
















Founded in 1969 by two former Police Officers, CIS initially operated as a security management and commercial investigation specialist, advising clients on matters relating to security practice and providing loss prevention.
In 1972, the company joined the Security Personnel industry after identifying a gap in the market focusing on providing professional, qualified, and trained personnel able to fulfil our customer requirements.
CIS Security Personnel Division was then formed and has organically grown to be an award-winning security company, with over 3,500 employees and a portfolio of over 500 clients.
Over the years we have continually added to our services offered and now provide in-house consultancy and managed security services to our customers, drawing on the vast knowledge of our people, based on 50+ years of industry experience.
In 2019, CIS Innovative Solutions was formed, to meet the needs of all our customer’s physical, technological, and strategic security requirements.
Our success reflects our core values: passion, determination and leadership and underpins all our business operations. Our mission is to be recognised as a leader in security excellence in all aspects of our business operations and we will achieve this through the introduction of best working practices, training, and development of our employees, and by the application of innovation and the best in new technologies, at all times striving to exceed our customers’ expectations while adding genuine value to their business.

Innovative Solutions is one of three divisions of CIS Security.







CIS Innovative Solutions is one of three divisions of CIS Security.
Innovative Solutions is a Security Systems integrator, that works on behalf of our customers and stakeholders to ensure the security systems used within their portfolios are enhancing the security provision provided by CIS.
• 24/7 Security Operations Centre
• Remote Monitoring of CCTV and Alarms
• Security Systems Design
• Security System Survey and Risk Assessments





• Security Systems Installation
• Security Systems Maintenance
• Project Management
• Car Parking systems and Management
• Security Equipment Procurement









CIS Innovative Solutions is a security systems integrator that provides an end -to -end service, capable of supporting your operations in every phase of the security system lifecycle.
Security risk or needs assessments
System engineering and design
Broad access to the leading product lines
Custom engineering when required
Alternate investment options
Procurement
Installation, commissioning and training
Full lifecycle service and maintenance
System functional and technology upgrades

A security systems integrator specialises in bringing together installers and subsystems into a whole and ensuring that those subsystems function together.



This document is a catalogue of recommend products used by CIS innovative Solutions. All products and services within this document are not exhaustive, tailored solutions and custom engineering are available to mitigate risk, we make recommendations through in-depth site surveys.









Whether you’re operating a small business or a global enterprise, LenelS2’s security access control systems support your evolving needs in the ever-changing security landscape.
A feature-rich access control system is only the beginning. By unifying your LenelS2 access control system with video management, intrusion alarms, building systems, business systems and more, you can synthesize data in a single user interface to enhance security, safety, building health and operational efficiency.
Your business, IT and system operator requirements should inform your security system setup. With a range of deployment options that include browser-based applications, easy-toinstall network appliances and the cloud, we can help you meet your needs.
With over 200 certified product interfaces and an open API, you can truly optimize your LenelS2 access control system to meet your security and operational needs for a variety of third-party products from human resource databases to elevator control.


Aging access control systems can be limited in functionality, exposed to vulnerabilities and costly to maintain. Our modern access control systems provide modern features, ongoing cybersecurity enhancements and automated software updates. An upgrade can utilize existing infrastructure, reducing costs and minimizing downtime.
Cloud technology offers the advantages of large-scale computing resources in an on-demand model, simplifying product and service delivery as well as minimizing costs. LenelS2 cloud-based solutions allow you to remotely manage your installed products or deploy an access control system.



Comprehensive physical access control systems for organizations of all sizes.
The OnGuard physical access control system exemplifies our commitment to providing a superior, integrated, and customizable security management system that meets your evolving needs. The OnGuard system delivers solutions that seamlessly unify access control and video monitoring for a wide range of industries.



Providing the means to aggregate, visualize and share security data from multiple sources, the OnGuard system helps companies recognize context and analyze inputs from a number of simultaneous events. Seamlessly synthesizing information from access control, video and other sensors, the OnGuard system delivers complete line-of-sight to all aspects of security and facilitates intelligent responses and outcomes.
The OnGuard system integrates seamlessly with a wide range of existing business systems. The OnGuard system can bi-directionally exchange cardholder data with many HR platforms, ERP systems and/or elevator systems, coordinate alarm/ event data with emergency response systems, and provide/receive event information with various building management, network management and third-party security systems.
Adaptable and scalable, the OnGuard physical access control system is appropriate for small localized environments as well as large global enterprise applications that span a wide geography. For businesses starting small and anticipating growth, the OnGuard system is ideally suited to meeting their expanding needs. Our physical access control system delivers unlimited scalability, flexibility, and industry-leading performance.
Leveraging OnGuard clients and apps in your OnGuard system turns an excellent security management solution into an exceptional one. These OnGuard utilities improve your overall user experience and provide a path to view, manage and authorize in an increasingly mobile and remote workplace.


CIS Innovatiove Solutions partners with Johnson Controls and subsiderary Envison Intelligent Solutions. Johnson Controls owns the access contorl product C-Cure 9000 and Envision provide vacant premises mitigation and ARC services.
C•CURE 9000 is one of the industry’s most powerful security management system providing 24x7 mission critical security and safety protection for people, buildings and assets. It provides a standard approach to physical access authorization throughout all your buildings, regardless of age, layout or location that you can access on your workstation, laptop or mobile device. The native interfaces combined with the Connected Partner Program helps us to deliver seamless integrations with over 300+ third-party security and business technologies.


� OSDP support for reader to panel communications on iSTAR Ultra Series controllers
� Supports up to 5,000 readers per single server and 60 satellite application server scalabilities for Enterprise systems
� Enterprise system remains operational throughout upgrade process with multi-version software support
� Access to C•CURE 9000 from any internet browser with C•CURE Web
� Administer and monitor C•CURE 9000 from your mobile device with C•CURE Go
� Software House Connected Partner Program for standards-based integrations
� Part of the Cyber Protection Program to reduce the risk of vulnerabilities
� Support for iSTAR Ultra G2 and iSTAR Ultra G2 SE door controllers with advanced embedded cybersecurity
� C•CURE Web-based Client – Dynamic Access and Video Monitoring Views and Layouts, Swipe & Show, Health Dashboard, etc. (Phase III)
� C•CURE ID HID SEOS and MIFARE DESFire EV1/EV2 support, for card encoding of multiple applications simultaneously (up to 5)
� C•CURE Portal moved to the latest Angular web framework, meeting latest in cyber security
� Email template customization for C•CURE Visitor Management and Access Management Workflow
� As an option, C•CURE 9000 version 3.0 and later supports SQL database hosted by Amazon Relational Database Services (RDS)™ powered by Amazon Web Services (AWS)™





� Unification with American Dynamics’ victor Professional provides a multidimensional single-point event management
� Single server for managing security and events for video, access control, intrusion, central station, fire, real-time location, and other supported systems
� Reduced footprint to decrease required rack space, power, cooling, and overall cost and maintenance
� Single server database for advanced cross-pollination of events across multiple supported systems
� Run C•CURE 9000 and victor Professional efficiently as native 64-bit applications
� Single unified security client provides an all-inclusive real-time alert notification GUI with advanced event management and superior interactive mapping for situational awareness
� Minimizes learning curve by consolidating requirement of multiple singledimensional client applications
� Event linking and cross-product association for event activations across dispersed security systems with associated time-synchronized video
� Integrated policy management with advanced auditing capabilities
Gallagher’s industry leading security solutions are designed to meet the unique access control needs of sites varying in size and scale from one door to thousands. Whether it’s a small business, large enterprise organization, or sites with critically sensitive infrastructure, we have a solution that will keep your people and assets safe.
Gallagher Command Centre is a powerful operator-friendly security management system that enables you to:
� Manage cardholders, including their access, credential and photo identification
� Monitor alarms and control all system aspects
� Retrieve and report on stored system information
� Interface to and exchange information with third party systems
� Configure the site and all system component







Gallagher controller devices can greatly expand the control capabilities of a security system:
� Remove the risk of one compromized connection taking down all downstream devices
� Monitor and report the state of balanced inputs
� Enforce decisions to switch output relays
� Manage multiple access points efficiently
Gallagher’s reader range provides contactless proximity card readers for access control management delivering:
� Rapid and secure access decision responses
� Support for multiple card technologies and mobile credentials
� A diverse selection of reader mounting and protection accessories
The Brivo enterprise solution protects 70,000 business locations around the world – discover how we can protect yours









Brivo Provides a Comprehensive Enterprise and Corporate Physical Security Solution.
Design and implement an effective security plan. Use Brivo’s scalable enterprise cloud-based solution to satisfy the most stringent compliance and IT requirements.


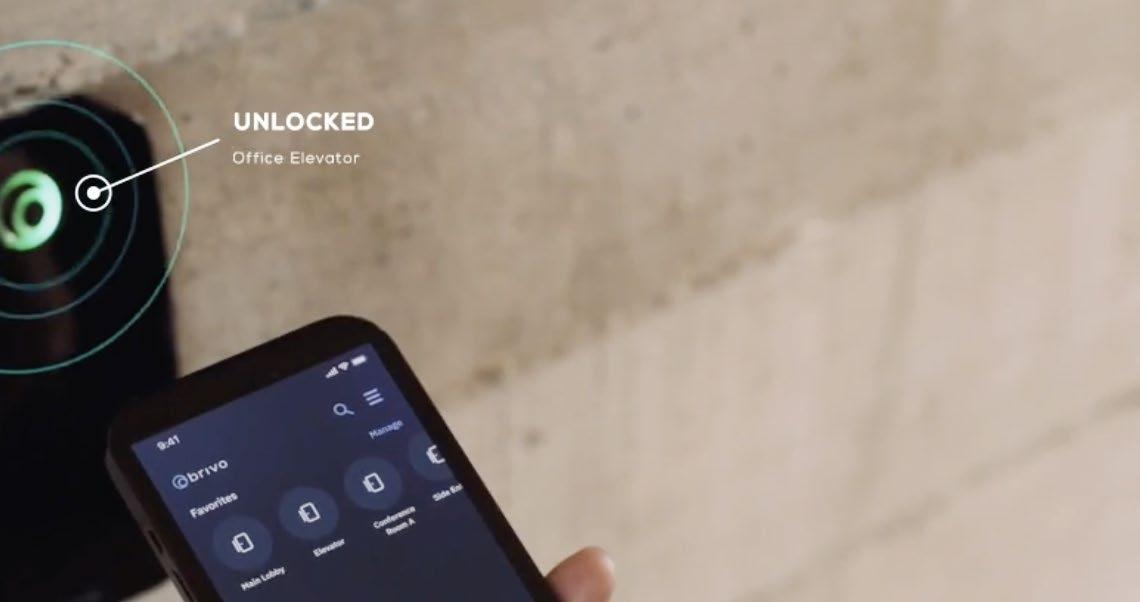
Brivo mobile-centric platform supports security leaders who directly manage security systems while improving the experience for all users.
To keep you secure, Brivo offers an integrated security platform which includes access control, mobile credentials, mobile administration, video surveillance, identity and visitor management and elevator control. Brivo also offers an open API to build custom integrations that bring your entire physical security ecosystem together.




Security made simple.


Net2 is our networked access control system. It can be administered using one or more PCs and can be monitored and managed from a central location. It is a complete solution that encompasses wireless door handles and door entry.


� Convenient end to end security that eliminates the need for keys.
� Start simple, expand as and when you need to.
� A powerful all in one solution that works with a range of systems.
� License free.
� Free upgrades.
� Integrates with a vast range of leading security brands.
� Easy to quote, easy to install, easy to deal with.








Modern CCTV systems generally fall into two categories:
1. On-Premise Systems – Video footage is stored locally using DVR/NVR hardware at the physical site.
2. Cloud-Based Systems – Video footage is stored in remote data centres accessed via secure cloud platforms.
A Hybrid Cloud System incorporates both methods: footage is recorded locally for immediate access and resilience, while selected or full footage is simultaneously backed up to the cloud.
Evaluation Criteria
The recommendation is based on the following assessment factors:
� Data security & GDPR compliance
� Reliability and system resilience
� Remote accessibility
� Scalability across future sites or additional cameras
� Installation and maintenance requirements
� Total cost of ownership (TCO)
� Risk mitigation (hardware failure, theft, downtime)

Analysis of System Types
1. On-Premise CCTV Strengths:
� High control over data and infrastructure
� Operates independently of internet connectivity
� Predictable long-term costs after initial investment


Limitations:
� Vulnerable to local hardware failure, physical damage, or theft
� Complex remote access setup
� Requires IT/security staff for maintenance
Limited scalability without major hardware upgrades
2. Cloud-Based CCTV Strengths:
� Easy, secure remote access from any device
� Automatic updates, patches, and cybersecurity
� Highly scalable
� No local servers/NVRs required
Limitations:
� Fully dependent on internet upload bandwidth
� Higher long-term operational costs (subscriptions)
� Potential vendor lock-in
� Data residency and compliance must be verified


3. Hybrid Cloud CCTV
Strengths:
� Local recording provides high reliability and continuous capture even during connectivity issues
� Cloud backup ensures footage is protected off-site
� Fast local retrieval + secure remote access
� Scalable without large hardware investments
� Supports compliance through encrypted storage and multi-site redundancy
� Reduces single points of failure associated with both pure cloud and pure on-premise systems
Limitations:
� Higher initial cost compared to cloud-only systems
� Requires configuration of both local and cloud components
Hybrid Cloud CCTV System is the optimal choice.
Rationale
� Resilience: Local NVR ensures uninterrupted recording; cloud backup protects against theft, fire, and hardware failure.
� Compliance: Cloud providers often offer certified UK/EU data centres with strong encryption, supporting GDPR obligations.
� Remote Monitoring: Management teams can view live and recorded footage securely from mobile and desktop platforms.
� Futureproofing: Additional cameras or locations can be added easily without major infrastructure upgrades.
� Cost-Balanced: Avoids the high long-term cloud costs of a full cloud deployment while reducing maintenance burden of a fully on-premise system.

Genetec VMS (via its Security Center / Omnicast) is a mature, enterprisegrade video management platform. It combines flexibility, scalability, strong cybersecurity, deep analytics, and unified security operations. It’s particularly well-suited to organisations with complex security needs, multi-site operations, and a desire to integrate video with other physical security systems.
� Genetec offers a powerful VMS as part of its Security Center platform.
One powerful interface. Total situational awareness.
Customizable dashboards and a dynamic, map-based view bring all your data together—video feeds, people counters, and more—in a single interface. Monitor activity, track key metrics, and respond to incidents without switching screens, so you always have the full

� Their VMS component is called Omnicast.


See and understand your environment like never before
Omnicast is an intuitive video surveillance platform. It provides access to critical information while keeping it simple for the operator.

Bring your video surveillance to life with dynamic maps and custom dashboards. Your team will know not only what, but where things are happening at all times.
See it all in one place
Unify video with other core security systems such as access control, automatic license plate recognition (ALPR), intrusion monitoring, and communications.
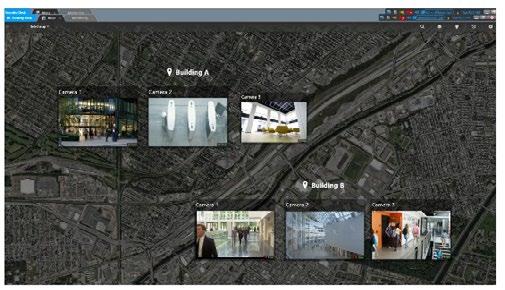
Monitor all your sites from a single location with Security Centre Federation. Enhance cooperation between teams and lower your security costs.

� It supports on-premises deployments, cloud, and hybrid models.
� The VMS is part of a unified security system — integrates with access control, ALPR (automatic license plate recognition), intrusion, communications, etc.
Key Features of Genetec VMS / Security Center
1. Scalability & Architecture
� Built to scale: from small sites to very large, multi-site deployments.
� Open architecture: supports a wide variety of cameras and hardware.
� Federation: central control of multiple sites.
2. Cybersecurity
� Strong security: Genetec puts emphasis on encryption, authentication, and data protection.
� UL certification: Omnicast has UL 2900-2-3 Level 3 cybersecurity certification.



Enterprise-grade video management designed to evolve with you
Find what you’re looking for faster with advanced search capabilities powered by intelligent automation (IA). Use natural language search to quickly identify a person or object of interest. Then, find that individual across multiple locations, pinpoint when an object entered or exited a scene, and review nearby activity. Click, click, case closed.

Experience a modern investigation process, from collection to distribution. Bookmark, snapshot, and export video with ease. Add in relevant data from your unified access control system. Then, maintain the chain of custody with digital evidence management.


� Forensic search: ability to search large volumes of video using metadata, filters, NLP (natural language), even voice.
� Smart analytics: motion detection, object/person tracking, edge analytics.
� Intelligent automation: can trigger alerts, automate responses based on rules.
4. Reliability
� High availability: built-in redundancy, failover to reduce downtime.
� Flexible storage: supports local and cloud storage, hybrid deployment.

5. Unified Interface & Situational Awareness
� Single dashboard: map-based views, customizable dashboards, unified client.
� Integration with other security systems gives a single pane of glass for operations.

� Secure chain of custody for video evidence.
� Ability to bookmark, snapshot, export footage securely.
7. Deployment Options
� On-Premises: Traditional setup with local servers.
� Cloud / SaaS: Through Security Center SaaS you can run the VMS in the cloud or as a hybrid.

Genetec video surveillance as a service (VSaaS) delivers non-stop connectivity and an intuitive monitoring and investigation experience across all your sites. With unmatched flexibility, you can record video locally or in the cloud and choose the cameras that work best for you. Use direct-to-cloud cameras or connect through managed appliances. It’s flexible, enterprise-grade VSaaS backed by over 25 years of video innovation.
� Edge: Genetec supports edge analytics and can minimize bandwidth by processing data locally.


� Web and mobile apps let users monitor video, manage alarms, and investigate incidents remotely.
� Built-in privacy tools: video anonymization, encryption, fine-grained user permissions.
� Helps with regulatory compliance.





Reliable
Avoid downtime or data loss with proven technology based on Milestone’s 25 years of market experience.
Accept no limitations on your video capabilities with an open platform that can be adapted as your needs develop.
Gain full control over all your software and hardware with a complete and intuitive overview that allows easy collaboration.
Build the solution you need
There is no one-size-fits-all when it comes to video technology. Every operation is different, with needs constantly evolving. That’s why XProtect’s flexible open platform architecture makes it such a future-proof investment. You can adapt and scale your video solutions as well as update them with the latest analytics and AI technologies.
13,000+ supported cameras and other devices Extensions include Smart Wall and Smart Map 1,000+ compatible third-party integrations.



Thanks to a single interface, multi-layer maps and advanced search, the task of protecting people and property and improving operations is made simple and centralized. XProtect helps staff to ensure everything is monitored, and that proactive or reactive measures can be quickly set in motion.

Whether you focus on security, operational efficiency, or customer experiences — XProtect keeps you informed in real time of events that may need your attention. It’s conveniently accessible from desktop computer and mobile device clients.
Program the Alarm Manager with specific alarm triggers Get desktop and Smart Map alarm notifications Instantly access any connected camera or sensor.



Analyse and manage evidence
When an incident takes place, XProtect lets you condense and filter hours of footage to quickly resolve it. The tracking and monitoring functions not only assist investigations, but they also allow you to keep a virtual eye on objects and people.
� The Incident Manager streamlines incident reporting
� Evidence Lock ensures video can’t be prematurely deleted
� The Export Function ensures compliant third-party sharing

and manage evidence
When an incident takes place, XProtect lets you condense and filter hours of footage to quickly resolve it. The tracking and monitoring functions not only assist investigations, but they also allow you to keep a virtual eye on objects and people.
� The Incident Manager streamlines incident reporting
� Evidence Lock ensures video can’t be prematurely deleted
� The Export Function ensures compliant third-party sharing





Video technology can help take the pressure off staff and budgets. XProtect’s single interface, multi-layer maps and advanced search simplify and centralize operations. Third-party integrations such as access control and people counting analytics further optimize resources.
� The intuitive interface can be adjusted to individual, or team needs
� Centralized Search accelerates finding and sharing footage
� Proactive analytics enable preventative measures.
No organization wants to deal with the disruption, costs, and distress of cybersecurity breaches. That’s why XProtect is designed and independently tested to meet the highest security standards. And it’s supported by a security response team.
� Manage user access with tiered admin and user rights
� Features high-level encryption and password protection
� Receive patches, hotfixes, and security alerts.

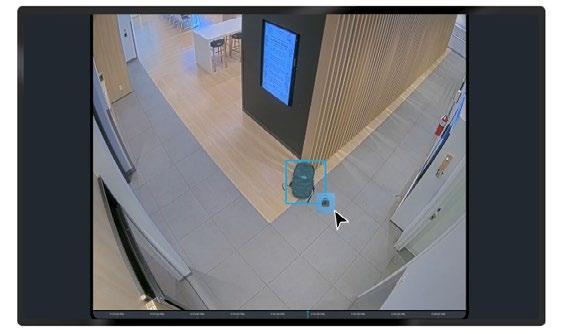
Improve visibility and increase efficiency across your entire organization with the Avigilon Alta cloud security suite, equipped with AI-powered analytics and fully integrated technology.
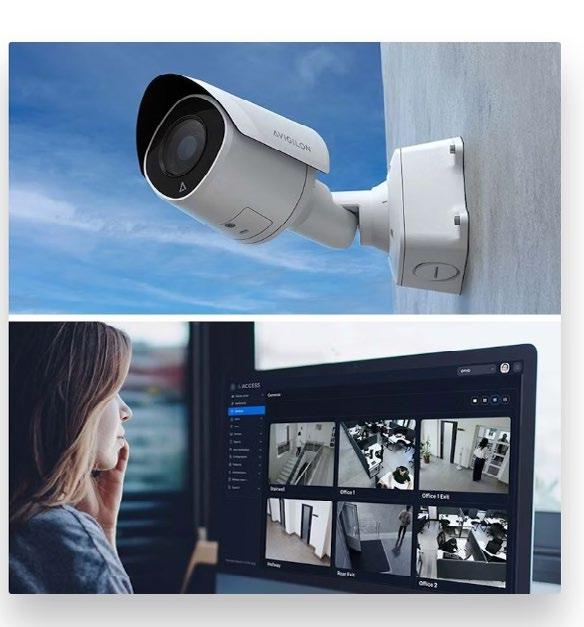





Secure, scalable, and easy to use, Avigilon’s video management systems provide an enterprise-grade, AI-enabled solution, equipped with integrated machine learning capabilities.



When every minute counts, video management software with advanced search technology speeds your investigations without sacrificing any level of detail.



Avigilon video management systems are equipped with advanced video analytics technology and features that bring all the details into focus.



Avigilon gives you the flexibility to deploy an advanced video management system that fits your unique security needs.



Intelligence within reach. Our cloud-based AI video analytics software has the power to provide 360-degree awareness to your Avigilon Ava cloud IP cameras or to your existing cameras and sensors.
Add maps of all your locations in Avigilon Alta Aware to gain enhanced situational awareness. Classify and assign people, vehicles and other objects as they move on your premises.
Powered by deep learning, Alta Aware automatically changes video streams with real-time alerts and notifications to describe the incident, the time and the place it occurred.
Search by event and similarity, and perform appearance and image detection powered by machine learning capabilities to quickly comb through countless hours of video throughout your entire deployment.
On-premise VMS that highlights the most important security information at your fingertips, so that you are always kept instantly in the know for the moments that matter.
Accelerate response times by quickly identifying people of interest with AI that delivers actionable results through advanced pattern-based analytics, teach-byexample technology and facial recognition.
Make watching live video obsolete with an intuitive view of your site. The AIenabled interface provides color-coded alerts, indicating importance level, for events requiring attention.
Expedite investigations and improve incident response time by initiating a search across multiple sites of a vehicle or person based on physical descriptions or by uploaded photo or video.





Accelerate response times by quickly identifying people of interest with AI that delivers actionable results through advanced pattern-based analytics, teach-byexample technology and facial recognition.
Make watching live video obsolete with an intuitive view of your site. The AIenabled interface provides color-coded alerts, indicating importance level, for events requiring attention.
Expedite investigations and improve incident response time by initiating a search across multiple sites of a vehicle or person based on physical descriptions or by uploaded photo or video.
AVIGILON

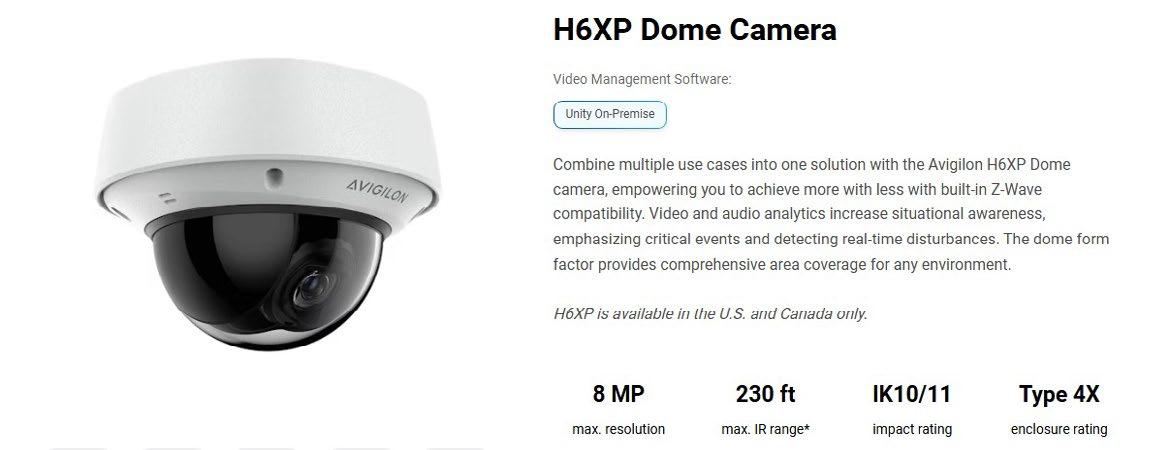




Secure your sites with superior 180, 270 or 360-degree views, so you’re covered from all angles. Combining NextGeneration Video Analytics with three or four adjustable sensors provides you with one powerful solution. The Avigilon H5A multi-sensor camera can monitor virtually any area in all lighting conditions to protect building corners, parking lots, intersections and more.



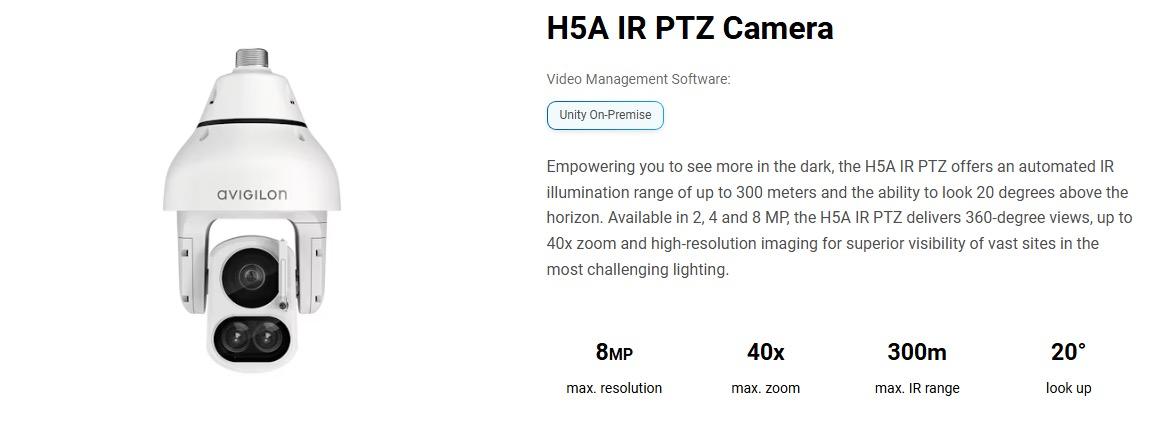



PTZ cameras - Pan, tilt, and zoom capabilities for wide-area coverage

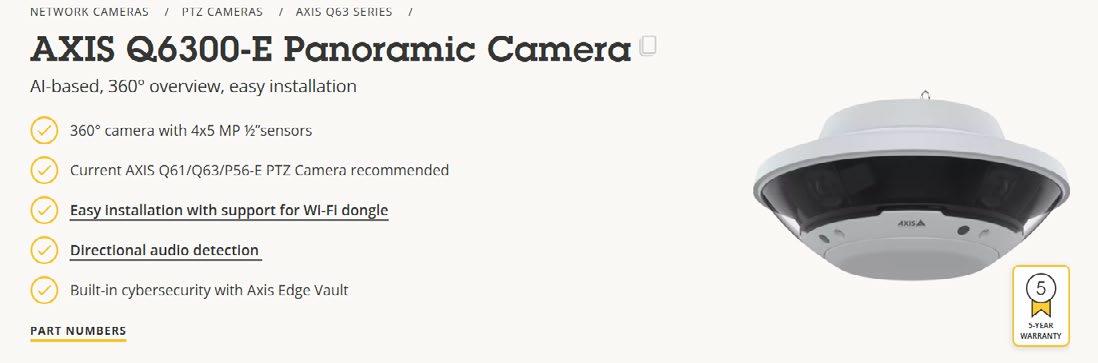
PTZ cameras from Axis use pan, tilt and zoom to provide both wide-area coverage and great detail with a single camera. Great image quality and the ability to zoom in make it possible to verify detected security events.
The cameras are equipped with a variety of intelligent features and can move between pre-set positions and zoom in automatically in response to detected events. They can also be easily integrated into a system with other cameras.






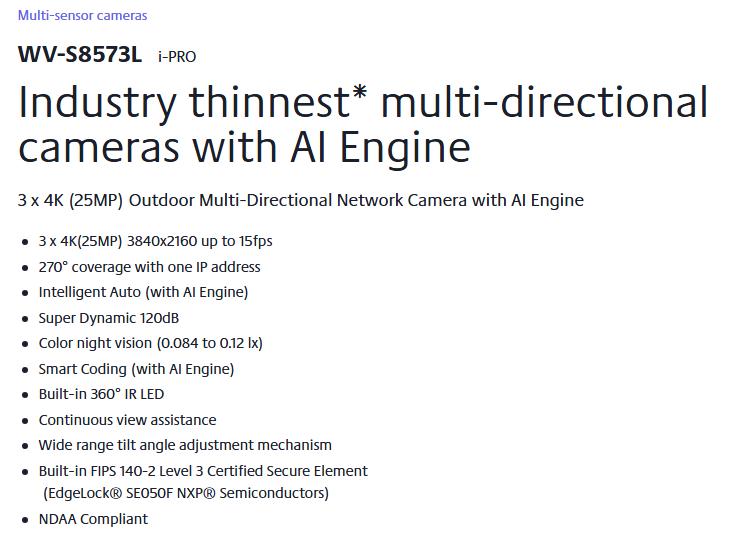
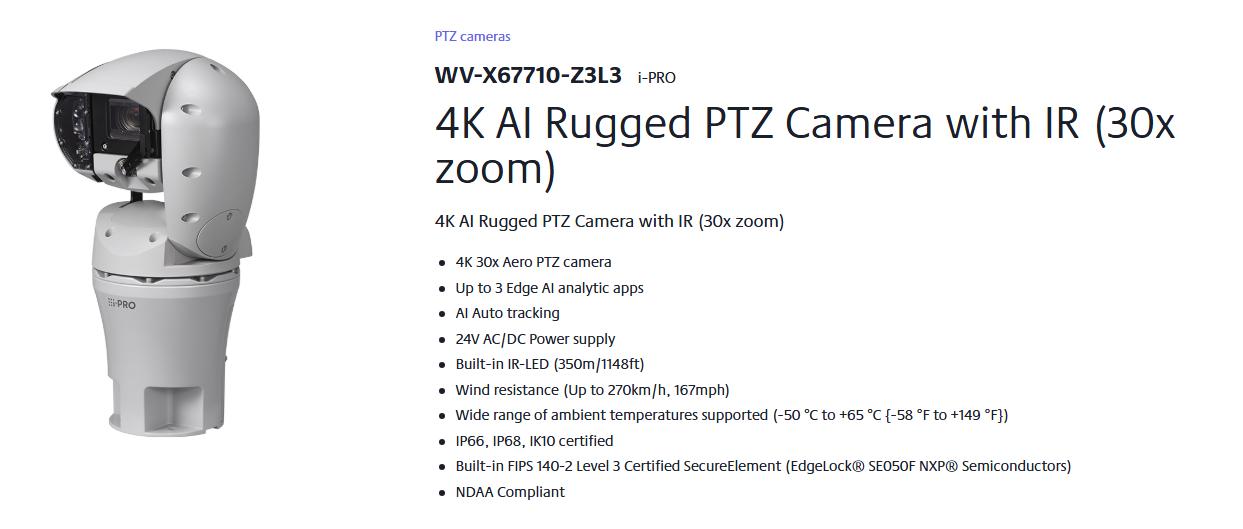
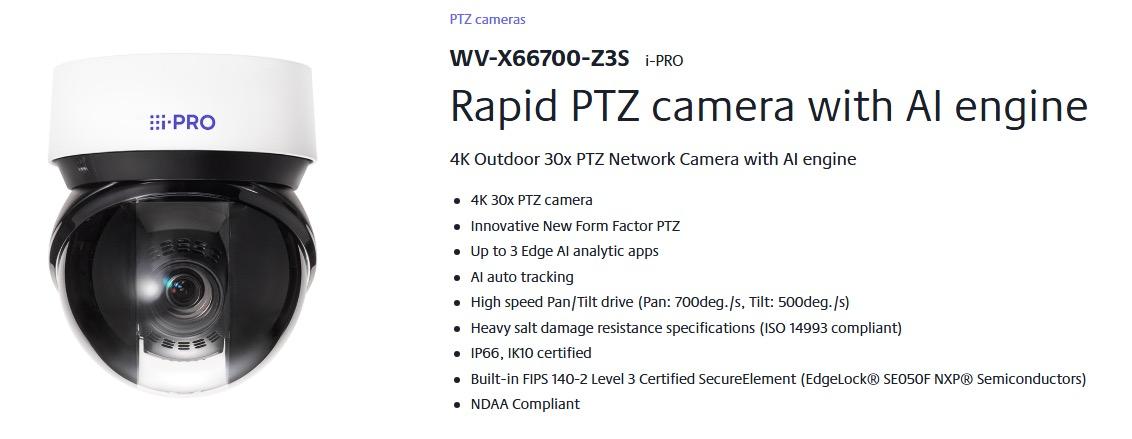
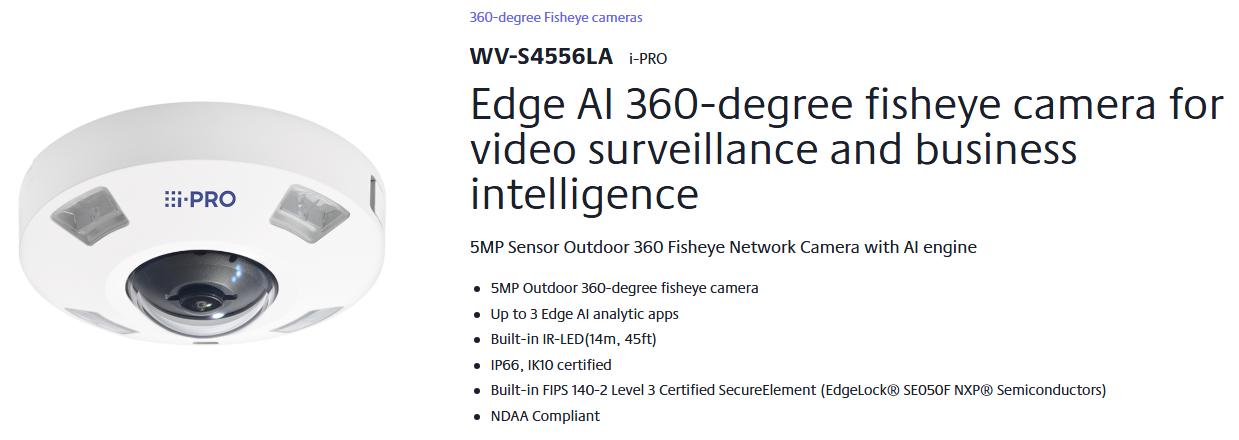
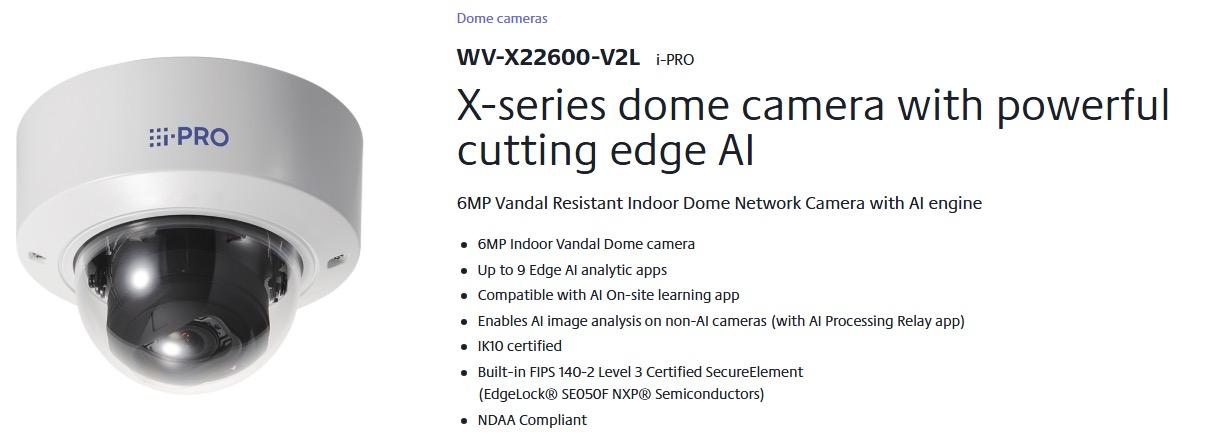
High-Definition Imaging from Multiple Angles i-PRO multi-sensor cameras capture the highest quality images even in very challenging dynamic environments. These cameras can excel at capturing clear images, even in low light conditions from multiple angles through the use of their four repositionable lenses.
























CIS Innovative Solutions recommed the following three BWC systems AXIS.
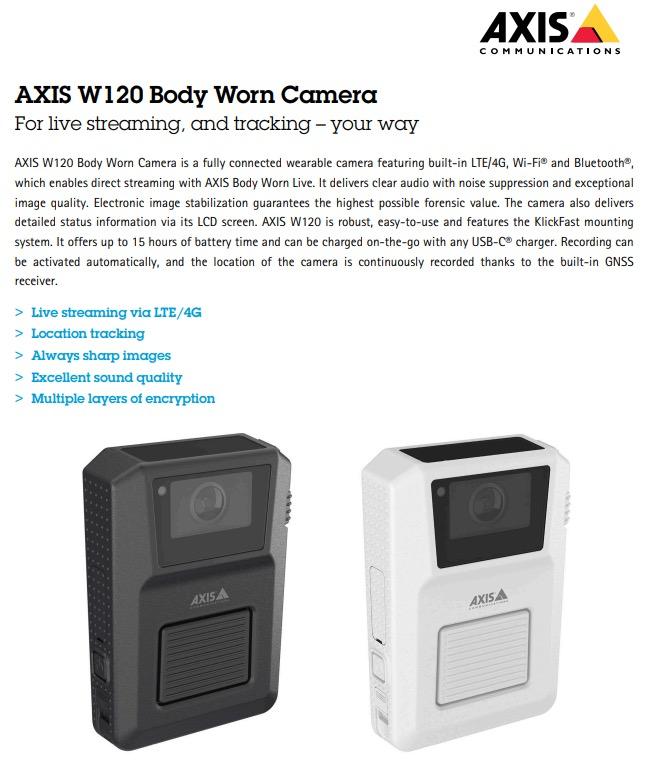
AXIS W120 Body Worn Camera makes wearers feel they’re not alone. Thanks to on-demand streaming, and location tracking, someone always knows what’s happening – and where. Plus, AXIS W120 plugs into the system of your choice, and you can manage video your way.

AXIS W120 Body Worn Camera offers live streaming via inbuilt LTE/4G, so you can always connect using AXIS Body Worn Live. At the click of a button, you can stream sharperthan-ever images and clear audio with advanced noise and wind suppression. It provides location tracking and it’s robust and waterproof. AXIS W120 buffers up to 120 seconds, so you’ll catch the whole encounter. It has stealth mode for surreptitious recording. And a battery life of up to 15 hours, charging on-the-go with any USB-C charger, and fast offloading make it ready to go when you are, and a snap to put away.












AXIS TW1200 Body Worn Mini Bullet Sensor is small and light and can be easily attached to, for example, helmets or caps. It supports the Picatinny mounting system and is compatible with many types of gear.
AXIS TW1200 offers the same optical performance as Axis body worn cameras with sharp images even in challenging conditions, which makes it a discreet alternative to filming with the full-sized camera.



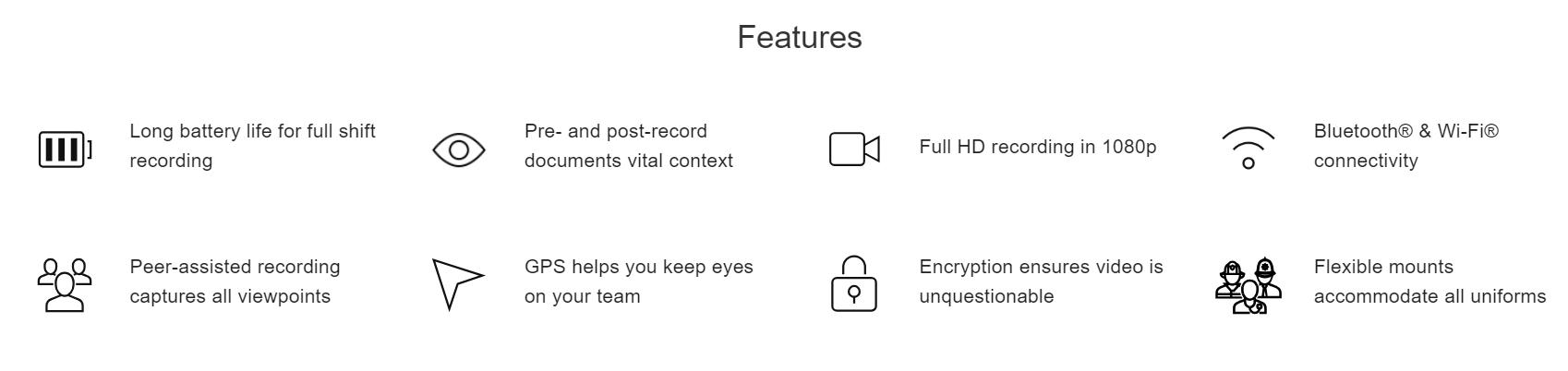
Meet your best witness. The V500 body camera is a radical evolution of our industry-leading body camera platform, enabling you to leverage real-time intelligence for a more collaborative, effective response.










Intended to support your workers when dealing with aggression or confrontations on a daily basis, the VB400 enables you to foster trust between your team and the public by providing an unbiased independent witness. See what your team sees and watch key decisions unfold, either in real time or after the fact.
The VB400 seamlessly fits around your existing workflows. All configuration and maintenance can be done ahead of time with our easy-to-use backend software, VideoManager – so your workers can grab their cameras and get to work with minimal training and disruption. In the field, features including dual microphones, a wide-angle lens and intuitive buttons ensure that every interaction can be captured in high-definition from start to finish.


All footage is stored and encrypted on the VB400 until it is redocked, at which point it is offloaded securely and automatically. But your cameras are just one part of your operation. Combine other pieces of technology – such as fixed video and Bluetooth sensors – with the VB400’s superior connectivity for a more complete and effective response.


WHETHER YOU’RE USING A SINGLE CAMERA OR STREAMING LIVE BODY-WORN AND FIXED VIDEO INTO THE SAME VMS, THE VB400’S CONNECTIVITY ENABLES YOU TO UNDERSTAND THE FULL CONTEXT OF A SITUATION. SEE THE BIGGER PICTURE





EVERY ASPECT OF THE VB400, FROM ITS RESILIENT OUTER CASING TO THE WAY IT FITS ON YOUR UNIFORM, IS BUILT TO LAST – NO MATTER HOW OR WHERE YOUR TEAM WORKS.
Your body-worn cameras should fit around your organization’s routine operations – which means accommodating a variety of shift patterns, environments, and uniforms. That’s why the VB400 is as tough as your team is: compatible with whatever clothing they’re wearing, it can record for however long they’re on duty and withstand whatever conditions they encounter.
TEMPERATURE & WEATHER RESISTANT
The environment shouldn’t stop you from getting the video you need. Operate in temperatures between -20°C and +50°C, with IP67 rating for protection against wind, rain and snow.
SHIFT-LONG BATTERY LIFE
Record for up to 12 hours continuously on a single charge. Configurable standby and safety modes preserve battery life.
RUGGEDISED EXTERIOR
Protect your evidence in a resilient outer casing. Certified to MIL-STD-810G drop test requirements, the VB400 is built to withstand the rigours of the job – whatever that entails.
SECURE MOUNTING OPTIONS
Be confident in the knowledge that your VB400 will stay firmly attached to your uniform, regardless of whether you’re wearing a shirt, jacket or protective clothing.


Body-worn cameras provide an invaluable first-person perspective. And now, these insights aren’t just after the fact; equipped with multiple ways to connect, the VB400 gives you crucial insights when you need them most. Use Peer-Assisted Recording to ensure every angle is being documented, stream over Wi-Fi to the Video Management System (VMS) that handles your fixed CCTV cameras and use built-in GPS to keep

WHETHER YOU’RE USING A SINGLE CAMERA OR STREAMING LIVE BODY-WORN AND FIXED VIDEO INTO THE SAME VMS, THE VB400’S CONNECTIVITY ENABLES YOU TO UNDERSTAND THE FULL CONTEXT OF A SITUATION.
Body-worn cameras provide an invaluable first-person perspective. And now, these insights aren’t just after the fact; equipped with multiple ways to connect, the VB400 gives you crucial insights when you need them most. Use Peer-Assisted Recording to ensure every angle is being documented, stream over Wi-Fi to the Video Management System (VMS) that handles your fixed CCTV cameras, and use built-in GPS to keep track of your team’s locations.
THIRD PARTY VMS INTEGRATION
Maximise your existing investments by centralizing both body-worn and fixed camera live streams in any ONVIF-compatible platform.
PEER-ASSISTED RECORDING
Minimise workload for responding workers; your VB400s can be triggered to start recording immediately, when another one does so in a configurable radius.
GPS LOCATION TRACKING
Keep your workers safe using the Tactical VideoManager interactive map – or leverage VideoManager’s powerful API to interface with your own software.
RADIO INTEGRATION
Reduce your teams’ workload; trigger VB400s to start recording when Motorola Solutions radios enter an emergency state.










The Axon Body 4 camera is designed for law enforcement and security personnel, offering features such as:
� Enhanced Camera Options: Includes a 5 MP sensor and a 160-degree field of view for better visibility.
� Battery Life: A 4300 mAh battery allows for a full shift without needing to recharge.
� Bi-directional Communication: Allows users to communicate with support teams in real-time.
� User Manual: For detailed operation and features, refer to the Axon Body 4 Camera User Guide.

support.
Receive alerts and locate users on live maps, upload video remotely and communicate bi-directionally with support teams when used with Respond+.


Increased visibility with 4:3 aspect ratio and 160-degree field of view.
Don’t let a dead battery leave you exposed. With a larger 4300 mAh battery, Axon Body 4 lasts a full shift.
Enhance collaboration with our two-way communication feature, enabling field personnel to share body camera livestreams with support teams.
Secure clearer and more detailed images for improved evidence collection with an upgraded 5MP camera sensor.
Easily manage cameras and track recording status with simplified registration, programmable buttons, mute reminders, and confirmation prompts.
Axon Respond offers real-time support with live maps, instant alerts, and live streams. Upload critical recordings on-the-go.
Get back to work quickly with the new magnetic disconnect fast charge cable, which delivers 20% charge to your device in 30 minutes.


Capture secure footage with XTS-AES 256 encryption and store more with 128GB solid state hard drive.
Expand Axon Body 4 camera’s perspective with the Flex POV accessory, which is IP67 waterproof, durable, and wearable without needing charging. Please note: the body-worn camera itself is IP68 waterproof.
This is a feature (“skill”) built into Axon Assistant, which runs on the Axon Body 4 body-worn camera. Officers can use a push-to-talk mechanism to translate spoken language live. It supports 50+ languages at launch. The translation is bidirectional: when the officer speaks, their words are translated into the other person’s language, and vice versa. It can auto-detect the other person’s language, or the officer can manually set the target language. All interactions via the translation feature are recorded (audio + video) on the bodycam, so there’s a transcript and evidence for later review.





This is Axon’s AI-powered transcription service. It converts audio from bodyworn cameras (and other audio sources) into text. Transcripts are time-synced with the video/audio. So you can play back the recording and follow along in the text. Accuracy depends on recording quality (mic, environment). Axon notes that microphone quality and how/where the audio was recorded are big factors. The AI-generated transcript is marked as unverified until a human reviews and edits it. The original audio is preserved, so if there’s a mishearing, you can always go back to correct the text. All transcripts are stored securely in Axon Evidence. Auto-Transcribe also supports Auto-Translate for non-English audio (e.g. Spanish → English), though this provides a base understanding rather than courtroom-certified translation. It’s used to power other Axon tools: Draft One (for report generation), priority video audit, audio redaction, etc.






Galaxy Dimension - Integrated intrusion and door
panel range
The Galaxy® Dimension series of security systems is a fully integrated intrusion and door control security solution for mid to large commercial security installations. It offers your customers a user-friendly system in a cost-effective and fully compliant Security Grade 3 package.
With innovative wireless capability and user-friendly remote management options, the series provides high quality, reliable security solutions, with the flexibility to meet the needs of every commercial and industrial application.



To ensure fail-safe communications, multiple path communication options for alarm signalling include GPRS, Ethernet and standard telephone line (PSTN). These options also allow maximum flexibility and customisation to capitalise on existing network infrastructures and minimise disruption for customers.
A choice of LCD Keypad and Keyprox options including the MK8, with a modern design and all the familiarity and functionality of the MK7, for ease of programming across the range. In addition, all user interfaces feature a proximity function allowing quick and secure set and unset without PIN code. The GX Remote control mobile App allows control of the system from anywhere in the world from your preferred smart device (requires E080-04 Ethernet module).
With Galaxy® Dimension, an Alarm Receiving Centre (ARC) can listen in using independant audio channels to identify the specific location where the alarm has been triggered and verify source and cause. This reduces false alarms and increases system reliability.
The Remote Servicing Suite (RSS) is a maintenance tool enabling complete remote control of the panel, allowing installers to give customers instant support. Installers can complete remote routine inspection reducing the need for time consuming and costly site visits. The RSS software uses a common database to communicate with all Galaxy® panels from one programme. A networked version of the Remote Servicing Suite offers access to up-to-date records for all users. This guarantees the secure management of information in one central location. Both wired and wireless components can take advantage of the easy remote diagnostics and maintenance functionality in this software.


Galaxy Dimension offers customers a user-friendly, integrated security solution that is flexible and upgradeable to meet specific security needs. Honeywell provides sales and marketing support and organises frequent training to boost system understanding and to ensure trouble-free installations every time.


Texecom is trusted by professional installers to protect the world’s most important properties and the people who use them.
More speed. More flexibility. More choice.
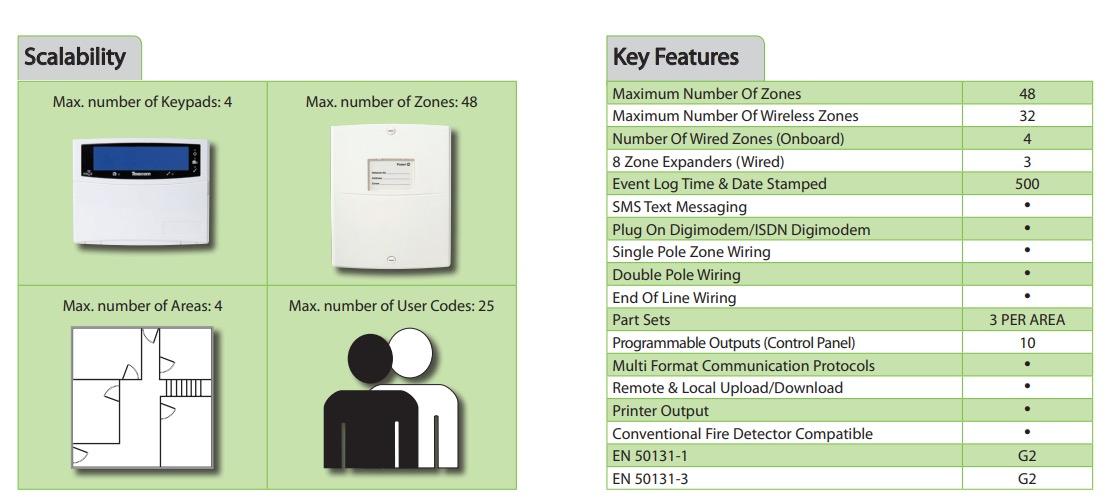
The Premier Elite 48-W is a wireless control panel suitable for a wide variety of security applications. Combining class-leading Premier Series control panel architecture with Ricochet mesh network wireless technology, the Premier Elite 48-W is compatible with Texecom’s entire range of peripheral devices.
� Suitable for premium residential and commercial applications
� Expandable to 48 zones with 4 partition areas
� Accepts up to 32 Ricochet enabled wireless devices - No wireless expander required
The Ricochet wireless technology has been invented to provide reliable wireless communications in commercial environments. The Premier Elite 48-W features Signal Security™ and self-healing functions delivering unparalleled communications reliability.








Elevate your brand, deliver the highest quality security. The Odyssey X range brings innovation and a modern twist to external sounders, providing unparalleled performance and extensive features to benefit installers and end users alike.





We provide a range of innovative fire protection systems to help you monitor and minimise threats, whilst meeting current building regulations and health and safety standards.
Protecting both your staff and investments from the threat of fire is crucial. Our range of innovative fire protection systems help you to monitor and minimise threat, whilst also meeting current building regulations and health and safety standards.
We will survey your property free of charge and recommend the best system for your needs.
We are proud to support the following systems, but not limited to:











Our conventional panels are ideal for use on smaller retail and commercial buildings. Easy to install, use and maintain, they are the system we would recommend when budget and simplicity are of importance. Different models come with various numbers of zones, so whatever your requirements, there will always be an appropriate panel available.
Addressable fire detection systems are the most widely used panels in the industry today. Suitable for any sized project or application, they recognise specific devices, making locating the exact origin of detection incredibly quick and easy.
We always utilise the leading open protocol panel manufacturers as these are compatible with the leading detector manufacturer protocols. Addressable systems are easily integrated with other control systems via interfaces, so cause and effect systems can be established in the building.
The latest in fire alarm systems, they require no cables to fit and are therefore easy to install. The radio signal technology provides an aesthetically pleasing and surprisingly cost-effective alternative to wired systems.
We supply and install all types of fire detection systems, including:

� Conventional Panels
� Addressable Fire Alarm Systems
� Wireless Detection Systems
� Gas Suppression Systems
� Aspirating Systems
� Beam Detection Systems
� Radio Fire Alarm Systems
� Temporary Building Site Fire Alarm Systems



British Standards require that fire extinguishers are placed in buildings in easily accessible areas, fire escape routes and areas of higher fire sensitivity. We utilise our extensive experience in the fire and safety industry to take on board your requirements and place them in the most appropriate and legally correct locations throughout your property.
As there are a variety of fires, each based on their cause of ignition, there are also a number of concordant extinguisher types (water, foam, CO2 and powder) designed specifically for each cause of fire. We ensure that the appropriate fire extinguisher is placed in all specified areas of a building.
As well as portable fire extinguishers, fixed hose reels can be found in many buildings that give a constant water supply in the event of a fire.
British Standards also state that like all fire and security systems, fire extinguishers must be properly maintained to ensure their proper and accurate function in the event of a fire, and their safe storage within a building. All extinguishers must be given an annual basic service. When they reach their life expectancy (either five or 10 years) they must also undergo an extended service and recharge.
We take this service and responsibility incredibly seriously and we are meticulous with our maintenance and security testing to ensure that our clients are protected at all times.







C-TEC’s cost-effective and easy-to-install SigTEL system is designed to meet the demand for BS 5839 Part 9 compliant disabled refuge, fire telephone and stadium marshalling systems. Current Building Regulations insist all new nondomestic buildings with more than one storey provide ‘refuge’ areas – safe places where people who cannot easily use fire escapes and evacuation lifts can call for assistance and wait until help arrives. SigTEL provides simple, effective two-way communication in these areas to assist rescue teams in determining where assistance is required and to reassure people help is on the way. It can also be used by trained personnel in sports stadia etc to help ensure the orderly evacuation of people in an emergency.
Our SigTEL 4–224-line emergency voice communication system comprises three wall-mounting master controllers (the ECU-4, ECU-8 and the ECU-16 which can handle 4, 8 or 16 lines). Typically located in a building’s control room or fire services access point, they allow emergency personnel to communicate via a telephone-style handset with the system’s ‘outstations. A powerful networking facility allows up to 14 master controllers (any mix) to be interlinked meaning systems of up to 224 lines can easily be created.



For SigTEL systems with multiple outstations, our new ECU-224-line desk controller is just the job for Disabled Refuge or Fire Telephone Outstations! Connect it to a SigTEL controller using an ECU-723 interface/ network card and away you go!

Hands off
Designed for disabled refuge systems, our ‘Type B’ outstations offer true hands-free duplex speech and allow anyone in a refuge area to communicate with building control at the touch of a button. Features include additional connections for an optional induction loop system and a general-purpose relay output that closes on activation of the unit.

BS 8300 recommends all disabled refuge outstations have facilities to assist the hearing impaired. Our new PDA103i is a ‘bolt on’ hearing loop system that can be used to help satisfy this requirement. Housed in a water-resistant enclosure it has adjustable input and output controls so it can be set up to suit the exact characteristics of any environment. Ensure your disabled refuge systems – both new and existing –are accessible to all by connecting a PDA103i to your outstations today!


Our ‘Type A’ telephone-style outstations are designed for use in stadium marshalling systems and other emergency evacuation applications. Comprising a telephone handset in a push-to-open or key lockable red steel cabinet, they are typically located at entrances and fire-fighting lobbies to allow fire marshals and other trained personnel to communicate with building control during an emergency.
C-TEC’s roaming portable handsets and fire telephone jack plates are increasingly in demand overseas where ‘Type A’-style portable handsets and jack plate combinations are accepted by prevailing standards. Jack plates are typically located in stairwells and risers allowing marshals, security guards and sports stewards to plug their handsets into them in an emergency.
With fire legislation in many countries now stating any power supply performing a mandatory function of a fire alarm system must be certified to EN54-4, C-TEC’s range of Series 5 switch-mode digital hybrid LPCB/ VDS certified power supplies has come into its own. Ideal for controlling beam detectors, auto-dial communicators, aspirating smoke detectors, electromagnetic door holders, ventilation systems and more, the range comprises 1.5A, 3A and 5A 24V units and a 2A 12V unit. A comprehensive range of non-EN54 PSUs is also available.



Our market-leading NC951 accessible toilet alarm kit contains everything you need to create a BS8300 clause compliant single zone emergency assistance system including a stylish double gang call controller, ceiling pull, overdoor light c/w sounder and reset point c/w sounder. Systems can be easily expanded to include up to three additional 800 Series Call System devices. Recently updated to include a Call Accept function, in the true spirit of BS8300 the NC951 now provides audible and visual indication inside the WC that help is on the way.

Introducing our new QT951 addressable disabled persons toilet alarm kit, specifically designed to meet the rising demand for true BS8300 compliant accessible WC alarm functionality on our Quantec addressable call system. This costeffective expansion kit allows people in distress to call for assistance and staff to send a confirmation signal that help is on the way. Must be used in conjunction with a Quantec controller.






Analog and digital two-way radios differ in several ways, including their technology, performance, and features. In this blog, you can examine their key differences, as well as how operators of analogue radios can migrate to the advanced capabilities of digital radios.
The standard for analogue two-way radios were created by the FCC in the late 1970s and have been popular for decades. However, the Digital Mobile Radio (DMR) standard was created in 2007 as a more advanced level of communication for the same type of applications. While analogue allows twoway communications in certain frequency bands for business and commercial systems. Analog radios are simple to use and are often all that is needed on a personal level. On the other hand, when you need a more advanced radio capable of messaging, location services and more, then look towards digital radios.
Both analogue and digital radios are capable of sending signals over a radio channel using a Very High Frequency (VHF) or Ultra High Frequency (UHF) carrier waves. In simple terms, analogue radios use frequency modulation (FM) to encode a voice signal within a carrier wave. Your voice changes, or modulates, the frequency of the wave. The difference between the modulated frequency and the baseline channel frequency can then be demodulated by the receiving radio and turned back into a comprehensible voice message.
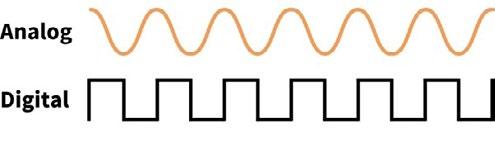


Digital radios do the same thing, but they have an extra encoding step before the voice signal reaches the carrier wave. The voice message is encoded into binary packets (ones and zeroes). These packets of numbers are then able to modulate the frequency of the carrier wave. The modulated frequency of a digital signal is not a continuous wave but instead an intermittent stepped change (as illustrated bottom left).
Digital Mobile Radio (DMR) is an open digital mobile radio standard defined by ETSI (The European Telecommunications Standards Institute), and this is applicable all over the world. All commercial products must comply to it, and users are not locked into proprietary solutions. The DMR standard Consists of DMR Tier I, Tier II and Tier III. Each tier provides different functionality and coverage range.

Digital radios provide several advantages and additional benefits compared to analogue radios as follows:


DMR uses the two-slot TDMA in a 12.5 kHz channel – this means that, as opposed to analogue communication, you have two slots for communication instead of one. Time is essentially split up in milliseconds so that users don’t notice the time gaps, allowing a doubling of capacity for two channels instead of one.
Analog radios support up to 16 channels, and some analogue radios have continuously rotating channel selector switches that can support up to 128 channels. DMR radios with advanced trunking technology can support hundreds of channels.
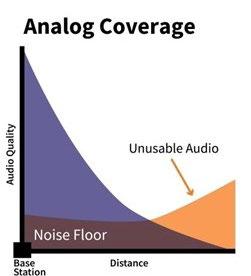
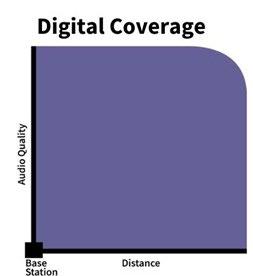
A standard analogue radio is going to decrease in signal the closer you get towards its maximum range, at which point, all you hear is white noise. On the other hand, a digital radio is going to remain much more consistent in sound quality regardless of distance to or from the maximum range.
An analogue radio and digital radio with the same transmission power radio will transmit over the same distance, the digital radio will remain loud and clear all the way to the end of the covered area whereas the analogue radio will gradually fade towards the end of the covered area.
With the use of repeaters, the range of digital radios can extend for hundreds of miles, and even without repeaters they are far superior in range to analogue radios. Analog radios have continuously rotating channel selector switches that can support up to 128 channels. Unlike analogue, digital transmissions can be in any form such as voice or data.
Analog signals are typically less tolerant to external noise interference, which means lots of unwanted background noise that can get in the way of crisp and clear communications. In other words, noise adds extra random information to analogue signals.
Each time the signal is amplified the noise is also amplified. Digital radios feature real-time audio processing that focuses on speech and reduces any background noise. This means that the received audio quality is enhanced when compared to an analogue radio system.
Digital technology also allows the receiving radios to auto-correct any errors in the received signal to maintain audio quality at the extremes of the radio coverage. Hytera digital radios contain unique technology that filters communication channels, fills in microscopic gaps, breaks in transmission, and minimizes error rates. Digital radios can make your communications clearer by reducing unwanted background audio and focusing on the wanted speech. Increased audio quality in poor coverage areas reduces the need to repeat information and improves efficiency.
Because they are more efficient, digital radios feature a longer battery life, and require less frequent charging or battery change out. The difference is substantial because digital radios extend operational battery life for several hours. That means more reliable communications and eliminates the need for staff to carry multiple batteries for a single shift.
One of the most important advantages is security. With digital radios, encryption can be used without degrading the quality of the audio, or the range at which the radio works.


Additional capabilities enabled by digital radio technology include GPS tracking, text messaging and data services, private calling, group calls, and safety features
Trunked Radio systems are two-way radio systems that optimize voice call or data traffic through a limited number of frequencies, maximizing the available resource for a large group of users. This is critical to ensure that communication is always instant and available for professional or enterprise level users.
DMR Tier III Trunked Radio utilizes repeater technology with a dedicated control channel, managed by a server. This allows resources to be brought together, controlling radio traffic for multiple user groups. Unlike other networks, DMR Tier III trunked networks deliver feature-rich, missioncritical communications over large geographic areas making it useful for enterprise level operations. Digital radio repeaters can be connected over IP networks to enable wide-area radio network of multiple repeaters.
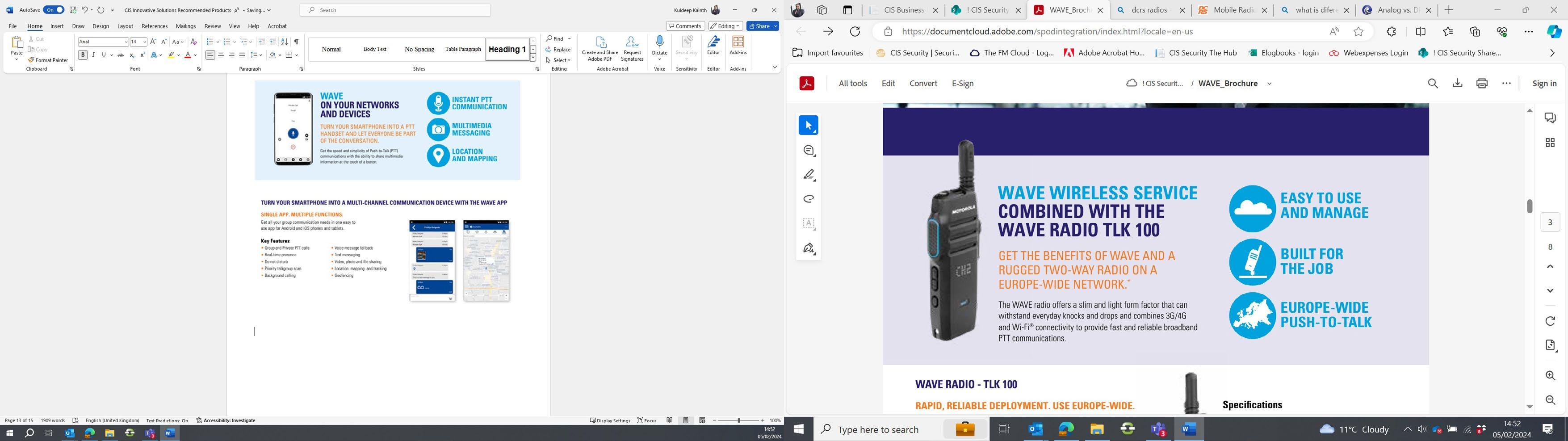


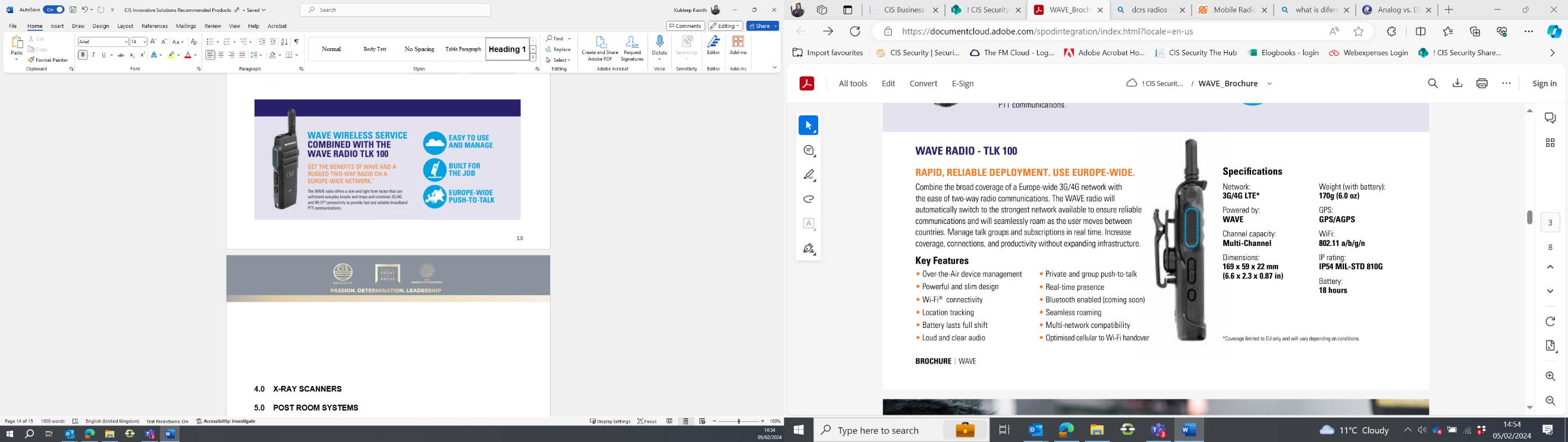
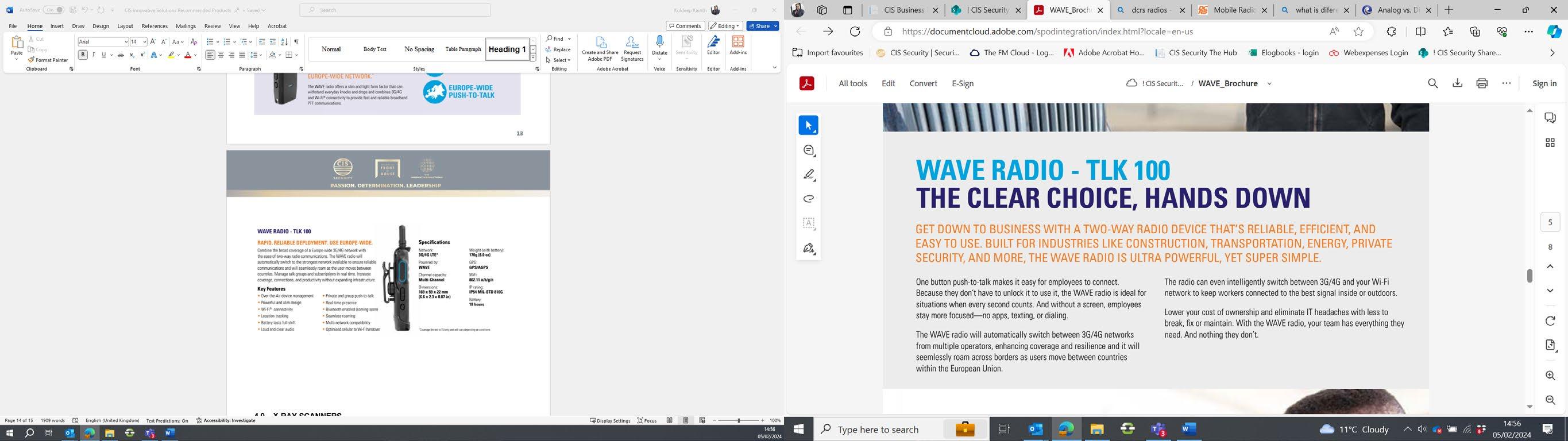



Ever thought how great it would be to have the reliability and simplicity of two way radios with the global coverage of mobile?
IDARO is the revolutionary smart solution that takes instant team communications to the next level. Marrying the functions of two way radios with the features of a smartphone, IDARO instantly connects your teams, across global networks, at the touch of a button, no matter the sector.
With IDARO, there is no need to carry separate radios, smartphones, or other devices around with you. A single handset, a single contract, and you have all the communication functions you need at your fingertips



Whether it’s a single conversation, a group call, or a company-wide session, IDARO is the smart solution for any organisation, bringing teams together instantly and effectively with a single touch of a button. Faster than scrolling through contact lists or setting up online meetings, IDARO is the responsive solution you need.
As businesses increase their geographical reach and more and more people work from remote locations, IDARO removes the coverage limits of analogue and digital radios to connect everyone in your team, wherever they are. Utilise broadband networks with PTT communication that allows you to connect from anywhere with network coverage.
GROUP OR INDIVIDUAL CALLS
A single person can reach hundreds of users, organised in groups or have 1-to-1 private calls or send messages outside of a group.
TASK MANAGER & CENTRAL COMMAND
Assign tasks to team or individuals. Real time status report. Multiscreen central command centre.
As tough as a two-way radio, as featurerich as a smartphone – IDARO handsets deliver the best of both worlds.
EMPLOYEE SAFETY
Man Down: automatic emergency notification. Fall detection with instant alert. Conforms to British certification standards.
LOCATION & MAPPING
Real time location and Geo-fencing on a map, creates alerts, records last location, and provides coverage in enclosed environmentsstandards.






Figures show that unauthorised vacant property was up by 25% in 2020 in the UK. This coupled with the increase in homelessness, (Shelter report every 1 in 206 are homeless. Since the pandemic there are 180,00 households now homeless, with 91 families a day adding to this number). The increase in resources for accommodation in terms of families not being able to afford the current rents is also a factor. The numbers for current known squatters in the UK are stated at 200,000. This figure changes depending on sources. However, with websites that actively encourage how to squat, the rights, law and processes, this information to encourage squatting puts our customers properties at risk.
While we understand that this is a desperate situation, we need to look at the risks this poses to our customers and their business. Any vacant property that may be under your portfolio will need to be assessed and appropriate discussions with the customers regarding vacant property protection. Squatters themselves have numerous tactics. These are some that CIS team have experienced:



1. Some groups will occupy buildings, open communications to stay in those properties and come to agreements with the owners that the building will be taken care of, and they will agree to leave at specified dates. This gives them a home for free and protects the building from other less scrupulous squatters. (rare)
2. Will occupy, have no open comms and then it is down to luck as to what state the building is in when they are removed
3. Will occupy and then the immediate area becomes a sudden crime hotspot, parties, ASB, drug use and dealing, theft etc.
4. Severe building damage, theft of metals, cabling, and other valuable construction materials, potentially leaving the building structurally unsound.
5. May barricade themselves in, set booby traps and have limited access/egress from the property, including utilising the security measures applied to keep them out. All to make repossession as difficult as possible

There are many difficulties in dealing with squatters in terms of what their rights are and what we can do. Below is an overview for your information:

Squatting is when someone deliberately enters property without permission and lives there or intends to live there.
This is sometimes known as ‘adverse possession’ or ‘occupying a building’.
Squatting in residential buildings (like a house or flat) is illegal. It can lead to 6 months in prison, a £5,000 fine or both.
Anyone who originally enters a property with the permission of the landlord is not a squatter. For example, if you’re renting a property and fall behind with rent payments you’re not squatting if you continue to live there.
Although squatting in non-residential building or land is not in itself a crime, it’s a crime to damage the property.
It’s usually a crime not to leave land or property when you’re instructed to do so by:
� The owner
� The police
� The council
� A repossession orders

A non-residential property is any building or land that is not designed to be lived in.
Simply being on another person’s non-residential property without their permission is not usually a crime. The police can act if squatters commit other crimes when entering or staying in a property.
Crimes include:
� Causing damage when entering the property
� Causing damage while in the property
� Not leaving when they’re told to by a court
� Stealing from the property
� Using utilities like electricity or gas without permission
� Fly-tipping
� Not obeying a noise abatement notice
You can remove squatters using an interim possession order (IPO) or making a claim for possession.

Do not try to remove the squatters yourself using force or the threat of forceyou’re committing a crime if you do.
Interim possession orders
You can only apply for an IPO if it’s been 28 days or less since you found out your




Property’s been squatted.
Fill in an application for an IPO and send it to your local county court.
The court will send you confirmation of your IPO within a few days. They will also send you documents that you must give to the squatters within 48 hours. After being served with an IPO squatters can be sent to prison if they do not:
� Leave your property within 24 hours
� Stay away from your property for 12 months
� To get final possession of the property, you must make a claim for possession. You can do this on your IPO application form or separately online.
You cannot use an IPO if:
� You’re also making a claim for damages caused by the squatters - instead you should make an ordinary claim for possession
� You’re trying to evict former tenants, sub-tenants, or licensees.
Make a claim for possession if it’s been more than 28 days since you found out about the squatters.
CIS Innovative Solutions can provide the following services to help you mitigate against occupation of the buildings.

Effective physical security is based on the concept of defence in depth, the creation of multiple layers of security.
Defence in depth is characterised by interdependent concentric layers of security controls, with each layer consisting of increasingly complex measures designed to protect people, property, and information.
In the case of void property this would consist of the following:
� Perimeter fencing - boundary marker denoting ownership
� Concrete barrier blocks - to prevent vehicle access to the site
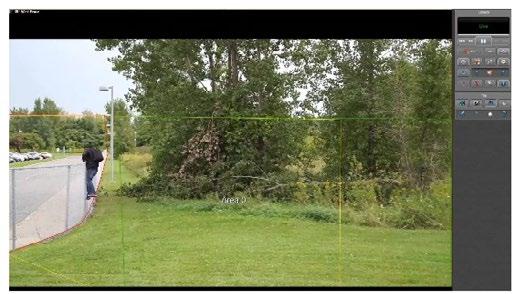
� External mounted Video verification systems – detection
� Windows and doors boarding-up - delay intruders
� Internal video systems / intruder alarms - adversary path confirmation
Boarding up of windows and doors is one layer of a physical security system, the primary purpose of which is to both deter those that can be deterred and to delay those that can’t.
There are a variety of options available to property owners and landlords when considering boarding up a vacant property.



Steel Perforated Sheets:
Steel perforated sheets provide a heightened level of security when compared with timber. The benefits of PS screens include:

� Visible deterrent to criminals
� Creates a steel barrier over the window
� Perforation lets light through to allow internal viewing
� Resistant to arson attack
� Cut to size to fit into window reveals
� Fairly cheap long-term solution

The benefits of Perforated steel screens over timber boarding are obvious, however similar to timber they are fitted directly into either the window frame or brick wall, once again damaging the fabric of the property.
There are also limitations in using Perforated Steel sheets on listed properties, often resulting in Perforated Steel screens being fitted to the inside of the window (internally), which significantly reduces the effectiveness of this solution due to the ease with which such screens can be kicked out once the glass has been smashed.

Sitex security screen panels became popular in the 1990’s after their introduction by a leading security company. They quickly became the preferred solution for securing vacant properties requiring a heightened level of security.
Sitex security screen panels are secured by either drilling holes in the window frame and inserting cables which are then secured internally across the window by a steel bracket, which is then attached to the panels creating a very strong seal, or more commonly the glazing is removed when using this method of boarding up solution.
The benefits of utilising Sitex security screen panels include:
� A highly visible deterrent to trespassers
� Robust and long lasting
� Perforations allow light and ventilation
� Installed from the inside for maximum security and minimum damage
� Arson-resistant
� Can be fitted over doors, windows, and other entry points


This innovative method of boarding up has the following benefits:
� Quickest method of installation
� Multiple contact points create a rigid secure barrier
� Bolted panels cover all shapes of enclosure
� Rapid removal and re-use of panels
� No requirement to remove windows
� No drilling into window frames or brick work
� Damage free secure barrier
� Maintains environmental seal
Compression security screens have been designed to provide a rapidly deployable boarding solution that is as secure as Sitex security screen, as quick to install as Perforated Steel screens, but doesn’t require the time-consuming removal of windows or cause damage to the property.
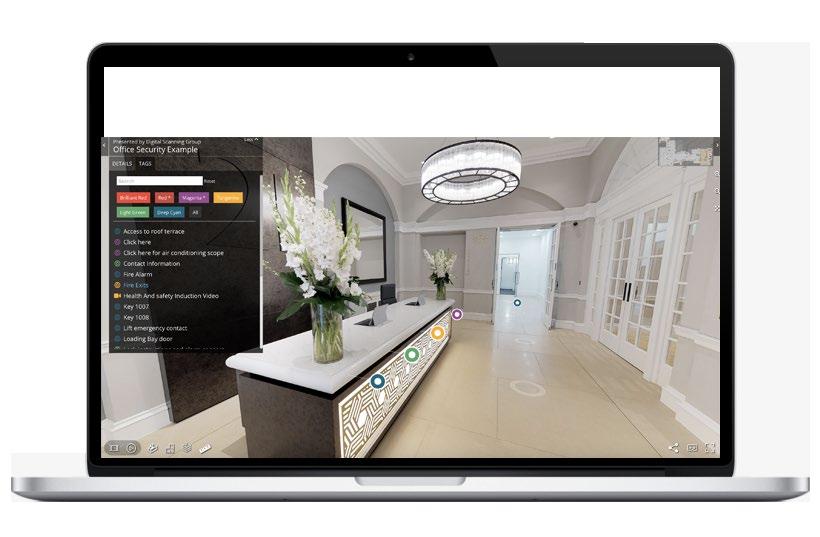
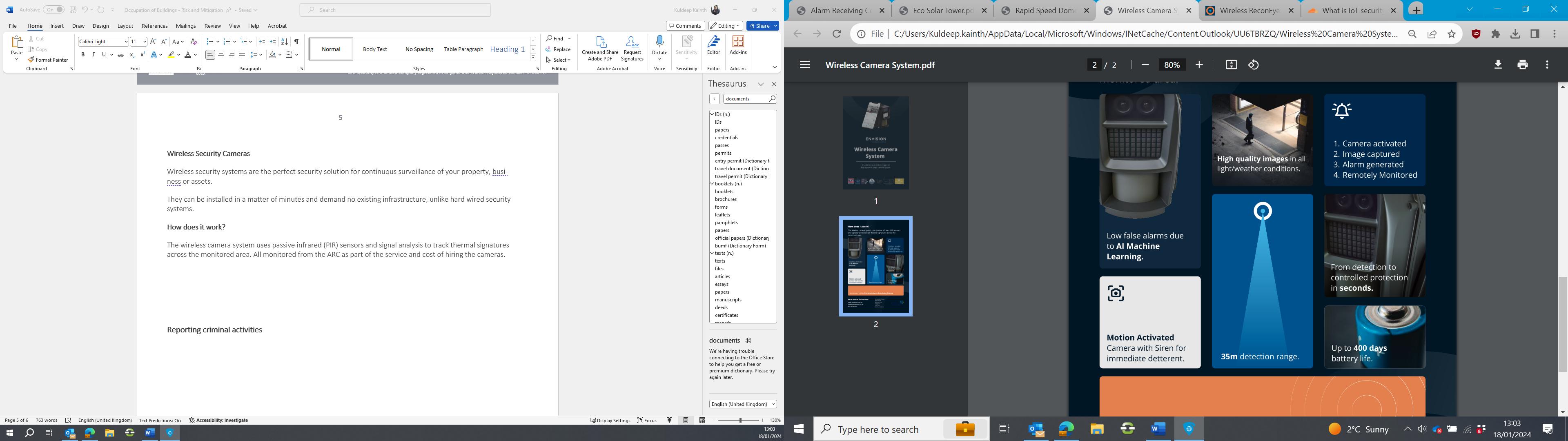
CIS Innovative Solutions partner with Envision Intelligent Solutions to provide the latest monitoring services for empty buildings. Alarm Receiving Centre


How does it work?

How does it work?

The Envision ARC is a high availability Connected Solutions Centre that can remotely monitor any IOT (computerised Internetconnected objects, i.e. networked security cameras) device on a fully managed service.
The wireless camera system uses passive infrared (PIR) sensors and signal analysis to track thermal signatures across the monitored area. All monitored from the ARC as part of the service and cost of hiring the cameras.





A 4G Re-deployable CCTV Infra-Red Speed Dome design specifically to deliver live and recorded high-definition images via 4G mobile transmission.
This 4G IR Speed Dome Camera is designed and built for applications where you need fast deployment of CCTV. The Rapid Speed Dome is perfect for temporary installation where you need to send live video via 4G mobile network. It is specifically designed to be mounted quickly and securely on various locations with a unique plug and play design with single power connector enabling easy installation and redeployment.




Eco Security Towers are wireless solar CCTV towers designed to provide site security for construction sites, critical national infrastructure or any location requiring standalone wireless CCTV with full surveillance.
Eco Solar Towers provide live 24/7 site security with a dedicated account manager, helpdesk and qualified engineers will be on-hand to offer support. The cameras will be monitored from the ARC as part of the unit higher fees.





CSOC | CIS Security Operations Centre









































Capra Hircus was created to provide our customers with cutting-edge dependable mobility for their applications. The state-of-the-art mobile robot answers the issues that have troubled the mobile robot industry for years, namely a lack of versatility, poor driving capabilities, short ranges, low operating time, and high pricing.
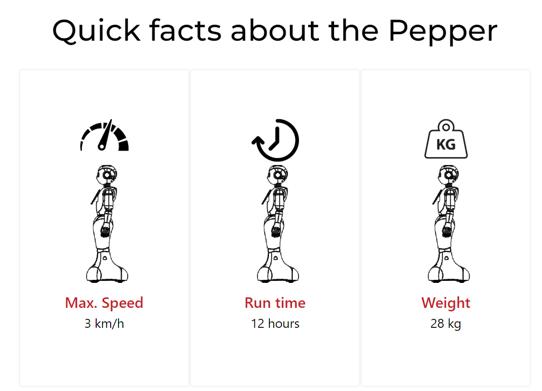
Pepper the robot was designed to interact with people and be expressive, as it is equipped with a set of sensors and interactive equipment, allowing it to lead a discussion with the user. In addition, it is equipped with a set of sensors, such as laser sensors, to manage its safety and that of people around.
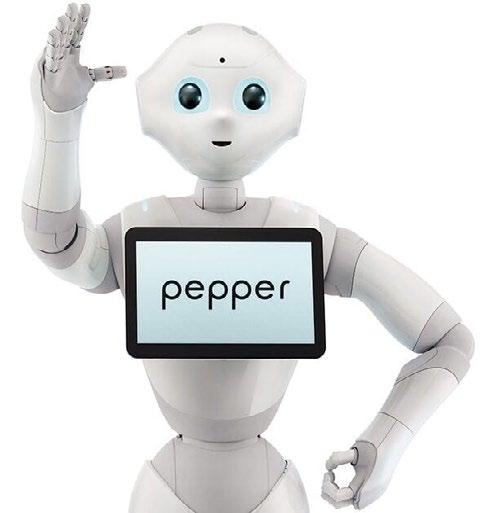


Pepper is the world’s first social humanoid robot able to recognize faces and basic human emotions. Pepper was optimized for human interaction and is able to engage with people through conversation and his touch screen.


World’s first cost-effective robot that delivers groundbreaking engagement solutions for your business or personal needs utilizing Temi’s proprietary autonomous navigation and AI technologies















Axon Air is Axon Enterprise’s integrated drone platform designed to enhance situational awareness and support public safety operations.
� Axon Air provides a complete drone ecosystem built for law enforcement and public safety agencies.
� It offers real-time aerial video so command staff and field personnel can monitor incidents as they develop.
� All captured data seamlessly integrates with Axon Evidence, ensuring proper storage, chain of custody, and case management.
� The platform supports Drone as First Responder (DFR) workflows, enabling rapid deployment and early visual assessment before units arrive on scene.
� Axon Air is powered by DroneSense, which supplies the flight control, program management, and operations interface.
� Axon also partners with Skydio for autonomous drone hardware.
� Additional integration exists with Fotokite, offering tethered drones that stream live footage directly into Axon Evidence.

� Live livestreaming to command centers and authorized users.
� Centralized program management for pilots, missions, hardware, and flight logs.
� Regulatory compliance tools to support safe and approved flight operations.
� Deep integration with Axon Respond (real-time operations) and Axon Evidence (digital evidence management).
� A Transparency Dashboard that allows agencies to publicly display flight data to build community trust.
� Support for various drone platforms, including Skydio X10 (outdoor) and Skydio R10 (indoor).

� A legacy Axon Air app exists for piloting and uploading footage.
� The newer Axon Air powered by DroneSense app on iOS provides an updated interface aligned with DroneSense’s capabilities.
� Axon views robotics—including drones—as a core part of future public safety operations, aimed at improving safety by giving responders more distance, visibility, and time.
� The company’s goal is to create scalable, data-integrated drone programs that operate seamlessly within the broader Axon ecosystem.


Advantages
� Rapid situational awareness
� Improved responder safety
� Streamlined evidence capture and management
� Comprehensive program oversight
� Scalable across agencies and hardware types
Challenges
� High costs for equipment, training, and program setup
� Regulatory hurdles, such as BVLOS rules
� Pilot training requirements
� Public perception and privacy concerns, though transparency tools may help.
If you want, I can also shorten this into a onepage brief, create a slide-ready bullet outline, or rewrite it for a non-technical audience.

DJI Dock 3 is a next-generation “drone-in-a-box” system designed for fully autonomous, 24/7 remote operations. It supports enterprise missions such as inspections, monitoring, emergency response, and automated routine flights.
� A rugged, self-contained launch, landing, and charging station for compatible DJI enterprise drones.
� Built for continuous, remotely managed operations through DJI FlightHub 2.
� Can be deployed in fixed locations or mounted on vehicles for mobile missions.






Tando™ is a self-navigating AI-based security robot drone that monitors and alerts you about intruders, security breaches, safety issues, and potential hazards while eliminating false alarms. Tando™ is a flexible, efficient, and futureproof security solution for commercial spaces.
While not in flight, Tando™ docks on the ceiling, serving as a security camera.


Tile™ is our patented ceiling-mounted docking & charging station. Tile™ is designed to support Tando™’s zero breaks schedule so Tando™ can monitor and inspect your space for security, safety, and maintenance issues even while charging. Tando™ can “hop” from Tile™ to Tile™ to cover large spaces more efficiently.
Control Bridge is the brain that manages Tando™’s operations. Create new missions and schedules, launch ad-hoc missions and get alerts on events, detections and changes customed to your needs. The Control bridge SW easily connects to any building system and other IoT devices.




















As facial recognition technology has only recently become available on the market, you may be wondering what aspects can play a role in the application. Below will provide better insight into what facial recognition access control entails exactly, and what to consider when purchasing such a system.
Improved convenience, increased security.
Biometric technology offers a highly secure and efficient method of access control by verifying unique physical traits such as fingerprints, facial features, or iris patterns. By eliminating the risks associated with lost or stolen credentials, biometrics provide fast, reliable, and seamless authentication, enhancing security while improving user convenience.
Iris scan: Every human iris has its own unique traits. An iris scanner identifies pits, furrows and striations in the iris and converts these into an iris code. Comparing this code to a database subsequently determines whether to allow access.
Palm veins: Near-infrared illumination exposes a palm’s unique pattern of veins and capillaries. Some palm scanners also measure features such as creases and nodules. This information creates a unique profile that can be linked to an authorised individual.
Fingerprint: There are various types of fingerprint scanners in existence. These all work by registering the unique pattern of lines on the skin. The resulting data can be used to determine whether to allow access.

Facial recognition: An algorithm is used to filter a human face from a video or photographic image. In only a few milliseconds, the face’s characteristics are recorded and converted into a unique code. Then the facial recognition software compares the code to a database. If it finds a match, this can be used to identify the individual in the image and determine whether or not to allow





Facial recognition technology provides fast and secure access control by identifying individuals based on unique facial features. Offering a touchless and efficient authentication method, it enhances security while streamlining entry, reducing reliance on physical credentials, and integrating seamlessly with modern access control systems.
Mass Surveillance
Mass surveillance uses facial recognition to pick individuals out of a crowd. This requires specialised hardware and powerful software in order to be effective.
This type of facial recognition is commonly employed in mobile devices such as smartphones, with relatively simple software and hardware requirements. Here the face is used as an alternative to a passcode.
Facial recognition can also be used to reconstruct an individual’s route based on video images. For example, such data can help identify where a fugitive was located over the past 24 hours.
Finally, facial recognition can be used within access control. It is important to have the software set up to compare information from multiple cameras with the database in real time. Based on the database size, a server is installed that can verify the authorisation with sufficient speed and then the access point can be opened.
One of the major advantages of facial recognition access control is the lack of waiting at the access point. The software will register a person’s face as they approach and can determine whether to allow access in the time needed to arrive at the gate. When the authorised person is near or at the access point, the system opens the gate. This prevents unauthorised individuals from slipping in through the open gate. Also, the person can proceed smoothly through the access point.




Stereovision has been proven through rigorous testing to be extremely accurate, and when paired with a security revolving door or portal and access control system, can prevent unauthorised entry without the need for manned supervision.
As a result of its constant data collection and configuration settings, Stereovision is capable of providing security managers with predictable metrics tied to asset protection, compliance and risk.
Features
� Prevents piggybacking (two people attempting to enter the door at one time)
� Replaces traditional weight systems or contact mats
� Sunlight or reflections do not impair sensor technology
� Differentiates between two people and one person with an object
� Seamless integration with access control system
� Provides predictable metrics tied to compliance and risk
� Fully adjustable to suit the user’s requirements
Benefits
� Piggybacking prevention ensures only authorised users can enter
� Accurate for all users regardless of height or weight
� Reduced / eliminated guard salary allows for quick ROI
� Data collection allows for the accurate prediction of the risk of infiltration




































Safe. Secure. Reliable.
Selecting the right physical security entrance is essential for effective access control. With a range of solutions available, each offering unique capabilities, Boon Edam categorise security entrances by their level of security to help professionals make informed decisions.
The effectiveness of a security entrance depends on its ability to deter, detect, or prevent unauthorised access. The right solution ensures security while supporting operational efficiency and compliance.
Security entrances can be classified into three levels, each designed to meet specific needs:
Low Security – Deters casual intrusion while maintaining an open and welcoming environment.
Medium Security – Detects and responds to unauthorised access attempts. High Security – Prevents intrusion with advanced security features and reliable authentication.

Wide Lane Access Gates

For entrances that need to remain welcoming while subtly enhancing security, wide lane access gates are the perfect solution. These gates act as a deterrent to unauthorised visitors, balancing accessibility and security. Designed to provide spacious and comfortable passage, they are ideal for supporting disabled access while discouraging casual intrusion.
Winglock Swing provides a smooth, barrier-free entry while ensuring controlled access for authorised users.



When balancing security with efficient visitor management, speed gates are essential. These gates create a strong visual barrier and detect tailgating attempts, triggering real-time alerts when integrated with biometric or access control systems. Perfect for building reception areas, speed gates help ensure regulatory compliance, reduce risks, and enhance operational security.
Lifeline Speedlane Swing provides seamless and intuitive access control, efficiently guiding users while deterring unauthorised entry.
Lifeline Speedlane Vision is an advanced speed gate with integrated AI facial recognition, combining fast, touchless access with smart security.
Speedlane Compact delivers efficient, space-saving access control with a sleek, minimalist design, ensuring security without slowing down user flow.


For critical security needs, high-security revolving doors and portals offer unmatched protection against unauthorised access. Their advanced design prevents intrusion and eliminates or reduces the need for guard supervision, delivering a fast return on investment. These robust solutions are ideal for environments requiring maximum security and reliability.
Tourlock 180 provides secure, two-way access control while preventing unauthorised entry, ensuring both safety and efficiency.
Circlelock Solo ensures controlled and automatically monitored access to your secure and sensitive areas.
Circlelock Combi enhances security for swing doors, controlling access and preventing unauthorised entry.

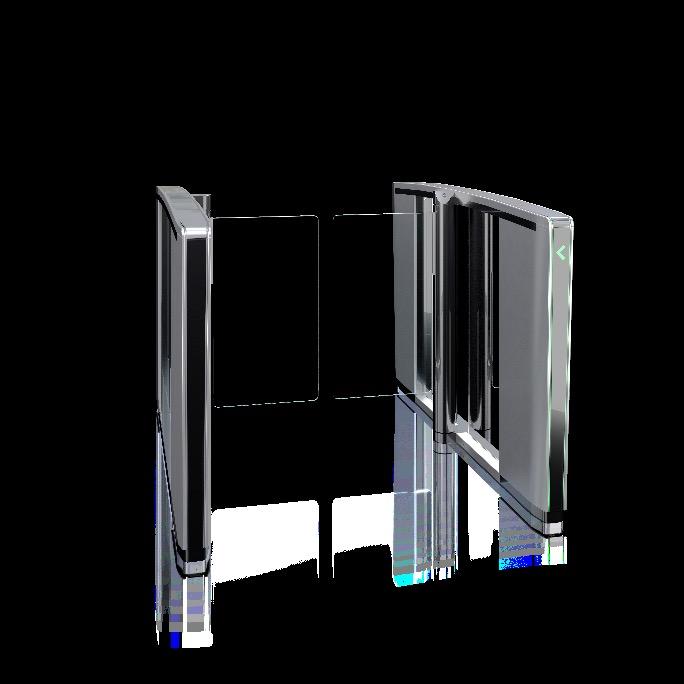
Piggybacking occurs when two individuals collude to enter a secured area using a single authorised credential—whether intentionally or not. While often confused with tailgating, piggybacking specifically involves cooperation between individuals. High-security doors combat this threat with advanced overhead sensor systems, detecting multiple occupants in compartments designed for single-person entry.
Tailgating happens when an unauthorised individual follows an authorised person through an access point—either innocently, such as assisting a colleague who forgot their access card, or maliciously, by sneaking in undetected.
Security entrances are designed to mitigate tailgating by offering various levels of detection and prevention, from solutions that require guard supervision to fully automated systems capable of maintaining high security even when unstaffed.




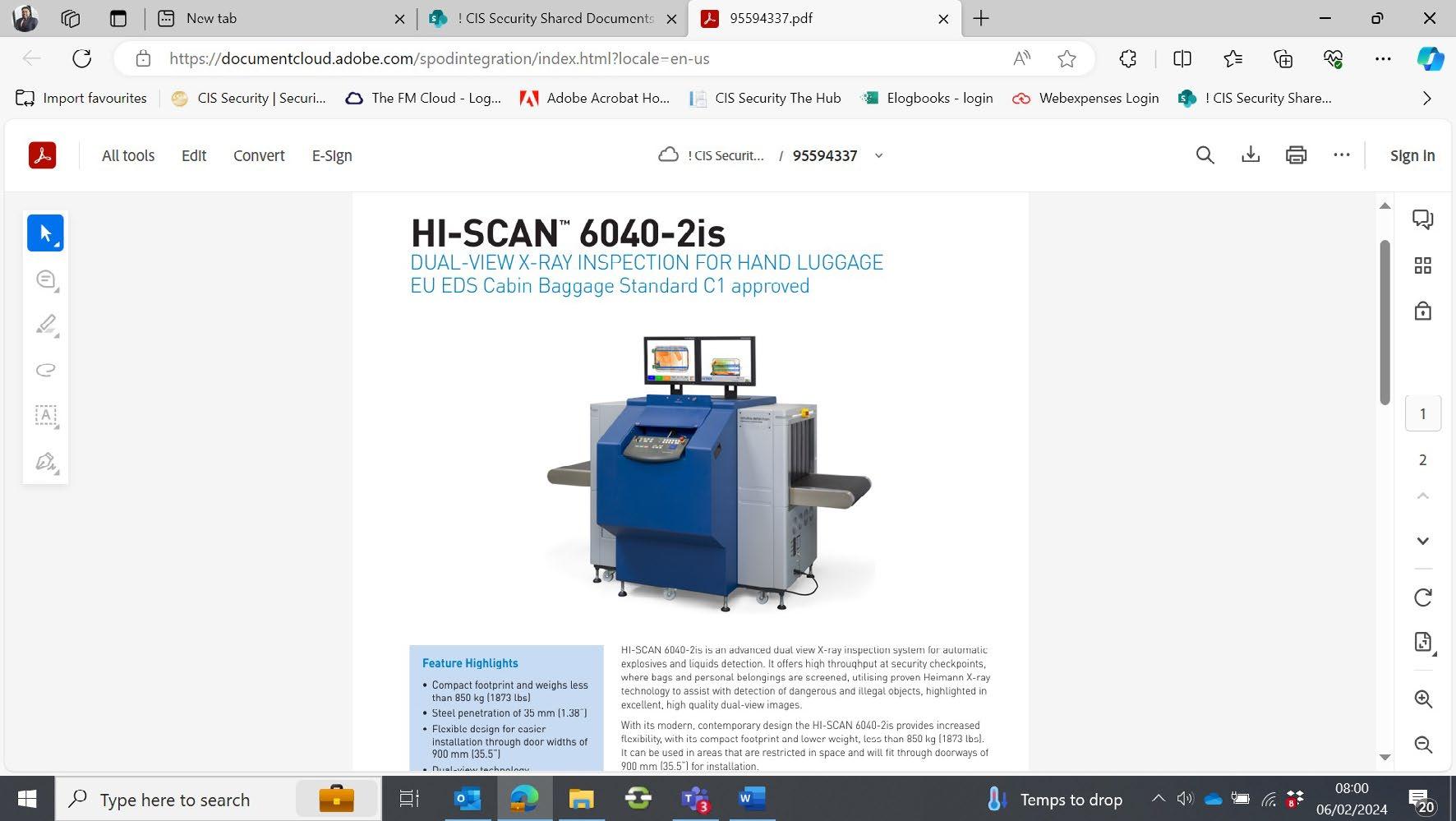
Offering superior image quality, smart display functions and easy integration into tray handling and management systems, it is the ideal solution for efficient screening in high threat applications such as airports, government facilities, embassies, or banks.

EDS CB C1 and LEDS algorithms – in combination with the optional iCMORE weapons capability for automatic detection of pistols, revolvers, gun parts, flick, and fixed blade knives – elevate security, efficiency, and automation, without requiring additional hardware.
The HI-SCAN 6040 DV also provides high levels of protection against cyber threats by applying industry best practices such as operating system hardening, a host-based firewall, TripWire integrity monitoring and powerful user management with highly configurable password policies.
HI-SCAN 6040 DV is compatible with the Checkpoint.Evoplus screening and management platform which supports actionable operational data insights and health status monitoring plus centralised screening.
Straightforward integration into Smiths Detection or third-party tray handling lanes makes it an ideal choice for high-throughput applications.




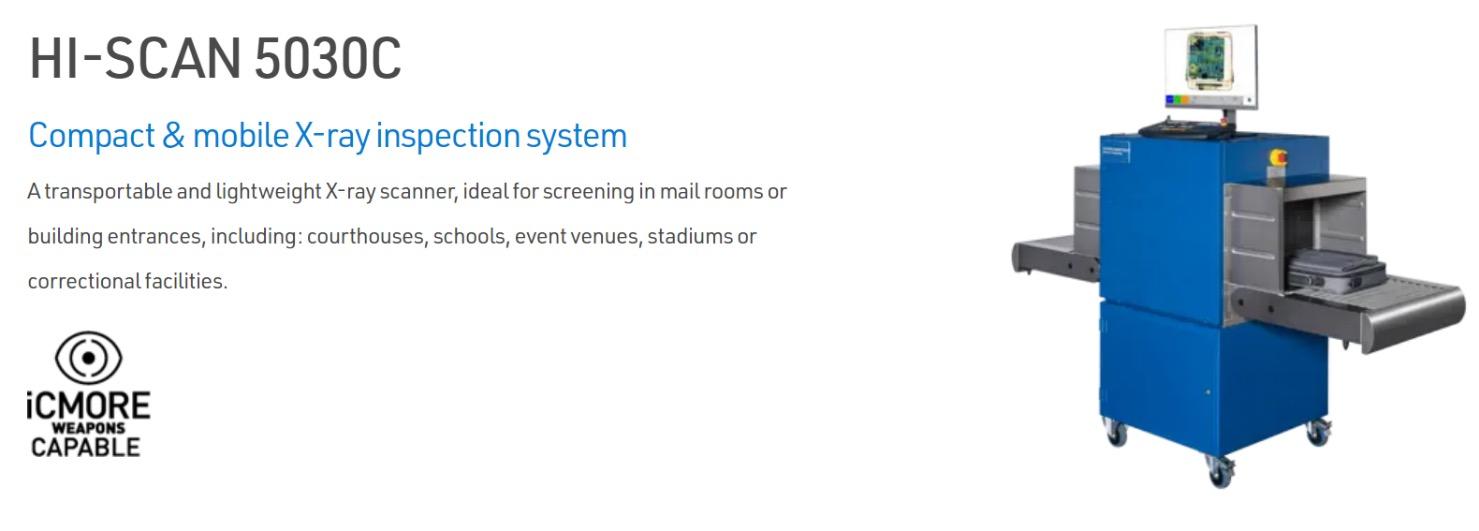

The HI-SCAN 5030C X-ray scanner is an ideal solution for screening mail and personal belongings in commercial and public buildings due to its size, mobility and durability.
The HI-SCAN 5030C is specifically designed to enhance security screening operations from courthouses to corporate campuses. Its compact size and lightweight construction enable it to fit seamlessly into checkpoints and mailrooms. Vibration absorbers make it possible to transport HI-SCAN 5030C between various locations without requiring re-calibration, providing maximum flexibility.
Featuring proven HiTrax 3 electronics and software platform to enhance and expedite security screening operations. It produces reliable and easy-tointerpret scanned images enabling screening personnel to make threat and contraband assessment of parcels to personal items quickly and confidently.
The HI-SCAN 5030C is available as a stationary desktop scanner or as a mobile version on wheels featuring vibration shock absorbers and a storage compartment.



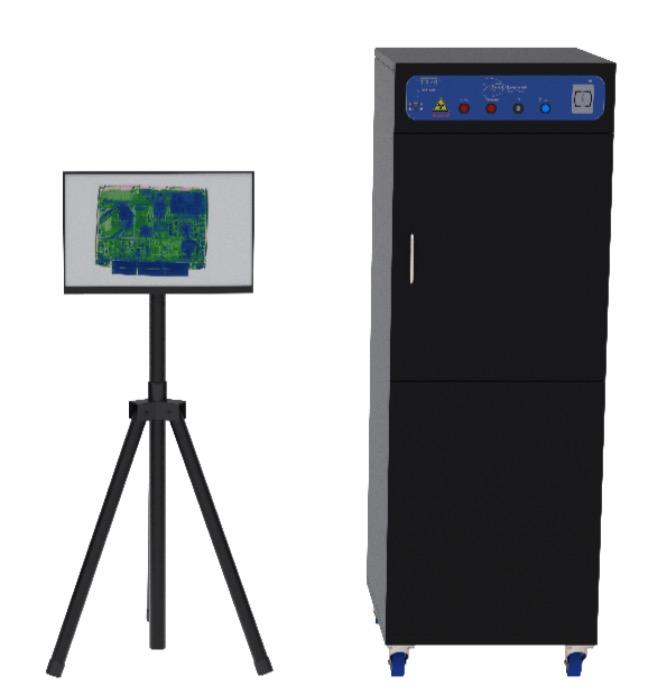

The very latest generation TR40 +Smart Scan cabinet scanner from Todd Research provides a new benchmark of threat detection and image management for compact cabinet scanners. At the heart of the TR40 +Smart Scan is a completely new software platform, managing the functionality and an intuitive user interface via a touch screen monitor. The smart card login means the TR40 +Smart Scan can be configured to enable data collection of individual user sessions further enhancing the effectiveness of the operators.

This is the largest cabinet scanner in the range, the generous chamber can accommodate mail sacks, large boxes and courier deliveries, with its one touch operation the TR40 allows rapid processing of scanned items all within a compact footprint.









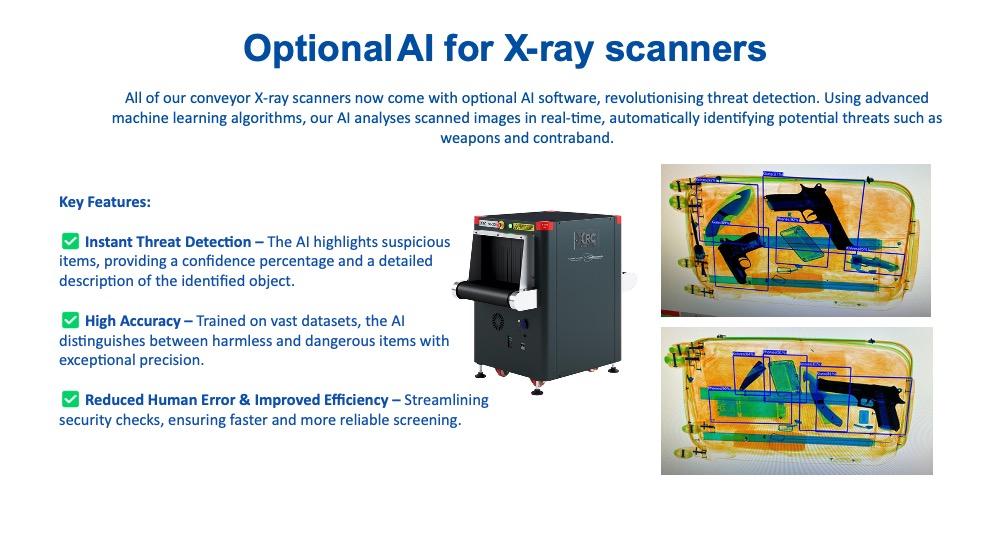




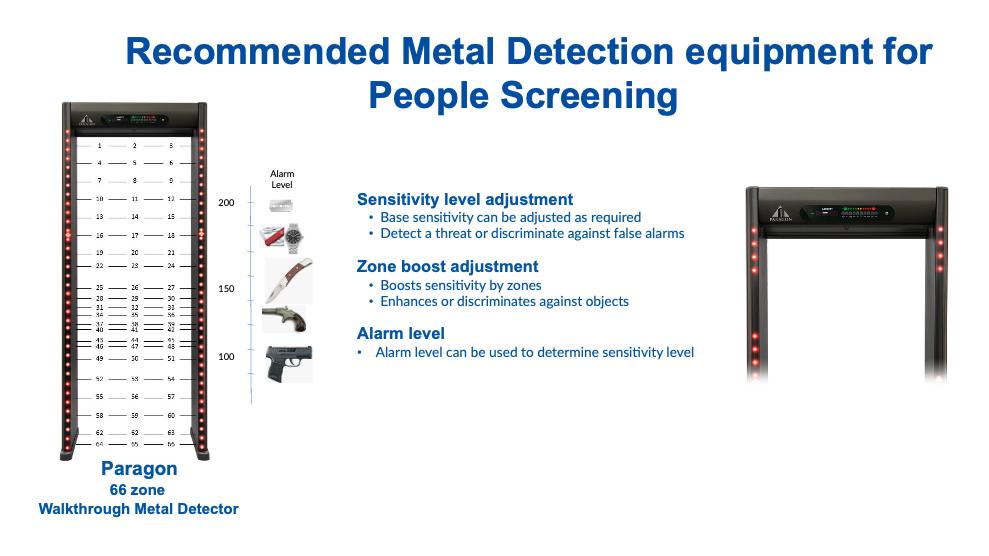











































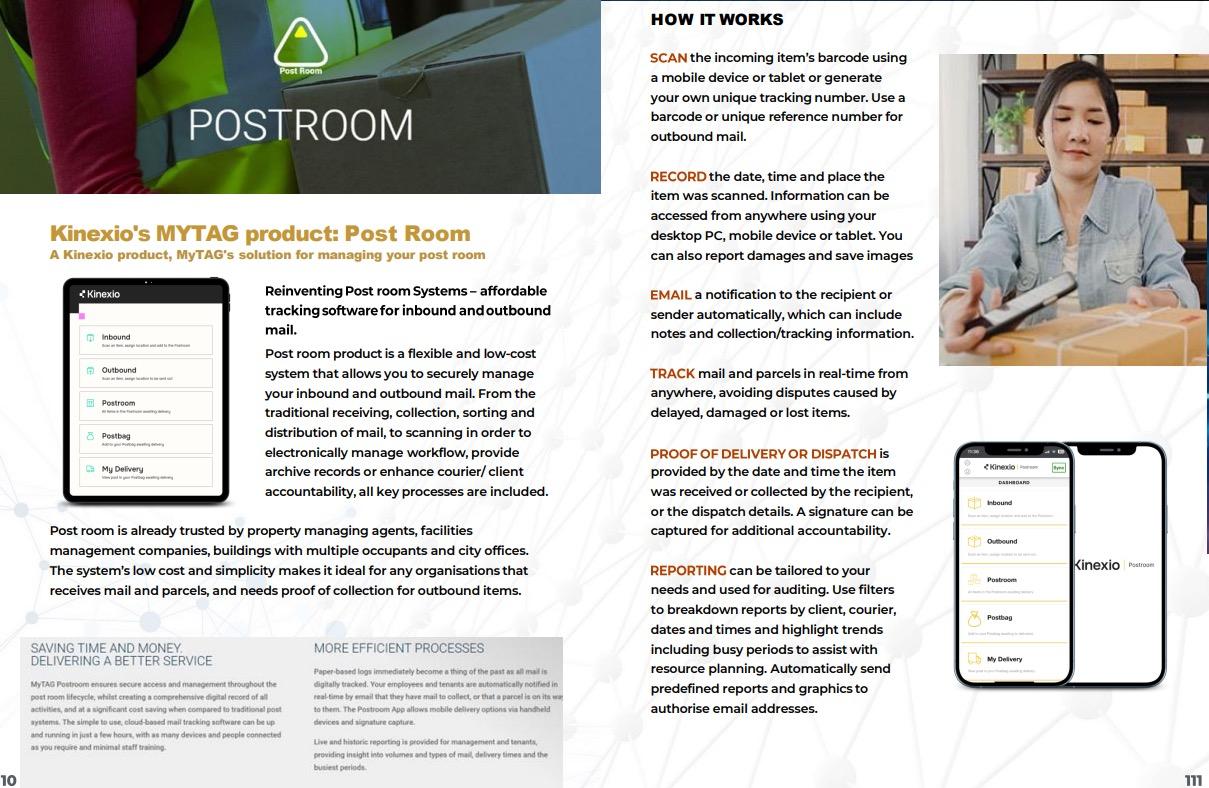


Delivery tracking software is a cloudbased solution which can be used for internal delivery tracking needs. Delivery tracking allows organisations and businesses to log all inbound parcels and mail items via an easy-touse system for end-to-end custody tracking and visibility.
Information can be accessed on any PC, mobile device, tablet or iOS/Android phone either within the building or remotely for live location tracking.




All you need to do is add a list of recipients to the admin back-end, and they will become searchable on any device using an app. Using barcode technology, a PDA (Personal Digital Assistant), or any mobile device you can access the back-end admin interface where all information is stored. PDA’s can display who the recipient is, the delivery details and the details of the item due for delivery. It can also notify recipients and senders of the package’s location before delivery.





Such delivery management software monitors deliveries in and out of premises for a full chain of custody tracking and reduced loss. It can track packages from destination to destination. All you need to do is update the system by scanning the barcode. The software will provide updates to recipients, so they know exactly where their parcel is.





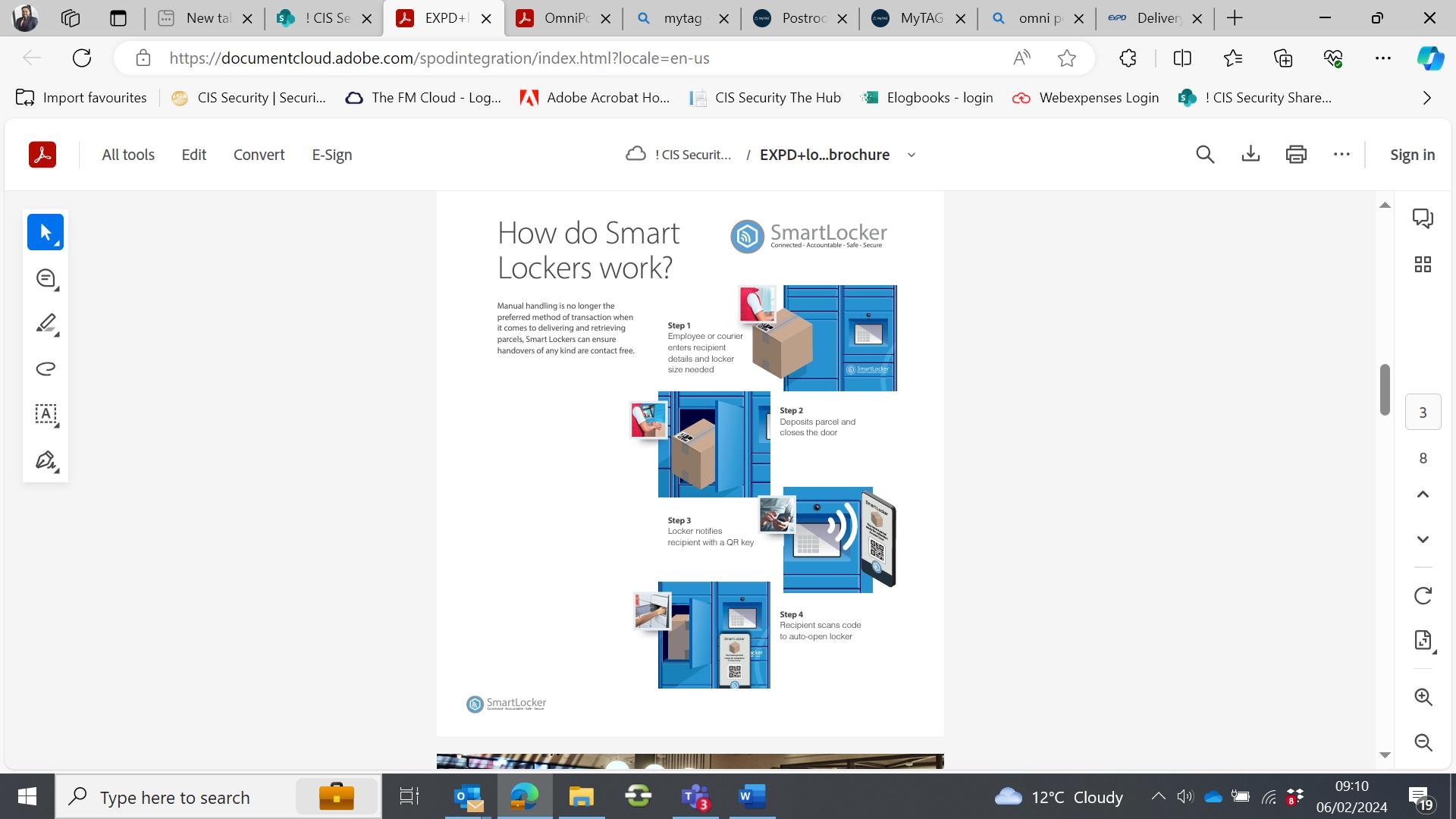








Staff, tenants and occupiers, reception teams and building management can access real-time visitor data. This allows for strategic decision-making on staffing, space utilisation and compliance. Smarter visitor access control gives you the ability to manage visitor movement and add additional layers of building security.
Bluepoint integrates with tenant platforms such as OfficeApp and HqO and leading access control manufacturers including, Lenel S2, CCure and Gallagher. So, whether you need hybrid, flexible, contactless or experience led visitor management, Yardi Bluepoint has you covered.


� Gain actionable insights to enable safer and more efficient management of your spaces
� Stay up to date with planned visitors and keep account of drop-in visitor numbers
� Plan in advance for reception services, security and visitor amenity requirements by reviewing Bluepoint data.
� Create branded visitor invitations with key information such as pre-visit forms or travel details.
� Integrate Bluepoint with on-site access control and include a QR code in the visitor invite for fast check-in
� Deliver a great experience from shortterm visitors and event attendees to contractors and staff.



� GDPR Compliant – stay up to date with visitors in your building for critical security and compliance
� Gain an accurate overview of who is where and when in your building with Bluepoint’s check-in and check-out process
� Implement additional security with time-limited, temporary access passes for visitors and staff



� Manage access permissions for meetings and events and enable your tenants to book time-limited appointments by visitor type
� Integrate with existing tenant management software to provide a seamless experience
� Invite visitors directly from any calendar: Outlook, Gmail; desktop or mobile – Bluepoint is compatible with all calendar apps



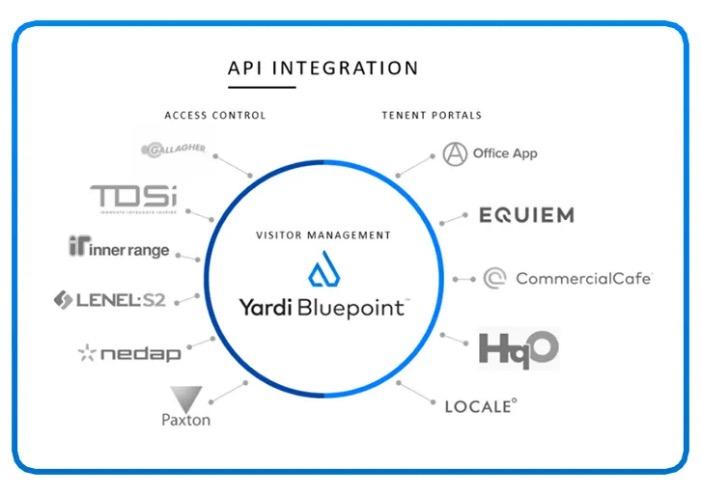
� Fully featured API allows for smart connections with new and existing building management technology
� Access control integrations with leading manufacturers and tenant engagement platforms allow for an improved experience
� Easy to implement and secure. The Bluepoint team are on hand to ensure a successful deployment.





� Bluepoint visitor management allows for smart access using existing access control with a mobile QR code or access card
� Activated Bluepoint QR codes can be used with speed lanes, lifts and even meeting rooms
� Facilitate contactless check-ins with a free standing or desk mounted kiosk
SkyVisitor, the visitor management system from ExPD, ensures checking in to your building is the simplest and most professional experience possible.
First impressions count, but regulatory compliance and the safety of visitors, contractors and your team, matter even more –SkyVisitor has that covered too.

Little can be more important in facilities management, than the way you physically manage visitors, contractors and your people to and through your buildings. We work with everything from prestigious multi-tenanted apartments and corporate headquarters, to food handling facilities, shopping centres and NHS Estates. SkyVisitor goes to work before your visitor, guest or contractor even arrives on site. When the host books a visit, the visitor management system automatically issues an invitation email. Although auto-generated, the content of the email can be branded and is fully customisable to include all the information the guest needs to simply and safely begin that visit.
That includes your location, which entrance to arrive at, and how to request and be assigned a parking space. It accommodates ad hoc visitors, contractors and staff and can outline security requirements and include essential health and safety information. It can even provide pass numbers or keys or include a unique QR code for contact-free, speedy check-in from their smartphone or mobile computer.
In addition to the systems for all visitor check-ins, SkyVisitor makes the management of staff, visitors and contractors on-site safer, more professional and more accountable.Pre‐planned visits ensure all documentation is in place before an individual even arrives on site. It also acts as a second layer of health and safety management and accountability.

Only once the host checks documentation is submitted and correct is the visit from a staff member, visitor or contractor approved.




The SkyVisitor Portal includes dynamic, real-time lists of expected, arrived and departed staff, visitors and contractors and allows for future planning and resourcing. Reports can include visitor statistics, trends, volumes, no‐shows and much more, ensuring your reception systems are working effectively. These can flag trends before they become issues.
The Online Portal allows you to view dynamic lists of expected, arrived and departed visitors and produce statistical reports such as visitor statistics, trends, volumes, no-shows and much more. SkyVisitor allows you to create your own custom reports and have these saved in the system. This means that you can get customised meaningful data out of your visitor system.
The integrated visitor photo badge system is quick and simple, badges can even be pre-printed for planned arrivals. They can be produced at any size on a host of printers: card, paper, thermal, re‐writable card or label.


Items issued to visitors – such as radios, keys, access cards and fobs – can be registered through SkyVisitor and onscreen alerts created when the visitor checks out.
The system is set up with a location hierarchy. This can be separate offices, different parts of sites etc. Having multiple locations allows you to report on activity at different offices for example. It also means that you can have different rules and workflows for visitors at each location.
If a visitor is pre-booked they can be sent a QR code before their arrival. When the visitor arrives at the site they can scan their QR code on a scanner at the check-in location and this instantly checks the visitor in. Doing this speeds up the check-in process and also means that it is a contactless check-in.
SkyVisitor has the ability to integrate directly with your access control system. You are able to define what locations visitors have access to via your visitor system, you can also see when a visitor has moved between areas at your site.












Traka is the leading solution for securing and tracking keys, trusted worldwide by many of the world’s biggest organizations across nearly every sector. Our proven and reliable key cabinets provide fast and convenient access to keys for the right people at the right time, with total control and centralized visibility.

Traka’s electronic key cabinets are an intelligent management solution that help secure, control and audit the use of every key.Only authorised staff are allowed access to the custom key cabinets and only then, to designated keys.Our highsecurity electronic key control solutions provide a full audit trail of who removed the key, when it was taken and when it was returned keeping your staff accountable at all times.
� Authorized users can quickly access the system via access card, fingerprint or PIN
� You determine who has access to which keys, and when
� An audit trail is recorded of every transaction for total accountability
� Set curfews to ensure that keys are returned on time
� Receive instant notifications of important events, such as an overdue item
� Dozens of customizable features allow the system to meet your unique access protocols.
� Robust key storage in secure, networked electronic cabinets
� Traka iFob ensures reliable record-keeping
� Web-based management and reporting platform saves time
� Auditable reporting and management reporting on key use
� Integrates with other access management solutions to provide an integrated access management solution.
� Our systems scale with your business needs.
Controlling access to your key inventory is important for the safety, security and efficiency of your business. Traka Touch Pro key cabinets provide efficient, automated access to keys while maintaining the strict security protocols that protect your operation, all with no adminitrative oversight required.





Key control solutions ranging from a simple, standalone system, to thousands of networked systems across the globe.
� Four key cabinet sizes (5-180 key positions) available for any application.
� Scalable and modular design allows the solution to grow with the needs of your business
� Centrally manage all key cabinets and equipment lockers from TrakaWEB, with regionalization for simplified administration
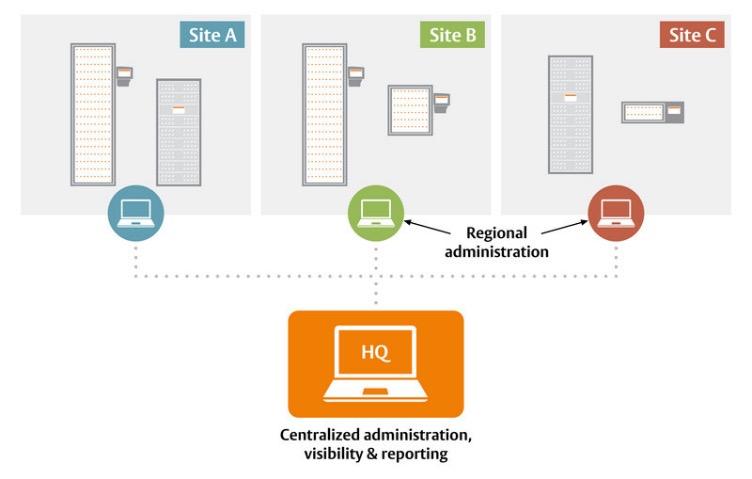


Traka Touch Pro L
Traka’s intelligent key management systems secure, manage and audit the use of every key in your business.
The Traka Touch Pro is our most secure and sustainable key management range to date.
The Touch Pro L electronic key management system is designed especially for larger organizations with a high key turnover. Accommodate up to 180 keys (360 using double-density strips) in one key cabinet, and up to 720 keys using extension units.
� Manage up to 180 sets of keys or 360 using double-density strips in one unit
� Manage up to 720 using extension units
� Secure and durable
� Modular and scalable


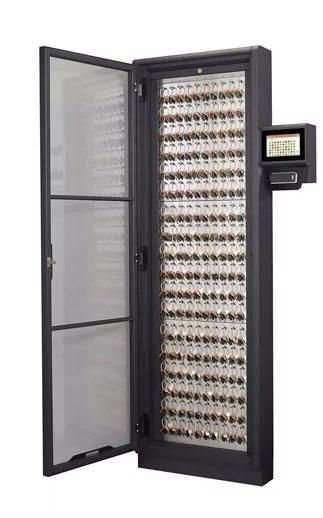


Traka’s electronic key management systems secure, manage and audit the use of every key in your business.
The Traka Touch Pro range is built to last, built for simplicity, built for flexibility, and built with sustainability in mind.
Traka Touch Pro M key cabinets can manage 20 keys (or 40 keys using doubledensity strips) and are ideal for organizations with smaller amounts of keys to




The Traka Touch Pro range of key cabinets is our most secure and sustainable to date.
Touch Pro S key cabinets are a versatile solution allowing for system scalability. Accommodate up to 60 key sets in this innovative key cabinet or 120 using doubledensity receptor strips. Or up to 480 keys using extension units.
� Manage up to 60 sets of keys (120 with double-density strips) in one unit
� Manage up to 480 using extension units
� Secure and durable
� Modular and scalable

Traka HC key cabinets are uniquely designed for the property management sector, which require strict control over a high volume of keys in a small footprint.




cost-effective, Traka21 helps trace and account for every key or keyset, which are individually locked in place, ensuring that critical business operations are never jeopardized.
Ensuring that the right keys are available to the right people at the right times is a concern for every organization. Traka21 is a sophisticated stand-alone key management system that combines innovative RFID technology and robust design to provide small and medium-sized businesses with our advanced key management products of 21 keys or keysets in an affordable plug and play unit.




A digital locking and access management system for changing needs
ABLOY PULSE is a unique digital locking and access management system that does not require batteries or cabling: The system gets its operating power when key is inserted to cylinder. An easyto-manage cyber-secure system offers a new kind of smoothness and security for offices and commercial buildings, educational institutions, healthcare and any small or medium-size locations where people and needs change frequently.



of ABLOY PULSE locking solution in a nutshell:
� Secure digital locking system for changing needs
� Covers the customer’s total need for locking
� One key principle
� Flexible electronic key and access management through a cloud service
� No cables, no batteries – generates its own energy
� Cost-efficient and energy-efficient through the whole lifecycle
� Upgradable investment for the future
� Reusable, sustainable choice – protects also nature
� Possible to update the system countless times
� Knowledge increases security – up-to-date information on access rights
� Easy to start to use
� Unique finished design & care-free locking experience
� Quick, cost-effective installation .
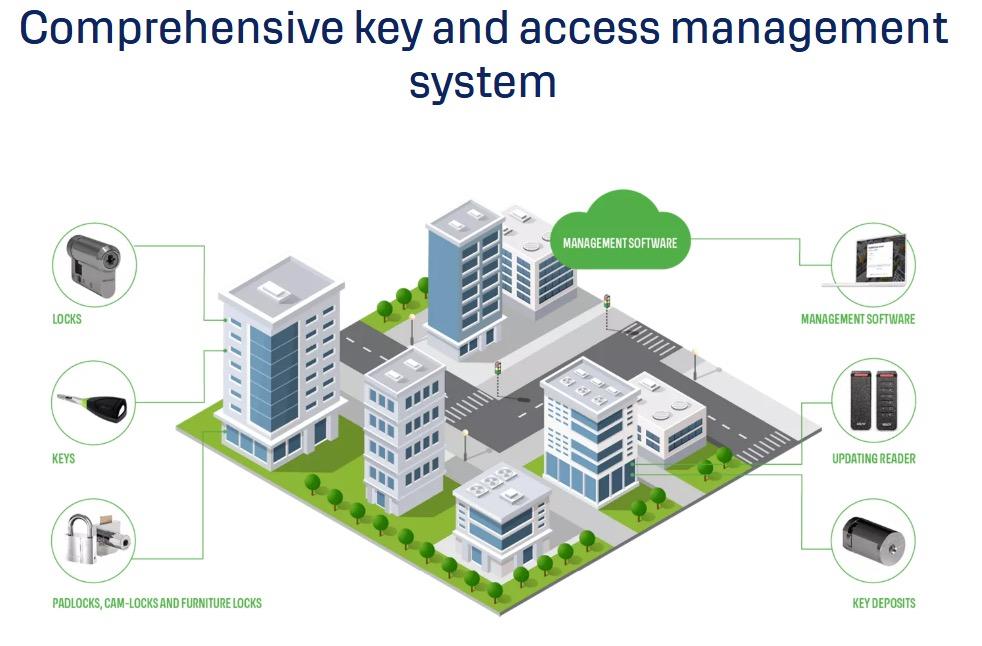



Aperio is a technology developed by Assa Abloy to complement the use of traditional electronic access control systems, by providing end users with a simple, intelligent way to enhance the controllability and security of their premises. This is achieved without the disruption and costs associated with dedicated direct cabling and provision of power to every door.
An Aperio Wireless Lockset or Cylinder is designed to serve as a combined cardreader and locking device, as well as providing a real-time link to the on- line processor unit. As each card is read, ‘Aperio Gateway Controllers’ distributed around the site make all of the access decisions, with all access configuration and history managed by your access control software.










The hub is a bespoke cloud-based platform that supports security personnel on-site.
The Hub comprises various key applications including the Daily Occurrence Book, Incident Management, Hub Patrol, Document Manager and Site Visit Assessments.
The Hub constantly updates to keep up with modern security trends supporting on-site teams.


The Hub Patrol is a real-time patrol solution which allows fast, secure, and efficient access to patrol data. Anywhere that there is a need to prove and ensure the physical attendance of a person at a specific location, the Hub Patrol is the ideal solution for the following key reasons:
� It will give you an audit trail to prove the location and activity of your staff and assets.
� It is simple for the end user with minimal set-up time
� It offers proof of attendance in realtime, with alerts being supplied if there are non-attendance risks.
� Managers and staff can exchange actions and messages via mobile phone.
The Hub Patrol dashboard gives the Controller access to view live patrols and can communicate with the Patrol Office.


The system highlights which patrols are still ongoing so that they can be monitored.
The Manager can get time-sensitive information from the dashboard and can search for a specific time period if required.
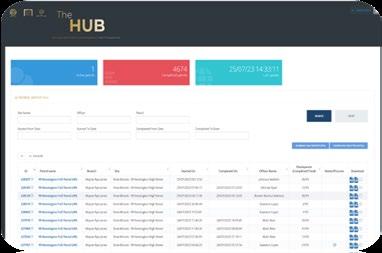
The Patrol Report includes the Patrol Officer’s name for audit purposes.
The system records the GPS location of the device whenever it hits a point and when you click on the position this opens up Google Maps and display the location.
The system requires users to hit the start and finish NFC points. The system has the ability to make the Officers conducting patrols follow the same route through the force sequence feature.
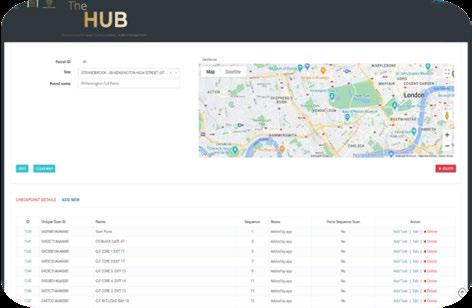
Patrols conducted can be exported in PDF format.
The system has an automated mailing feature which can be set up to send customers patrol reports either as the patrol is completed, on a daily, weekly, or monthly basis.
Customers can have access to the system to view the patrol, daily occurrence, incident reporting and site visits..

The end user can add notes and pictures which will appear on the report.


Kinexio Proof of Presence


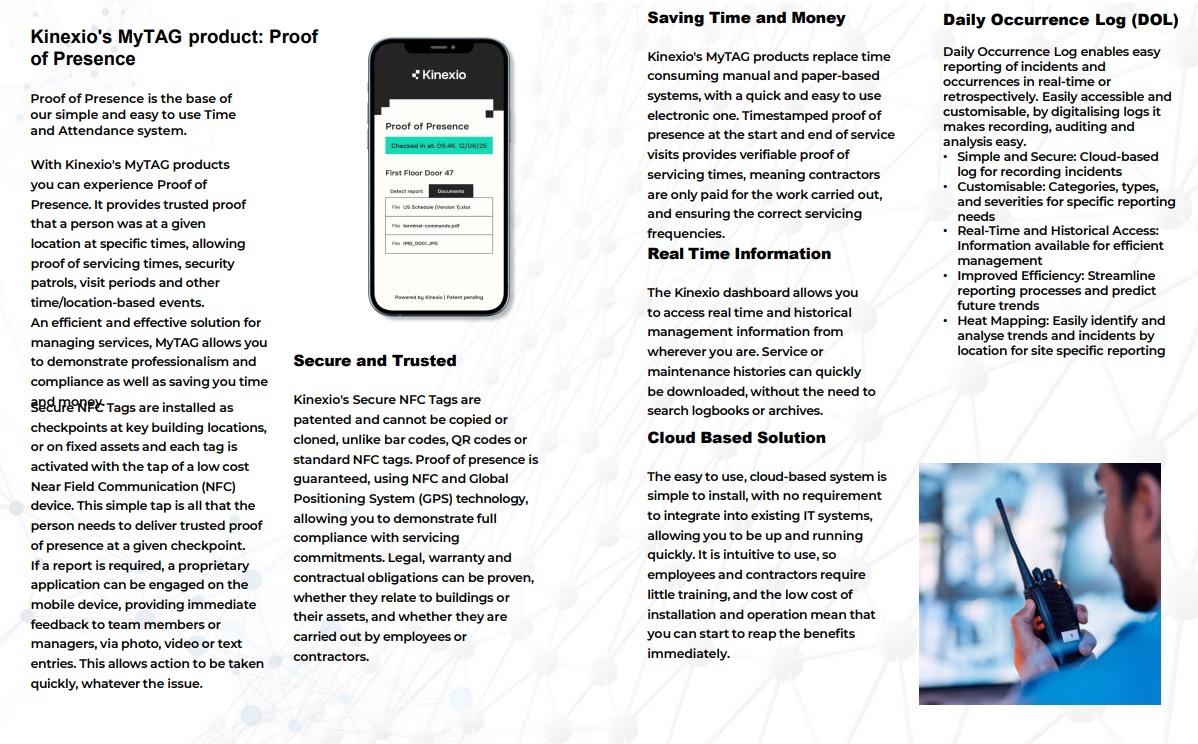

MyTAG Secure NFC Tags are patented and cannot be copied or cloned, unlike bar codes, QR codes or standard NFC tags. Proof of presence is guaranteed, using NFC and Global Positioning System (GPS) technology, allowing you to demonstrate full compliance with servicing commitments. Legal, warranty and contractual obligations can be proven, whether they relate to buildings or their assets, and whether they are carried out by employees or contractors.
MyTAG replaces time consuming manual and paper-based systems, with a quick and easy to use electronic one. Timestamped proof of presence at the start and end of service visits provides verifiable proof of servicing times, meaning contractors are only paid for the work carried out, and ensuring the correct servicing frequencies.
The MyTAG dashboard allows you to access real time and historical management information from wherever you are. Service or maintenance histories can quickly be downloaded, without the need to search logbooks or archives. This allows a quick response to any queries or issues and provides an instant overview of current activities.




The easy to use, cloud-based system is simple to install, with no requirement to integrate into existing IT systems, allowing you to be up and running quickly. It is intuitive to use, so employees and contractors require little training, and the low cost of installation and operation mean that you can start to reap the benefits immediately.
MyTAG Proof of Presence is the base of our simple and easy to use Time and Attendance system. Ideal for part-time and temporary employees, everyone is assigned an individual tag, which is scanned when they start and end their shift. An accurate record of hours worked can be automatically inputted into the payroll system, or transferred to Excel if required, supporting efficient contractor management.
MyTAG Proof of Presence can be used to prove delivery of any facilities services against agreed SLAs and KPIs. With the critical importance of cleaning during the Coronavirus pandemic, it provides evidence that crucial tasks, such as high touch point and washroom cleaning, have been completed according to the schedule.







CIS Innovative Solutions have teamed up with MyTAG and Mallcom to launch a smart building App.

The App will be aimed at facilities management and occupiers. Incorporated within the App will be broadcast messaging system, post room/deliveries, visitor management, local restaurant offers, news and travel.
The App will be a communication tool for all building users and can be tailored and branded specifically per building.





Base plate consisting of 2No. central sliding and 2No. fixed bollards. Opening aperture – 3991mm
Classification: IWA 14-1: 2013 Bollard V/7200[N2A]/64/90:0.1
Manual version (where you would physically push the 2No. central sliding bollards to the side)


To supply and install Terror Stopper 1 PAS 68 Static Bollard - 219mm diameter bollard 7.5 tonne vehicle at 30 mph. PAS68:2010 rating of V7500(N2)48/90/0.0/0.0




Comes complete with Core Bollards, Socket, standard oval stainless-steel shroud, and rebar. (200mm Foundation/40mph Solution)





Comes complete with Core Bollards, Socket, standard oval stainless-steel shroud, and rebar. (200mm Foundation/40mph Solution)
� Auto Arm Barrier – 30mph Impact Tested Barrier Equipment (PAS 68:2010 V/ [N2]7500/48/90:2.4/7.9)
� 4 metre clear opening, Model 942 Impact Tested heavy duty, Electrohydraulic traffic control barrier: 230v single phase or 400-volt three phase supply with an operating speed of approximately 15 seconds per raise or lower for a 5-metre boom (QTY 1)
� Fixed-end support structure to receive barrier boom when in the lowered position (QTY 1) OR 6 metre clear opening, Model 942 Impact Tested heavy duty, Electro-hydraulic traffic control barrier: 230v single phase or 400-volt three phase supply with an operating speed of approximately 15 seconds per raise or lower for a 5-metre boom. (QTY 1)
� Fixed-end support structure to receive barrier boom when in the lowered position (QTY 1) Control Equipment
� Dual aspect Red/Green traffic light and mounting post. (QTY 2)
� HGV height control reader posts to mount intercom equipment. (QTY 2)
� Vandal resistant intercom system comprising: 2 controls to 1 receiver units, suitable for external use. (QTY 2)
� Housing mounted “test/access isolate” key switch, control unit. (QTY 1)
� Safety Equipment Safety induction loop vehicle detection system. (QTY 1)
� Photocell safety system (QTY 2)
� BAE sensor, presence detection system. (QTY 2)

The operation of automatic rising arm traffic barriers can create a hazard to persons or vehicles in the vicinity of the barrier. The above Safety equipment is included to negate some, or all this hazard Additional Safety equipment may be available, please check with us for details. Control of the barrier will be as follows: Entry will be affected by: - Intercom and push button provided by Safetyflex. Exit will be affected by: - Exit vehicle detection loop provided by Safetyflex. Please note that our proposal is subject to site survey to confirm barrier length required to secure intended location.
� Generic drawings (up to revision c) showing suggested equipment layouts and incorporating standard “as tested” civil works and local cable ducting requirements. Where there is a requirement to validate foundation details in respect of transition between adjacent equipment, or local ground conditions, Heras can recommend a suitably qualified structural / civil engineer to undertake this work at additional cost.
� Delivery to site using a HIAB vehicle consisting of two consignments for separate delivery of stanchions and the remainder of barrier equipment -Commissioning of the equipment shown in Section 1.
We can supply a Shallow Mount Viper Roadblocker crash tested to 7.5 tonnes @ 80kph
Barriers are 3.0 metre, so you would need 2No. for the larger openings.




Another option is to have a mixture of fixed and automated raised bollards.
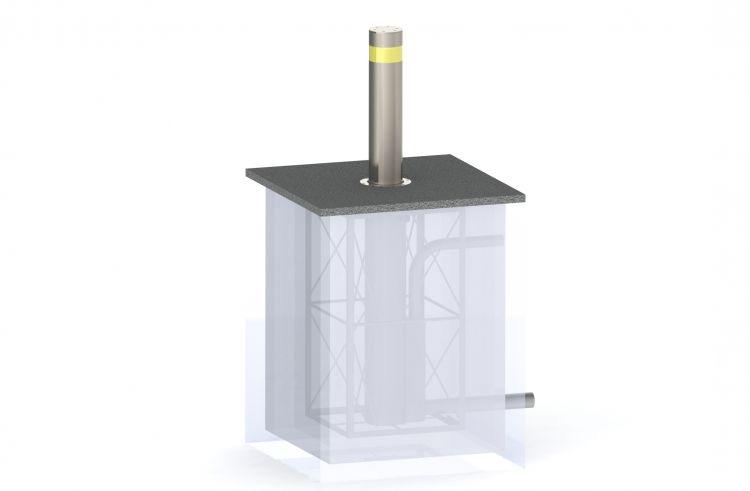




Tested to the limits and bearing the PAS 68: 2010 standard, our security planters are in place outside banks, local authority buildings and railway stations across the country, ready to mount an effective defence against any vehicle used as a battering ram.
Their appeal is that while they are capable stopping and disabling a 7.5 tonne truck travelling at 64kmh, the planters are aesthetically pleasing and can be used to mount an attractive floral display to bring a touch of nature’s colour to the concrete jungle.
They are available in three different sizes and range of finishes, including stainless steel and bronze patina, the security planters can be installed quickly and, at 100mm, have the shallowest fixings in the industry, so there’s no danger of disturbing underground facilities.
� Identical to standard planters
� Available in 3 sizes and in a range of colours
� Surface mounted
� Enhances the landscape as well as providing protection
� Easily and quickly installed by our trained fitters.












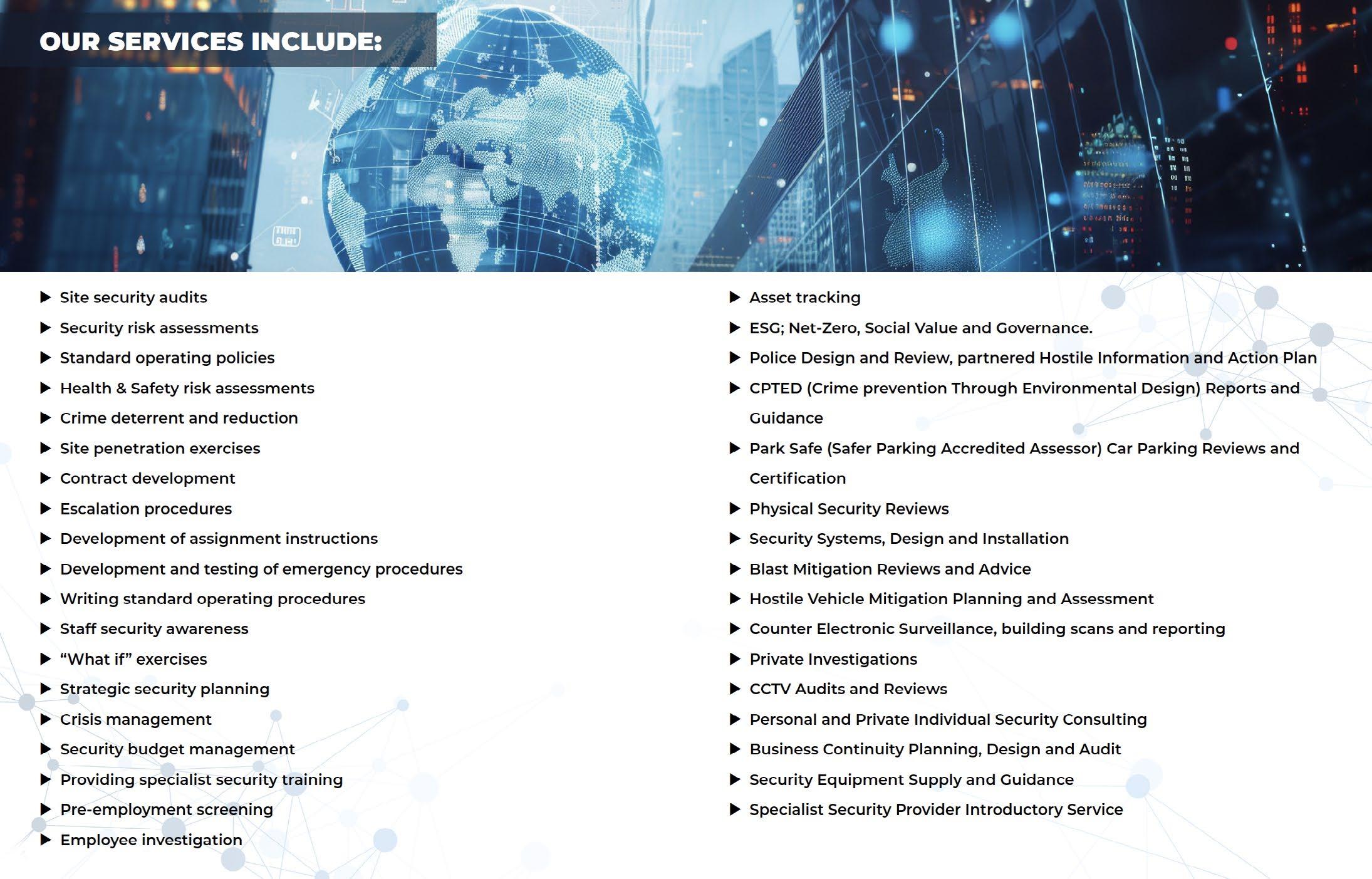






















Precision. Awareness. Total Operational Control.
Our Security Control Room solutions are built to deliver uninterrupted visibility, rapid incident response, and flawless coordination across your entire security ecosystem. Designed for mission-critical environments, every element—from operator ergonomics to technology integration—is crafted to elevate awareness and streamline operations.

Comfort-driven productivity for 24/7 performance.
� Ergonomic consoles with adjustable height and optimized reach
� Multi-display configurations for seamless visual flow
� Anti-glare lighting and acoustically treated interiors
� Clean, efficient cable and power management.


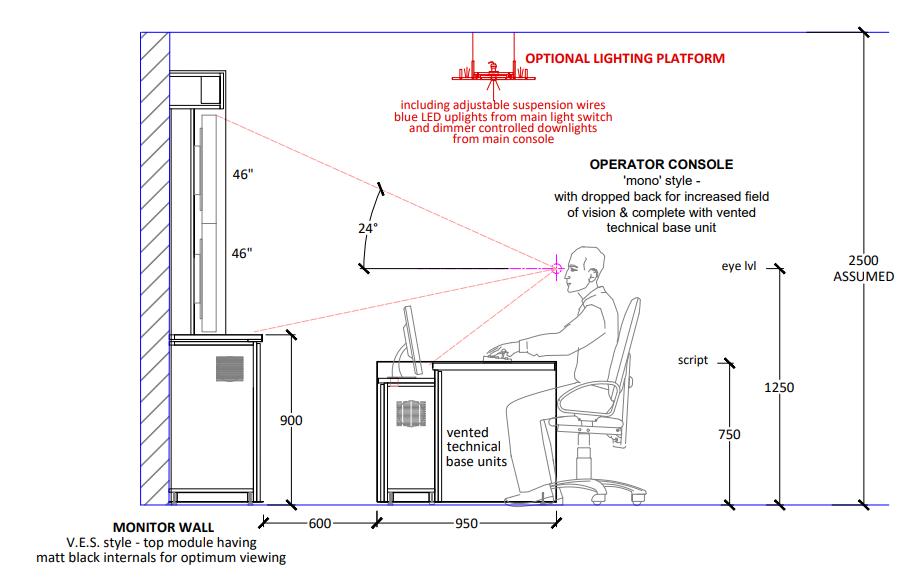


Your team stays alert, focused, and empowered during every shift.

Total situational awareness at a glance
� High-resolution video walls
� Unified dashboards for CCTV, access control, alarms, and analytics
� Intelligent overlays for event tagging and data interpretation
� Instant switching between live feeds, incident views, and system health
Keep eyes on what matters most—with clarity and control.

Engineered for reliability, scalability, and seamless connectivity
� • High-bandwidth networking and secure backbone architecture
� • Redundant power, cooling, and server systems
� • Unified integration with surveillance, access, and perimeter devices
� • Expandable layouts to support future technologies and growth
A robust foundation that supports today’s demands and tomorrow’s innovations.



Faster decisions. Smarter coordination. Stronger outcomes.
� Automated alerts and prioritized event queues
� Streamlined communication with field teams
� Customizable SOP workflows and incident management tools
� Secure, documented reporting for full traceability
Turn information into decisive action—instantly and confidently.


Tailored layouts. Modular components. Brand-aligned design.
We design each control room around your operational needs, architectural constraints, and brand identity. From finishes and lighting tones to console configuration and equipment placement, every detail reflects your environment and enhances operator performance.
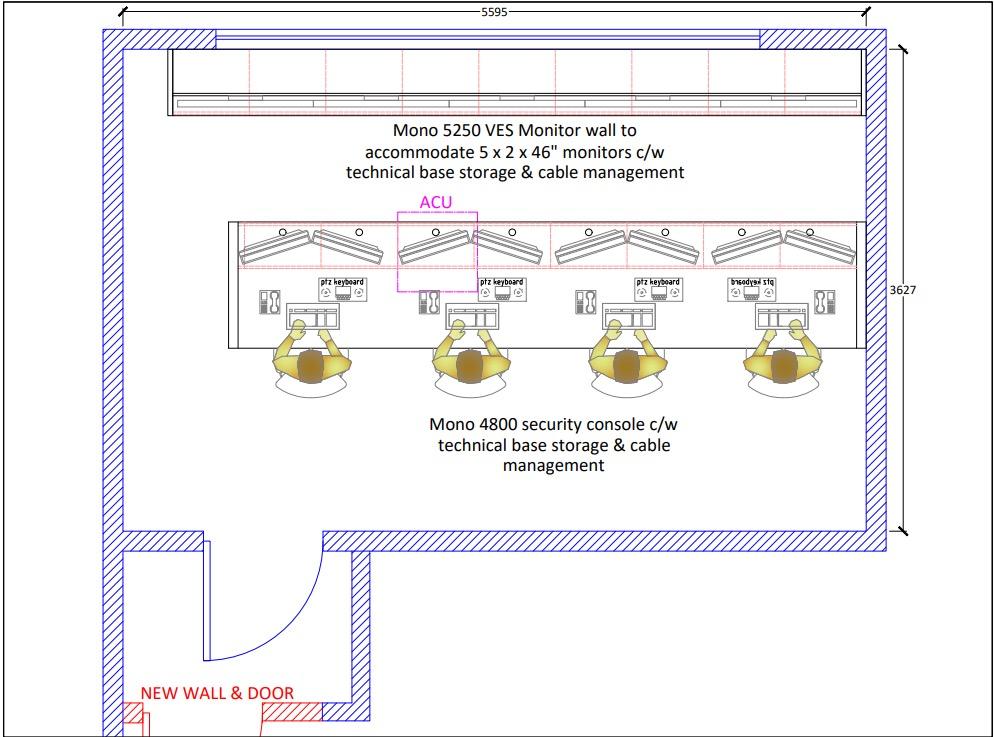





Our Security Control Room solutions bring together design, technology, and workflow intelligence to create an operational hub that empowers your team and strengthens your entire security infrastructure.






Parking Management systems have become a crucial part of the parking process for both parking operators and users with the emergence of parking technologies. Nowadays, parking management without a systematic system is complex and, in some cases, even impossible. Parking management systems provide convenience and flexibility when controlling the flow of vehicles in a parking area. With a CIS Innovative Solutions management system, you can enjoy various parking facilities and ensure outstanding results. Investing in a good parking solution is necessary to manage your car park effortlessly. Our expertise will assist you in understanding why you need an efficient parking management system and how it can benefit you.
As we navigate the benefits of parking management systems, it’s evident how crucial they’ve become in today’s car park landscape. These systems make the parking process efficient and add value in ways we might not always recognise at first glance. Let’s explore these benefits in detail:
Parking management systems are known for their integration with technology. Most of these systems are based on improved models and technological innovations so that they can be used in various car parks. Moreover, you can customise the smart system based on the needs and requirements of your car park, whether for residential or commercial use.
Better car park management means happier customers. A parking management system enhances the customer journey by providing a unified procedure. An efficient parking management system enables users to find empty parking spaces, saving time and fuel and improving customer satisfaction.


Parking management systems have advanced security features like ANPR technology to enable you to prevent parking misuse and suspicious activity in your parking facility. Parking management systems provide upgraded security, safety and privacy so car owners can rest assured that their cars are well-protected.
Vehicles circling an area searching for an empty parking space cause most city traffic. Moreover, significantly driving around or waiting for a parking space to be vacant burns through a lot of fuel and releases emissions daily. An optimal parking management system opens the option of quicker parking that significantly reduces city traffic, driving time, vehicle emissions, and carbon footprint.
Another benefit of a parking management system is that it can be designed and implemented efficiently. These systems have a well-organised structure; you can easily manage, control, and regulate them. CIS Innovative car parking management systems are also user-friendly, so the parking staff won’t have any difficulties handling the system, thus improving the whole car park management process.





Another advantage of installing a CIS Innovative Solutions parking management system is the cost. It runs on a low workforce so that you can save money and time. Another great feature of a parking management system is controlling the car park/ streetlights and other services that require electricity.
You can set all electrical devices to shut automatically at a particular time every day or remotely switch them on/off depending on the car park usage level. The potential options are limitless.


Parking management solutions use software and applications that can be combined. Depending on your car park’s requirements, many customisation options are available. Whatever your requirement is, an effective parking management system will accommodate this and make the parking experience more convenient.
Implementing the correct parking management system saves costs, time and energy. With the increasing need for parking, upgrading to a well-organised parking space is crucial. At CIS Innovative Solutions, we aim to make your car as precisely as you want. Our parking management system guarantees that your parking facility will work far more efficiently.




In short, parking management systems give smart and easy solutions for today’s car park challenges. Using tech, they make parking smoother and better, helping with convenience and safety and looking after the environment. Making parking methods better saves time and money for everyone. There are many good things about parking management systems for car park owners and those who use them. Owners get things done more efficiently, while people parking find it simple and stress-free. These ways of working lead the way in making parking less of a headache, cutting down on pollution, and making our city spaces last longer.
Kuldeep Kainth Director of Innovative

The information found within the CIS Innovative Solutions Catalouge are an illustrative portfolio of the services and products we offer. Tailored solutions and custom engineering are available to mitigate all risks through in-depth site surveys.
Please contact the team using the details below if you would like to book a site survey or require further product information.








