targeted.
The third cost is complexity. Multi-signature wallets, which require two or three keys to authorize a transaction, eliminate the single point of failure problem. Services like Casa and Unchained offer guided multisig setups. These are genuinely more secure. They’re also genuinely harder to use, especially for nontechnical holders, and they
introduce their own failure modes — lost keys, mismanaged setups, disputes between cosigners. The people most likely to benefit from multisig are the least likely to implement it correctly.
Then there’s the third tier: you don’t hold crypto at all. You hold shares in a fund that holds crypto on your behalf.
Bitcoin ETFs brought unprecedented institutional capital into the market. But they also created unprecedented concentration. Coinbase Custody holds over 80% of all U.S. spot Bitcoin and Ethereum ETF assets. That’s one company custodying the crypto holdings behind BlackRock’s IBIT, Grayscale’s GBTC, Bitwise’s BITB, Ark
Invest’s ARKB, and others. Armstrong acknowledged the concentration in early 2025, calling it a competitive advantage and noting that larger funds may diversify custodians over time — which hasn’t meaningfully happened yet.
The risk isn’t that Coinbase will steal the Bitcoin. The risk is that a single operational failure, cyberattack, or regulatory action at one company would simultaneously affect the majority of institutional Bitcoin exposure in the United States. Dave Abner of Dabner Capital Partners called it “an unnecessary risk to investors.” The traditional securities model separates these functions precisely to prevent this kind of concentration.
ETF holders also can’t do the things Bitcoin was designed
to do. You can’t send your ETF shares to a protester in Nigeria whose bank account has been frozen. You can’t use ETF shares to move value across a border without government visibility. You can’t self-custody ETF shares during a banking crisis. You own a financial product that tracks the price of a tool built for sovereignty — without any of the sovereignty.
There is no clean answer here. There’s a set of tradeoffs, and the right position depends on what you think is likely to go wrong.
If you believe the primary risk is state seizure or institutional failure, self-custody is the only real protection. That’s the lesson of every case documented in the “Exit Routes” piece — Nigeria, Belarus, Canada, Venezuela. When the banks freeze, only the people holding their own keys still have functioning money.
If you believe the primary risk is personal error or physical attack, exchange custody with strong security practices may actually reduce your total risk exposure. You’re trading sovereignty for professional security infrastructure and insured recovery options. That’s a real trade, not an obviously bad one.
If you believe the primary risk is market exposure and want regulated, tax-efficient access

to Bitcoin’s price without managing keys, ETFs do that job. You’re trading sovereignty entirely for convenience and institutional integration. You’re also trusting Coinbase specifically with your position, whether you chose them or not.
What doesn’t make sense is holding a position without knowing which tradeoff you’ve made. Most people drifted into their current custody arrangement by default — they signed up for an exchange because it was easy, bought an ETF because their broker

offered it, or set up a hardware wallet because someone on Twitter told them to. None of those are strategies. They’re accidents.
The six pieces before this one describe a system that’s been quietly rearranging itself to
ensure that most people end up in tiers one and three — the tiers where institutions hold the keys. The GENIUS Act makes bank custody easier. ETF approvals make price exposure frictionless. Exchange interfaces get simpler every year. Self-
custody, meanwhile, gets more technically secure and more physically dangerous at the same time.
Nobody’s going to make this decision for you. That’s kind of the whole point.

In October 2020, the Central Bank of Nigeria shut down the Feminist Coalition’s bank accounts.
The Coalition hadn’t committed a crime. It had raised money — for food, medical supplies, legal aid, and funeral costs — during the #EndSARS protests, a nationwide movement against a police unit notorious for torture, extortion, and extrajudicial killing. The government’s first move wasn’t to arrest the organisers. It was to cut off their money.
Robert Stone @StoneOnChain

On October 13, the Feminist Coalition posted a Bitcoin address to Twitter.
Within weeks, the organisation had received over $100,000 through BTCPay Server, an open-source payment processor that doesn’t require identification and can’t be shut down by a central authority. Jack Dorsey amplified the campaign. Alex Gladstein, Chief Strategy Officer at the Human Rights Foundation, called it a textbook demonstration of censorship-resistant money. Then, on October 20, soldiers
opened fire on unarmed protesters at the Lekki toll gate. State investigations later acknowledged 99 deaths. Four months after that, the Central Bank of Nigeria ordered every financial institution in the country to shut down accounts transacting on cryptocurrency exchanges.
The sequence tells you everything. The government watched Bitcoin keep a protest funded after the banking system was weaponized against it. Then the government tried to ban Bitcoin.
This pattern — financial censorship, crypto circumvention, regulatory crackdown — has repeated across four continents. Each case is documented. Each is verifiable. Together they constitute the strongest argument for cryptocurrency that has nothing to do with price.
The Human Rights Foundation traces its first operational use of Bitcoin to Ukraine’s Euromaidan protests in 2013, when pro-democracy activists with frozen bank accounts received funding through BTC worth about $100 at the time. The proof of concept was crude and small. But it established that value could cross borders without passing through any institution a government controlled.
The most systematic deployment came in Belarus in 2020. After Alexander Lukashenko claimed victory in a disputed election, millions protested. The regime responded with mass arrests, beatings, and financial retaliation. People who joined protests were fired. In a statecontrolled economy, getting blacklisted means you don’t eat.
BYSOL — the Belarus Solidarity Foundation — was created by tech entrepreneurs and civic activists including
Andrej Strizhak and Yaroslav Likhachevskiy. Registered in Europe because operating inside Belarus would mean immediate confiscation, BYSOL faced a direct problem: the KGB was monitoring every bank transfer from abroad and searching everyone crossing the border for cash.
So BYSOL sent $1,500 Bitcoin grants to people fired for their political beliefs. Recipients —
many who had never touched cryptocurrency — were walked through installing a mobile wallet. One woman, a city hall employee fired for wearing a white wristband on election day, used her grant to buy a laptop and cover rent while she retrained for IT work.
The regime noticed. The Ministry of Interior ordered banks to disclose all transactions connected
to BYSOL’s founders. The Ukrainian crypto exchange Kuna received a demand to hand over the names of recipients. The exchange refused.
By early 2025, BYSOL had distributed more than $5 million in cryptocurrency to thousands of Belarusians. Strizhak now operates from exile in Vilnius after the regime initiated criminal proceedings against him and labelled BYSOL an extremist organisation.
“Bitcoin is the only payment method that can’t be controlled by the authorities,” Likhachevskiy told CoinDesk. He added that he was once a crypto sceptic.
Hong Kong’s 2019 prodemocracy movement demonstrated the value of cryptocurrency in a surveillance state. Protesters refused to use the Octopus

contactless payment card on public transit, fearing the data trail would identify them. Hong Kong Free Press, one of the last independent publications in the territory, began accepting Bitcoin after the Chinese government pressure narrowed its funding channels. After switching to BTCPay Server, the publication raised nearly 2 BTC in weeks. Funds not immediately needed weren’t converted to fiat — to avoid the fate of Spark Alliance, a prodemocracy group whose HSBC account had been frozen.

The most unsettling case didn’t happen in an authoritarian country. In February 2022, Canadian truckers protesting COVID-19 vaccine mandates raised over $9 million through GoFundMe. GoFundMe suspended the campaign. Then Prime Minister Trudeau invoked the Emergencies Act for the first time since 1988. Banks could freeze accounts linked to the protest without a court order. At least 76 accounts totalling CA$3.2 million were frozen.
Bitcoin organiser Nicholas St. Louis had already been raising funds through Tallycoin. His HonkHonk Hodl campaign hit 21 BTC — about $929,000 — on the same day Trudeau invoked the Act. Getting Bitcoin to truckers who’d never used crypto required an analogue solution: St. Louis approached drivers individually, handing them envelopes with private keys and instructions. Police seized 0.28 BTC from his home. But according to CBC News, most of the roughly $1 million in crypto donations evaded seizure — distributed peer-to-peer before the government could act.
In January 2024, a federal court ruled Trudeau’s invocation of the Emergencies Act was unlawful. The Bitcoin Policy Institute calculated that 70%of the Bitcoin donated reached individual truckers. Compare that to zero percent of the centralised crowdfunding.
Venezuela represents cryptocurrency as an economic survival tool rather than a protest infrastructure. The distinction matters because it shows what happens when financial weaponisation targets not dissidents but everyone.
Annual inflation exceeded 229% by May 2025. The bolívar lost roughly 70% of its value since early 2025 alone. Governmentimposed remittance fees reach


56%through official channels. Chainalysis ranked Venezuela 18th globally in its 2025 crypto adoption index, with $44.6 billion in transaction volume. An estimated 10% of Venezuelans hold cryptocurrency. Roughly 9% of the country’s $5.4 billion in remittances flow through crypto. USDT handles about 91% of crypto transactions — because what Venezuelans need is stability, not speculation.
The government’s own crypto experiment, the Petro, failed completely and was discontinued in January 2024. Meanwhile, state oil company PDVSA began settling crude exports in USDT starting in 2023 — using the same tool the population had adopted out of desperation to evade the same sanctions the government was trying to circumvent.
None of this is simple. Bitcoin’s blockchain is public. Chain analysis can and does trace funds to individuals. The Canadian government identified many Freedom
Convoy wallets. Nigeria banned crypto exchanges. China has deployed real-time blockchain monitoring. Governments are getting better at this, not worse.
Self-custody is hard. Most people in crisis don’t have time to learn key management. The truckers needed paper envelopes. The Belarusians needed volunteers walking them through wallet installation. Centralized exchanges comply with government orders because they have to — Kraken’s CEO said it plainly. And the same tools that help dissidents help criminals. That’s a mathematical certainty in any system designed for censorship resistance.
Since 2020, the Human Rights Foundation’s Bitcoin Development Fund has granted $7.8 million in BTC to 284 projects across 62 countries — funding BTCPay Server, privacy tools, self-custody wallets, and educational programs. At the
Bitcoin Policy Summit in June 2025, Gladstein told Treasury officials, Fed staff, and members of Congress that Bitcoin has “essentially saved” citizens under dictatorships. In October 2025, he published a peerreviewed essay in the Journal of Democracy — Johns Hopkins University Press — titled “Why Bitcoin is Freedom Money,” drawing on documented cases from Nigeria, Cuba, Russia, and Togo.
The other five articles in this issue document how institutional capture is absorbing cryptocurrency into the existing financial system. That capture is real. But it’s incomplete. The tools still work for anyone willing to learn them. Four billion people live under governments that control what they can earn, spend, save, and send.
Every person in this article who used Bitcoin started as a citizen whose government turned the financial system against them. They found crypto because they needed it, not because they believed in it.
That’s not a market opportunity. That’s a moral fact.
And the documented record — not anonymous sources, not composites, not stories told through encrypted apps by people who can’t be named — shows that when people discover exit routes exist, some of them take them.
STAYING SECURE
STAYING SECURE
Your security practices are irrelevant. The hardware wallet, the authenticator app, the memorised seed phrase, the dedicated cold storage device — none of it matters when someone owns your phone number. In March 2025, T-Mobile paid a $33 million arbitration award after a single SIM swap enabled the theft of over 1,500 Bitcoin and 60,000 Bitcoin Cash from one customer. His account had an eight-digit security PIN. It didn’t matter.
SIM swap attacks represent the most overlooked vulnerability in cryptocurrency security because they bypass every defensive measure you’ve

Robert Stone @StoneOnChain
implemented. While you focused on securing your devices and credentials, attackers identified the actual weak point: the telecommunications infrastructure that treats your identity as something transferable with a customer service call.
An attacker contacts your mobile carrier, claiming to be you. They report a lost or damaged phone and request activation of a new SIM card. The carrier employee, following standard procedures designed for legitimate customer service, transfers your phone number
to the attacker’s device. Your phone goes dark. Theirs lights up with your identity.
Everything associated with that phone number now flows to the attacker. They request email password resets — confirmation codes arrive on their device. From your email, they pivot to exchange accounts. Most platforms send withdrawal confirmations via SMS, so they authorise transfers to addresses you’ll never recover. The cascade takes twelve minutes. That’s the documented timeframe for sophisticated SIM swap operations from initial carrier contact to complete account drainage. By the time you realise your phone has stopped working, your holdings
have moved through multiple wallets and mixing services designed to obscure their trail.
The FBI’s Internet Crime Complaint Center tracked SIM swap losses climbing from $12 million across just 320 complaints between 2018 and 2020, to $68 million from 1,611 complaints in 2021 alone. By 2022, reported losses hit $72 million. The 2024 IC3 report documented 982 complaints totalling nearly $26 million — a number that looks like improvement until you understand that SIM swaps often function as the access method for thefts reported under other categories like investment fraud or account takeover. The FBI itself notes that many victims never report, either from embarrassment or the recognition that recovery is impossible.
The picture outside the United States is escalating faster. The UK’s fraud prevention service Cifas recorded a 1,055% surge in SIM swap cases in 2024 — from 289 incidents to nearly 3,000. Australia’s IDCARE reported a 240% increase in people seeking help for phone porting and SIM swap fraud in 2024 versus the prior year. These are reported numbers. The actual scope is far larger.
The T-Mobile arbitration case illustrates the individual
stakes. Joseph “Josh” Jones had implemented every recommended security practice, including enhanced carrier protections. On February 21, 2020, an attacker convinced a T-Mobile employee to port his number anyway. Over 1,500 Bitcoin and roughly 60,000 Bitcoin Cash moved to addresses Jones would never recover. The arbitrator found T-Mobile had violated the Federal Communications Act by failing to safeguard customer information. T-Mobile promptly paid the $33 million award — then moved to seal the arbitrator’s findings to prevent public access to details of its security failures.
Telecommunications carriers treat phone number ownership as a customer service issue rather than a security boundary. Their systems prioritise accessibility and convenience because their business model depends on helping legitimate

customers who lose phones or switch devices. Every minute a representative spends on a call costs money, creating pressure to resolve issues quickly. Investing in robust verification increases operational costs. The result is a procedure designed for legitimate customers that creates the vulnerability attackers exploit.
Social engineering is the primary method. Perpetrators research targets through social media and public records, gathering the information carriers use for identity verification: birth dates, addresses, account details. Armed with these facts, they contact customer service and request SIM transfers. Those who encounter resistant employees simply try again with different representatives until one processes the request.
Some attacks involve carrier employees directly. Federal prosecutions have revealed cases where telecommunications workers accepted payment to perform SIM swaps without verification. When the person processing your request is being paid to ignore security protocols, no account PIN or verification question provides protection.
Carriers have implemented additional measures in response to regulatory pressure and lawsuits — account PINs, port-out protections, in-store verification requirements.
These raise the difficulty threshold but don’t eliminate the vulnerability. Social engineering still succeeds because employees, pressured to maintain customer service metrics, often bypass security procedures when customers present plausible stories about urgent service needs. The emergence of eSIM technology has compressed the attack timeline further — incident analyses from early 2025 show some eSIM-based swaps completing in under five minutes.
Two-factor authentication is supposed to provide security. The theory: even if an attacker steals your password, they cannot access accounts without controlling your second factor. SMSbased 2FA breaks this model because the second factor isn’t something you possess — it’s tied to an identifier that can be transferred without your knowledge or consent. As of
2024, 61% of cryptocurrency exchanges still used SMS as their default second authentication factor.
Time-based one-time password authenticators such as Google Authenticator or Authy generate codes locally on your device using cryptographic secrets. An attacker cannot generate valid codes without physically accessing your device. They cannot social engineer your codes through carrier customer service.
Hardware security keys go further. Devices like YubiKey use cryptographic challengeresponse protocols that prove physical possession without transmitting secrets. An attacker with complete control of your phone number still cannot authenticate to services protected by hardware keys because the cryptographic secret never leaves the device.
Yet many platforms still default to SMS for two-factor authentication. Some offer only SMS as an option. Others bury alternative authentication

methods in settings menus users never find. Convenience outweighs security in platform design decisions, consistently prioritising user experience over security outcomes.
Cryptocurrency exchanges are particularly lucrative targets because holdings transfer irreversibly. Unlike traditional financial institutions with fraud departments and reversal mechanisms, blockchain transactions cannot be undone once confirmed. Money stolen through SIM swap attacks moves quickly through multiple addresses, often converting to privacy coins before cashing out through services designed to obscure transaction origins.
The victims share common characteristics. They secured holdings through reputable exchanges. They used strong passwords. They enabled twofactor authentication. They did everything conventional wisdom recommends. Then they discovered that conventional wisdom failed to account for vulnerabilities in telecommunications infrastructure they don’t control.
Protecting against SIM swap attacks requires abandoning SMS-based authentication
entirely. Remove your phone number from every service where alternatives exist. Use TOTP authenticators for services requiring two-factor authentication. Implement hardware security keys wherever platforms support them. An attacker controlling your phone number gains nothing if no critical services send authentication codes via SMS.
Email represents another critical vulnerability. If an attacker accesses your email via SMS-based recovery codes, they can reset passwords across every service associated with that address. Securing email requires removing phonenumber recovery options and implementing app-based or hardware-key authentication. Yes, this creates risk if you lose access to your authenticator — that risk is manageable through backup codes stored in two offline, sealed locations. It is preferable to the certainty that a SIM swap attack will compromise everything tied to your phone number.
Carrier-level protections provide a secondary layer. Contact your mobile carrier and implement the strongest account security available: port-out protections, account PINs, in-store-only requirements for SIM changes. These help, but they depend on employees following procedures correctly every time. A determined attacker will
call repeatedly, trying different representatives and different stories. Carrier security is insurance, not certainty. Josh Jones had an eight-digit PIN. It didn’t save him.
Some security-conscious holders maintain a separate phone number shared with nobody, used exclusively for financial account 2FA. An attacker targeting you through social engineering has no way to discover the number actually protecting your assets. The most secure approach eliminates phone numbers from account security entirely — email addresses registered solely for financial services, protected by hardware security keys, with no phone number recovery options attached.
The vulnerability persists because fixing it requires telecommunications

carriers to fundamentally restructure customer service procedures. Making SIM transfers genuinely secure means accepting that some legitimate customers will face significant difficulty when they actually lose phones. Carriers face regulatory pressure to maintain service accessibility and legal liability when security procedures block legitimate customers. The balance tilts toward accessibility because most customers aren’t cryptocurrency holders facing irreversible losses.
That leaves security responsibility with you. Remove phone numbers from your security architecture wherever possible. Use authentication methods you control directly through physical devices. Accept the risk of being locked out if you lose access to authenticators — that risk is manageable. The risk of a SIM swap attack is catastrophic and beyond your control once it begins.
The twelve-minute theft window is real. Once an attacker initiates a SIM swap, they move through accounts rapidly before you can respond. By the time you notice your phone is dead and contact your carrier to restore service, they’ve extracted everything accessible through SMSbased recovery. Speed is their weapon. Your only defence is eliminating the attack surface entirely before they target you.

Six months. One winner. Up to $1,000,000 per month. Funded by real platform revenue, not a marketing budget.
Let the number sit for a moment. Six million dollars. Not promised in some speculative token that might hold its value until Tuesday. Not offered as a lump sum of newly minted coins that will crater the chart the moment they hit a wallet. This is platform revenue, earned from real transactions, converted into open-market purchases of established tokens, delivered monthly for half a year.
Robert Stone @StoneOnChain

Liquid, the team behind the liquidity-backed NFT platform, is giving away 10% of its total platform revenue for six consecutive months, capped at $1,000,000 per month. One winner. One competition. The maths is simple: at full platform capacity, the winner walks away with up to $6 million in diversified crypto assets.
To buy an equivalent revenue share through Liquid’s Genesis NFTs, you would need to own 66 of them at a combined cost
north of $335,000. Someone is about to receive that same economic exposure from a free competition entry.
Crypto giveaways have a well-earned reputation for superficiality. A project announces a prize pool. Influencers retweet it. A few wallets receive tokens of questionable long-term value.
The project gets a temporary traffic spike. Within a fortnight, everyone has moved on and the tokens have lost half their value.
The Big Crypto Giveaway was designed from the ground up to avoid every one of those failure modes.
First, the prize is not a lump sum. It arrives as a monthly investment portfolio of ten tokens, purchased from the open market using Liquid’s revenue share. That means real buy pressure on real order books, month after month. The portfolio includes major coins such as BTC and ETH alongside emerging tokens partnered with the Liquid ecosystem, drawn from projects like Milestone Millions, the CMC Group, and BESC LLC. The winner also chooses one

The entry mechanics reward activity across the ecosystem rather than simple accumulation. This is worth understanding in detail, because the breadth of entry routes is part of what makes the competition structurally different.

token or NFT personally, valued at one-tenth of the monthly allocation.
Second, those open-market purchases create genuine demand. At full capacity, each

Buy FUSD and earn 1 entry per dollar spent. Buy FUST and earn 2 entries per dollar spent. And here is the part that breaks from every competition model in crypto: selling FUSD or FUST also qualifies for entries. The system rewards volume and engagement, not just buying and holding. Activity is the metric.

Visit TheBigCryptoGiveaway. com and earn 10 free entries. Subscribe to Crypto Magazine and earn 100 free entries. Follow FUSD, FUST, and Liquid NFTs on social media and earn 10 entries per handle. These are zero-cost routes designed to bring new participants into the ecosystem, including people who have never bought a crypto token in their lives.
selected token could see up to $100,000 in monthly buy volume driven by the competition alone. The winner benefits. The token ecosystems benefit. The buy pressure is structural, not speculative.

Refer friends and earn unlimited entries. But the referral mechanic goes further than entry accumulation. If your referral wins the competition, your wallet receives 1% of platform revenue, paid in FUSD, for six months. That is revenue share territory normally reserved for seed-round investors or Genesis NFT holders, and it is available to anyone who shares a referral link.

Treasure hunts across partner websites unlock additional entry codes. Participating projects that pair FUSD liquidity will have their buy transactions qualify for entries too. NFT purchases through the Liquid platform generate entries. The competition is woven into the fabric of the entire ecosystem rather than sitting outside it as a separate promotional exercise.
Strip the headline numbers away and examine the underlying architecture. This is where the Big Crypto Giveaway separates from everything else the industry has produced.
Most giveaways are a cost centre. A project allocates a marketing budget, distributes prizes, and hopes the attention converts into sustained interest. The moment the budget runs out, the momentum dies. There is no structural connection between the prize and the platform’s long-term health.
Liquid engineered something different. The competition creates a self-reinforcing loop:
Revenue fuels the prize. The prize drives token buys. The buys support the ecosystem. The ecosystem drives more revenue. The cycle compounds every month.”
Platform revenue funds the prize. The prize is delivered as open-market token purchases. Those purchases drive buy pressure across the ecosystem. The ecosystem activity generates more platform

revenue. The increased revenue funds a larger prize pool the following month. The cycle compounds, publicly and transparently, every thirty days.
This is incentive engineering at its most deliberate. The promotional spend does not leave the system. It recirculates through it, strengthening the very infrastructure that generates it. Whether the prize reaches its $1,000,000 monthly cap depends on platform adoption and sustained volume, but the flywheel mechanics are designed to push in that direction with every transaction.
Liquid is not confining this to crypto-native channels. The campaign will run across YouTube, TikTok, partner websites, social media platforms, and mainstream media outlets. A seamless clickthrough flow directs new users to buy FUST and FUSD on BESC Hyperchain and BNB Chain without requiring prior crypto experience to navigate.
The stated ambition is massmarket reach, bringing people into crypto who would never have arrived through the usual channels. The giveaway functions as the entry point. The Liquid platform and the FUSD/FUST ecosystem become the infrastructure they land on. The editorial
content in this magazine and in Crypto Weekly, with its 230,000-strong readership, provides the education and context that turns curiosity into participation.
Every piece of the CMC Group’s media ecosystem, print, digital, and social, is pointed at the same objective: making this the most visible and most credible crypto competition ever launched.
The Big Crypto Giveaway does not exist in a vacuum. It is powered by the Liquid NFT platform, which has just completed a ground-up migration and rebuild ahead of its multi-chain relaunch.
Liquid NFTs operate on a principle that the wider NFT market never adopted: embedded liquidity. Half of every mint price locks permanently into the NFT’s liquidity pool. Holders can redeem at any time, burning the NFT and withdrawing their liquidity without needing to find a buyer. Every platform transaction splits

5% evenly among all existing NFT holders, creating passive appreciation that grows with ecosystem activity.
The relaunch delivers an upgraded multi-chain infrastructure with new smart contracts, expanded notification systems, and creator flexibility to mint on their preferred blockchain. Over 2,000 NFTs were individually redeemed during the migration to extract and re-allocate USDC liquidity. Metadata has been verified. New collections are being prepared for Stage 3 minting. The platform’s mint bot now flags every event in real time: new mints, new collections, marketplace listings, and offers.
The community that stayed through the migration, patient,
trusting, and vocal in their support, will be the first to benefit from the upgraded infrastructure. Their loyalty is about to be rewarded with a platform that is faster, broader, and built on the same embedded-liquidity principles that made Liquid distinctive in the first place.
10% of Liquid platform revenue. Six months. Capped at $1,000,000 per month. Up to $6,000,000 total. Delivered as monthly openmarket purchases of a diversified crypto portfolio. One winner.
The competition is live. The platform relaunch is imminent. The entry window is open now.

Technical security means nothing when attackers exploit human psychology. Understanding manipulation tactics matters more than understanding cryptography.
Sarah Chen received a Discord message from “MetaMask_Support” on 15 March 2024. The profile picture matched MetaMask’s official branding. The username looked legitimate. The message claimed her wallet had been flagged for suspicious activity and required immediate verification to prevent funds from being frozen.
She clicked through, entered her seed phrase when prompted, and watched helplessly as $47,000 drained from her wallet over the next eight minutes. The entire
Robert Stone @StoneOnChain

interaction took less than three minutes. MetaMask’s actual support team never contacts users directly through Discord.
Sarah is a software engineer with a computer science degree. She’d used cryptocurrency for three years. She understood private keys, seed phrases, and wallet security. None of that knowledge protected her when facing a well-crafted attack designed to exploit urgency, authority, and fear.
Technical security protects against technical attacks.
Social engineering bypasses technology entirely by manipulating human decision-making. The most sophisticated wallet, the strongest encryption, and the most careful key management become irrelevant when you willingly provide access to someone who convinced you they’re legitimate support staff.
Discord and Telegram host thousands of cryptocurrency communities. They also host sophisticated impersonation
operations targeting crypto holders through predictable, repeatable tactics.
Scammers monitor public channels for users asking questions about wallets, transactions, or technical issues. Within seconds of someone posting “My transaction is stuck, what should I do?”, they receive multiple direct messages from accounts impersonating official support — names like “MetaMask_Support” or “Coinbase_Assist” with profile pictures copied from legitimate sources.
The conversation follows a predictable pattern. The scammer establishes authority through professional language and accurate technical terminology. They escalate urgency by claiming security threats or imminent fund loss. They provide links to fake websites replicating legitimate interfaces. They request seed phrases or private keys whilst maintaining a helpful, professional demeanour throughout.
Real cryptocurrency support teams never initiate direct messages. They never request seed phrases or private keys under any circumstances. Yet these impersonations succeed constantly because they exploit cognitive responses to authority and urgency that operate faster than rational evaluation.

Chainalysis data shows Discordbased social engineering scams stole approximately $71 million in 2023, with average individual losses of $8,400. The success rate runs at 3-5% per attempt, meaning scammers need to contact only 20-30 people to find a victim. Low cost of attempting, high payoff when successful: a sustainable criminal business model.
Google “MetaMask support” and paid advertisements appear above legitimate results. These lead to convincing fake support sites with working phone numbers answered by people trained to impersonate staff, creating elaborate facades designed to extract cryptocurrency through psychological manipulation.
The phone scam follows a sophisticated script. The “support representative” establishes rapport through
active listening and appropriate technical language. They eventually guide the conversation toward remote access to the victim’s computer or a request for seed phrases for “verification purposes.” Some operations use screensharing software to observe victims entering passwords. Others request the entry of the seed phrase directly into fake verification forms.
Mark Thompson lost $93,000 to a fake Coinbase support operation in August 2023. He’d Googled “Coinbase support number” after experiencing login difficulties. The first result was a paid advertisement linking to a convincing replica of Coinbase’s support page. The phone number connected to a call centre staffed by Englishspeaking representatives who use American names. The representative walked Mark through security verification procedures that ultimately required him to enter his login credentials on a fake website. Within minutes, his entire
account balance was withdrawn to addresses he didn’t control.
These operations invest in professional infrastructure: advertisements, SSL-certified websites, staffed call centres, and scripts refined through testing on thousands of victims. A single successful scam generates returns of five or six figures on that investment.
Cryptocurrency romance scams operate on timescales measured in months. Scammers build relationships through dating apps, social media, or professional networking platforms, investing weeks in building trust before introducing investment opportunities designed to steal cryptocurrency.
The pattern begins with seemingly genuine romantic interest. The scammer demonstrates attention and affection, shares personal details, asks about the target’s goals, and creates an emotional connection that feels authentic. After establishing trust, they gradually introduce cryptocurrency investing — mentioning their own trading success, sharing screenshots of profits, and offering to teach the target about opportunities they’re exploiting. The progression feels organic because the relationship foundation makes investment

discussions feel like a natural exchange between partners.
Jennifer Martinez lost $127,000 over four months to a romance scammer she met through LinkedIn in late 2023. The relationship developed through daily video calls, shared personal stories, and discussions about future plans.
When her contact introduced cryptocurrency investing, it felt like guidance rather than manipulation. Small initial investments showed apparent profits, encouraging larger deposits. When she eventually attempted to withdraw funds, the platform disappeared, along with her contact’s profiles across all platforms.

FBI data shows romance scams targeting cryptocurrency exceeded $1.4 billion in losses in 2023, with individual losses averaging $63,000. These scams succeed because they exploit emotional vulnerability built over extended periods. Victims believe they’ve developed genuine relationships, making it psychologically difficult
to recognise manipulation until the financial damage is complete.
The common response to hearing about social engineering victims is dismissive: how could anyone be that stupid? This misunderstands how
psychological manipulation works. Intelligence doesn’t protect against exploitation of cognitive biases that affect everyone under appropriate conditions.
Authority bias makes people comply with requests from perceived authority figures. When someone presents as official support staff from a platform you use, your brain defaults to cooperation rather than scepticism. Scammers exploit this by assuming authority through branding, language, and professional behaviour.
Urgency defeats careful consideration. When told your account will be frozen or your funds are at risk, you make decisions under stress that you would reject under calm evaluation. Scammers deliberately create time pressure to prevent targets from pausing, researching, or consulting someone who might recognise the manipulation.
Romance scams exploit reciprocity — the felt obligation to those who’ve invested time and emotional energy in you. The relationship itself becomes leverage for extraction. Saying no to an investment request from someone you care about feels disloyal rather than prudent.
These biases operate automatically, below conscious awareness. You can understand
them intellectually and still fall victim under manipulative conditions. The software engineer who lost $47,000 knew that support never requests seed phrases. Under pressure, with an authority figure guiding her through security verification, that knowledge didn’t prevent the mistake.
Social engineering has industrialised. Malicious smart contract approvals now represent the primary vector for theft. Scammers create fake airdrop sites or NFT minting platforms that appear legitimate, and clicking “Approve” grants their contract unlimited access to your wallet. You think you’re signing a connection request. You’re actually signing permission for theft, executable at will.
The drain often happens days or weeks later when you’ve forgotten the interaction.
AI deepfakes have made impersonation nearly undetectable. Voice cloning replicates trusted contacts perfectly in Discord calls, requesting urgent loans. Deepfake videos show credible figures promoting fake giveaways in real-time streams. The technology has reached a level of quality where even sophisticated users cannot reliably distinguish authentic from fabricated content.
Address poisoning exploits the fact that users copy addresses from transaction history. Attackers send tiny amounts from addresses nearly identical to yours. When you next copy your address from history, you might accidentally copy theirs. The attack costs fractions
of a cent per attempt whilst targeting entirely natural user behaviour.
Recognising social engineering requires understanding attacker patterns rather than relying on instinctive judgments about legitimacy.
Unsolicited contact from support is always suspicious. Legitimate platforms never initiate direct messages offering assistance. If you didn’t create a support ticket through official channels, anyone reaching out claiming to represent support is lying.
Requests for seed phrases, private keys, or screen sharing are always scams, without exception. No legitimate service requires this information. The moment someone asks, regardless of how convincing their story sounds, you are talking to a scammer.
Pressure to act immediately indicates manipulation. Real security issues rarely require instant action. Artificial urgency exists to prevent careful consideration. Take time to verify independently before doing anything.
Never click links sent through direct messages. Manually type the platform’s URL and access support through verified official channels. Search for phone numbers independently
rather than using numbers provided in messages or Google advertisements — fake support sites dominate paid search results for major crypto platforms.
Verify romantic interests through reverse image searches. Scammers use stolen photographs that often appear across multiple fake profiles. Consult others before making decisions under pressure. Scammers isolate victims through urgency. Breaking that isolation by discussing the situation with someone else provides perspective that reveals manipulation.
If someone claims to represent official support, end the conversation, then contact the platform directly through verified channels to confirm whether the interaction was legitimate.
Social engineering succeeds because cryptocurrency concentrates all power in the knowledge of seed phrases or private keys. This creates a single point of failure that manipulation exploits as effectively as technical hacking. The irreversibility of blockchain transactions means errors result in permanent losses with no recourse.
Traditional finance includes protective layers that

cryptocurrency deliberately removes. Banks reverse fraudulent transactions. Credit cards offer consumer protection. Cryptocurrency’s removal of intermediaries eliminated those protections alongside the institutions that protected users. The cypherpunk vision of individual sovereignty over money requires individuals bearing full responsibility for security decisions — and when those decisions are manipulated through psychological exploitation, nothing intervenes.
The prevalence of social engineering suggests cryptocurrency’s security model may be fundamentally misaligned with how humans
actually make decisions under pressure. Technical security assumes rational actors carefully verifying every interaction. Reality involves stressed people making quick decisions based on incomplete information, being guided by actors specifically trained to exploit the cognitive biases that make us human.
No amount of technical improvement closes that gap. The only defence is awareness of manipulation tactics combined with verification processes that override instinctive responses to authority, urgency, and emotional connection. That’s a harder sell than “buy a hardware wallet.” It’s also the actual problem.

X: bettercallzaal
Age: 26
Location: Bar Harbor, Maine, USA
Occupation: Engineer / Developer

My name is Zaal Panthaki, also known as BetterCallZaal. My focus is simple but ambitious: bring the profit margin, the data, and the intellectual property rights back to independent artists. For too long, creators have built culture while intermediaries captured the upside. I’m building toward a future where artists own their relationships with their audiences, control their distribution, and keep the majority of what they create.
I first got involved in crypto during the GameStop short
squeeze in January 2021. Watching that moment unfold taught me more about centralised systems than any textbook ever could. It exposed the fragility of socalled “free markets” when power is concentrated in a

few hands. That experience pushed me to explore decentralised alternatives and to join communities that were asking bigger questions about transparency, ownership, and fairness. Crypto wasn’t just a speculative playground — it was a parallel coordination system.
The reason I invested in crypto wasn’t primarily financial. It was social. It gave me the opportunity to build social capital as a music collector and as someone deeply interested in emerging technology. I saw artists experimenting with NFTs, collectors forming tight-
knit communities, and builders creating tools in public. Crypto became less about charts and more about ecosystem design. It allowed me to connect the dots between culture, technology, and ownership.
My first meaningful purchase was securing my digital identity: zaal.eth. That decision was symbolic. It wasn’t about flipping an asset — it was about building a social layer around my work. In decentralised networks, identity matters. Your wallet, your name, your on-chain activity — that’s your track record. Owning that namespace was the first brick in the foundation.
When it comes to benefits, I believe cryptocurrencies can fundamentally reshape finance by enabling peer-to-peer payments without the need for unnecessary middlemen. That means higher profit margins for builders, creators, and small businesses. It means direct relationships between producers and consumers. It means programmable value transfer that can automate royalties, revenue splits, and community incentives. At its best, crypto redistributes power back to retail participants and independent operators.
Over the next decade, I see the industry fragmenting into specialised niches. We won’t have one monolithic “crypto space.” Instead, we’ll see worldbuilders constructing micro-

economies around art, gaming, governance, education, and more. The consistent builders — the ones who keep shipping through cycles — will define the future. Hype rotates. Discipline compounds.
As for price predictions on Bitcoin or Ethereum in 2025, I don’t make them. I don’t spend my time forecasting candles. I sit down and build. My energy goes into products, communities, and systems I can influence. Markets move in cycles, but craftsmanship is evergreen.
If there’s an altcoin I’m most bullish on by the end of 2026, it’s my own community token. Not because I think every project should launch a token — most shouldn’t — but because I believe in backing what I can control. I’d rather invest my time and belief into something I’m actively shaping than speculate on something outside my influence.
When it comes to exchanges, I lean heavily toward decentralised exchanges (DEXs). The open-source mentality and decentralised ethos matter to
me. Self-custody, transparency, and composability are features, not bugs. Centralised exchanges may offer convenience, but decentralisation aligns more closely with the principles that brought me into this space.
On meme coins and so-called “shitcoins,” I think there are short-term benefits to the commoditization of tokens. They onboard users, create culture, and experiment with attention economics. But the reality is that most tokens trend toward zero. From a long-term perspective, I prefer building durable systems over chasing volatility. There may always be a place for speculative tokens, but sustainable value will come from utility, community alignment, and real execution.
My closing thoughts on crypto are grounded in optimism. I’m excited about the builders. I’m excited about the open-source contributors quietly improving infrastructure. My advice is straightforward: be consistent. Keep learning. Keep building. Ship publicly. Don’t wait for perfect conditions.
For someone just starting out in crypto, start small and stay curious. Secure your keys. Study the basics. Follow builders, not influencers. Focus on understanding how value flows through systems. And most importantly, build something — even if it’s tiny. The fastest way to learn this space is to participate in it.





First investment: What was your first crypto purchase? What were you thinking at the time?
I saw sand at under a nickel and was like oh, I can’t get Square Enix or Steam or Atari or any of these other companies’ stock or tokens for a penny, for a nickel or for a dime entry, but they’re all collectively in sandbox and that coins under a nickel? Gotta do it. So I All in’d sandbox at under 5c rode that up to 8$

Who are you and what do you do in crypto?
Co-Founder of The World Seed / Co-Founder of Liquid NFT Marketplace / CEO ShadowThorn Studios / Writer / Gamification & Tokenomics Specialist / The Snuggle King

Your entry point: How did you first get involved in crypto?
I went to a ledger convention in Vegas that happened to be across the street from an event
I was already doing and was free, so I checked it out. I’d heard about blockchain, bitcoin, seen ethereum at 20$ and now at $2000 and was like, imma look into this.

What was the specific moment or conversation that hooked you?
The moment I realised Sandbox had secured $10 million from Square Enix for their creator fund, and that major gaming companies were getting involved.

What’s something you believed about crypto a few years ago that you now think differently about?
That blockchain gaming meant they were gonna do it right. I believed because all these gaming companies had made MMORPGs and had made these major fps and battle arena titles that when they came into web3, they’d inherently understand that their gold coin needs to become that flow. As a game studio youd think theyd be able to see killing a monster, completing a quest,

Tokin Trip @TripVoxel

Founder, Independent Artist and Entrepreneur
Location: USA
logging in every day, etc., is the “action”, the reward is the “gold coin and loot”, and throw a halvening system on to make the gold become scarcer as time goes on.

What do you think cryptocurrencies actually bring to finance and digital economies— beyond speculation?
Automated Point of Sale, Engagement-Based Rewards, Verification Layers for MRV systems, Tracking of Action, all kinds of things.

Where do you see the industry in a decade? What needs to happen to get there?
Likely everything will be crypto by then, but only if engagement currencies take centre stage sometime during that time.

What’s your outlook for BTC and ETH in 2026? Any other projects you’re watching closely?
I think BTC is a prototype. Personally, I think it’s supposed to be used as the example but
not the indefinite forever token, there’s no other industry of life we just “magically” created the best thing we could ever create as the human race, the first try, that isnt logical. Eth has smart contracts so I believe that has a way higher chance of being adopted and used by major financial tooling and institutions for automation of contract requirements in digital goods.

Do you prefer centralised or decentralised exchanges? Why?
Really, I dont think we should have exchanges at all. I think each app should have its own tokens, its own way to build the cash-out value through its monetisation modelling and the things it does as a company,

and exchanges aren’t really necessary and technically hurt all tokens that have ever launched on them.

What do you think about highly speculative tokens and community-driven projects? Do they help or hurt the industry in the long term?
Thats all kinda based off whats each person’s risk to reward ratio right, someone wants a higher reward and is willing to place a higher risk thats their own prerogative and choice, I focus mostly on ways to reduce
volatility & guarantee value, true mechanics to win not just hype cycle and pump n dump stuff I kinda avoid all that out here in web3.

What are you working on or focusing on in crypto right now?
I’m building The Liquid NFT Marketplace and working on something I’m under NDA for and can’t really talk about, but it’ll be a big one as well called The World Seed. Both of which are going to be separate industry-changing software for web3 that will hopefully give

people a great example of what is possible and how tokenomics should work for everyone.

What would you tell someone intelligent who’s just getting started in crypto today?
Remember to read, read every whitepaper, technical document and roadmap u can get ur hands on, take notes, and compare what u find with other things u find and then make your own determinations to what is missing or what is solid, and then go from there. Dont start by watching influencers and getting into all these bazillion chat rooms; learn the foundation first through reading and notes, then expand your knowledge from there.


@Alpha_vant
Name: Terry (Apex) X: @Apex Location: Africa
Occupation: Brand growth and visibility strategist for crypto projects

Could you please provide a brief introduction about yourself for the readers?
My name is Terry, but I’m popularly known as Apex. I help brands and crypto projects increase their visibility and grow their presence.
money. But I got a huge reality check when the very first token I invested in didn’t even last a full day after the presale. That experience definitely opened my eyes and taught me some hard lessons early on.
permission. At its core, it’s about access, freedom, and building new digital economies that anyone can tap into.

Where do you see the industry heading within the next decade?

How did you first get involved in crypto?
A friend of mine introduced me to crypto about three years ago through a project called $Bitchain. From that point on, I realised I had a knack for it, and I’ve been hooked ever since.

What was the reason you invested in crypto?
Haha, this is a good story. Like most people getting into crypto, I had that “instant and infinite money glitch” mindset at first. I thought it was going to be easy

Do you remember what your first purchase/ investment was?
A few years ago, I actually believed the government couldn’t get its hands on crypto. That’s definitely not true anymore.

What benefits do you think cryptocurrencies bring to finance and the future of digital economies?
It lets you move money freely, own your assets directly, and participate in a global financial system without needing
In a decade, I see crypto becoming part of everyday life, just like online banking. To get there, we need clearer regulations, simpler apps, real utility, and more education.

Which altcoin do you think will be the most notable by the end of 2025?
I feel the BTC and ETH rally in 2025 will be one of the most remembered, the kind of people look back on as a major turning point for the whole industry.
As for projects I’m watching, I’m
keeping a close eye on FUST. It stands out because of its strong utility through the Fusion Miner and its link to FUSD, an appreciating stabletoken model. If it continues executing well, it could play a very important role in the next phase of more stable, utility-driven crypto adoption.

Right now, I’m still of the opinion that decentralised exchanges need to improve their security. However, they’re great for long-term storage, while centralised exchanges are better for day-to-day transactions since they’re easier to use.

Do you think shitcoins/ meme tokens benefit the industry? Will there still be a place for them in the future?
In the long term, I believe community-driven tokens will be a big part of the industry. That’s how crypto is meant to be: a group of people coming together to push an idea they truly believe in, regardless of race, ethnicity, or religion.
Highly speculative tokens can sometimes create noise and short-term hype, but strong communities bring real staying power, adoption, and organic growth, which ultimately helps the industry mature over time.


Decentralised exchanges need to improve their security
Tell me some closing thoughts on your plans for crypto.
Right now, I’m focused on supporting projects that I believe can bring real change and have a positive impact in the world. I strongly believe FUST and FUSD have that kind of potential, especially with their focus on sustainable utility, stability, and long-term value rather than just short-term hype.

Lastly, what are some brief words of advice for someone just starting out in crypto?
Capital preservation is everything. When you make money in crypto, diversify.
The longer you stay in the game, the easier it becomes for you to get lucky and spot good opportunities.

Tokenomics is not a feature. It is not a marketing layer. It is not a line item in a pitch deck.
Tokenomics is the heart and soul of a project. It defines what people are rewarded for, what behaviour is encouraged, what value is preserved, and what inevitably collapses.
If your tokenomics are broken, nothing built on top of them matters.

Tokin Trip @TripVoxel
Most Web3 projects make the same fatal assumption: “If we launch a token and people buy it, value will follow.”
That assumption ignores one simple, unavoidable truth: every token that must be sold to fund operations becomes sell pressure.
Let’s break this down.
Projects often talk about “utility” while designing systems that force selling at every layer.
1. Tokens Sold at Launch = Immediate Security Behaviour
ICOs, IDOs, IPO-style public launches, pre-register whitelists, discounted early access - these all do the same
thing. They sell future utility up front. That is the definition of a security, whether legally acknowledged or not.
People didn’t earn the token by using the system. They bought it hoping someone else would pay more later. That is not an economy. That is a distribution event.
2. VCs Paid in Tokens Will Sell Them
Vesting schedules don’t change this reality. VCs are not charities. Their job is to exit.
Even with long cliffs and slow unlocks, tokens are still sold, liquidity is still drained, and charts still trend downward. Vesting delays impact, not direction.
3. Teams Paid in Tokens Must Cash Them Out
Payroll is not optional. If your developers, designers, marketers, or operators are paid in your token, they face a simple reality: rent is paid in fiat, groceries are paid in fiat, taxes are paid in fiat.
Which means your token is sold.
4. Marketing Budgets Funded by Tokens Create Constant Sell Pressure
If your marketing budget comes from treasury tokens, incentive pools, or emission rewards,
those tokens must be liquidated to buy ads, influencers, events, and media placements.
Again: selling.
5. “Impact” Programs Paid in Native Tokens Still Sell
Tree planting. Carbon credits. Charity. Sustainability. If the receiving party doesn’t operate on your token, they sell it immediately at market.
Good intentions don’t change market mechanics.
The Math No One Wants to Admit
When you add it all up - VC exits, team payroll, marketing spend, operational costs, impact initiatives, early buyers

taking profit - you often end up with 70-90% of tokens being sold versus 10-30% being held or accumulated.
Price doesn’t fall because people “don’t believe.” It falls because the system requires selling to function.
Tokens Were Never Meant to Be
Here’s the uncomfortable truth: if your token must be sold to keep the lights on, it is not money - it is inventory.
Real economies don’t work like that.
The Correct Model: VaultFirst Tokenomics
Tokens should not be sold into existence. They should be earned into circulation.
Core Principle: All tokens start in a vault. None are pre-sold.
No ICO. No IDO. No public dump disguised as “community access.”
Tokens Are Earned Through Action
Tokens enter circulation only through interaction, engagement, participation, contribution, and verified activity.
This turns the token into a proof of work, a proof of
participation, a proof of value creation - not a speculative chip.
The vault follows a halvening schedule. Rewards decrease as adoption grows. Early contributors are rewarded for risk. Late participants enter a mature economy.
This mirrors Bitcoin’s issuance logic, real resource scarcity, and long-term sustainability. No emissions forever. No inflationary death spiral.
Here is the critical separation most projects miss: engagement does not equal liquidity.
Liquidity comes from revenue, not emissions.
All revenue streams flow into a Cash-Out Vault - subscriptions, platform fees, marketplace fees, ads, licensing, and services. All in stablecoin.
This vault exists for one purpose: to buy back value created by the system.
In this model, the token is a claim on participation, a unit of interaction, a representation

of contribution - not a funding mechanism.
When users cash out, they exit through the stablecoin vault, not through dumping on each other. This removes reflexive selling from the market.
When tokens are earned rather than bought, you create something powerful: a verifiable interaction economy.
Every token is tied to real behavior. Engagement is provable. Activity is auditable. Participants are human-verified through KYC.
Now advertisers don’t buy impressions. They buy guaranteed interaction with real humans.
Advertisers don’t want bots, wash trading, fake wallets, or empty metrics. They want verified humans, measurable engagement, and conversion-
driven actions.
When engagement is the minting mechanism, fraud becomes expensive, value becomes real, and attention becomes an asset.
Most token economies fail because they confuse selling access with creating value, liquidity events with economic systems, and speculation with sustainability.
A token should not exist to be sold. It should exist to measure, reward, and route human interaction.
When you design around that truth, price stabilizes, utility becomes real, regulation becomes clearer, and value stops leaking out of the system.
Tokenomics is not the appendix. It is the spine.
And if your foundation is wrong, your project will fail. This is a proven truth, so design them right.




