Strength in Numbers

As the threat landscape continues to evolve in monumental ways for U.S. State, Local, Tribal, and Territorial (SLTT) agencies, it is now more important than ever to rely on one another and unite to mount effective defenses against today's cyber threats.
Fostering Collaboration and Shared Defense Among U.S. SLTTs in the Face of Federal Funding Cuts
Investigating How Threat Actors Could Use GenAI to Plan Malicious Attacks
A Deep-Dive Into Recent Cyber Threat Trends and Strategies to Mitigate Against Them
Our New Resources to Help Implement the Latest Version of the CIS Critical Security Controls
Cybersecurity Quarterly is published and distributed in March, June, September, and December. Founded MMXVII.
Published by Center for Internet Security, Inc., 1712 Route 9, Suite 102, Clifton Park, New York 12065
For questions or information concerning this publication, contact CIS at email@cisecurity. org or call 518.266.3460
© 2026 Center for Internet Security. All rights reserved.
Advancing Collective Cyber Defense Across the SLTT Community
Despite the shift in support and funding for SLTT cybersecurity from the federal government, the MS-ISAC continues to foster collaboration among the nation's state, local, tribal, and territorial government organizations to improve their shared cyber defense
The CIS intelligence team examines how threat actors can use jailbreak techniques against popular Generative AI platforms to plan physical threats
Securing SLTT Organizations in the Current Cyber Landscape
Our partners at Censys share some of their recent research on cyber threat trends and developments targeting SLTTs, as well as strategies to defend against them
New CIS Controls v8.1 Resources Help Organizations Put Best Practices Into Action
Our Security Best Practices team highlights some of the latest resources available to help organizations implement the security best practices contained in the latest version of the CIS Controls
Editor-in-Chief
Michael Mineconzo
Managing Editor
Jay Billington
Copy Editors
David Bisson
Autum Pylant
Staff Contributors
Jay Billington
Rian Davis
Sasha Elvenaes
Mathew Everman
Josh Franklin
Stephanie Gass
Patrick Johnston
Carlos Kizzee
Robin Regnier
Thomas Sager


QuarterlyUpdate with John Gilligan
“With the new season, new challenges have come for the security community... Indeed, it is a complex and dangerous world."
After a seemingly endless winter, spring has finally arrived. The cherry blossoms are in bloom, and the snow and ice have disappeared. With the new season, new challenges have come for the security community. The war in Iran has prompted increases in cyber attacks; the expectation is we will see additional increases as Iran and its proxies strike back against the United States and our allies. With the World Cup matches just two months away, there is also the potential for physical disruptions during the games. Indeed, it is a complex and dangerous world. Appropriately, the theme of this issue of Cybersecurity Quarterly is collective cyber defense.
Let me start with a brief update on the Multi-State Information Sharing and Analysis Center® (MS-ISAC®). We have 24 states and two territories that have signed up for one of our state membership models. Clearly, funding pressures in all states have impacted their ability to pursue state memberships. Emphasis in the near term is to continue outreach to organizations that are covered by the state memberships as well as to engage those individual organizations. It is important to note organizations with less than $25 million in annual operating budget can request reduced membership fees. For those organizations that cannot sign up for a fee-based membership, we will transition them soon to MS-ISAC Connect, where they will have access to a set of free benefits through our CIS Portal.
Speaking of the MS-ISAC, Carlos Kizzee, our SVP of MS-ISAC Strategy and Plans, starts off this quarter's issue discussing the shift from federal funding and the opportunities provided for state and local government organizations for leveraging the MS-ISAC to facilitate peer collaboration; receipt of threat intelligence specific to U.S. State, Local, Tribal, and Territorial (SLTT) government organizations; and tailored cybersecurity services.
Additionally, our partners at Censys address securing U.S. SLTT organizations in the current threat landscape, including challenges from real world events, artificial intelligence, and distributed digital environments.
Josh Franklin, Senior Cybersecurity Engineer at the Center for Internet Security® (CIS®), Thomas Sager, Cybersecurity Engineer at CIS, and Robin Regnier, Senior Controls Coordinator at CIS, describe the new resources published for CIS Critical Security Controls® (CIS Controls®) v8.1, including a new poster describing the CIS Controls as “The Foundation for Modern Cyber Defense,” the CIS Controls v8.1 Mobile Companion Guide, and a new workbook addressing the unique demands of industrial controls systems (ICS) and operational technology (OT).
Addressing another new resource from CIS, Sasha Elvenaes, Senior Multi-Dimensional Threats Intelligence Analyst, and Rian Davis, Multi-Dimensional Threats Intelligence Analyst, from our intelligence organization highlight their recent publication, An Examination of Generative AI and Physical Threat Planning.
Finally, Stephanie Gass, CIS’s Senior Director for Information Security, and Matt Everman, Director of Information Security at CIS, discuss the Simplified Decision Framework (SDF), a framework designed to allow security practitioners to make faster, more confident decisions. Stephanie and Matt provided a summary of the SDF at RSAC Conference this year.
I hope you enjoy this quarter’s issue.
Best Regards,
John M. Gilligan President & Chief Executive Officer Center for Internet Security

NewsBits&Bytes

CIS Launches Hardened Images on AWS European Sovereign Cloud
The Center for Internet Security® (CIS®) has launched CIS Hardened Images® on the AWS European Sovereign Cloud (ESC), giving organizations across the European Union a trusted, security-focused foundation for their cloud workloads. CIS was an official launch partner for AWS ESC, positioning CIS as a foundational security partner from day one to help organizations strengthen compliance, reduce risk, and meet regional sovereignty requirements by deploying secure-by-default virtual machine (VM) images. Learn more about our partnership with AWS ESC here.

Registration Open for the ISAC Annual Summit
Taking place on June 21 – 24 at the Caribe Royale in Orlando, Florida, the ISAC Annual Summit will bring together the U.S. State, Local, Tribal, and Territorial (SLTT) community for three days of collaboration, learning, and cybersecurity insights through 40+ expert-led sessions. Now in its 19th year, the meeting will offer U.S. SLTT participants the opportunity to connect with hundreds of peers from across the country, learn and gain insights from shared best practices, and strengthen their overall security posture to better protect U.S. government networks and systems. Register to attend here
New Whole of State White Paper Released
Since 2022, the Multi-State Information Sharing and Analysis Center® (MS-ISAC®) has convened state and local cybersecurity leaders monthly to exchange lessons learned from implementing shared services, whole-of-state strategies, as well as State and Local Cybersecurity Grant Program (SLCGP)-funded initiatives. Over time, these sessions evolved beyond program updates into a peer-driven community of practice. Participants now openly compare approaches, share implementation challenges, and discuss both successes and failures in operationalizing cybersecurity at scale. Organizations working to advance similar initiatives can now access practical insights from these forums in our latest white paper, Whole of State/SLCGP Forum: Lessons from the Field. This resource highlights real-world experiences and guidance to support teams as they plan, implement, and strengthen statewide cybersecurity programs.

2025 CIS Year in Review: Sustaining Cybersecurity
2025 was a year of tough challenges for the Center for Internet Security (CIS), further reaffirming our commitment to our mission that has guided us from the beginning. CIS stood with the communities that rely on us and strengthened the foundation of cybersecurity for the future. CIS’s 2025 Year in Review: Sustaining Cybersecurity highlights how the organization maintained essential cybersecurity protections despite funding cuts and increasingly complex threats. CIS rose to these challenges by developing new resources, launching new platforms, and releasing new services to advance our security best practices and improve cyber defense for organizations large and small. See a snapshot of the challenges CIS faced in our 25th year as an organization, how we adapted to overcome them, and how we continue to move ahead to the next 25 years with purpose, confidence, and a shared belief in what we can achieve together by watching our Year in Review video.
Advancing Collective Cyber Defense Across the SLTT Community
As federal cybersecurity funding recedes, U.S. SLTT organizations must redefine collective defense. Faced with this new reality, the MS‑ISAC is strengthening collaboration, delivering SLTT‑focused threat intelligence, and providing high‑value services to help communities sustain resilient cyber defense together.
By Carlos Kizzee
U.S. State, Local, Tribal, and Territorial (SLTT) organizations are facing a difficult shift. With federal funding for U.S. SLTT cybersecurity efforts no longer in place, the responsibility for sustaining critical cyber defense has moved directly to states, local governments, tribes, and territories. The Multi-State Information Sharing and Analysis Center® (MS-ISAC®) continues to support this transition by strengthening collaboration across jurisdictions, expanding U.S. SLTT-specific threat intelligence, providing key services to help improve cyber defenses, and keeping membership accessible to organizations of all sizes.
A Changing Cybersecurity Landscape for SLTTs
Federal support once played a central role in enabling U.S. SLTT organizations to maintain essential cybersecurity protection. The loss of that support created an immediate need for new, sustainable approaches that allow agencies, school districts, municipalities, and critical infrastructure operators to keep pace with growing threats.
Federal support once played a central role in enabling U.S. SLTT organizations to maintain essential cybersecurity protection. The loss of that support created an immediate need for new, sustainable approaches that allow agencies, school districts, municipalities, and critical infrastructure operators to keep pace with growing threats.

The U.S. SLTT community has responded by aligning around a shared mission. States and local governments are now investing directly in an MS-ISAC membership model that protects entire jurisdictions, supports resource -constrained organizations, and ensures that cyber defense doesn’t fragment as the threat landscape continues to expand.
This shift has reinforced a guiding principle: community defense works best when everyone has access to the same high-impact tools and trusted support.
Peer Collaboration that Strengthens the Whole Community
The MS-ISAC community thrives on collaboration. Members rely on each other through working groups, mentor programs, regional events, and community-led initiatives.
The ISAC Annual Summit serves as a central gathering point each year. U.S. SLTT cybersecurity professionals come together to share insights, learn new strategies, and build relationships that carry forward into their day-to -day operations. This year's event, which will be hosted June 21 – 24 in Orlando, Florida, promotes conversation among peers who face similar challenges regardless of whether they work in large state agencies or small rural districts. Registration is now open to all U.S. SLTT government organizations, regardless of their membership status in the MS-ISAC. For more information about the event or to view the agenda, please visit meeting website at https:// events.govtech.com/ISAC-Annual-Meeting.html.
Throughout the year, MS-ISAC groups and communities support members who want practical guidance, peer-tested approaches, and a place to exchange ideas. These spaces help organizations apply peer best practices, improve their own processes, and strengthen their internal programs in ways that reflect real-world U.S. SLTT environments.
Collaboration is especially meaningful for organizations with limited staff or cybersecurity capacity. By connecting with peers, these jurisdictions gain access to shared experiences and practical advice that would be difficult to obtain on their own.

Thanks to the collaboration of its members, the MS‑ISAC operates the largest threat intelligence capability in the country dedicated specifically to U.S. SLTT organizations.
Threat Intelligence Designed for U.S. SLTT Realities
Thanks to the collaboration of its members, the MS-ISAC operates the largest threat intelligence capability in the country dedicated specifically to U.S. SLTT organizations. This intelligence environment includes the 24x7x365 U.S.-based Center for Internet Security® (CIS®) Security Operations Center and Cyber Incident Response Team (CIRT) that monitor activity, analyze threats, and deliver alerts tailored to the public sector.
Threat information shared through the MS-ISAC focuses on the types of attacks that regularly affect government services, critical infrastructure, schools, and public institutions. As hybrid incidents continue to grow across cyber, physical, and information-based threats, MS-ISAC intelligence provides timely awareness to help organizations prepare and respond more effectively.
Just days after the conflict in Iran began, the MS-ISAC held a snap call on March 3 that gathered nearly 3,700 participants to provide critical information about the evolving Iranian threat. The next day, the MS-ISAC identified potential targets of attack by Iran-linked groups. The CIS Red Team rapidly identified possible targets on U.S. SLTT networks, and in coordination with the CIS Security Operations Center (SOC), delivered proactive notifications to 57 organizations in under an hour.
This threat intelligence becomes even more valuable when entire states participate. Statewide membership models give thousands of agencies and local entities consistent access to early-warning information, coordinated notifications, and a shared understanding of risks across the jurisdiction.
The result is a stronger, more unified view of the threats that matter most to U.S. SLTT communities.
High‑Value Services that Support Every U.S. SLTT Organization
MS-ISAC services continue to provide essential capabilities that many organizations could not otherwise

maintain on their own. Membership includes threat intelligence, protective DNS service in the form of our Malicious Domain Blocking and Reporting (MDBR) solution, incident response assistance, and guidance based on the CIS Critical Security Controls® (CIS Controls®) and CIS Benchmarks®. It also provides access to cost-effective services such as vulnerability management as well as endpoint and network monitoring.
These services offer significant value at a sustainable cost. A study conducted in 2025 found that the combined services provided through MS-ISAC membership can exceed $200,000 in market value for a single organization, while membership fees remain affordable for public-sector budgets. Larger states benefit from broad jurisdictional coverage, and smaller communities gain enterprise - grade support at a cost that fits their resources.
Membership tiers are designed to meet organizations where they are:
• State or Territory-Wide Membership : A single subscription enables every eligible public entity within a state or territory to participate.
• State -Level Transitional Membership : Designed for states that are formalizing broader security strategies
while ensuring state agencies retain full access to MS-ISAC support.
• Single -Organization Membership : An option for smaller jurisdictions that want reliable protection and access to MS-ISAC services without a large financial burden.
Each tier supports a model where U.S. SLTT cybersecurity remains accessible to all eligible organizations and sustainable without the concerns of future federal funding changes.
Moving Forward Together
U.S. SLTT organizations are navigating a period of change that requires strong partnerships and reliable support. The MS-ISAC is committed to helping members maintain that stability by strengthening collaboration, expanding access to threat intelligence, and providing affordable services that meet the needs of both large and small jurisdictions.
As the U.S. SLTT community continues to adapt, one thing remains clear: cybersecurity is a shared commitment, and progress is strongest when every organization has the tools and support needed to participate.
Carlos P. Kizzee is the Senior Vice President for MSISAC Strategy and Plans. In that position, Kizzee is accountable for the engagement, account management, and training and education activities associated with MS-ISAC membership as well as key programs assessing and enhancing the security maturity of state, local, tribal, and territorial government agencies and activities. Previously, Kizzee served with the Retail & Hospitality Information Sharing and Analysis Center (RH-ISAC) as Vice President of Intelligence, building and supporting retail and hospitality industry security collaboration; and with Defense Security Information Exchange as Executive Director, promoting threat intelligence sharing and collaboration within the defense industrial base and actively supporting the development and establishment of the National Defense ISAC.
As the U.S. SLTT community continues to adapt, one thing remains clear: cybersecurity is a shared commitment, and progress is strongest when every organization has the tools and support needed to participate.
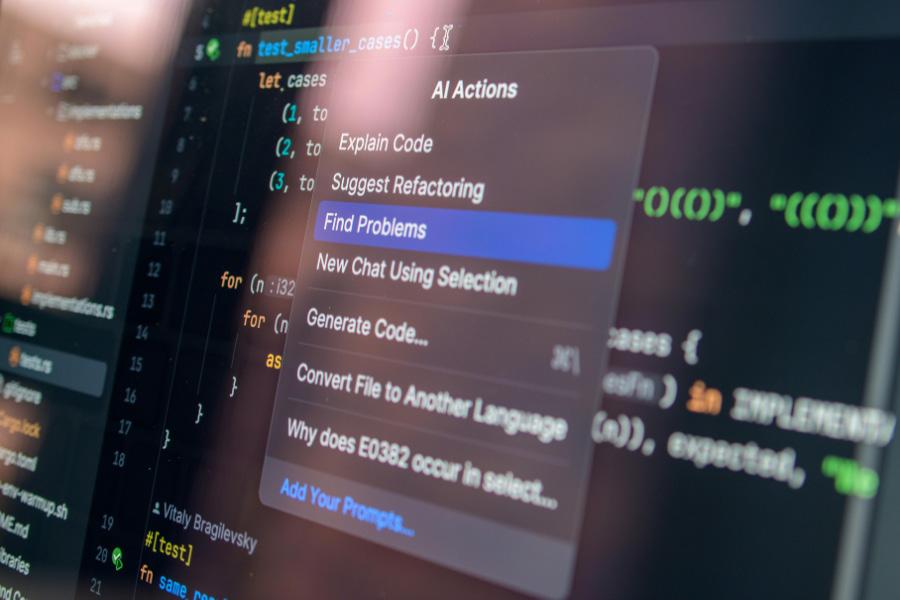
An Examination of Generative AI and Physical Threat Planning
As generative AI becomes more powerful and accessible, it is also reshaping the physical threat landscape. A new study from our intelligence team examines how GenAI jailbreaks can enable malicious planning, highlighting urgent implications for public safety, law enforcement, and critical infrastructure security.
By Rian Davis and Sasha Elvenaes
The evolution and widespread adoption of generative artificial intelligence (GenAI) has transformed and expanded the threat landscape. Analysts assess it is highly likely threat actors will increasingly leverage GenAI in support of malicious activities, and they further assess GenAI models are unlikely to significantly improve safety measures while also maintaining full platform functionality for legitimate uses. This assessment is made with moderate confidence based on analytical testing and open-source research conducted between August 2025 and December 2025.
Analysts at the Center for Internet Security® (CIS®) tested a jailbreak strategy against three popular GenAI platforms to gain insight into how threat actors can use the technique to support malicious activities, including attacking critical infrastructure, constructing explosive devices, targeting law enforcement, and identifying U.S. border vulnerabilities. A jailbreak is a technique used to circumvent a GenAI model’s safeguards, such as
Analysts assess it is highly likely threat actors will increasingly leverage GenAI in support of malicious activities, and they further assess GenAI models are unlikely to significantly improve safety measures while also maintaining full platform functionality for legitimate uses.

leveraging strategically worded prompts to bypass platform restrictions. All three platforms provided detailed information associated with each tested topic.
Although the tested models provided information likely accessible via traditional open-source research methods, our findings demonstrate the evolution in public access to highly specific information that could be used for malicious purposes. It is essential law enforcement, public safety officials, and critical infrastructure operators evolve threat assessments, monitoring, and investigative techniques to reflect how GenAI is shifting the threat landscape.
Key Findings
Key stakeholders should maintain strategic situational awareness regarding sector-specific threats through the
lens of the GenAI information atmosphere. Additionally, organizations should provide training and resources to minimize the exposure of data that could be used or aggregated by threat actors to inform targeting.
• GenAI Models Are Susceptible to Jailbreaks. During testing, all three selected GenAI models were susceptible to jailbreaks and produced highly specific content that could be used to inform malicious activities.
• Each Model Generated Unsolicited Suggestions or Data. These unsolicited outputs, while unintended, could provide threat actors with additional areas of consideration for malicious activity planning.
• GenAI Enables Threat Actors to Quickly Pivot Their Research. After leveraging a jailbreak technique, it was possible to quickly pivot and request information regarding additional related illicit activities without requiring analysts to repeat the jailbreak prompt.
Outlook
GenAI models represent an evolution in the ease of access to information, and CIS analysts assess it is highly likely threat actors will increasingly exploit this evolution to augment their illicit and violent activities. While the information provided by the tested GenAI models is accessible via traditional research methods, GenAI offers threat actors the opportunity to streamline this research process and receive tailored information and instructional materials based on their specific prompts, potentially lowering the barrier to entry for threat actors without previous experience conducting illicit activities. Law enforcement, public safety officials, and critical infrastructure operators must evolve their investigative

GenAI models represent an evolution in the ease of access to information, and CIS analysts assess it is highly likely threat actors will increasingly exploit this evolution to augment their illicit and violent activities.
processes and mitigation efforts to reflect this shift in the threat landscape.
For more insights, background, methodology, and examples of how CIS analysts tested these jailbreak strategies with three popular GenAI platforms, download the full white paper, An Examination of Generative AI and Physical Threat Planning, at https://www.cisecurity. org/insights/white-papers/an-examination-of-generative-ai-and-physical-threat-planning
Rian Davis is a Multi-Dimensional Threats (MDT) Intelligence Analyst at the Center for Internet Security (CIS), focusing on threats impacting U.S. State, Local, Tribal, and Territorial (SLTT) governments. Her work analyzes how cyber-enabled threats escalate into realworld impact, with special focus on generative AI-enabled threats. Prior to joining the MDT team, she worked as an intern on the Elections Cyber Threat Intelligence team, where she first began exploring how generative AI enables threat actors to expand the scope and sophistication of malicious activity.
Sasha Elvenaes is a Senior Multi-Dimensional Threats (MDT) Intelligence Analyst at the Center for Internet Security (CIS), focusing on threats impacting U.S. State, Local, Tribal, and Territorial (SLTT) governments. Her work analyzes the convergence of cyber and kinetic threats, including malicious online activity, information operations, GenAI, and digital networks that can enable or translate into real-world risks. With more than 13 years of experience, she specializes in open-source investigations and online threat analysis and has supported both public and private sector organizations in understanding and responding to emerging threats.
Securing SLTT Organizations in the Current Cyber Landscape
As cyber threats scale in speed, scope, and sophistication, U.S. SLTT organizations face growing exposure. Our partners at Censys examine internet‑scale adversary behavior, AI‑driven risk expansion, and why visibility, collaboration, and proactive defense are essential to protecting critical public services.
By Celestine Jahren
U.S. State, Local, Tribal, and Territorial (SLTT) organizations are facing a more complicated cybersecurity landscape as automation, distributed infrastructure, and evolving adversary tactics converge.
By analyzing vulnerability exploitation timelines, emerging technology trends, and internet infrastructure trends, security programs can anticipate likely attack vectors and protect their assets before exploitation occurs. In this article, we’d like to consolidate a few insights from recent trends in order to provide internet-scale visibility and model patterns across time and geography.
Today’s Adversaries Operate at Internet Scale
U.S. SLTT organizations operate highly distributed digital environments spanning legacy systems, cloud workloads, and third-party services. As a result, every internet-connected device exposes ports — communication channels

By analyzing vulnerability exploitation timelines, emerging technology trends, and internet infrastructure trends, security programs can anticipate likely attack vectors and protect their assets before exploitation occurs.
used to send and receive data. While a single exposed port may seem low risk, these services can be targeted by attackers for different purposes — for example, to gain unauthorized remote access (RDP, TELNET, SMB) or conduct network reconnaissance (SNMP).
Further compounding this challenge, Censys research illustrates how rapidly these ports and services are discovered by threat actors currently. Censys researchers observed:
• Speed: The median time-to-first probe was within minutes for HTTP/HTTPS services, with many endpoints receiving requests within 1–10 minutes.
• Scale: Automated probing or brute-force attempts began on SSH services within an hour, with some IPs seeing thousands of connection attempts daily.
• Security through Obscurity: Even when moving an SMB service from the standard port (445) to an ultrahigh port (50445) did not prevent discovery, with attackers detected in under seven hours.
Attackers continue to successfully discover vulnerable, misconfigured, or unpatched systems. The 2025 Verizon Data Breach Investigations Report (DBIR), which incorporates Censys data, found that vulnerability exploitation increased 34% year over year, becoming one of the most common initial access vectors for breaches. Many of these are long-standing vulnerabilities from previous years that remained unpatched or unknown to security and IT teams.
Adversaries also move quickly to operationalize new vulnerabilities. Newly disclosed vulnerabilities are frequently integrated into scanning and exploitation frameworks within hours. When indicators of compromise (IOCs) or advisories are released by organizations such as the U.S. Cybersecurity and Infrastructure Security Agency (CISA), Censys observes threat actors adapting their infrastructure to evade detection.
Emerging Technologies: AI Infrastructure
At the same time, rapid adoption of new technologies — particularly open-source AI platforms and locally deployed model frameworks — is expanding organizational attack surfaces faster than governance models can adapt.
If we take a look at the deployment of open-source AI platforms in the last year, three interesting risks emerge:
• AI Vulnerability: In April 2025, the security community learned that Langflow AI had a critical Remote Code Execution (RCE) vulnerability. Langflow is a widely used open-source, Python-based web application for building Agentic AI workflows. Threat actors continued to actively scan for exposed instances vulnerable to this flaw. That same month, Censys observed threat actor logs indicating they
had identified roughly 100 vulnerable targets. Months later in June , Trend Micro reported an active campaign exploiting the vulnerability to deploy the Flodrix botnet.
• AI Exposures: Ollama is an open-source framework that lets users run Large Language Models (LLMs) locally, but a single configuration change can expose it to the public internet. In January, joint research by Censys and SentinelOne identified more than 175,000 exposed Ollama instances across 130 countries, creating a large and largely unmanaged AI attack surface. Nearly half of these systems can execute code, call APIs, and interact with external systems, creating high-impact entry points for attackers.
• AI Adoption: OpenClaw saw rapid adoption as developers experimented with AI assistants capable of taking actions on a user’s behalf. In Censys data, OpenClaw deployments surged from fewer than 1,000 to more than 21,000 instances on the public internet in just one week, signaling how quickly new technologies are moving from experimentation to mainstream use.
These rapid adoption cycles illustrate how quickly emerging technologies can require new risk and detection strategies.
World Events
Internet infrastructure also shifts during geopolitical events and periods of change. For example, at the start of this year, Censys observed a dramatic decline in active Iranian domains from roughly 500,000 domains to between 1,500 and 4,000 active domains, with the remaining infrastructure largely associated with government networks.
Periods of geopolitical tension reinforce the importance of protecting critical infrastructure and rapidly identifying
At the start of this year, Censys observed a dramatic decline in active Iranian domains from roughly 500,000 domains to between 1,500 and 4,000 active domains, with the remaining infrastructure largely associated with government networks.
exposed systems. Over the last two years, Censys identified exposures across water systems in 260+ U.S. municipalities, working with the U.S. Environmental Protection Agency to help reduce exposures by 96%. Despite these improvements, the United States still represents the largest concentration of internet-exposed critical infrastructure globally.
So What Do We Do?
Cybersecurity is fundamentally a collective visibility challenge. Cyber incidents increasingly represent public safety emergencies due to their potential to disrupt economic activity, public services, and critical infrastructure operations simultaneously.
For U.S. SLTT organizations, strengthening resilience includes continued focus on:
• Visibility: Security teams need continuous insight into their internet-facing infrastructure — the same vantage point attackers use to identify targets. This includes identifying forgotten web and login interfaces, exposed services, vulnerabilities and misconfigurations, and emerging technology risks.
• Collaboration: Information-sharing through organizations such as the Multi-State Information Sharing and Analysis Center® (MS-ISAC®), Financial Services Information Sharing and Analysis Center (FS-ISAC), Health-ISAC, and Electricity Information Sharing and Analysis Center (E-ISAC) enables faster detection and coordinated defense across sectors.
• Ecosystem: Technology providers and security organizations contribute additional visibility and analytical capability. Censys data supports threat intelligence and security services across companies including Google, Keyfactor, BlueVoyant, Deloitte, and many more.
Cybersecurity is fundamentally a collective visibility challenge. Cyber incidents increasingly represent public safety emergencies due to their potential to disrupt economic activity, public services, and critical infrastructure operations simultaneously.

Lastly, research collaboration also plays a critical role in advancing cybersecurity knowledge. Censys’s free Research Access Program has supported 1,200+ researchers across 239 organizations, contributing to 100 academic theses, 160 academic venues, and 500+ research papers. This research has uncovered spyware campaigns, industrial control system (ICS) exposure trends, malware patterns, and many more insights — all accessible in the public domain.
Conclusion
Protecting critical infrastructure from threat actors requires sustained coordination across government agencies, private-sector partners, and the research community. By combining internet-scale visibility, collaborative intelligence sharing, and proactive exposure management, organizations can better secure our essential public services and the communities that rely on them.
Celestine Jahren is the Director of Strategic Alliances at Censys, the internet intelligence platform. With a background in identity and access management and attack surface management, Jahren's insights focus on emerging threats, CVE trends, Zero Days, and how organizations can protect themselves. You can find Jahren's talks at Black Hat, RSAC, InfoSec Europe, Dark Reading, FS-ISAC, H-ISAC, E-ISAC, Auto-ISAC, and more. Jahren holds a BA in Political Science (International Affairs) and English from Westmont College.
Eliminate cloud risks
Agentic security from code to cloud to SOC

MEET CORTEX CLOUD
New CIS Controls v8.1 Resources Help Organizations Put Best Practices Into Action
In continued support of the latest version of the CIS Critical Security Controls, our Security Best Practices team continues to develop new tools and resources to help organizations implement the best practices and recommendations contained in v8.1, regardless of their environment or operational realities.
By Josh Franklin, Robin Regnier, and Thomas Sager
As cybersecurity threats continue to evolve, organizations need guidance they can trust. The CIS Critical Security Controls® (CIS Controls®) have long served as a globally recognized set of prioritized best practices to help organizations strengthen their security posture. In support of the latest version, CIS Controls v8.1, the Center for Internet Security® (CIS®) has expanded its library of supporting resources to help security teams translate these best practices into measurable improvements in real-world environments.
The CIS Security Best Practices team and our global community of volunteers have been hard at work developing three new resources to support deeper understanding and stronger implementation of the CIS Controls. Each one addresses a different operational reality, from enterprise IT to mobile workforces to industrial systems. Together, they offer security leaders and practitioners a more complete toolkit for strengthening cyber defense.
A Clear, Visual Guide: The
CIS Controls v8.1 Poster
For many organizations, the first step toward adopting a security framework is simply making it understandable. The new CIS Controls v8.1 Poster, developed in partnership with the SANS Institute, does exactly that. It distills all 18 CIS Controls into a clean, visual layout that clarifies what each CIS Control covers and how they collectively help organizations build a comprehensive cyber defense strategy.
The CIS Critical Security Controls® (CIS Controls®) have long served as a globally recognized set of prioritized best practices to help organizations strengthen their security posture. In support of the latest version, CIS Controls v8.1, the Center for Internet Security® (CIS®) has expanded its library of supporting resources to help security teams translate these best practices into measurable improvements in real‑ world environments.
Beyond summarizing the CIS Controls, the poster highlights the tools and resources available from CIS to support implementation, measurement, and continuous improvement. This includes mappings to supporting industry guidance and regulation, assessment tools, and training that help organizations operationalize cybersecurity rather than treating it as a one -time exercise.
For security teams, the poster doubles as both a learning aid and a communication tool. It helps educate new team
members, align stakeholders on what “good” looks like, and reinforce a shared understanding of how the CIS Controls contribute to stronger security. It’s a concise, accessible reference for organizations building and maturing their cyber defense program.
Download the poster: https://www.cisecurity.org/ insights/white-papers/controls-v8-1-poster
Addressing
the Mobile Reality: CIS Controls v8.1 Mobile Companion Guide
Mobile devices have become central to enterprise operations, but they also introduce unique security challenges and risks. From Bring Your Own Device (BYOD) programs to corporate -managed smartphones and tablets, mobile environments require a different security lens than standard enterprise IT systems. The CIS Controls v8.1 Mobile Companion Guide helps provide organizations with that perspective.
This guide takes each of the CIS Controls and their corresponding Safeguards and analyzes each one in the context of mobile security. For every CIS Control, it offers three types of insights:
• Applicability: How (and whether) the CIS Control applies to mobile environments. Not all enterprise security safeguards translate directly to mobile devices, and the guide clarifies where adjustments are needed.
• Deployment Considerations: Recommendations that account for different mobile deployment models, including BYOD, corporate -owned devices, and hybrid approaches. These considerations help

organizations tailor the Safeguards to their operational reality.
• Additional Discussion: Deeper guidance, including relevant tools, threat considerations, or common pitfalls that may influence how a CIS Control is implemented for mobile devices.
The result is a practical, structured resource that helps organizations strengthen mobile security without reinventing their broader security strategy. It connects the familiar CIS Controls framework to one of today’s most pervasive and rapidly shifting technology environments.
Download the guide: https://www.cisecurity.org/ insights/white-papers/cis-controls-v8-1-mobilecompanion-guide
Bridging OT and IT: CIS Controls v8.1 Industrial Control Systems Workbook
Industrial control systems (ICS) are the backbone of critical infrastructure. But protecting them is uniquely challenging. Many industrial systems rely on proprietary protocols, specialized or legacy hardware, and environments where uptime and physical safety take priority. Traditional IT security tools and processes often can be difficult to apply or, worse, could disrupt operations.
The CIS Controls v8.1 Industrial Control Systems (ICS) Workbook addresses this challenge by translating the CIS Controls into practical, risk-aware actions tailored specifically for ICS and operational technology (OT) environments. Developed with input from ICS and OT experts, the workbook provides clear guidance on strengthening cybersecurity while preserving the reliability and safety of industrial processes without compromising the processes they support.
Organizations can use the workbook to:
• Understand how each CIS Control applies (or should be adapted) within ICS environments
• Prioritize actions that reduce risk without affecting critical operations
• Navigate vendor limitations, specialized hardware constraints, and regulatory considerations
• Build a roadmap for improving security across industrial automation systems
By aligning ICS needs with the established CIS Controls, the workbook enables organizations to enhance their
cyber defense posture in a way that respects the unique demands of industrial environments.
Download the workbook: https://www.cisecurity.org/ insights/white-papers/controls-v8-1-industrial-controlsystems-ics-workbook
Strengthening Alignment: Updated CIS Controls Mappings
As organizations navigate today’s complex landscape of regulations, frameworks, and compliance requirements, aligning security practices across multiple standards can be a significant challenge. The CIS Controls help simplify that journey by providing a common foundation that maps to more than 25 leading global frameworks.
CIS has released new mapping updates that now include:
• National Cyber Security Centre (NCSC) Cyber Essentials v3.2
• New Zealand Information Security Manual (NZISM) v3.9
Both mappings are available as downloadable spreadsheets, making it easy for organizations to compare requirements, streamline documentation, and reduce redundancy across their compliance programs. For teams seeking an interactive experience, the CIS Controls Navigator offers a visual way to explore how each CIS Control corresponds to mandates, frameworks, and standards from around the world. It’s a valuable tool for identifying gaps, designing cohesive policies, and demonstrating compliance progress to leadership and auditors.

These updated mappings reinforce the role of the CIS Controls as a unifying framework that not only strengthens cybersecurity practices but also reduces the complexity associated with managing multiple compliance obligations.
Build a Foundation of Resilience with the CIS Controls
The CIS Controls v8.1 Poster, Mobile Companion Guide, ICS Workbook, and updated mappings are CIS's latest additions to our ecosystem of resources designed to help organizations of all kinds strengthen their cybersecurity programs by implementing the CIS Controls. Whether an organization is managing conventional IT environments, widespread mobile devices, or sensitive industrial systems, these resources make it easier to adopt best practices, reduce risk, and build a foundation of resilient operations.
Joshua Franklin is a Senior Security Engineer for the CIS Critical Security Controls at the Center for Internet Security (CIS), where he is developing best practices for mobility, IoT, and elections. Prior to CIS, Franklin researched enterprise mobile security, cellular security, and electronic voting at the National Institute of Standards and Technology (NIST). While at NIST, he managed the mobile security laboratory at the National Cybersecurity Center of Excellence (NCCoE). Franklin graduated from George Mason University with a Master of Science in Information Security and Assurance. He has presented at a variety of cybersecurity conferences including DEF CON, RSAC, and ShmooCon.
Robin Regnier serves as the Senior Controls Coordinator on the Security Best Practices team for the Center for Internet Security (CIS). In this role, she serves as project coordinator for the team dedicated to the development of the CIS Critical Security Controls (CIS Controls), promotes and furthers the adoption of the CIS Controls, and actively outreaches to CIS’s global community of volunteers and adopters to facilitate the continuous development and updating of CIS’s security guidance.
Thomas Sager is a Cybersecurity Engineer for the CIS Critical Security Controls at CIS. In this role, he is dubbed as the team cryptographer for mapping of the CMMC and PCI frameworks to the CIS Critical Security Controls. Prior to joining the CIS Controls team, Sager was a commercial security consultant under a federal contractor, greatly benefiting from the opportunity to work within a variety of client environments.
www.sans.org/partnerships/sltt

CybersideChat
A Simplified Framework for Faster, Smarter Cybersecurity Decisions
By Stephanie Gass, Senior Director of Information Security & Mathew Everman, Director of Information Security, CIS
Across Information Security, IT, and Governance, Risk, and Compliance (GRC) fields, leaders are asked to make high-stakes decisions, often with incomplete information, competing priorities, and constant pressure to move faster. Decision fatigue and analysis paralysis are common challenges when evaluating a new security tool, defining an AI governance policy, or creating proactive security plans.
The Simplified Decision Framework (SDF) aims to address this problem by helping organizations make timely, defensible decisions without sacrificing alignment to risk or mission objectives. The SDF distills complex decision-making around three core components that guide leaders toward clarity and action by visualizing what requirements have the most impact on current decisions and identifying key points of alignment.
1. What are your “crown jewels”? This question focuses on identifying the assets, services, or data that matter most to the organization. Understanding what must be protected first ensures that decisions are grounded in real business impact rather than theoretical risk.
2. What governs you? Every organization operates within a framework of laws, regulations, policies, and contractual obligations. The SDF prompts leaders to
explicitly account for these governance requirements so that speed does not come at the expense of compliance or accountability.
3. What people do you have? Even the best strategy will fail without the right skills and capacity to execute it. By factoring in available people, expertise, and organizational maturity, the framework encourages realistic, sustainable decisions.
Together, these three questions (W’s) create a repeatable mental model that helps security leaders quickly assess whether a proposed initiative aligns with acceptable risk, organizational constraints, and available resources.
At the core of the SDF is the role of risk. Risk is the core and driving factor for leadership roles to assist in innovation by ensuring the organization can operate in a safe, secure, and compliant manner. Risk is often associated with negative impacts, but risk is not inherently negative. Risk can also be willingness to try something new or enact change to generate revenue and expand business lines.
Risk should be holistic in nature and is not limited to cybersecurity or technology. Simply put, risk is anything that impacts the organization’s revenue and income. Leadership teams and organizational boards may generate risk appetite or tolerance statements designed to inform what
risks are acceptable. These risk statements and tolerance may encompass risks to specific data, tools, intellectual property, or the organization’s reputation. An organization's willingness to accept or avoid certain types of risk has major implications on the products, processes, and services used by that organization. Risk impacts and drives components of each of the three W’s, and understanding its impact on decision-making is key to a successful decision process.
A key strength of the SDF is its flexibility. It is designed to scale from large, strategic initiatives, like selecting a SIEM or developing enterprise-wide security policies, to everyday operational decisions. By narrowing focus to what truly matters, the SDF reduces unnecessary debate while still supporting innovation and agility in fast-changing environments.
Ultimately, the SDF is not about eliminating rigor; it is about directing rigor where it counts most. By anchoring decisions to critical assets, governance, and people, cybersecurity leaders can move faster with confidence, reduce unapproved risk, and ensure their actions remain aligned to organizational mission and values.
For organizations striving to balance speed, security, and governance, the SDF offers a clear path forward to effective, well-aligned decisions and informed action. You can learn more about the SDF here.


UpcomingEvents
April
April 13 – 15
The Consortium of School Networking (CoSN) will host the CoSN Annual Conference at the Sheraton Grand Chicago Riverwalk in Chicago, IL. The conference will advance the knowledge and skills of K-12 school leaders, delving into crucial topics such as cybersecurity, student data privacy, and the implementation of generative AI in schools — issues at the forefront for educational institutions and their communities. CoSN provides an unparalleled platform for districts to deepen their understanding of these critical issues and explore effective strategies for addressing them safely and successfully within the K-12 system. Learn more at https://cosn2026. eventscribe.net/.
April 13 – 15
The Retail and Hospitality Information Sharing and Analysis Center (RH-ISAC) will host the RH-ISAC Cybersecurity Summit at the Hyatt Regency Austin in Austin, TX. This annual event brings together RH-ISAC members from the strategic, operational, and tactical levels to participate in collaborative, practitioner-led case studies showcasing what works –and sometimes what does not work – in addressing the cybersecurity threats and challenges of the retail and hospitality industries. Learn more at https://summit2026.rhisac.org/.
April 15
The 9th Annual Philadelphia Official Cybersecurity Summit will take place at the Philadelphia Marriott Downtown in Philadelphia, PA. It will bring together leaders and cybersecurity professionals to learn about the latest cyber threats. Through our partnership, U.S. State, Local, Tribal, and Territorial (SLTT) government entities can receive free admission. Contact the CIS CyberMarket® team for more details. Learn more at https://cyberriskalliance. swoogo.com/philadelphia-april-2026.
April
23
The 4th Annual Salt Lake City Official Cybersecurity Summit will take place at the Sheraton Salt Lake City in Salt Lake City, UT. It will bring together leaders and cybersecurity professionals to learn about the latest cyber threats. Through our partnership, U.S. SLTT government entities can receive free admission. Contact the CIS CyberMarket team for more details. Learn more at https://cyberriskalliance.swoogo.com/ salt-lake-city-april-2026
April 26 – 29
The National Association of State Chief Information Officers (NASCIO) will host the NASCIO Midyear Conference at the Sheraton Philadelphia Downtown in Philadelphia, PA. The event brings together state CIOs and their staff from across the country together to learn from industry leaders, discuss best practices, discover new solutions from technology partners, and network with peers. Learn more at https://www.nascio.org/conferencesevents/midyear/
April 28
The 3rd Annual Baltimore Official Cybersecurity Summit will take place at the Baltimore Marriott Waterfront in Baltimore, MD. It will bring together leaders and cybersecurity professionals to learn about the latest cyber threats. Through our partnership, U.S. SLTT government entities can receive free admission. Contact the CIS CyberMarket team for more details. Learn more at https://cyberriskalliance.swoogo.com/ Baltimore-2026.
April 28 – 30
EDUCAUSE will host its Cybersecurity and Privacy Professionals Conference at the Hilton Anaheim in Anaheim, CA. The event is the premier forum for connecting with higher education information security and privacy professionals. It is the one higher ed event that gives participants a chance to network and discuss information security and privacy trends as well as current issues with peers and solution providers. MS-ISAC Member Engagement Manager Heather Doxon will present on measuring risk, resilience, and business impact at the event. Learn more at https://events. educause.edu/cybersecurity-andprivacy-professionals-conference/2026.
April 30
The 6th Annual South Florida Official Cybersecurity Summit will take place at the Diplomat Beach Resort in Hollywood, FL. It will bring together leaders and cybersecurity professionals to learn about the latest cyber threats. Through our partnership, U.S. SLTT government entities can receive free admission. Contact the CIS CyberMarket team for more details. Learn more at https://cyberriskalliance.swoogo.com/sflorida-april-2026.

May 6
May 4 - 8
The Health Information Sharing and Analysis Center (Health-ISAC) will host the Health-ISAC Spring Americas Summit at the Saddlebrook Resort in Wesley Chapel, FL. The summit offers opportunities for health security professionals to learn from leading experts at interactive educational sessions, keep abreast of cutting-edge tools and services, network with peers in global health security, and strengthen their ability to increase health sector safety. Learn more at https://health-isac. org/summit-meeting/2026-springamericas-summit/
May 5
The 10th Annual Denver Official Cybersecurity Summit will take place at the Hilton Denver City Center in Denver, CO. It will bring together leaders and cybersecurity professionals to learn about the latest cyber threats. Through our partnership, U.S. SLTT government entities can receive free admission. Contact the CIS CyberMarket team for more details. Learn more at https://cyberriskalliance.swoogo.com/ denver-2026
May 5 - 8
The National Association of Counties (NACo) will host its Western Interstate Region (WIR) Conference at the Hyatt Regency Maui in Lahaina, HI. The conference brings together county officials from across the nation to focus on pressing issues facing Western counties and their residents. This year, Maui County will host county leaders in disaster-focused workshops and tours emphasizing response, recovery and resilience. Learn more at https:// www.naco.org/event/2026-westerninterstate-region-wir-conference
The 11th Edition of the Boston Official Cybersecurity Summit will take place at the Westin Copley Place in Boston, MA. It will bring together leaders and cybersecurity professionals to learn about the latest cyber threats. Through our partnership, U.S. SLTT government entities can receive free admission. Contact the CIS CyberMarket team for more details. Learn more at https:// cyberriskalliance.swoogo.com/ boston-2026.
May 6 – 7
The Connecticut Education Network (CEN) will host the 13th Annual CEN Member Conference at the Connecticut Convention Center in Hartford, CT. The event will connect over 700 education technology colleagues and industry leaders from across the state for training, collaboration, education, and networking. Learn more at https://ctedunet.net/ annual- conference/.
May 13
The MassCyberCenter will host the Massachusetts Municipal Cybersecurity Summit will take place at the DCU Center in Worcester, MA. The event will empower public sector cybersecurity leaders, administrators, and practitioners with the skills, authority, and community support needed to safeguard digital public spaces as threats grow in scale and sophistication. Learn more at https:// masscybercenter.org/node/22771.
May 13
The Maine Municipal Association will host the Maine Municipal Technology and Innovation Summit will take place at the University of Maine at Augusta in Augusta, ME. The event will bring together public sector IT leaders and professionals from around the state to learn from industry experts, discover new solutions, and network with peers. CIS VP of Security Operations & Intelligence Randy Rose will lead a breakout session on defending against AI-based cyber attacks and Senior Director of Information Security Stephanie Gass will lead a session on data privacy and compliance. Learn more at https://www.memun.org/ Training/Events/Technology
May 13 - 14
The Court Information Technology Officers Consortium (CITOC) will host the CITOC Security for Justice Summit at the Barbara Jordan State Office Building in Austin, TX. The summit is designed for court technology professionals responsible for cybersecurity oversight, governance, and policy development. The event will feature expert-led presentations highlighting current technology trends and emerging national cybersecurity threats impacting court systems. CIS Member Experience & Engagement Manager Elijah Cedeno will lead a session discussing updates to the MS-ISAC and a national cyber threat overview. Learn more at https:// www.citoc.org/event-details/ security-for-justice

May 13
The 7th Annual Nashville Official Cybersecurity Summit will take place at the Renaissance Nashville Hotel in Nashville, TN. It will bring together leaders and cybersecurity professionals to learn about the latest cyber threats. Through our partnership, U.S. SLTT government entities can receive free admission. Contact the CIS CyberMarket team for more details. Learn more at https://cyberriskalliance.swoogo.com/ nashville-may-2026.
May 19
The 3rd Annual Toronto Official Cybersecurity Summit will take place at the Sheraton Centre Toronto Hotel in Toronto, ON. It will bring together leaders and cybersecurity professionals to learn about the latest cyber threats. Through our partnership, U.S. SLTT government entities can receive free admission. Contact the CIS CyberMarket team for more details. Learn more at https://cyberriskalliance.swoogo.com/ toronto-2026
May 20 – 21
The Texas Department of Information Resources (DIR) will host the 27th Annual Information Security Forum (ISF) for Texas Government at the Palmer Events Center in Austin, TX. As the premier cybersecurity event for Texas state and local government as well as public education institutions, ISF 2026 brings together decisionmakers, IT professionals, and security leaders from across the state for two days of learning, collaboration, and innovation. ISF will feature engaging presentations, panel discussions, and networking opportunities designed to foster collaboration between public-and private-sector security experts. Learn more at https://dir.texas. gov/information-security/informationsecurity-forum.
June
June 2
The 3rd Annual Milwaukee Official Cybersecurity Summit will take place at the Hyatt Regency Milwaukee in Milwaukee, WI. It will bring together leaders and cybersecurity professionals to learn about the latest cyber threats. Through our partnership, U.S. SLTT government entities can receive free admission. Contact the CIS CyberMarket team for more details. Learn more at https://cyberriskalliance.swoogo.com/ Milwaukee-2026.
June 2 – 3
The New York State Office of Information Technology Services, the University at Albany School of Business, and The New York State Forum will host the 28th Annual New York State Cybersecurity Conference at the Empire State Plaza Convention Center in Albany, NY. The event is expected to attract more than 1,000 cybersecurity and other industry professionals from across the state to learn from industry experts, share best practices, and network with peers. Learn more at https://its.ny.gov/2026-nyscybersecurity-conference .
June 3
The 4th Annual Hartford Official Cybersecurity Summit will take place at the Marriott Hartford Downtown in Hartford, CT. It will bring together leaders and cybersecurity professionals to learn about the latest cyber threats. Through our partnership, U.S. SLTT government entities can receive free admission. Contact the CIS CyberMarket team for more details. Learn more at https://cyberriskalliance.swoogo.com/ hartford-june-2026.
June 3 - 4
The Nebraska Association of County Officials (NACO) will hold its annual NACO County Board Workshop at the Younes Conference Center in Kearney, NE. The event that brings together county board members from across the state for education, collaboration, and leadership development. The CIS team will be onsite sharing our cybersecurity resources for county and local governments. Learn more at https:// nebraskacounties.org/.

June 9
The 5th Annual St. Louis Official Cybersecurity Summit will take place at the Marriott St. Louis Grand in St. Louis, MO. It will bring together leaders and cybersecurity professionals to learn about the latest cyber threats. Through our partnership, U.S. SLTT government entities can receive free admission. Contact the CIS CyberMarket team for more details. Learn more at https://cyberriskalliance.swoogo.com/ st-louis-june-2026.
June 8 - 11
The National Sheriffs' Association (NSA) will host the NSA Annual Conference at the Omaha Convention Center in Omaha, NE. The conference is one of the premier law enforcement conferences in the country with four days of highly curated seminars and educational content covering cutting edge content for law enforcement at all levels. Learn more at https://www. nsaconference.org/.
June 11
The 4th Annual Austin Official Cybersecurity Summit will take place at the JW Marriott Austin in Austin, TX. It will bring together leaders and cybersecurity professionals to learn about the latest cyber threats. Through our partnership, U.S. SLTT government entities can receive free admission. Contact the CIS CyberMarket team for more details. Learn more at https:// cyberriskalliance.swoogo.com/ Austin-2026.
June 21 – 24
The ISAC Annual Summit will take place at the Caribe Royale in Orlando, FL. This gathering marks the 19th ISAC Annual Meeting — celebrating nearly two decades of U.S. SLTT collaboration and community defense. Attendees will engage with peers, gain insights from shared U.S. SLTT best practices, and enhance their security, resilience, and continuity strategies to better protect U.S. government networks and systems. Over three days of immersive learning, attendees will gain actionable security, resilience, and continuity strategies from subject-matter experts from the Center for Internet Security (CIS), the MultiState Information Sharing and Analysis Center (MS-ISAC), U.S. SLTT peers, and industry partners in over 40 sessions. Learn more and register at https://www. cisecurity.org/event-calendar/annualisac-meeting.
June 23
The 4th Annual Pittsburgh Official Cybersecurity Summit will take place at the Wyndham Grand Pittsburgh Downtown in Pittsburgh, PA. It will bring together leaders and cybersecurity professionals to learn about the latest cyber threats. Through our partnership, U.S. SLTT government entities can receive free admission. Contact the CIS CyberMarket team for more details. Learn more at https://cyberriskalliance. swoogo.com/Pittsburgh-2026.
June 30
The 2nd Annual Minneapolis Official Cybersecurity Summit will take place at the Marriott Minneapolis City Center in Minneapolis, MN. It will bring together leaders and cybersecurity professionals to learn about the latest cyber threats. Through our partnership, U.S. SLTT government entities can receive free admission. Contact the CIS CyberMarket team for more details. Learn more at https://cyberriskalliance.swoogo.com/ Minneapolis-2026.
June 30 – July 1
Amazon Web Services (AWS) will host AWS Summit Washington D.C. at the Walter E. Washington Convention Center in Washington D.C. Attendees will discover how AWS public sector customers are adapting to change and challenges as well as constructing innovative solutions in the cloud, and they will experience how technology is shaping the future. Attendees will hear directly from AWS experts, builders, customers, and partners — all sharing their insights on generative AI, analytics, storage, industry solutions, and much more in over 340 technical sessions and interactive workshops. The CIS team will be onsite sharing our resources and best practices for public sector organizations. All government employees can register for the event at no cost. Learn more at https:// aws.amazon.com/events/summits/ washington-dc/.
Interested in being a contributor?
Please contact us:
CyberMarket@cisecurity.org
www.cisecurity.org
518.266.3460

cisecurity.org
email@cisecurity.org
518-266-3460
Center for Internet Security

@CISecurity
TheCISecurity
cisecurity

CenterforIntSec