Switch to Speed. Scale Without Limits.

Meet the SwitchBlade x908 GEN3
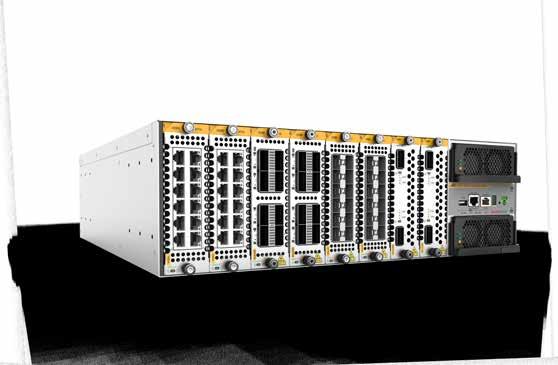
The SwitchBlade x908 GEN3 is our most advanced modular switch, delivering blazing speed and scalable growth for future-ready enterprise and data center networks.
Blazing Bandwidth: Up to 400G connectivity for high-performance workloads.
Scale Without Limits: 12.8 Tbps of power in a compact 3U chassis.
Flexible & Modular: Compact chassis with versatile interface options.
Smart Management: Zero-touch provisioning and centralized control with AlliedWare Plus™.
Whether you’re scaling a data center or optimizing enterprise networks, the SwitchBlade x908 GEN3 keeps your network fast, flexible, and fail-proof.
Take control. Stay ahead. Transform your network today.
www.cxoinsightme.com
24 THE TRUST MANDATE
Highlights from CXO Insight ME’s exclusive roundtable powered by Corelight and Malcrove on how AI is reshaping the SOC
INTERVIEWS
28 INTELLIGENCE ON RECORD
Oracle NetSuite’s Nicky Tozer and James Chisham on ERP’s evolution as AI moves into core workflows, redefining data integrity, automation, and the system of record
30 THE GOVERNANCE IMPERATIVE
ServiceNow’s Cathy Mauzaize explains why AI at scale demands leadership-level governance, transparency, and structured accountability
VIEWPOINTS
34 FROM HALLUCINATION TO CONTROL
Globant breaks down why human oversight, structured safeguards, and context engineering are central to reliable AI systems
40 ADAPT OR STALL
AVEVA on how industrial enterprises must redesign operations for resilience as climate risk, grid constraints, labour shortages, and AI-driven change converge
50 The latest gears and gadgets to keep you ahead of the curve
RESILIENCE IN PRACTICE
SANS Institute’s Ned Baltagi on why the region’s AI ambition must be matched with real defensive maturity and operational discipline








Published by

THE DISCIPLINE OF SCALE
As AI embeds itself into enterprise operations across the region, governance is no longer a back-office concern. It sits alongside growth, risk and performance. The question leaders are grappling with is straightforward: as digital systems scale, is accountability scaling with them?
This month’s cover star, SANS Institute’s Ned Baltagi, examines that tension directly. The region’s AI ambition is visible. What determines advantage, however, is operational capability. Compliance may satisfy regulators, but resilience is measured in detection times, response discipline and the ability to withstand live pressure. AI systems must be secured and governed as production infrastructure.
That same realism was at the centre of our roundtable with Corelight. The discussion was not about AI potential; it was about evidence. It shed light on how automation without clarity simply amplifies noise. Turn to page 24 for the full discussion.
This edition also features a conversation with Cathy Mauzaize of ServiceNow, who takes the argument into the boardroom, noting that governance is not the
same as compliance. It is the framework that allows innovation to scale without losing control.
Elsewhere in this issue, Genetec examines how physical security data is becoming a source of operational insight. Oracle NetSuite explores AI embedded within the system of record. Riverbed looks at agentic automation and the guardrails it demands. Globant addresses human oversight in the age of generative systems. AVEVA considers industrial resilience in a volatile year.
Across these conversations, resilience emerges not as an add-on to innovation, but as the condition that allows it to endure. What happens next will depend less on deployment speed and more on how firmly these foundations — and the accountability behind them — are set.
Publication licensed by Sharjah Media City
@Copyright 2026 Insight Media and Publishing
Managing Editor
Adelle Geronimo
adelleg@insightmediame.com
+97156 - 4847568
Production Head
James Tharian
jamest@insightmediame.com
+97156 - 4945966
Adelle Geronimo
Managing Editor
Commercial Director
Merle Carrasco
merlec@insightmediame.com
+97155 - 1181730
Administration Manager Fahida Afaf Bangod fahidaa@insightmediame.com
+97156 - 5741456
Operations Director
Rajeesh Nair
rajeeshm@insightmediame.com
+97156 - 4110215
Designer
Anup Sathyan
While the publisher has made all efforts to ensure the accuracy of information in this magazine, they will not be held responsible for any errors
Adelle

WhatsApp has launched “Strict Account Settings,” an optin high-security mode designed for high-risk users such as journalists and activists. The feature blocks media from unknown senders, disables link previews, and silences unknown calls, trading some functionality for stronger protection against sophisticated cyber threats.

UAE Verify, the Telecommunications and Digital Government Regulatory Authority (TDRA) blockchain-based platform has issued over 30.7 million Digital Trusted Documents since 2022, supporting 66 document types from 25 government entities and enabling instant, secure digital verification without physical copies.

Snowflake has appointed Dayne Turbitt as Senior Vice President for EMEA, tasking him with leading and expanding the company’s go-to-market operations across Europe, the Middle East and Africa. Turbitt’s 25+ years of tech leadership experience will help accelerate AI adoption and regional growth.

Doha has been ranked the world’s fastest city for mobile internet performance by Holafly, with average download speeds of around 354.5 Mbps. The recognition underscores Qatar’s advanced digital infrastructure and reinforces Doha’s position as a leading hub for high-performance connectivity and next-generation mobile networks.

GISEC Global is launching a Cyber Diplomacy Forum at its 2026 edition, creating a high-level platform to bridge cybersecurity with international policy, trade and national security. The forum will bring governments, multilateral institutions and the private sector together to tackle crossborder cyber risks and strengthen global cooperation.

Securonix has named Bassam Sartawi as Senior Director for MEA, strengthening leadership across the Middle East and Africa. Sartawi will drive strategic growth and support partners in delivering Securonix’s next-gen security analytics and SIEM solutions to address evolving cyber threats across the region.
WhatsApp unveils high-security mode
GISEC GLOBAL to Debut Cyber Diplomacy Forum in 2026
Dayne Turbitt to lead Snowflake’s EMEA expansion
Securonix appoints Bassam Sartawi as MEA Senior Director
Doha named city with fastest mobile internet performance globally
‘UAE Verify’ crosses 30 million mark in trusted digital documents







UAE joins UN independent scientific panel on AI
United Nations Secretary-General António Guterres has submitted to the General Assembly a list of 40 prominent international experts from across regions, including the UAE’s Tuka Alhanai, as part of preparations to establish the Independent International Scientific Panel on Artificial Intelligence.
Announcing the move at UN Headquarters in New York, Guterres described it as a decisive step to ensure artificial intelligence serves all of humanity. The panel is being formed in
Amazon sees 50% jump in capital spending
response to a mandate issued by Member States under the “Pact for the Future,” which seeks to strengthen multilateral solutions for emerging technologies reshaping societies and economies.
Guterres said the panel will become the world’s first fully independent global scientific body dedicated to bridging the knowledge gap in artificial intelligence and assessing its real-world impacts.
“AI is moving at the speed of light. No country can see the full picture alone,” Guterres said. “We need shared
Amazon expects to increase capital expenditures by more than 50 percent this year, outlining plans to invest about $200 billion in 2026, up from $131 billion in 2025, as it accelerates infrastructure expansion to support artificial intelligence and cloud growth, according to Reuters.
The scale of the planned investment unsettled markets, with shares falling sharply in after-hours trading following the announcement.
Chief Executive Andy Jassy addressed growth comparisons during the company’s earnings call, stating: “As a reminder, it’s very different having 24 percent year-over-year growth on $142 billion annualised run rate, than to have a higherpercentage growth on a meaningfully smaller base, which is the case with our competitors.”
Amazon’s cloud arm, Amazon Web Services, reported $35.6 billion in revenue for the December quarter. While competitors have
AI is moving at the speed of light. No country can see the full picture alone
understandings to build effective guardrails, unlock innovation for the common good, and foster cooperation.”
He added that the panel will help distinguish facts from misinformation and provide a trusted, impartial reference amid the rapid pace of AI development.
The selection followed a global open call that attracted more than 2,600 nominations. Members, drawn from disciplines including machine learning, data governance, public health, cyber security, child development and human rights, will serve in their personal capacities and independently of governments or institutions.
The panel’s first report is expected ahead of a global AI governance dialogue scheduled for July.

posted faster percentage growth, the company pointed to differences in scale.
Reuters noted that the four largest hyperscalers — Microsoft, Google, Meta and Amazon — are collectively expected to invest more than $630 billion in infrastructure this year.
The investment surge reflects the escalating race to build AI-ready data centres and expand cloud capacity.
However, the market reaction underscores investor sensitivity to rising capital intensity and the need for clear returns on large-scale AI spending.
OpenAI, Snowflake team up to power AI-ready data

OpenAI and Snowflake have entered a multi-year strategic partnership to embed advanced AI models directly into Snowflake’s data cloud, aiming to accelerate enterprise adoption of production-grade artificial intelligence. Through the collaboration, OpenAI’s models will be integrated into Snowflake Cortex AI, allowing organisations to build and deploy AI applications directly on governed enterprise data. The move is designed to help companies shift from isolated AI pilots to operational
EDGE signs agreement to pilot sovereign autonomous logistics platform
deployments by bringing AI capabilities closer to where data is stored and managed.
The agreement includes joint product development and go-to-market initiatives focused on delivering trusted AI agents that function within secure, compliant data environments.
Christian Kleinerman, Executive Vice President of Product at Snowflake, said: “For AI to truly deliver value, it must move beyond experimentation and become engrained within the systems teams rely
$200 million
The
value of the multiyear AI partnership between OpenAI and Snowflake
on every day... helping enterprises deliver real business impact with AI.”
Valued at $200 million, the partnership reflects increasing demand from enterprises seeking scalable AI tools that align with governance, security and data residency requirements. By combining OpenAI’s models with Snowflake’s platform, organisations will be able to query structured and unstructured data using natural language and streamline analytics and automation within existing infrastructure.
EDGE has signed a Collaboration Agreement with Technology Innovation Institute (TII), SteerAI and Micropolis to pilot an autonomous logistics platform (ALP) designed to automate the movement of assets within and between manufacturing facilities.
Signed at the Unmanned Systems Exhibition (UMEX) and Simulation and Training Exhibition (SimTEX) 2026, the agreement aims to advance sovereign Emirati capabilities in unmanned ground vehicles (UGVs), AI systems and smart infrastructure.
The ALP will combine custom-built UGVs with AI-driven software, integrating fleet

management, navigation and safety, digital twins, situational awareness, operational optimisation, advanced analytics and enterprise integration. Micropolis will provide the UGV hardware (M1 and M2 variants), SteerAI will deliver its CoreConnect fleet management system, and TII will contribute advanced analytics and sovereign AI-driven situational awareness through TACTICAai.
Bader Al Jaberi, Vice President for Industrialisation Technologies, EDGE BRIDGE, said, “As a catalyst for injecting emerging technologies into the UAE’s industrial defence hub, we are partnering with the UAE’s growing autonomous ecosystem to champion the development of advanced manufacturing systems.
This Collaboration Agreement marks a significant step forward in our mission to build sovereign, end-toend autonomous capabilities, from advanced research to industrial-scale manufacturing.”
Dr Najwa Aaraj, CEO of TII, said, “TACTICAai reflects our vision for next-generation situational awareness... The result is reduced decision time and operational risk, with resilient, sovereign AI that augments human judgment in complex environments, while keeping humans in the loop.”
Microsoft, Ericsson expand enterprise connectivity with 5g in Windows 11

Microsoft and Ericsson have unveiled a joint solution that brings enterprise-grade 5G laptop management to Windows 11, aiming to simplify connectivity, security and policy enforcement for distributed PC fleets.
The integrated solution combines Microsoft Intune device management with Ericsson Enterprise 5G Connect (formerly Ericsson Enterprise Virtual Cellular Network), an AI- and cloudanalytics-powered platform that continuously monitors network quality
Dell Technologies, Ooredoo partner to advance AI innovation in Qatar
Dell Technologies and Ooredoo have signed a Memorandum of Understanding (MoU) aimed at advancing artificial intelligence innovation and deepening cooperation on modern AI services, according to company statements.
The MoU was signed in Doha by Travers Nicholas, Managing Director, North Gulf at Dell Technologies, and Hassan Ismail Al-Emadi, Chief Business Officer (CBO) at Ooredoo Qatar. Under the agreement, Ooredoo and Dell plan to deliver AI-as-aService through Ooredoo’s Sovereign AI Cloud. The service — powered by Dell — is
and automatically adjusts connectivity for performance and security.
The embedding of AI-based 5G management into Windows 11 enables IT teams to automate how devices connect, seamlessly switch between communications service providers’ networks and apply in-house enterprise policies, the announcement said.
According to the companies, through Microsoft Intune and Ericsson Enterprise 5G Connect, IT teams can automatically
designed to offer organisations secure and scalable AI capabilities hosted within locally governed cloud infrastructure to enable innovation and improve operational efficiency across industries.
Al-Emadi said: “This agreement underscores our dedication to delivering exceptional, future-ready digital experiences to our customers. With

AI-powered 5G laptops are redefining how and where work gets done
ERIK EKUDDEN
Ericsson
enforce secure connectivity profiles and enterprise policies across every 5G-connected device, reducing manual setup while ensuring consistent, compliant user experiences wherever employees work.
Erik Ekudden, CTO of Ericsson, said: “AI-powered 5G laptops are redefining how and where work gets done. Together with Microsoft and leading CSP partners, we’re enabling organisations to seamlessly automate the deployment and operations of secure, always-connected devices regardless of location – creating a smarter, more responsive workplace for the AI era.”
Ian LeGrow, Corporate Vice President, Core OS at Microsoft, added: “Windows 11 is the optimal enterprise platform for deploying and managing 5G-connected PCs at scale... Enterprise IT teams can ... seamlessly provision, manage, and secure both devices and 5G connectivity.”
The joint solution is now available in key markets including the United States, Sweden, Singapore and Japan, with further rollouts planned in 2026.
Dell’s unparalleled expertise in advanced infrastructure and AI capabilities, Ooredoo will be able to drive innovation that will transform industries and create meaningful impact for businesses and communities in Qatar.”
Nicholas added: “At Dell, we are dedicated to empowering organizations to harness the full potential of data and AI. This collaboration with Ooredoo combines our advanced AI and infrastructure solutions with their forward-thinking approach to telecommunications, enabling meaningful digital transformation. Together, we aim to deliver cutting-edge solutions that drive measurable outcomes and equip businesses with the tools to seize new opportunities.”
The partnership reflects a broader regional emphasis on leveraging sovereign cloud and AI services to support digital transformation across sectors.



INTO NEW WORLDS
You’re One LEAP Away
From 13-16 April 2026
Riyadh Exhibition and Convention Center - Malham, Saudi Arabia
SECURE YOUR PASS NOW
Lockheed Martin to boost defence innovation in Riyadh
Lockheed Martin has launched a software factory in Riyadh, Saudi Arabia, introducing its advanced software development ecosystem to the Kingdom, the company announced.
The new facility will support the rapid development of sovereign software applications and enable their integration into Lockheed Martin platforms and systems, marking a significant step in expanding digital defence capabilities in the region.
“This is a strong example of what can be achieved when Lockheed Martin works closely with Saudi industry and academia to develop world-class, integrated command-and-control capabilities in the Kingdom,” said Joseph Rank, CEO, Lockheed Martin Saudi Arabia and Africa. “For more than 60 years, Lockheed Martin has partnered with Saudi Arabia in support of regional deterrence and stability. The software factory is one of several initiatives focused on building local capacity and accelerating the transfer of advanced technical expertise, while supporting US jobs and strengthening the resilience and global reach of the US defence industrial base.””
The facility has already demonstrated early successes: in under two weeks, Saudi interns worked with engineers

The software factory is one of several initiatives focused on building local capacity and accelerating the transfer of advanced technical expertise…”
JOSEPH
NTT DATA and AWS to accelerate enterprise cloud and agentic AI adoption
NTT DATA has signed a multi-year Strategic Collaboration Agreement with Amazon Web Services to help enterprises modernise legacy systems, adopt agentic artificial intelligence responsibly and scale innovation across industries, according to company announcements.
The partnership brings together NTT DATA’s expertise in cloud transformation, cloud-native modernisation and agentic AI with the scale and innovation velocity of AWS services. Together, they will deliver tailored enterprise solutions

from Saudi Arabian Military Industries (SAMI) Advanced Electronics Company to integrate commercial aircraft location data into Lockheed Martin’s CommandIQ common operating picture, showcasing rapid mission-relevant software delivery.
“SAMI Advanced Electronics Company is committed to strengthening the Kingdom’s sovereign defence capabilities by deepening local engineering expertise and accelerating the delivery of missioncritical digital solutions,” said Eng. Ziad H. Al-Musallam, CEO of SAMI Advanced Electronics Company. “This collaboration with Lockheed Martin’s Software Factory shows how joint delivery teams can rapidly integrate advanced software into operational command-and-control environments while transferring knowledge to Saudi talent and industry.”
designed to modernise missioncritical workloads, build secure cloud foundations and drive measurable business outcomes across regulated and high-growth sectors.
Under the agreement, the companies will accelerate enterprise transformation in four priority areas, including AI-driven large-scale cloud modernisation, industry cloud solutions across sectors such as financial services and healthcare, AIenabled managed services and customer experiences, and digital sovereignty and regulated cloud offerings on the AWS European Sovereign Cloud.
To support delivery, NTT DATA has formed a dedicated AWS Business Group with close to 11,000 AWS-certified experts, with plans to certify nearly 10,000 more over the next three years.
RANK Lockheed Martin

“THE CHALLENGE WE FACE TODAY IS NOT A FAILURE OF INNOVATION. IT IS A FAILURE OF ALIGNMENT. IF AI IS TO BECOME A TOOL FOR GLOBAL CONVERGENCE RATHER THAN A WEDGE FOR DEEPER INEQUALITY, WE NEED A NEW OPERATING MODEL”
HE Badr Jafar, UAE Special Envoy for Business and Philanthropy
“DUBAI IS CONTINUING TO STRENGTHEN ITS POSITION AS A GLOBAL HUB FOR LEADING TECHNOLOGY AND DIGITAL INNOVATION COMPANIES, SUPPORTED BY A FLEXIBLE,

BUSINESSFRIENDLY ENVIRONMENT AND ADVANCED INFRASTRUCTURE THAT KEEPS PACE WITH THE RAPID EVOLUTION OF THE DIGITAL ECONOMY”
HE Omar Sultan Al Olama, Minister of State for Artificial Intelligence, Digital Economy, and Remote Work Applications and Chairman of Dubai Chamber of Digital Economy
THE ROAD FROM PILOT TO PRODUCTION
Enterprise AI programmes are entering a decisive phase. Organisations across banking, manufacturing, retail, insurance and the public sector are increasing budgets, expanding platform footprints and embedding AI tools into dayto-day workflows. Adoption at an individual level is rising, and infrastructure investment is strengthening. Yet operational scale remains constrained. According to Alteryx’s newly released “From AI Ambition to Impact” report, fewer than one in four AI pilots successfully transition into production.
The research, based on a survey of 1,400 business and IT leaders across the Americas, EMEA and APJ, captures a widening gap between AI ambition and measurable business impact. Forty-eight percent of leaders plan to boost spending on AI infrastructure and tools, while 89 percent say they will maintain or increase AI budgets
in 2026. AI platforms are projected to expand from 33 percent of enterprise data stacks in 2024 to 51 percent within three years. Two-thirds of respondents report using AI more in their roles than they did a year ago. Investment and usage trends suggest acceleration rather than hesitation.
The constraint lies elsewhere. Trust remains limited when AI moves beyond low-risk automation. Nearly half of respondents express confidence in using AI to automate repetitive tasks, draft content and monitor systems. Confidence declines sharply in higher-stakes applications. Only 28 percent trust AI to support decision-making, and 27 percent trust it to facilitate forecasting or planning. In enterprise environments where accountability is financial, regulatory and reputational, that hesitation materially affects deployment decisions.
Data quality and governance are identified as critical determinants of progress. Forty-nine percent of leaders cite highquality, accessible and wellgoverned data as the primary factor enabling agentic AI to achieve its potential.
The findings suggest that many stalled initiatives are linked to organisations layering generative capabilities directly onto fragmented or poorly structured data environments. Inconsistent outputs, shifting responses and limited explainability undermine executive confidence and delay operational rollout.
The report also points to an organisational rebalancing of AI ownership. Responsibility for AI workflows is expected to move away from centralised teams towards individual lines of business, rising from 22 percent today to 33 percent by 2028
— an 11 percent shift over three years. As AI becomes embedded within operational domains, governance requirements become more complex, requiring consistent standards across distributed decision-making structures.
Twenty-eight percent of leaders plan to prioritise improvements in data governance, indicating recognition that scaling AI depends on disciplined foundations rather than incremental experimentation alone.
“AI adoption is accelerating fast,” said Andy MacMillan, CEO of Alteryx. “Our research shows that compared to a year ago, two-thirds of business and IT leaders are using AI more in their roles... The most advanced organisations are doubling down on improving data quality and integrating AI across their operations.”
In a nutshell, the findings describe an enterprise landscape where financial commitment is strong, experimentation is widespread, and structural maturity is uneven. The ability to convert pilots into sustained production capability will depend on whether organisations treat data governance, workflow design and accountability as strategic prerequisites rather than secondary considerations.
1 in 4
51%
The number of AI pilots that successfully reach production
49%
The share of enterprise data stacks expected to include AI platforms within three years
The proportion of leaders who cite high-quality, well-governed data as the most critical factor for agentic AI impact

RESILIENCE IN PRACTICE
Ned Baltagi, Managing Director – Middle East, Turkey and Africa, SANS Institute, discusses why digital ambition must be matched by defensive maturity and operational capability as the region scales AI, cloud and critical infrastructure
The GCC’s AI trajectory is no longer experimental. Across the region, sovereign cloud infrastructure is expanding, national AI programmes are being operationalised and generative models are embedded into enterprise workflows and public services. Security operations centres are integrating AI-assisted detection and response into live environments. The shift from pilot to production is well underway.
What is less certain is whether defensive maturity is scaling in parallel.
“The ambition is undeniable,” says Ned Baltagi, Managing Director, Middle East and Africa at SANS Institute. “The pace of AI adoption — from pilot to permanent, scaled deployment — mirrors what we’re seeing globally. But defensive maturity is not always advancing at the same speed. In many cases, investment in AI capability is outpacing investment in AI protection and governance.”
That imbalance introduces structural risk precisely because AI systems are no longer peripheral tools.
“AI is not secure by default,” Baltagi adds. “Adversaries will target it. The organisations keeping pace are those applying structured discipline alongside ambition — implementing layered protections across access, data, deployment, inference and monitoring, modernising SOC operations to counter AI-enabled threats, and elevating governance to the executive level.”
The global context reinforces the point. The Global Cybersecurity Outlook 2025 from the World Economic Forum highlights how AI is increasing both the sophistication and speed of cyber threats, while defensive preparedness remains uneven. Acceleration without embedded controls does not create advantage; it amplifies exposure.
In the GCC, where AI is increasingly integrated into nationalscale infrastructure, the stakes are not simply operational. They are economic and strategic.

From frameworks to function
Over the years, the region’s cyber maturity has evolved beyond compliance checklists toward demonstrable operational capability.
“The biggest shift has been from compliance as an endpoint to capability as an outcome,” says Baltagi. “In the recent past, the emphasis was often on frameworks, controls and documentation. Today, leading governments are asking more operational questions: Can you detect? Can you respond? Can you recover?”
That shift reflects a more mature understanding of resilience. Compliance frameworks establish a
baseline. They do not, on their own, ensure that an organisation can withstand a live incident.
“The difference is visible the moment an incident unfolds,” Baltagi explains. “Operationally resilient organisations have built detection and response around real telemetry and tested use cases, not just audit requirements. They measure mean time to detect and contain, and they track improvement over time.”
Practice, he argues, is as important as architecture. “They run realistic scenarios. Their analysts have handled simulations that resemble real adversary behaviour. Operationally resilient organisations

prioritise adversary-informed, hands-on skill validation, measuring performance improvement over time rather than tracking attendance or certification alone. Compliance may satisfy regulators, but operational resilience withstands attackers.”
The threat environment has forced this recalibration as cloud and identity-based attacks now dominate many environments. “Credential abuse and misconfiguration can be more damaging than traditional malware,” he adds.
The 2025 Cost of a Data Breach Report from IBM, which found the global average cost of a breach to be US$4.44 million, ranks stolen or
compromised credentials among the five most common initial attack vectors, responsible for 10 percent of incidents analysed.
At the same time, Operational Technology (OT) and Industrial Control Systems (ICS) environments are increasingly targeted, demanding defenders who understand industrial systems as well as enterprise IT. As connectivity deepens, resilience carries implications beyond data protection into operational continuity.
Overlay AI onto that already complex landscape, and the tempo increases again.
“Threat actors have evolved in ways that require defenders to evolve as
AI security maturity means treating AI systems as production infrastructure with a defined attack surface, not as experimental tools
well,” Baltagi says. “AI has introduced a new acceleration dynamic. Adversaries can iterate and scale faster. That means defenders need stronger analytical discipline, automation design skills, and a deeper understanding of how to validate AI-assisted outputs within the SOC.”
Validation becomes critical because AI is now embedded inside security operations themselves. Detection engines incorporate machine learning. Automation coordinates response workflows. Large language models assist analysts with investigation summaries. Yet governance frameworks have not always matured at the same pace.
“In many cases, AI has moved quickly from pilot projects to scaled deployment across business units and the SOC, while governance frameworks are still maturing,” Baltagi notes. “The gap often appears in limited visibility into AI systems, incomplete control mapping, and unclear accountability for AI-driven decisions.”
Without AI-specific monitoring and playbooks, speed can introduce new risk.
“AI security maturity means treating AI systems as production infrastructure with a defined attack surface, not as experimental tools,”
he says. “In practical terms, it aligns to a structured approach: Protect AI, Utilise AI and Govern AI — implementing layered controls across access, data, deployment, inference, monitoring and model security.”
That includes defending against model poisoning, prompt injection, data leakage and shadow AI. Mature organisations maintain visibility into models and data flows, continuously monitor behaviour and embed governance at the executive level.
Capability as national strategy
Technology architecture alone does not determine resilience. Across AI, cloud and industrial convergence, Baltagi returns consistently to one structural factor: talent.
“The region has made significant progress in structured workforce development,” he says. “But demand
still outpaces supply, particularly for experienced practitioners capable of operating in Security Operations Centres (SOC), incident response, cloud and OT environments.”
What separates progress from optics, he argues, is the difference between short-term training efforts and sustained capability building.
“A serious, future-ready cyber workforce strategy is role-based, structured and long-term,” Baltagi explains. “It defines competencies clearly, maps them to operational needs, and creates progression pathways. It includes practical skill validation and measures outcomes in terms of job performance. Short-term initiatives often focus on attendance metrics or general awareness. Future-ready strategies build pipelines — from talent identification through training,

mentorship, certification and ongoing development — aligned to national and sectoral priorities.”
The approach is already visible in how SANS is working with institutions in the region. In Kuwait, its partnership with the Kuwait Institute of Banking Studies (KIBS) and the Central Bank of Kuwait (CBK) is focused on strengthening cybersecurity capability within the banking sector, aligning technical training with both international standards and national security priorities. The Kuwait Cybersecurity Leaders Program, developed jointly with KIBS and CBK, is structured to equip professionals with the expertise required to manage evolving cyber risk across financial institutions.
Delivered through intensive, handson training, the programme prepares participants for globally recognised Global Information Assurance Certification (GIAC) credentials, enabling them to move directly into operational cybersecurity roles within Kuwait’s financial sector.
“SANS programmes are designed around real operational roles, guiding learners from assessment through advanced training to GIAC, ensuring graduates can perform in live environments from day one,” Baltagi says. “The focus is on applied skills, not theory alone, delivered by active cyber practitioners and mapped to recognised workforce frameworks.”
AI security itself is crystallising into a defined profession within that pipeline.
“Organisations need capability aligned to Protect AI, Utilise AI and Govern AI,” he reiterates. “On the protection side, that means AI
Investment and regulation matter. But the defining factor will be the depth and adaptability of the talent base

and ML security engineers who understand how to secure LLM applications, RAG architectures and agentic systems against adversarial manipulation. Within the SOC, roles such as AI SOC Orchestrator reflect a shift toward machine-speed detection and coordinated AIassisted response. At the governance layer, AI Governance Leads and Ethics and Compliance Officers are becoming essential.”
Another frontier the region is already preparing for is quantum cybersecurity.
The implications may feel distant, but the groundwork must begin well before disruption forces it.
“Quantum readiness is relevant now because cryptographic transitions take years, especially at national scale,” Baltagi says. “Leaders sometimes focus on the date when quantum computers might break current encryption. The more strategic question is when migration must begin to avoid being caught mid-transition.”
This perspective underpins SANS’ partnership with the UAE
Cybersecurity Council, focused on strengthening quantum cybersecurity awareness and structured preparedness across the UAE. The collaboration recognises that postquantum transition is not a technical swap-out exercise; it is a nationalscale coordination challenge.
Cryptography is deeply embedded across government systems, financial infrastructure, energy networks and industrial environments. Identifying where it resides, understanding lifecycle dependencies and planning phased migration requires institutional clarity well before quantum capability becomes commercially disruptive.
“There is also misunderstanding around data longevity,” Baltagi notes. “Sensitive information with long confidentiality requirements may already be exposed to ‘harvest now, decrypt later’ risk.”
Preparing for quantum resilience, he argues, is about institutional readiness — building practitionerlevel capability and leadershiplevel understanding so that when migration becomes necessary, it is deliberate rather than reactive.
Across AI scale, cloud convergence and quantum transition, the conclusion converges on one defining variable.
“Investment and regulation matter,” Baltagi says. “But the defining factor will be the depth and adaptability of the talent base. Technology changes rapidly, and regulatory frameworks establish baselines. Leadership is ultimately demonstrated in how effectively teams detect, respond, recover and adapt.”
The region’s digital ambition is evident in its infrastructure and policy direction. The challenge is not whether technology is being adopted quickly enough, but whether protection, utilisation and governance are maturing at the same pace. The next phase is ensuring capability grows in parallel with innovation.
Securing the next era — whether driven by AI, quantum or whatever follows — will depend on embedding operational discipline into acceleration.
In a region moving at scale, that discipline may prove to be the decisive advantage.

THE TRUST MANDATE
CXO Insight ME, powered by Corelight in collaboration with Malcrove, hosted an exclusive CXO roundtable examining how AI is reshaping the SOC — and why trust, data structure and network evidence now define security maturity

Artificial intelligence has shifted from proof of concept to operational dependency inside the enterprise SOC. Across the Middle East, organisations are embedding AI into detection workflows, automation layers and response playbooks. At the same time, attackers are doing exactly the same. The result is not simply more sophisticated defence — it is acceleration on both sides. Exploitation windows are shrinking. Dwell time is collapsing. Tolerance for
false positives is diminishing. And the margin for misjudgement, particularly in regulated and critical sectors, is narrowing.
These tensions shaped a recent executive roundtable hosted by CXO Insight Middle East in collaboration with Corelight. Around the table were CIOs, CISOs and senior technology leaders spanning government, finance, healthcare, industrial operations and energy. The discussion moved quickly beyond hype. The central issue was practical: if AI is now embedded in the SOC, what determines whether it adds clarity — or simply scales confusion?
For Corelight, the starting point is Network Detection and Response.
Basil Shahin, Regional Sales Director at Corelight, opened by addressing the velocity shift underway. “The speed at which vulnerabilities are exploited has changed,” he said. “Back in the day, it used to take weeks and months for attackers to reverse engineer and use a vulnerability to their advantage. Today that has been shrunk into hours and minutes. AI in the hands of bad guys can be very bad.”
But he cautioned that matching speed with speed is not enough. The differentiator lies in data structure.
“We fed some AI models some okay data — not very complete or comprehensive — and then we fed very clean, very pristine data and asked it to generate output,” Shahin explained. “It was a huge difference. That was actually a very important lesson for us. Fundamentally, algorithms are great, and they’re going to continue to become more advanced, but the underlying data is extremely important — how you format that data.”
He described high-quality telemetry as “clean fuel.” Without it, AI does not fail loudly — it produces shallow answers.
Trust, Shahin suggested, is built at that layer. When AI outputs are backed by structured, contextualised network data, confidence follows. When they are not, doubt creeps in — even if the alert looks convincing.
Corelight’s NDR platform builds on Zeek, the long-established opensource network security monitoring
framework. “We invested in a data format 25 years ago. It’s still tried and tested today,” Shahin said. That consistency allows thousands of attributes — protocol behaviour, session characteristics, file hashes — to be extracted and structured before analytics are applied.
He drew a clear distinction between roles. “Machine learning is more focused for us on the detection part, whereas generative AI is more focused on the automation part.” Detection models surface behavioural anomalies; generative layers assist analysts in interpreting implications and next steps.
“What’s really important is collecting a lot of traffic,” he added. “That traffic contains header information, ports, hashes — thousands of elements that we convert into a schema. That’s what enables us to apply models effectively.”
Even so, he stressed restraint. “There is no technology in the world that will stop everything. That’s why the human element is important. Automation left blindly is not the right approach.”
That operational perspective was reinforced by Mark Pearce, COO of Malcrove, a regional managed security services provider operating across complex, hybrid environments. His focus was less architectural and more practical — what happens when theory meets real-world pressure.
“We have a golden rule,” Pearce said. “They must verify.” Verification, he notes, is not about slowing automation down. It is about maintaining trust between analysts, tooling and executive stakeholders. Without that confidence, speed becomes a liability.
“Our SOC teams are becoming ever more reliant on AI, but we must have that confidence between the AI and the network evidence that has come through.”
Alert fatigue remains a reality.
“There’s lots of false positives. There’s the dreaded analyst fatigue,” he noted. “You see analysts just pushing things through and relying on AI. We’re not that kind of organisation.”
Instead, Malcrove treats NDR as





an evidentiary backbone. “We’re strengthening our threat hunting and investigation through this evidence base,” Pearce said. “It’s making our analysts better and helping them take better decisions.”
In several customer cases, tracing lateral movement across east-west traffic — rather than relying solely on endpoint alerts — shortened investigations and prevented unnecessary escalations. In tightly regulated environments, that distinction can determine whether an event triggers disclosure or is contained quietly and confidently.
Dr Ahmed Alketbi, Co-Founder and General Manager of Malcrove, extended the conversation to detection strategy itself. Signaturebased approaches, he noted, cannot keep pace with adaptive adversaries who deliberately avoid repetition. The shift must be behavioural.
Detection must therefore shift from “Is this known bad?” to “Is this normal for this environment?”
Behavioural baselining, particularly across east-west traffic, becomes critical in that context. In hybrid and distributed estates, internal movement often carries more risk than perimeter intrusion. Anomalies — unusual authentication paths, unexpected data transfers, deviations in service communication — reveal more than static indicators.
Following the presentations, the roundtable discussion opened into broader architectural and operational considerations.
Leaders from financial institutions and government entities acknowledged that attackers are “always faster,” particularly when leveraging AI-assisted tooling. One participant observed that what once took hours to exploit can now unfold in minutes. The challenge, he noted, is compressing detection and response timelines without amplifying false positives and overwhelming analysts.
Behavioural baselining across eastwest traffic is increasingly critical, particularly in hybrid estates where internal movement often presents greater risk than perimeter intrusion. Unusual authentication paths, unexpected service communications and anomalous data transfers frequently tell a clearer story than static indicators.
As the discussion broadened, participants acknowledged that attackers are “always faster,” particularly when leveraging AI-assisted tooling. What once unfolded over hours can now happen in minutes. The challenge is compressing detection timelines without overwhelming analysts with noise.
East-west visibility was raised repeatedly. With encrypted traffic increasing and workloads distributed across cloud environments, perimeter controls alone offer limited assurance. Shahin clarified that Corelight’s sensors process traffic locally, extracting relevant metadata rather than exporting full packet
captures. “It’s extracting the right data that is needed for analysis,” he said. Structured metadata provides long-term visibility without the burden of indiscriminate storage.
OT environments introduced further complexity. In systems where endpoint agents are not viable and downtime is unacceptable, network telemetry becomes the primary source of visibility. Dr Alketbi noted that while availability remains paramount, the relative stability of such environments can make behavioural deviations more apparent when baselines are properly established.
Across the table, the discussion consistently returned to one operational reality: AI may accelerate detection, but its effectiveness depends on the quality and structure of the telemetry beneath it. Automation can reduce triage time, generative models can interpret payloads, and machine learning can surface anomalies. Yet when incidents escalate beyond the SOC, decisions still rest on evidence that can be traced, explained and verified.
As the session drew to a close, the emphasis was on disciplined implementation. In an environment of compressed timelines and heightened scrutiny, network evidence remains what allows organisations to answer difficult questions with confidence — a foundation that, more than automation alone, shaped the tone of the discussion.
Basil Shahin, Regional Sales Director, Corelight
Mark Pearce, COO, Malcrove
Dr Ahmed Alketbi, Co-Founder & GM, Malcrove
INTELLIGENCE ON RECORD
On the sidelines of Oracle SuiteConnect Dubai, Nicky Tozer, SVP, EMEA, Oracle NetSuite, and James Chisham, VP, Product Management, Oracle NetSuite, outlined how they see ERP evolving as AI becomes embedded across enterprise systems

Across industries, AI conversations are increasingly shifting from experimentation to operational integration. CFOs and CIOs are no longer asking whether to use AI, but where it belongs. In many organisations, that question leads back to ERP — the system that holds financial truth, governs transactions, and underpins reporting. As intelligence moves closer to core business processes, the debate is less about replacing ERP and more about redefining its role.
For Tozer, the starting point is simple: AI does not sit outside ERP. It sits inside it.
“It’s a topic that comes up quite a lot,” she said. “You’ve seen a lot about what AI can do around the edges of ERP and how it can be embedded into ERP systems to drive value. But in the end, there has to be a system of record.”
Her position is that ERP’s role as the trusted source of financial and operational data does not diminish as AI scales. “There will always be an ERP system of record, and it
will increasingly have AI embedded within it,” she said.
That direction underpins NetSuite Next. Rather than treating AI as an overlay, it is built directly into workflows. “ERP will continue to be the system of record, but it will be embedded with more AI so it can drive more analytics and more autonomous, agentic workflows around the ERP system — helping with many of the manual tasks that ERP often generates,” Tozer explained.
Chisham returned to the importance of data integrity. “The system of record remains critical because the best data drives the best AI results,” he said. New interfaces, including conversational dashboards, are meaningful only if the data beneath them is unified and governed.
“The way we interact with ERP will change dramatically. You’ll just interact with the system conversationally,” he added, describing a model where a finance leader can ask for operational cash flow or margin performance and receive a direct response.
Having that unified platform also makes it the ideal foundation for AI, because AI is driven by data — and this is your data, unified in one place
NICKY TOZER
Oracle NetSuite
NickyTozer, Oracle NetSuite
Human-in-the-loop is fundamental. Trust is
critical
NetSuite’s positioning as a unified platform becomes more significant in that context. “If you go back to the premise of NetSuite, it’s a unified business platform to run your business,” Tozer said. “Our small to medium businesses minimise the number of additional applications they use because they centralise everything on NetSuite.”
That centralisation strengthens AI deployment. “Having that unified platform also makes it the ideal foundation for AI, because AI is driven by data — and this is your data, unified in one place,” she said.
She acknowledged that companies may never operate on a single application. “Whether you could ever say there will only be one application in a company is unlikely,” she said. “But it will definitely reduce that ‘hairball’ of integrated systems that creates risk, cost and time overhead.”
The technical foundation behind that model is shared with Oracle’s broader cloud infrastructure.
“NetSuite Analytics Warehouse uses Oracle Analytics Cloud. NetSuite is architected on the same platforms as Oracle. All our customers run on Oracle Cloud Infrastructure, and they are migrating to the Oracle Autonomous Database,” Chisham said.
“That gives us a strong technology foundation and enables us to layer AI services across NetSuite. AI sits as a layer across it — woven into the fabric of what customers do.”
Alongside embedded AI, NetSuite has introduced an AI Connector Service designed to allow external AI tools to interact with the system of record. Governance, Chisham emphasised, is built in from the outset.

“MCP bridges enterprise applications and AI systems. Security is top of mind,” he said. “It’s fully underpinned by NetSuite security roles and permissions. Agents cannot access data they’re not authorised to.”
The connector does not weaken data controls. “It’s wrapped in industry-standard authentication and security layers. Customer data is never shared externally or used to train models. We host an internal MCP server in NetSuite to keep it secure,” he added.
In practice, organisations can connect external AI tools while maintaining strict role-based access and data boundaries. The system of record remains protected, even as AI capabilities expand.
Human oversight remains part of the model. “Human-in-the-loop is fundamental. Trust is critical,” Chisham said. “Even if AI flags an exception, a person can step in, review and override if needed. Governance and traceability are key.”
Accountability remains with business leadership. “A CFO must trust and verify numbers. That
requires traceability and auditability. AI assists, but humans remain accountable,” he said.
Tozer described the balance plainly. “AI provides advice and assistance. It makes processes faster and less risky, but in the end, someone still says, ‘Yes, I accept this’ or ‘No, I don’t.’”
Measuring AI’s impact requires iteration. “AI success can be intangible because measuring it isn’t always straightforward,” Chisham noted. Feedback across a broad customer base, combined with the ability to drill down into source transactions and review the algorithm behind outputs, will shape how NetSuite evaluates progress.
Looking ahead, Chisham was clear that AI within ERP is not about displacing functions. “It wouldn’t render anything obsolete. It’s about automation, insight and agility. AI will automate manual processes, provide insights and help users make better decisions. It frees people from repetitive manual work so they can focus on higher-value analysis and insight — the work they actually trained for.”
JAMES CHISHAM Oracle NetSuite
James Chisham, Oracle NetSuite
THE GOVERNANCE IMPERATIVE
Cathy Mauzaize, President – EMEA, ServiceNow, outlines how enterprises must align AI scale with structured accountability

Today, most enterprises are no longer debating whether to adopt AI. Generative tools sit inside service desks.
Automation drives compliance workflows. Autonomous agents are embedded in business processes. The discussion has shifted from adoption to oversight — and to who is actually steering it.
“AI has become a CEO-level priority,” says Cathy Mauzaize, President – EMEA at ServiceNow. “Nearly half of CEOs are saying that if they don’t embrace AI, they risk being left behind. It’s transformative. But if you want to use AI at scale, governance must sit at leadership level.”
Compliance vs governance
The shift from execution to accountability demands a clearer definition of governance. For Mauzaize, governance must be clearly distinguished from compliance.
“Compliance is whether you respect rules — reporting to regulators, adhering to requirements,” she explains. “Governance is the framework that gives people space to innovate within boundaries. If you confuse the two, you risk slowing — or even killing — innovation.”
In 2026, that distinction is practical. The EU AI Act is operational, with enforcement underway, requiring enterprises to classify AI systems by risk, document datasets and maintain audit trails. At the same time, Gulf digital authorities have embedded expectations around transparency, traceability and data oversight into national digital strategies. Boards are no longer asking whether AI is deployed; they are asking how it is controlled.
“Governance gives you visibility and traceability,” Mauzaize says. “You need transparency across your stack. That’s why this is a leadership issue.”
Accountability does not sit with a single executive. CIOs typically own architecture, while CISOs have become central as risk
If you treat AI as a tool, you fail. If you treat it as a framework to connect data, employees and AI agents to put work into action, then it becomes both a business and technology agenda
and security concerns grow alongside AI’s operational footprint.
“In practice, CIOs are uniquely positioned,” she says. “And CISOs have to be in the room, because risk and security are inseparable from AI.”
This partnership has become more important as enterprises confront the real-world implications of autonomous systems. AI no longer just analyses data, it takes action. Decisions must therefore be accountable, traceable and aligned with policy.
“AI is not just a tool,” Mauzaize says. “It’s a framework. If you treat AI as a tool, you fail. If you treat it as a framework to connect data, employees and AI agents to put work into action, then it becomes both a business and technology agenda.”
One of the most visible stress points remains shadow AI — employees using unapproved tools because enterprise systems are fragmented or outdated. The productivity upside is real; so are the risks of data leakage, compliance gaps and inconsistent decision-making.
“If you don’t provide employees with modern, connected platforms, shadow AI becomes inevitable,” she says. “You reduce it by design. Provide modern tools. Embed security and regulatory controls directly into workflows. Governance must be built into the work itself.”
The AI Control Tower
This need for operational oversight is where the concept of an AI Control

Tower enters the conversation.
ServiceNow describes its AI Control Tower as a centralised governance layer built into its platform, connecting strategy, oversight, management and performance across enterprise AI initiatives.
Rather than monitoring isolated projects, the Control Tower provides a single environment to discover, manage and govern AI assets — including models, agents and workflows — whether native to the platform or sourced externally. It acts as a unified command centre, aligning visibility, lifecycle management and risk controls to business context.
“The world of tomorrow is made of huge amounts of data, huge amounts of AI agents, and still legacy systems,” Mauzaize says. “You need to make sure you can connect all of these and still orchestrate and operate at scale.”
The strategic value lies in bringing governance inside the workflow fabric rather than layering it on afterwards. Fragmented data weakens reliability. Unmonitored agents increase risk. Outputs that cannot be traced undermine accountability. The AI Control Tower is designed to create a single source of truth — a catalogue of AI systems, datasets and decision paths — allowing leaders to see what is deployed, how it behaves and where it intersects with core business services.
“If you don’t have the right data, there’s no AI,” Mauzaize says. “If
you cannot control all the agents connecting, you’re exposed to risk. You need to transform this into action through workflows.”
In practical terms, governance is not an overhead. It is the connective tissue between policy and execution — ensuring AI delivers value without creating unmanaged exposure.
Mauzaize positions the AI Control Tower less as a feature and more as a reflection of how ServiceNow views its role in the enterprise stack. The company runs approximately 80 billion workflows annually — a scale that places AI inside structured business processes rather than on top of them.
“We’ve seen what works — and what doesn’t — at scale,” she says.
The next phase of enterprise AI, she argues, will not be defined by adding more models. It will be defined by rationalising what is already deployed.
“We’re strengthening our stack, particularly in risk and security,” Mauzaize says. “Scaling AI requires connecting data, AI, workflows and security together. That’s the foundation.”
For leadership teams, the priority is structural. Organisations that embed oversight into enterprise architecture — rather than layering it on as compliance — are better positioned to scale responsibly.
“Visibility, traceability, execution — that’s what allows you to innovate with confidence,” Mauzaize says.

5 WAYS 2026 WILL SHAPE AI IN EMEA

By Ashley Woodbridge, Chief Technology Officer, Lenovo META
Artificial intelligence in EMEA is entering a new era defined not by experimentation, but by execution. Across the region, the conversation is shifting from “how do we build AI?” to “how do we power, govern, and scale it responsibly?”
The next twelve months will bring a significant convergence of three forces: energy constraints, regulatory fragmentation, and the rapid industrialisation of AI. Together, they will outline how enterprises plan, deploy, and extract value from AI at scale. Here are five key ways we can expect the impact to be felt.
1Every watt matters: Power becomes the first design principle
In 2026, energy will overtake compute as the primary design constraint for AI infrastructure across EMEA. Europe’s grid systems remain under strain, with the International Energy Agency projecting continued electricity demand growth and price volatility through 2026. At the same time, organisations are nearing sustainability commitments set pre-pandemic, forcing CIOs to treat energy not as an operational cost but as a strategic limitation. Every watt matters.
This shift will redirect infrastructure strategy. Data centre planning will begin with energy availability, efficiency, and location rather than server density. Poweraware design — low-footprint systems, advanced cooling, and intelligent workload placement — will become essential, particularly in secondary markets and edge locations with limited grid capacity. Regions with favourable energy profiles, such as the Nordics, will continue to attract AI investment, while Southern and Eastern Europe advance colocation and micro-grid development. Across the Middle East and Africa, hybrid and on-site generation models are moving into the mainstream.
As compute demand outpaces utility expansion, energy access becomes a competitive differentiator. In the UAE, projects such as the Mohammed bin Rashid Al Maktoum Solar Park are shaping AI planning, alongside liquid cooling and AI-driven resource optimisation to align with Net Zero by 2050 goals.
2Inference takes centre stage as AI moves to where the data lives
By 2026, the AI landscape across EMEA will undergo a fundamental shift: the centre of gravity will move from training massive models to running and refining them at scale through inference. As organisations deploy AI deeper into their operations, a powerful datagravity effect will take hold, pulling compute closer to the point where data is generated, regulated, and consumed.
For EMEA, this is amplified by stringent data-sovereignty requirements, regulatory fragmentation, and distributed markets. Enterprises will rethink infrastructure placement, moving away from centralised training environments toward edge and near-data-centre deployments that keep sensitive information within national or regional boundaries.
In the UAE, data sovereignty is driving investment in localised AI infrastructure. Federal Decree-
Law No. 45 of 2021 on Personal Data Protection reinforces the need to keep data within national jurisdiction as sectors such as healthcare, finance, and government adopt AI for real-time operations. Dubai’s Smart City initiatives reflect this shift, with edge AI applications such as traffic optimisation processing data locally for immediate response.
EMEA’s advantage will come from deploying intelligence where it creates the most value: close to the data and embedded in daily operations.
3
Regulation and sovereignty reshape the AI map
As energy and power become the physical constraints, regulation is emerging as the digital one. By 2026, the EU AI Act will be fully implemented, establishing a comprehensive framework for AI. Combined with data sovereignty requirements such as GDPR, this creates compliance zones across EMEA, where what is permissible in one jurisdiction may be restricted in another.
Infrastructure strategy therefore doubles as compliance strategy. Organisations must decide where models are trained, where data resides, and how inference workloads are deployed. Localcloud and edge architectures enable enterprises to keep data and compute within national or regional boundaries while still benefiting from AI-driven insight.
In the UAE, regulation is shaping responsible AI adoption. The UAE Artificial Intelligence Strategy 2031 prioritises ethical use, while enterprises leverage local data centres to protect sensitive information and align with national sovereignty goals, particularly in fintech and health informatics.
4
AI moves from experimentation to execution in EMEA
Organisations across the region are moving past proof-of-concept fatigue as macro-pressures, from economic volatility to tightening regulatory timelines, demand
By the end of 2026, AI will be a core business capability across EMEA: deployed, governed, and operationalised with far greater maturity than ever before
Agentic AI redefines businesses
By 2026, organisations across EMEA will move from traditional automation into agentic AI — systems capable of taking autonomous actions to personalise experiences, streamline operations, and augment employees. In retail, this means deeper engagement. In manufacturing, optimised production and reduced downtime. In financial services, real-time advisory support and stronger fraud detection. In the public sector, faster, more citizencentric services.
ROI from earlier AI investments, including computer vision and predictive maintenance, will fund this next phase.
technology that delivers measurable outcomes, not theoretical potential. With talent shortages intensifying and operational efficiency rising to the top of executive agendas, AI that simply tests an idea will no longer be enough.
Competition between Europe’s mature digital economies and the fast-scaling hubs of the Middle East and Africa is sharpening expectations for impact. CIOs will be evaluated on the business value deployed AI creates — in customer experience, supplychain performance, service responsiveness, and revenue growth. As early adopters demonstrate ROI, reinvestment will accelerate.
Amid regulatory complexity and evolving expectations for responsible technology, enterprises will prioritise AI that can be operationalised quickly, trusted fully, and governed consistently.
In the UAE, AI execution is becoming a differentiator. Initiatives such as Expo City Dubai’s sustainability tracking and the Roads and Transport Authority’s autonomous mobility trials show how deployment-ready AI can deliver tangible results across infrastructure and smart city programmes.
In the UAE, agentic AI is already being trialled in retail, manufacturing, and government, signalling readiness to adopt autonomous systems at scale.
Building the future responsibly By the end of 2026, AI will be a core business capability across EMEA: deployed, governed, and operationalised with far greater maturity than ever before. The organisations that thrive will be those that intentionally design for balance: between performance and constraint, innovation and oversight, automation and human accountability.
As power, policy, and people converge, the real question shifts from whether AI will transform the enterprise to whether enterprises have built the physical, ethical, and operational foundations to sustain that transformation. Success will belong to those that treat responsible AI not as a compliance exercise, but as a strategic advantage.
In the UAE, this balance will be critical to aligning AI transformation with long-term sustainability and compliance goals. Successful organisations will invest in building locally governed, globally informed AI systems capable of both scaling impact and maintaining trust among customers and regulators alike.
FROM HALLUCINATION TO CONTROL

WBy Fernando Cea, VP of Technology MENA & APAC, Globant
hat do a watchmaker and a doctor have in common? Both are expected to be perfectly accurate. That phrase, which now seems from another era, could today apply to what one expects from artificial intelligence.
In 2023, lawyer Steve Schwartz was involved in one of the most famous AI hallucination incidents. As the attorney for Roberto Mata, who was suing an airline over a flight issue, he submitted a declaration citing non-existent case law as well as real cases with errors. When the Manhattan court pointed this out, his defence was that he had drafted the brief using ChatGPT.
The mistake became a global headline and a cautionary tale. Here’s the truth: hallucinations haven’t gone away, but they’re happening less often and new safeguards and symbolic tooling are making AI more reliable than ever.
The lesson of this incident is clear: we shouldn’t fear AI hallucinations, but we need to understand them, minimise them (when needed), and then make sure humans remain in the loop.
Why hallucinations happen AI has a margin of error. Accepting this starting point is key to understanding the benefits – and the risks – when interacting with a chat
or developing AI software. We cannot bury our heads in the sand.
In September 2024, a group of researchers published an article in Nature analysing 243 cases of distorted information generated by ChatGPT hallucinations. They classified the errors into seven main categories for the public, for organisations, and to improve new AI versions.
They concluded that hallucinations could arise from data overfitting (i.e. analysing it too literally to interpret it correctly), logical errors, reasoning mistakes, mathematical errors, unfounded inventions, factual errors, or text output issues.
These errors are possible because generative AI doesn’t “know” facts in the human sense; it predicts patterns. That’s why outputs can look perfectly credible, yet be incorrect.
Still, it’s important to keep perspective: with more than 700 million people using these systems weekly, such errors remain the exception, not the rule.
Human supervision serves as a quality guarantee
We can understand the problem of hallucinations and take advantage of increasingly superior models, but AI adoption will not succeed without human oversight. Even the most advanced agents need it. The human-in-the-loop model is the new workplace dynamic.

Anyone who thought they could stop using their brain and let AI do everything will be disappointed. To deal with hallucinations, we must ask whether a response could fall into one of the error categories previously mentioned and verify the data sources.
Imagine this process within a company. An AI agent records an interview with a client about their requirements. Then, it can create a story map, develop software, present an MVP, and conduct tests. All of these tasks, which previously took weeks, can now happen in hours. However, the final word belongs to a person. For example, if at any stage the AI hallucinated or the collected data was insufficient, someone must serve as the quality guarantor.
For leaders, this oversight cannot be left vague – it must be operationalised. Human supervision of AI agents should include, for example:

We can understand the problem of hallucinations and take advantage of increasingly superior models, but AI adoption will not succeed without human oversight
with the same number of employees to serve twice as many clients, but critical thinking – and structured supervision – remains the verification that it works.
AI models are becoming more accurate
In February 2025, Sam Altman announced that the ChatGPT 4-5 model had halved the probability of hallucinations. In other words, it would be unlikely for a Schwartz-like case to happen again.
Gemini, DeepSeek, and Grok have also improved their training data architectures. Each model has its own comparative advantages, but in the ranking that evaluates intelligence, the Massive Multitask Language Understanding (MMLU), seven of them already have a response success rate of 80 percent or higher.
• Tiered review checkpoints where humans validate AI outputs – such as data summaries, client-facing drafts, or generated code – before results move forward. This prevents flawed outputs from compounding.
• Red flag protocols that train teams to recognise and escalate risky AI responses, whether fabricated citations, misapplied logic, or outdated references. Standardised checklists reduce the chance of blind acceptance.
• Pairing AI with domain experts for high-stakes contexts like financial forecasts, healthcare insights, or legal contracts. Experts can spot nuanced hallucinations that algorithms miss.
• Continuous auditing of models through sampling and back-testing AI outputs against ground truth data, treating oversight as ongoing quality assurance rather than a one-off step.
AI literacy is already one of the most in-demand skills in the job market, according to the World Economic Forum. Technology can increase productivity, allowing a company
One of the biggest drivers of this trend is Context Engineering. Instead of relying solely on training data, several approaches are enabling AI to fetch relevant, up-to-date information from external sources before answering. This simple idea dramatically improves reliability. Competition among AI providers is fuelling a virtuous cycle: better architectures, better safeguards, and fewer hallucinations.
Hallucinations shouldn’t stop AI adoption
The story of AI hallucinations is not one of fear, but of engineering maturity. Mistakes will happen, just as they do with people, but the key is how systems are designed to prevent, detect, and recover from them. Many of today’s AI platforms show that when learning, symbolic reasoning, and repeatability are built into the architecture itself, oversight becomes part of the fabric rather than an external patch.
AI is not replacing judgment; it is amplifying it. The organisations that win will be those that understand hallucinations not as a reason to slow down, but as a reason to design smarter. Human oversight and platform resilience together form the real guarantee of quality in the age of intelligent systems.
THE SAFETY RESET
Experts explore how trust, user behaviour, and governance are emerging as the foundations of digital safety in an AI-influenced internet
For much of the past decade, internet safety sat largely within the remit of IT teams, platform providers, and regulators. Risks were framed in technical terms, controls were infrastructure-led, and responsibility was often delegated down the organisation. That model no longer reflects how the digital world operates.
By 2026, the internet is inseparable from everyday business activity. Identity has replaced the perimeter. AI systems sit inside
workflows rather than at the edge. Employees, customers, and partners interact continuously with intelligent systems that influence decisions, behaviour, and trust— often without clear visibility into how those outcomes are shaped. In this environment, digital safety is no longer a purely technical concern; it has become an operational and leadership issue.
This is the context in which Safer Internet Day 2026 is being marked. This year’s theme, ‘Smart tech’, safe choices – exploring the safe
and responsible use of AI, reflects a growing consensus across the security and technology industry: the challenge is no longer whether AI is being adopted, but how responsibly it is being used.
From infrastructure risk to behavioural risk
Enterprise security strategies were traditionally built around infrastructure—networks, endpoints, and applications. Today, risk is increasingly behavioural. It emerges from what users trust, what they
authorise, and what systems are permitted to act autonomously.
AI has accelerated this transition, as generative models influence how people search, learn, communicate, and make decisions. Inside organisations, AI tools are embedded across productivity platforms, analytics workflows, and customer engagement systems, often faster than policies can keep pace. The gap between formal controls and real-world use has become a material source of exposure.
This behavioural layer is now where digital safety begins—or breaks down.
Meriam ElOuazzani, Regional Senior Director for the Middle East, Turkey, and Africa at SentinelOne, frames the issue in terms of awareness rather than restriction.
“Making the proper judgments is important, as the topic ‘Smart tech,
The only way to be safe in an AI-driven future is to make wise judgments for both people and machines
MERIAM ELOUAZZANI
Regional Senior Director –META, SentinelOne
safe choices’ reminds us. Since kids and teenagers commonly utilise AI tools, their safety is more determined by the decisions they make than by filters or settings.”
While her focus is youth digital safety, the parallel for enterprises is clear. Policies and safeguards matter, but they are effective only when people understand how technology shapes behaviour.
“AI can quietly affect behaviours, views, and trust while supporting innovation and learning,” says ElOuazzani. She notes that this dynamic applies just as strongly to employees using AI-assisted tools as it does to younger users navigating online platforms.
Identity has become the primary attack surface
As behaviour defines exposure, identity defines access. Across sectors, security leaders are seeing


the same pattern: attackers are no longer primarily exploiting technical vulnerabilities; they are gaining entry by compromising credentials.
Sophos’ upcoming Active Adversary Report highlights the scale of the issue. Compromised credentials accounted for 42.06 per cent of attacks in 2025, making them the most common initial access vector. This reflects how automation and AI have reshaped social engineering, allowing attackers to operate with speed, precision, and volume.
“The way attackers are using automation and generative AI to massively increase the speed and volume of their attacks suggests that attacks will become faster and more sophisticated,” says John Shier, Field CISO for Threat Intelligence at Sophos. “The best approach to protecting our identities and digital data is to take a proactive stance on defence.”
What makes this challenge particularly difficult is that attackers are targeting people rather than systems. “Criminals are increasingly targeting people rather than devices,” Shier explains, pointing to AI-generated phishing emails, messages, and voice-based scams designed to bypass instinctive scepticism.
Organisations need to understand where AI is being used across the business—not just the tools leadership approved, but the AI showing up in workflows, plugins, agents, and third-party platforms
Chris Cochran, SANS Institute
Meriam ElOuazzani, SentinelOne
CHRIS COCHRAN Field CISO and Vice President of AI Security, SANS Institute

Criminals are increasingly targeting people rather than devices
For enterprises, this has forced a reassessment of priorities. Patch management and endpoint security remain necessary, but they are no longer sufficient on their own. Credential hygiene, phishingresistant authentication, and user awareness have become frontline controls, inseparable from broader security strategy.
Enterprise AI and the visibility gap
Alongside identity risk sits a different but related challenge: visibility. Many organisations are adopting AI faster than they can account for it.
AI now appears across approved platforms, shadow IT tools, thirdparty services, and embedded agents operating with varying degrees of autonomy. For security and risk teams, the immediate concern is not model performance, but knowing where AI exists and what it can access.
Chris Cochran, Field CISO and Vice President of AI Security at SANS Institute, describes visibility
as the starting point. “The first step is visibility. Organisations need to understand where AI is being used across the business—not just the tools leadership approved, but the AI showing up in workflows, plugins, agents, and third-party platforms.”
That visibility must extend beyond surface-level deployment. “Maintaining an AI inventory is quickly becoming table stakes,” Cochran adds, highlighting the importance of understanding models, data sources, and external dependencies through mechanisms such as AI Bills of Materials.
As AI agents take on greater autonomy, traditional serviceaccount assumptions begin to fail. “Agents should be treated like operators on the network, not traditional service accounts,” Cochran explains. He highlights the need for explicit identity, short-lived authentication, and continuous monitoring. In practice, this shifts security from static trust models to controlled, observable access.
From awareness to accountability
What connects youth digital safety, credential abuse, and enterprise AI governance is a shared reality: digital safety now depends on accountability.
Technology remains essential, but it no longer determines outcomes on its own. Decisions made by users, employees, leaders, and autonomous systems shape exposure every day. Controls work only when they are understood, applied consistently, and aligned with how technology is actually used.
ElOuazzani emphasises this shift succinctly: “When we give children knowledge and cyber awareness, they use technology the right way. The only way to be safe in an AI-driven future is to make wise judgments for both people and machines.”
The digital world is now woven into how we learn, work, and operate as organisations. Making the internet safer is no longer about limiting access or reacting to threats after the fact. It is about equipping people to make better decisions, ensuring systems operate within clear boundaries, and recognising that responsibility does not sit with technology alone. Safety in an AI-influenced world is built through judgment, governance, and everyday choices that shape trust at scale.
John Shier, Sophos
JOHN SHIER Field CISO for Threat Intelligence, Sophos
THE 2026 TEST: ADAPT OR STALL

ABy Kim Custeau, EVP Portfolio Management, AVEVA
s we step into a year of slowing economic growth, industrial management becomes ever more demanding. There will be greater pressure to cut costs and streamline operations, because even small gains can enhance margins. Expansion gives way to efficiency. Only one scenario avoids a global balance sheet reset: accelerated productivity growth.
Productivity can spark the innovation and resilience needed to tackle macro challenges ranging from geopolitical shocks and workforce gaps to managing the net-zero transition. Continued success will likely depend on redesigning operations to function profitably in permanently highercost environments—through digital transformation, better operational visibility, rethinking business processes and encouraging open communications across teams.
That’s true for each of the year’s megatrends. Here’s how industry can use existing solutions to raise its game in 2026 and set the tone for the years ahead.
Climate events are now an operating reality
Extreme weather events are now more common. Climate-related losses reached $165 billion in the first six months of 2025, with earnings releases referring to climate resilience more frequently. Forward-thinking businesses have already onboarded the adaptive
technologies essential to staying resilient. A particularly sensitive flashpoint stems from water scarcity issues. On this front, Spain’s Acciona has shown how replicating its operations digitally can increase production capacity and measure changes to water composition, such as from climate-related pollutants. Similarly, as wildfires increase due to hotter, drier summers, pre-emptive mitigation is the way forward for companies like Avista. The Pacific Northwest utility uses a fire-risk dashboard to gather data from tens of thousands of sources across its operational footprint, so operators can proactively turn off the grid to prevent fires and reduce outages.
Electricity grids become the energy transition bottleneck The global energy access gap has worsened on the back of

Globally, technical skills such as AI, cybersecurity, and technological literacy are forecast to see the largest demand increases within just five years
population and industrial growth, and 730 million people have no electricity. On the other hand, demand is set to increase, with data centres in particular on course to double current consumption by 2030. While new technologies are entering the system at speed, according to the IEA, permitting delays now hold back at least 3,000 gigawatts of renewable projects – enough to power two billion households for a year. What that means depends on your business. For utilities, optimisation will take centre stage, a strategy Ontario Power Generation has used to save $4 million over two years. Industries need to do more with less—but also consider integrating on-site renewables.
Fractured supply chains are upending established business flows
From manufacturing to chemicals and automobiles, geopolitical issues are altering trade pathways.

Mexico already accounts for 15.4 percent of US trade, overtaking China at 13.9 percent. Meanwhile, one-third (33 percent) of companies are developing nearshoring or onshoring plans, with the majority (78 percent) citing trade uncertainty as their top concern. Manufacturers need to rebuild decades-old ingredients supply chains but shifting cargo routes also take their toll on maritime operations. Software can now continuously deliver industrial intelligence, such as tariff scenarios, risk planning and logistics costs—thanks to end-toend data visibility. The result is a new kind of human and technology partnership that enables companies to rebalance networks without long delays, while preparing for a future of human-machine collaboration.
AI’s multi-layered impact will touch nearly every sector
Artificial intelligence (AI) has advanced from hype to deployment and will move closer to achieving
a headline impact of nearly $15.7 trillion in global economic value over the medium term. Nine out of ten companies (88 percent) regularly use AI in at least one business function. By year’s end, the science will likely be used in many different ways, as multiple types of AI are used in practical and measurable ways to support complex outcomes—whether these are generative and vision applications or AI agents that automate routine tasks. Gartner predicts that by December 2026, some 40 percent of enterprise applications will host AI agents. AI enables multiple outcomes, depending on application, data quality and human interpretation. Predictive maintenance and quality control are the most common use cases across industries from manufacturing to utilities and energy. For some, the gains can be transformative: AI insights from operations have yielded €8 million annually for consumer goods
manufacturer Henkel in value and sustainability gains, or a total of €37 million to date.
Labour shortages are becoming structural
Demographic changes and new ways of doing business are driving systemic labour gaps. US manufacturers could face 1.9 million unfilled jobs by 2033 if current trends persist. Globally, technical skills such as AI, cybersecurity, and technological literacy are forecast to see the largest demand increases within just five years. The structural shortage extends to renewables, mining and energy, with universities unable to produce specialised technicians in sufficient numbers. Industrial platforms that extend worker productivity – such as by way of assisted maintenance, onsite training, automated quality checks and knowledge capture from retiring employees – are the only viable path to meeting output targets with available headcount, as the WEF notes. Seward Power Generation’s waste-coal-fired facility in Pennsylvania, for example, speeds up training time for new recruits and improves operational performance with digital simulator technology.
The year when industry moves from reactive to proactive
Underlying these trends is a common thread. With end-to-end data visibility and AI, industrial software can now scale to tackle increasingly complicated business problems and is evolving from a tool that reports on operations to one that runs them. In the process, human judgement is being augmented and strengthened across the value chain.
Industrial enterprises face what looks set to be a period defined as non-linear, accelerated, volatile but interconnected. The companies that thrive – won’t be those with the most advanced robots or the biggest datasets. Rather, they will be those that can do the math to orchestrate intelligence across their operations, by turning disconnected tools into integrated systems that learn and adapt continuously.
BEYOND THE PERIMETER
Andrew Elvish, Global Vice President of Marketing at Genetec, discusses how physical security is shifting from a cost centre to a source of operational and strategic insight

For a long time, physical security lived quietly at the edges of enterprise strategy. Cameras, access control systems, and alarms were installed to meet compliance requirements, reduce risk, and respond when incidents occurred. They were essential, but rarely discussed beyond security teams—and almost never treated as a source of insight into how organisations actually operate. That position is changing as facilities, infrastructure, and
operations become more digitised, with physical security systems generating continuous streams of real-world data. What was once static infrastructure is now closely connected to IT environments, analytics platforms, and operational workflows. As a result, physical security is being reassessed not just for protection, but for what it reveals about efficiency, resilience, and decision-making.
These shifts are reflected in the Genetec 2026 State of the Physical
Security Report, which captures how security, IT, and business leaders are rethinking the role of physical security inside the enterprise. Speaking to CXO Insight ME at Intersec , Andrew Elvish, Global Vice President of Marketing at Genetec, points to a clear change in how the industry frames its priorities.
“The conversations, the attendees, and the questions are fundamentally different,” he says. “Today, people are asking about resiliency, cloud adoption, cybersecurity best practices, compliance, and lifecycle management.”
The discussion has moved beyond devices and specifications. Physical security is increasingly evaluated alongside other enterprise systems, with expectations around integration, governance, and measurable outcomes.
From overhead to operational insight
One of the strongest signals in the Genetec’s latest report is how organisations now interpret the value of physical security data. Historically, security was treated as a necessary expense—something invested in to mitigate worst-case scenarios, rather than to actively improve how the organisation runs.
According to Elvish, this mindset has increasingly changed.
“Technologies like Genetec Security Center and our Cloud Link appliances are no longer viewed just as protective tools,” he says.
“They’re seen as sources of strategic advantage—ways to understand operations better.”
In practice, this means physical security data is no longer confined to security teams. It is increasingly shared across IT, HR, and analytics platforms, contributing to a broader
understanding of how facilities, people, and processes interact.
This broader visibility has also changed who engages with security systems. Senior executives are now closer to the data than they were in the past.
“Today, executives want dashboards, Power BI reports, performance metrics, and visibility into how efficiently threats are handled,” Elvish explains. “We’re seeing CEOs—from airports to oil and gas—actively engaged in physical security data.”
The operational impact of this shift is particularly visible in investigations. As platforms become more unified and data more accessible, the time required to understand incidents has dropped sharply.
“Investigations that used to take four to twelve hours are now being completed in minutes,” Elvish says. “That kind of time savings is critical when dealing with executive threats, infrastructure risks, or incidents that attract investor and public scrutiny.”
As physical security becomes more integrated with enterprise systems, it increasingly functions as a practical lens into how organisations respond under pressure—how quickly they act, how coordinated their teams are, and where inefficiencies surface.

AI, cloud, and the question of control The report also highlights growing tension around artificial intelligence. Interest in AI is strong, but confidence remains conditional.
“In our latest report, 70 percent of end-user respondents said they’re interested in AI—but majority of those also said they have serious concerns,” Elvish says.
Those concerns are rooted in accountability. Security and IT leaders remain responsible for outcomes, even when systems rely on automation. “CIOs and CSOs are accountable for AI-driven decisions, and that creates risk,” Elvish notes. “We’ve already seen legal cases where AI-powered systems made decisions that companies were held responsible for.”
As a result, many organisations are cautious about fully autonomous systems. There is growing preference for AI that supports human judgement rather than replacing it.
cloud deployment across the Gulf, especially in the UAE and Qatar, with Saudi Arabia not far behind. At the same time, physical security data introduces sensitivities that require careful architectural decisions.
“Data can remain on-site, fully sovereign, and disconnected from the internet, while still benefiting from cloud-based management and updates,” Elvish explains. “Our role is to support both, without compromising sovereignty.”
For many organisations, the challenge is not whether to adopt cloud or AI, but how to do so without losing control over critical systems and sensitive data.
AI supports decision-making, but humans remain in control
“AI supports decision-making, but humans remain in control,” Elvish says. “That’s why we use the term Intelligent Automation—automation surfaced clearly, with trained professionals deciding what action to take.”
Cloud adoption raises a parallel set of questions, particularly in regulated environments. According to Elvish, the report points to a strong and growing appetite for
Looking ahead, physical security is increasingly seen as a valuable source of insight into what is happening across facilities, how organisations respond to risk, and where operations can improve. The focus has shifted toward visibility, measurable outcomes, and control— using data to reduce investigation time, improve decision-making, and strengthen resilience. Whether through cloud architectures or AIdriven automation, the emphasis remains on transparency, human oversight, and practical impact. In that context, physical security is being evaluated not just for protection, but for the insight it brings into how organisations operate and perform.
BUILT TO GROW
In conversation with Contributing Editor Ruchika Sharma, Shailesh Davey, Co-founder and CEO of Zoho Corporation, outlines the company’s commitment to long-term thinking, building trust through privacy by design, and practising transnational localism
As Zoho expands its enterprise portfolio, how do you prevent complexity from creeping in while still encouraging innovation?
Zoho addresses complexity through a combination of internal usage, design reviews, and disciplined product validation. Every new solution is first deployed internally, which we call ‘eating our own dog food.’ With close to 18,000 employees worldwide using Zoho and ManageEngine tools, this internal ecosystem becomes a largescale testing ground.
Additionally, UI/UX, security, and privacy reviews are built into the development process, and beta customers are engaged early to provide real-world feedback. When a solution risks adding unnecessary complexity, the team is empowered to make the hard call to simplify, even if it means going back to the drawing
board. This approach preserves agility while ensuring innovation remains usable, scalable, and customer-friendly.
With enterprises consolidating vendors and scrutinising ROI, how has that shaped what Zoho chooses to build and not build?
Zoho’s philosophy has remained consistent: build within its means, take a long-term view, and stay true to what benefits the customer. Being privately held, the company isn’t driven by short-term shareholder pressure, so it avoids shortcuts and fads.
Rather than pursuing every market opportunity, Zoho focuses R&D on areas that directly enhance value for enterprise customers, particularly platforms, security, and AI integration. By investing more in R&D instead of marketing, Zoho ensures that innovation and engineering quality drive customer satisfaction and organic growth.

Zoho’s philosophy has remained consistent: build within its means, take a long-term view, and stay true to what benefits the customer
As enterprise platforms become more interconnected, how does Zoho design its architecture to limit blast radius, so a failure or breach in one product doesn’t cascade across the stack?
Zoho’s data centre and product architectures are intentionally designed for fault isolation. Each country operates an independent data centre that doesn’t interact with others, hence minimising the blast radius of a potential issue and supporting local compliance with data protection laws.
On the engineering side, products follow asynchronous messaging
patterns and avoid tight coupling between services. Regular code reviews and automated analysis make sure these rules are maintained, ensuring operational resilience and limiting cross-system exposure during failures or breaches.
What cybersecurity strategies is Zoho adopting as attacks shift from targeting enterprises to targeting entire geographies?
Cybersecurity is one of Zoho’s top three focus areas for 2026 and beyond, alongside AI and platform development. ManageEngine is rolling out a new wave of security products, including next-generation antivirus, anti-ransomware, cloudbased SIEM, and Zero Trust access solutions.

Zoho will continue advancing in three focus fronts –AI, security, and platform enablement
The goal is to address the growing strategic role of IT while helping CIOs manage evolving security threats with a single, dependable vendor across multiple layers. Every launch is guided by Zoho’s commitment to being a long-term, stable partner, not just a product provider, in the global technology landscape.
What did Zoho’s data centre investments in Saudi Arabia and the UAE signal to customers about trust and long-term commitment?
The new data centres in the UAE and Saudi Arabia are a clear demonstration of Zoho’s deepening commitment to the region. After 15 years of partner-led presence, the company now runs full local offices,
around 80 people in Dubai and about half that in Saudi Arabia, with locally based compliance and security teams.
By operating its own infrastructure and aligning with national data laws, Zoho signals reliability and intent to be a long-term partner. The investments also align with growing government digitisation efforts in both markets, where Zoho expects an increase in enterprise and publicsector adoption.
As AI adoption accelerates, which data governance or sovereignty risks do CEOs most often underestimate?
The biggest underestimated risk is data leakage from AI model interactions. Zoho tackles this through choice and transparency: enterprises can bring their own keys to secure hosted large models, use open-source models on Zoho’s infrastructure, or choose models developed by Zoho itself. If customers select Zoho-built models, they can be assured that data never leaves Zoho’s data centres. This multi-option strategy balances control, compliance, and functionality, giving CIOs and governments confidence over data sovereignty in an AI-driven era.
Looking ahead, what should customers and partners expect from Zoho over the next few years?
Zoho will continue advancing in three focus fronts – AI, security, and platform enablement. Expect a lineup of new cybersecurity and enterprise tools, deeper AI integration across products (both classical and generative), and broader adoption of the ‘platform’ approach, enabling enterprises to customise and build on Zoho systems.
At the same time, Zoho remains committed to its founding principles: long-term thinking, independence, customer-centric design, and reinvestment in R&D. Whether through transnational localism or privacy by design practices, Zoho’s next chapter will continue to blend innovation with trust and sustainability.
A LIGHTER HAND

FBy Salman Ali, Senior Manager – Solution Engineering, GCC, Riverbed Technology
or as long as IT operations has existed, so too has the ambition to make it invisible.
Terms such as self-healing networks, lights-out operations and zero-touch IT were already circulating in the late 1990s, when network management frameworks and early automation tools promised a future where systems could detect faults, fix themselves and move on without human intervention. Over the following decades, each new wave of technology has been positioned as the long-awaited breakthrough that would finally make this vision real.
And yet, despite all that progress, most IT teams today still spend a disproportionate amount of their time reacting to incidents, triaging tickets and firefighting issues after users have already been impacted. The concept of zero-touch digital operations has never been fully realised not because it was fundamentally flawed, but because the tools designed to deliver it never quite closed the gap between detecting a problem and actually resolving it.
In today’s digital landscape, effective network observability has become crucial for organisations aiming to ensure seamless digital experiences and robust security. With the proliferation of remote work, cloud services, and complex network architectures, traditional monitoring tools often fall short in providing comprehensive visibility and actionable insights.
Agentic AI changes the equation
Unlike previous generations of AI,
agentic systems are designed not just to analyse and recommend, but to act. They continuously observe digital environments, predict and detect signs of degradation, diagnose root causes using full-fidelity telemetry, and then autonomously execute remediation within clearly defined guardrails. In other words, they finally bridge the space between knowing and doing.
This matters because the complexity of modern digital estates has reached a tipping point. Hybrid work, cloud sprawl, SaaS dependency and increasingly distributed networks have made fully human-led operations unsustainable. Mean time to resolution has become less relevant than mean time to detect, because once an issue is identified early enough, an intelligent agent can often resolve it before performance degrades or users are even aware there was a problem.
Crucially, agentic AI operates across both proactive and reactive modes. It can intervene when early signals suggest something is about to go wrong, while still responding instantly to user-reported issues when they do arise. That dual capability is what brings zero-touch operations out of the realm of theory and into practical reach. Lowvalue, repetitive issues are handled automatically, while complex incidents are escalated to human experts with full context attached.
When IT stops firefighting, innovation becomes possible For IT leaders, this represents a structural shift in how work gets

done. One of the most persistent anxieties around AI is the fear that it will replace human roles. In reality, agentic AI does something far more pragmatic: it removes the drag of maintenance work that has quietly come to dominate IT teams’ days. Over time, we have normalised the idea that “keeping the lights on” is the core of IT’s job, simply because so much effort has been required to do it.
Imagine, instead, a more idyllic vision where once a system is deployed, it rarely if ever needs troubleshooting. Not because nothing ever goes wrong, but because issues are detected and resolved automatically, at machine speed. No, IT teams would not disappear overnight. Instead, they would be freed.
And that freedom fundamentally changes what IT teams are capable of contributing. When specialists are no longer consumed by alerts and interruptions, they gain the time and headspace to think creatively,
Governance and trust are foundational to successful agentic systems
challenge assumptions and engage deeply with the business. Innovation rarely happens in isolation. It requires collaboration with the employees closest to a problem, conversations with finance teams on feasibility, alignment with HR on workforce impact, and, increasingly, direct engagement with customers themselves.
When IT specialists are constantly pulled away to reset
devices, chase network issues or resolve application slowdowns, such transformation work slows to a crawl. When they are given the space to focus end-to-end on initiatives like this, the quality, ambition and pace of innovation changes dramatically.
This holds true across industries, whether it is a bank modernising customer onboarding, a healthcare provider rolling out virtual care services, or a logistics firm optimising real-time tracking. Transformation efforts demand deep, sustained attention. Agentic AI creates the conditions for that focus by quietly absorbing the operational noise that would otherwise fragment it.
Trust,
governance and human control remain central
None of this requires IT teams to surrender control. Governance and trust are foundational to successful agentic systems. Organisations define exactly which actions an agent can take autonomously,
where human-in-the-loop approval is required, and when escalation is mandatory. Every action is logged, auditable and fed back into a continuous learning loop that aligns the system with organisational priorities and risk tolerance.
Seen this way, agentic AI is no longer incorrectly framed as a replacement for human expertise, but rather as a new kind of teammate: one that never tires, never loses context, and is willing to handle the work that distracts skilled professionals from where they add the most value. It inverts the traditional support model. Instead of users raising tickets and waiting, issues are resolved and then reported. Instead of measuring success by how quickly teams respond, organisations begin to measure how rarely users are impacted at all.
Closing the gap between detection and response
After decades of promise, zerotouch digital operations are finally becoming achievable. This isn’t because systems have become simpler, but because intelligence has become actionable. By closing the gap between detection and response, agentic AI allows digital environments to manage their own health, while giving IT teams something increasingly rare – time. Time to innovate, to transform, and to build the future rather than endlessly repairing the past. Without modern visibility solutions that extend beyond the corporate WAN and data centre, IT teams are left in the dark, unable to diagnose performance issues or security risks. Organisations need a modernised observability strategy that integrates network intelligence across the distributed environment, enabling end-to-end visibility regardless of where traffic flows. Organisations must adopt modern observability strategies that leverage endpoint telemetry, metadata analysis, and AI-driven anomaly detection to maintain visibility without compromising Zero Trust security principles.

GOVERNED CONSENT

Sunil Paul, Co-Founder and MD, Finesse, discusses the importance of aligning digital platforms with the UAE’s evolving data protection framework
The UAE’s digital economy continues to expand across sectors. Organisations are deepening investments in digital platforms, analytics, personalisation and integrated customer journeys. Data now underpins marketing strategies, service delivery models and operational decision-making. Alongside this expansion, regulatory expectations have become clearer and more structured. Federal Decree Law No. 45 of 2021 — the UAE’s Personal Data Protection Law (PDPL) — requires organisations to demonstrate control over how personal data is collected and processed.
While much of the attention around PDPL focuses on governance frameworks and cross-border
transfers, one of the most immediate indicators of compliance maturity sits at the website layer: cookie and consent management.
Websites today operate as complex ecosystems of analytics scripts, advertising trackers, embedded tools and third-party integrations. These technologies are often deployed incrementally, without a consolidated understanding of what data is being captured or where it flows. Cookie governance compels that clarity.
The PDPL requires explicit and informed consent before nonessential cookies are activated. Consent must be obtained through a clear affirmative action. Analytics and marketing cookies cannot be enabled by default. Users must understand what data is collected
and for what purpose, and they must be able to withdraw consent easily. These requirements are direct, and the implications are broader.
To implement them properly, organisations must inventory tracking technologies, review third-party integrations, align legal requirements with technical configuration and maintain verifiable consent records.
In many cases, this process exposes gaps that extend beyond the website itself. Misaligned banners, uncontrolled scripts or undocumented trackers reflect limited oversight of data collection practices. For enterprises building advanced analytics or AI-driven capabilities, consent weaknesses introduce downstream exposure. Data sets derived without valid consent raise regulatory risk and undermine decision integrity.
Privacy posture is also increasingly scrutinised in procurement and enterprise partnerships. A poorly structured consent framework signals governance immaturity. It suggests that policy and execution are not aligned.
For many organisations, structured cookie and consent management should represent the first disciplined phase of PDPL implementation. It compels crossfunctional coordination between legal, IT, marketing and security teams. It establishes a consent lifecycle that supports broader data subject rights management and retention controls. Most importantly, it demonstrates operational accountability.
At Finesse, we work with enterprises to translate PDPL requirements into practical controls across websites, applications and backend systems. This includes consent management platforms, data mapping and governance alignment across business units. Cookie governance may appear modest compared to enterprisewide transformation programmes, yet it is often the clearest indication of accountability in action and sets the foundation for a sustainable privacy framework.


REOLINK: TrackFlex
Floodlight WiFi
Reolink has introduced its TrackFlex Floodlight WiFi, a hardwired outdoor security camera designed to deliver comprehensive coverage and detailed imaging without blind spots. The unit combines a dual-lens 4K camera system with pan-and-tilt controls to achieve 360° horizontal coverage for perimeter monitoring.
The camera’s dual-lens setup pairs a wide-angle 4K sensor for broad situational awareness with a secondary lens that supports up to 6× hybrid zoom for closer detail such as faces or license plates. Both views can be accessed concurrently in the companion
app for simultaneous wide and zoomed perspectives.
Integrated AI-driven autotracking allows the system to follow moving subjects across its field of view, and the combination of three passive infrared (PIR) sensors and automatic rotation helps capture events even beyond the current frame.
The unit includes dual adjustable floodlights rated up to 3,000 lumens with variable color temperature, providing fullcolor nighttime illumination and configurable lighting modes.
Other technical features include on-device AI video search, dual-band Wi-Fi 6 connectivity, microSD card support for local storage, and a built-in siren for deterrence. The camera’s design is intended for fixed outdoor installation and
INTEL: Panther Lake
Intel has announced its latest Core Ultra Series 3 processors, codenamed Panther Lake, marking the first client computing platform built on the company’s Intel 18A manufacturing process—the most advanced semiconductor node developed and fabricated in the United States.
Designed primarily for mobile PCs, the Core Ultra Series 3 lineup spans a range of configurations intended for ultra-portables, mainstream laptops, and performance systems. At the top end, select models offer up to 16 CPU cores, combining performance and efficiency cores to balance power and battery life. The processors integrate Intel Arc graphics with up to 12 Xe3 cores, enhancing on-chip graphics performance without requiring discrete GPUs in many designs.
The Series 3 chips also embed an AI Neural Processing Unit (NPU) capable of up to 50 trillion operations per second (TOPS), accelerating AI workloads locally on the device. Memory support includes LPDDR5X and DDR5, and the platform supports modern I/O standards such as PCIe 5.0.
Early performance figures from Intel and partners indicate significant gains in multithreaded CPU performance, integrated graphics throughput, and energy efficiency compared with previous generations. The processors are certified for use not only in consumer PCs but also in edge and embedded systems requiring continuous operation.

DELL: ULTRASHARP 52 THUNDERBOLT HUB MONITOR

Dell has unveiled the UltraSharp 52 Thunderbolt Hub Monitor (U5226KW), a large-format display aimed at professionals who require expansive screen space and high visual clarity.
The monitor features a 51.5-inch curved IPS Black panel with a 6K resolution (6144 × 2560) and a 120 Hz refresh rate, offering detailed imagery and smooth motion for multitasking environments. The panel’s IPS Black technology enhances contrast compared with traditional IPS, improving depth in darker
content while maintaining wide viewing angles. The display is TÜV Rheinland certified for eye comfort and includes an ambient light sensor to adjust brightness based on workspace conditions.
Connectivity is anchored by Thunderbolt 4, supporting up to 140 W power delivery, enabling laptops and workstations to be powered and docked through a single cable. The monitor also includes multiple USB-C and USB-A ports, HDMI, DisplayPort, and an Ethernet connection, allowing it to act as a central hub for peripherals and network access.
Additional utility features include integrated KVM support for controlling multiple connected devices from one keyboard and mouse, and flexible ergonomics with height, tilt, and swivel adjustments. The UltraSharp 52 is positioned for users managing complex workflows across large datasets, creative applications, and multitask environments.


From threat hunting to incident response, delivering full-spectrum, fully managed cybersecurity protection.

Email Security & Archival
API & Web Application Firewalling

Active AI Cyber Platform
Patch management
Next Gen Gateway Firewalling
Cloud Security Posture Management
Threat hunting and breach detection
Next Gen Endpoint protection
Digital Forensics
Intrusion Detection & Prevention
Multifactor Authentication
Zero Trust Network Access
Secure Access Service Edge
Mobile Device & Application Management

Privileged user management
Immutable Data Protection
Data Leak & Exploration Protection
Data Encryption solutions@teksalah
External Attack Surface Management
Network Admission Control Services
Vulnerability Management & Remediation