Interview:
Carlos Garcia, ASSA ABLOY

Markets:
How the Gulf Security Market Is Adapting Under Pressure
Interview:
Carlos Garcia, ASSA ABLOY

Markets:
How the Gulf Security Market Is Adapting Under Pressure











Walk into any house of worship in the Middle East, and the acoustic challenge is immediate. Domed interiors and marble prayer halls were built for awe, not intelligibility. The best PAVA deployments operate invisibly, delivering clarity under normal conditions and reliability when it matters most
16 Carlos Garcia, Sales Director, ASSA ABLOY Opening Solutions Middle East Wireless Access Moves from Alternative to Mainstream Across Sectors MARKETS
22 Navigating Stability How the Gulf Security Market Is Adapting Under Pressure
28 Stability Under Pressure Logistics as the Decisive Pillar of Oil & Gas Security
PRODUCTS & SYSTEMS
42 Building Management Systems BMS as the Intelligence Layer Shaping Quality of Life and Investment
48 Short-Circuit Proof According to Current Standard Worst Case in Grey Space
52 SecurOS Video Intelligence Platform
ISS Tech Transforms Port Security and Operations Across the Middle East
54 No More Manual Scanning How Modern Search Technology Is Changing Video Investigations
56 A Changing Nature of Access Control What the Mobile Credential Adoption Curve Really Demands From the Channel
58 Wireless intrusion detection and the economics of remote security Understanding the TCO When Securing Remote and Temporary Sites
60 Effective solutions driven by collaboration The Changing Landscape of Physical Security in the Middle East
62 XPass Q2 Unveiled Intelligent QR Reader for Enterprise, Commercial, and High-Traffic Environments
PRODUCTS & SYSTEMS
64 Execution Gap Compliant on Paper, Compromised in Reality
66 Infrastructure Under Pressure The Importance of Surveillance Infrastructure in Uncertain Times
68 Data Centers
From the Perimeter to the Rack: The Future of Physical Security
70 NBOX1 Facility
Secure Data Center Supports East Africa’s Digital Growth
50 AI-Driven Multi-Energy X-Ray Inspection Technology Changing the Logic of Cargo Inspection EVENTS
72 Intersec Dubai 2026 New Standards in Global Security
74 SECON & eGISEC 2026 Korea’s Blueprint for Trust in the Age of AI
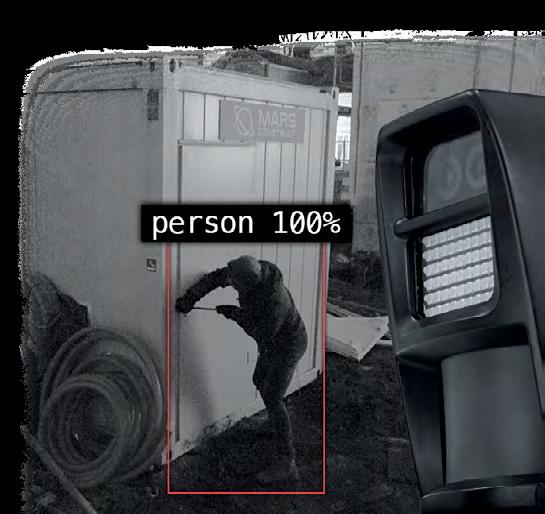
Redefine security for temporary or hard-to-secure sites with a fully wireless AI-verified intrusion detection system.
Meet us at

Dubai World Trade Centre, 12-14 January
Hall S1, Booth B42
Professional media for complete security solutions
Management
Mahir Hodžić, General Manager mahir.hodzic@asmideast.com
Adis Hodžić, CEO adis.hodzic@asmideast.com
Editorial Staff
Damir Muharemović, Editor-in-Chief mahir.hodzic@asmideast.com
Mirza Bahić, Associate Editor mirza.bahic@asmideast.com
Dženana Bulbul, Assistant Editor editorial@asmideast.com
Orhan Hadžagić, Journalist orhan.hadzagic@asmideast.com
Fatima Al Husseiny, Journalist fatima.alhusseiny@asmideast.com
Roman Ivanković, Journalist roman.ivankovic@asmideast.com
Art Staff
Sanel Palislamović, Art&Design Editor sanel.palislamovic@asmideast.com
Nelmedin Kolubara, DTP&Art Design dino.kolubara@asmideast.com
Sales Amar Pap, Business Development Manager amar.pap@asmideast.com
Internatonal Sales
Qatar: Mirsad Selimović, mirsad@techman.qa Southeast Asia: as-pr@taiwan.messefrankfurt.com
a&s Middle East offers the latest news and insights on video surveillance, access control, intrusion detection, fire alarm, perimeter protection, PA/VA, man guarding, cyber security, smart homes and buildings, industrial automation, information, communication technology, automation, and ICT to the Middle East region professional channel players.
a&s Middle East is part of the media network of the Messe Frankfurt Ltd – Taiwan Branch, which offers several media platforms — asmag.com and a&s magazines, published in English, traditional Chinese, and three other languages, providing the most comprehensive industry trends, product, and supply chain information. The total annual circulation is approximately 120,000 copies around the globe. a&s Middle East is published 6 times a year, Jan/Feb, March/ April, May/June, July/August, Sept/Oct, and Nov/Dec.
Payment Instructions
Annual subscriptions are payable in USD, EUR, or AED. Subscription inquiries per your request.
EUR: AE340400000653005131002
Account No. 0653005131002
USD: AE070400000653005131003
Account No. 0653005131003
AED: AE610400000653005131001
Account No. 0653005131001
Copyright Statement
© Copyright by Privus Agency Ltd. All rights reserved. Any republication, copying, redistribution, or reproduction of the magazine in any form, including electronic, without the prior written consent of the publisher, is prohibited. Advertisers are solely responsible for the content of advertising material. The publisher bears no responsibility regarding possible legal, patent, content, or brand disputes of the advertiser.
Legal Disclaimer
The information in this magazine has not undergone any formal testing by Privus Agency Ltd. and is distributed without any warranty expressed or implied. Implementation or use of any information contained herein is the reader’s sole responsibility. While this information has been reviewed for accuracy, there is no guarantee that the same or similar results may be achieved in all environments.
Corporate Address
Privus Agency FZ-LLC
JT010006, Al Shohada Road, Ras Al Khaimah, UAE
Tel: +971 58 983 4258
Web: www.asmideast.com
Welcome to a new edition of a&s Middle East, where we focus on a shift redefining how security is understood and deployed across the region: from a protective layer to an operational system.
Our cover story examines how the Gulf security market is responding to ongoing uncertainty not with reactive procurement, but with measured, strategic investment. Despite the broader security challenges affecting parts of the region, including the impact of conflict, the market continues to demonstrate a notable degree of resilience. Investment patterns suggest not hesitation, but recalibration, with stakeholders prioritizing solutions that deliver long-term operational stability rather than short-term fixes. Integrated platforms, AI-driven analytics, and unified command environments are no longer optional upgrades, but core requirements for maintaining continuity, visibility, and control.
This same logic extends into our feature on PAVA systems in houses of worship, where performance is defined not only by reliability, but by precision and restraint. In acoustically complex and culturally sensitive environments, systems must deliver clarity, resilience, and compliance, while remaining effectively invisible. Here, too, the emphasis is on systems that function consistently under pressure, without disrupting the experience they are meant to protect.
Across both segments, the message is consistent. Security today is not built around standalone technologies, but around systems that integrate, adapt, and operate without interruption. The ability to absorb disruption and continue functioning as intended is becoming a defining benchmark of system design.
As the region continues to evolve, success will depend not only on how well these systems align with real operational needs, but also on their capacity to maintain performance in the face of ongoing uncertainty.
Marketing: marketing@asmideast.com WANT TO RECEIVE THE MAGAZINE AT YOUR DOORSTEP?
Please visit our official website www.asmideast.com and select ‘Subscribe Now’ option under THE MAGAZINE menu.
Subscription includes all six editions.
Digital edition is FREE and readily available at the official website.
Create optimized environments with Automated Logic. Our innovative building-management solutions bring all building systems together into one cohesive ecosystem maximizing energy efficiency and sustainable building operation while ensuring comfort. We make it easy to manage your building from anywhere. automatedlogic.com





















The conflict involving the US, Israel, and Iran has tested how well Gulf states can protect critical infrastructure, maintain continuity, and absorb hybrid threats, with the UAE showing why cyber resilience, integrated security, and counterdrone readiness are becoming central to regional security investment.
The war has raised the security temperature across the Gulf, forcing states to treat regional escalation not as distant geopolitics but as a direct operational challenge. For the physical security industry, the most important lesson is that resilience now matters as much as prevention. Airports, ports, logistics corridors, utilities, and oil and gas assets all sit within a threat environment shaped by drones, missile risks, electronic interference, and cyber disruption.
In the UAE, the response has highlighted the value of layered protection around critical infrastructure rather than reliance on any single visible security measure. For the industry, that means renewed relevance for integrated command platforms, advanced video surveillance, perimeter detection, access control, intrusion monitoring, and rapid
incident coordination. The regional security climate is also likely to strengthen demand for counter-drone systems, especially for sites where continuity is as important as physical protection.
The cyber dimension has been equally explicit. The UAE Cyber Security Council said the national cyber system had thwarted organized attacks targeting digital infrastructure and vital sectors. According to Reuters and WAM, the activity included attempted network infiltration, ransomware deployment, and systematic phishing campaigns against strategic platforms, with officials also warning that AI was being used in offensive cyber tools. The council later conducted a crisis simulation exercise focused on disruptive attacks against shared government services and critical infrastructure, showing that cyber readiness is now being treated as a core part of national resilience.
This matters directly to the physical security market because modern security operations no longer end with cameras, guards, and gates. Surveillance networks, control rooms, visitor management, building systems, and emergency
response workflows all depend on secure digital backbones. If those backbones are targeted, physical protection can degrade quickly unless systems are designed for continuity, interoperability, and fast recovery.
Another important pressure point has been electronic interference. Reports from the Gulf have already highlighted the risks of GPS jamming and spoofing. This concern reaches beyond aviation into fleet tracking, drone operations, smart-city infrastructure, and synchronized security networks. For security vendors and integrators, this widens the market conversation from site protection to assured operations in disrupted environments.
Overall, the UAE appears to have shown a relatively high level of resilience. Authorities communicated centrally, maintained service continuity, and treated physical and cyber threats as part of the same security equation. For Gulf security buyers, the message is clear: the next wave of investment will favor systems that are interoperable, crisis-ready, and capable of sustaining operations when regional conflict spills into daily life. n


Makkah is accelerating the adoption of smart technologies and digital applications to enhance urban services, improve mobility, and strengthen safety for millions of residents and pilgrims visiting the holy city each year. Makkah is undergoing a major transformation driven by the deployment of advanced digital platforms and smart technologies aimed at improving services, operational efficiency, and visitor experience across the city. According to a report by the Saudi Press Agency, the initiatives are part of broader efforts to modernize infrastructure and support the Kingdom’s digital transformation strategy. Authorities are increasingly integrating intelligent systems into transportation, municipal services, and public safety operations, enabling faster response times and more efficient management of large crowds, particularly during the Hajj and Umrah seasons. Smart solutions also help optimize traffic flows, improve environmental monitoring, and enhance communication between authorities and the public. Digital platforms and mobile applications are playing a key role in facilitating ser-

vices for residents and visitors, providing real-time information and simplifying access to government services. The expansion of these technologies is expected to further strengthen Makkah’s ability to manage the large number of pilgrims who travel to the holy city each year.
The smart transformation aligns with Saudi Arabia’s Vision 2030 agenda, which emphasizes innovation, digital infrastructure, and the use of emerging technologies to enhance the quality of life and support sustainable urban development across the Kingdom. n
Saudi Arabia is emerging as a global hub for data and artificial intelligence under Vision 2030, driven by the support of His Royal Highness Prince Mohammed bin Salman bin Abdulaziz Al Saud, Crown Prince, Prime Minister, and Chairman of
of Artificial Intelligence in the Kingdom. Since its establishment in 2019, SDAIA has led the National Strategy for Data and Artificial Intelligence, which focuses on six pillars: ambition, competencies, policies, investment, innovation, and ecosystem.

the Saudi Data and Artificial Intelligence Authority (SDAIA). The momentum was underscored by the Cabinet’s approval today to designate 2026 as the Year
These efforts have moved the Kingdom from strategic planning to implementation, including regulating AI sectors and developing advanced digital infrastructure.
Saudi Arabia’s progress is reflected in global rankings. The Kingdom ranked 14th in the 2025 Global AI Index and holds a leading position in the Arab world for AI model development. Investment in the sector has grown significantly, with government spending on emerging technologies rising by more than 56% in 2024 and AI companies securing $9.1 billion in funding.
Infrastructure has expanded with the launch of the Shaheen III supercomputer and the Hexagon data center, the world’s largest government data facility with a capacity of 480 megawatts. The Kingdom has also established a National Data Lake integrating more than 430 government systems.
Human capital development remains a priority. More than 11,000 specialists have been trained, and the SAMAI program has reached over one million participants. n










Saudi Arabia’s National Cybersecurity Authority (NCA) has launched a public consultation on a proposed “Regulatory Framework for Licensing Cybersecurity Services, Products, and Solutions”, a move that could reshape how cybersecurity offerings are delivered, marketed, and assessed in the Kingdom.
The consultation signals stronger governance over the cybersecurity supply chain, potentially affecting service providers, product vendors, integrators, and consultancies operating in or targeting the Saudi market. Licensing requirements can also influence procurement decisions for end users by clarifying eligibility, accountability, and assurance expectations across different categories of cyber offerings.
For organizations building or expanding operations in Saudi Arabia, the proposed framework is likely to become a practical checkpoint for vendor selection, contracting, and compliance planning, particularly for services tied

to risk assessments, security operations, managed services, and the deliv-

ery of security products into sensitive environments. n
New findings from Genetec’s 2026 State of Physical Security Report suggest Saudi organizations are outpacing the wider EMEA market in cloud adoption, security spending, and modernization of physical security infrastructure.
Saudi Arabia is emerging as one of the most dynamic physical security markets in the EMEA region, according to Genetec’s newly released country findings from its 2026 State of Physical Security Report. Based on insights from more than 150 physical security professionals in the Kingdom, the report points to strong momentum in cloud adoption, higher security invest ment, and fewer legacy infrastructure constraints than in many neighboring markets.
One of the report’s clearest findings is Saudi Arabia’s lead in cloud-based physi cal security deployment. Genetec said 13 percent of respondents in Saudi

Arabia are already using cloud security systems, compared with an EMEA average of seven percent. The result reflects a growing preference for more flexible and scalable architectures that can support resilience, easier management, and long-term modernization goals.
Budget trends were also notably strong. Saudi Arabia recorded the highest level of operating expenditure growth among the EMEA markets surveyed, with 43 percent of respondents reporting increased physical security budgets in 2025. That is well above the regional average of 24 percent. Among those seeing budget growth, 92 percent said spending rose by more than 10 percent, while nearly two-thirds reported increases in the 11 to 25 percent range. n












































































































































































































































































































































































The Middle East and Africa cybersecurity market is projected to grow from $25.02 billion in 2025 to $39.98 billion by 2030, at a compound annual growth rate of 9.8%, according to MarketsandMarkets.
The forecast points to continued momentum in regional security spending as governments, enterprises and critical infrastructure operators respond to a widening threat landscape and deeper digital transformation across the region. MarketsandMarkets attributes the growth primarily to the rapid expansion of digital infrastructure and the region’s rising exposure to cyber risk. As more services, transactions and industrial processes move online, organizations are being pushed to strengthen defenses across cloud, application and network environments while also improving compliance and resilience.
The report segments the market across solutions such as identity and access management, firewalls, log management and SIEM, as well as professional and managed services. That structure reflects how cybersecurity investment in the

region is increasingly shifting from point products toward broader, service-led security strategies that combine technology deployment with consulting, monitoring and threat management support. The final sentence is an inference based on the report’s segmentation and service mix.
For the Middle East in particular, the outlook aligns with national digital agendas and modernization programs that con-
tinue to expand the attack surface across government, finance, energy, transport and smart infrastructure. As spending rises, the market is likely to create further opportunities for vendors and service providers focused on cloud security, identity protection and managed detection capabilities. This final sentence is also an inference grounded in the MarketsandMarkets forecast and category breakdown. n

Suprema is expanding its non-biometric access control portfolio with XPass Q2, a new intelligent reader that integrates multiple credential technologies into a single device. According to the company, the product supports QR codes, barcodes, RFID cards, and mobile credentials, positioning it as a flexible option for organizations that
need to manage both everyday access and visitor or ticket-based entry from a single platform. The launch reflects a growing demand for access solutions that can process users quickly without forcing operators to rely on separate systems for staff, visitors and event attendees. Suprema said XPass Q2 was developed for two
main scenarios: accelerating entry at high-traffic facilities where visitors authenticate via QR codes, and enabling fast ticket verification at venues such as events, stadiums and public facilities. In both cases, the focus is on reducing congestion and improving throughput at entry points.
For the security channel, that makes XPass Q2 relevant beyond traditional office access control. The product appears suited to a wider range of environments where convenience, temporary access and rapid authentication are becoming more important, including commercial buildings, leisure venues, transport-related facilities and public-facing sites. Its compact form factor and rugged design also suggest Suprema is aiming at deployments where space is limited, but reliability remains essential. n
Dubai and Abu Dhabi have emerged as the highest-ranked cities in the Middle East and North Africa in the IMD Smart City Index 2026, taking sixth and 10th place globally, respectively, out of 148 cities assessed. The index, published by IMD’s World Competitiveness Center, measures how residents experience urban technology, infrastructure, governance and quality of life, and relies heavily on survey feedback rather than on technology deployment alone.
The UAE’s performance stands out not only because both cities made the global top 10, but also because they are the only MENA cities to do so. Dubai and Abu Dhabi were each rated A across both the report’s Structures and Technology pillars, underscoring the extent to which digital services, public trust and institutional capacity are now reinforcing one another in the country’s smart-city model.

Saudi Arabia, however, delivered the broadest regional showing. Riyadh climbed to 24th globally, while Hail entered the ranking at 33rd and became one of the region’s strongest first-time performers. Makkah ranked 50th, Al Khobar 64th, Madinah 67th,
Jeddah 55 th, AlUla 85th and Hafr AlBatin 100th. AlUla posted one of the sharpest gains in the wider region, rising from 112th to 85th, which points to the impact of sustained investment in urban development and tourism infrastructure. n
Zenitel has presented a new maritime communications deployment for two 4,000-TEU container vessels being built for Turkon Line at Sedef Shipyard in Turkey, highlighting the growing role of integrated onboard communication platforms in operational safety and vessel coordination. The company said the vessels are
intended for liner services connecting Turkey, the Red Sea, and India.
According to Zenitel, the project includes a full onboard communication package designed to support both routine operations and safety-critical functions. The delivered scope includes the SPA V2 PAGA system, CIS TalkBack, Master Clock System, LAN

Distribution Network, ICS 6200 Integrated Telephone, Batteryless Telephone and Sound Signal Reception.
The company said such systems are essential for communication between the bridge, engine room, and deck teams, particularly during maneuvering, cargo handling, maintenance work, and timesensitive situations. Zenitel added that structured alarm management and clear voice communication help crews respond faster and maintain a safer and more coordinated working environment at sea.
Zenitel also noted that the vessels are the largest container ships built in Turkey to date and that standardized system configurations can simplify integration across multiple builds while helping crews adapt quickly to onboard communication tools. In the maritime security and safety market, the case underscores that communications infrastructure remains a core element of resilient vessel operations, especially on demanding regional and intercontinental routes. n

Carlos Garcia, Sales Director, ASSA ABLOY Opening Solutions Middle East
Within the Middle East, wireless locking solutions—particularly SMARTair and Aperio— have proven to be among the most popular and best‑performing within ASSA ABLOY Opening Solutions. Their success is driven by a combination of flexibility, scalability, and ease of integration, which are critical requirements in the region’s project‑based environments
n By: Damir Muharemović damir.muharemovic@asmideast.com
a&s Middle East: Could you tell us a bit about your background and career journey — what led you to the access solutions industry? Could you describe your current role at ASSA ABLOY, what your main responsibilities involve, and what you consider to be the most valuable aspect of working for the company?
Garcia: I have been working in the door hardware and access solutions industry for over 25 years. I started my career with a distributor, managing sales operations across Cuba and the Dominican Republic. This early experience provided me with a strong foundation in the commercial and technical aspects of the busi-
ness. I later transitioned to the manufacturing side, where I have spent the past 16 years based in the Middle East, managing multiple brands and overseeing operations across both the Middle East and APAC regions.
Having worked on both the distribution and manufacturing sides has given me a well-rounded perspective of the industry, allowing me to better understand the challenges, expectations, and priorities of our distribution partners.
Currently, I serve as Sales Director at ASSA ABLOY Opening Solutions Middle East. I am responsible for driving business growth across our full portfolio—from doors and mechanical hardware to advanced access control solutions. My role involves leading regional sales strategies, developing key client relationships, and ensuring alignment across diverse markets.
What I find most valuable about working at ASSA ABLOY is the breadth of innovation and the ability to offer fully integrated access solutions. Being part of a global organization that continuously evolves with technology allows me to contribute to meaningful, future-ready projects while delivering real value to our customers.
a&s Middle East: Tell us more about ASSA ABLOY’s presence and operations across the Middle East — where are your offices currently located, and what markets or sectors are you primarily focused on?
Garcia: Our regional headquarters are based in Dubai, which serves as our central hub for the Middle East. From here, we support and manage markets across the GCC, as well as the wider

Wireless locks offer a practical balance between advanced security, operational efficiency, and flexibility, which aligns well with the evolving needs of Middle Eastern customers across sectors such as hospitality, commercial real estate, and mixed-use developments

region, including the Levant and Egypt. We also have on-ground representation in key markets such as Saudi Arabia, Qatar, and Kuwait. While the GCC remains our primary focus, we work across a diverse range of sectors. These include data centers, government and semi-government entities, transportation infrastructure, and residential developments, allowing us to address both large-scale projects and recurring customer needs across the region.
a&s Middle East: Can you present or name some of your latest, most complex projects in the region?
Garcia: One of the most complex projects we’ve delivered in the region is the NEOM staff accommodation project. This was particularly challenging due to the scale of deployment and the requirement for wireless access control, combined with real-time data availability. The project was in partnership with Qantara Development, which strongly champions BIM-driven processes to im-
a&s Middle East: Which sectors are leading the adoption of advanced access control in the Middle East, and why?
Garcia: Government and public sector entities are currently leading the adoption of advanced access control solutions in the Middle East. This is largely driven by regulatory requirements and the need to protect critical infrastructure. At the same time, there is a strong emphasis on user convenience alongside security. As a result, we’re seeing rapid growth in the adoption of biometric technologies, particularly facial recognition. These solutions offer a high level of security while also delivering a seamless, contactless user experience, which aligns well with the region’s focus on innovation and smart infrastructure.
prove productivity and accelerate project delivery. Within the NEOM Workers’ Villages, their collaboration with ASSA ABLOY enabled a highly coordinated approach to design and implementation. By leveraging ASSA ABLOY’s Openings Studio specifications software, wireless access control solutions were successfully integrated into the BIM workflow, allowing for greater accuracy, efficiency,
and control throughout the project lifecycle. This project stands out as a strong example of how advanced digital tools and wireless technologies can support large-scale, complex developments while meeting demanding operational and security requirements.
a&s Middle East: Mobile credentials and biometric integration are surging

ASSA ABLOY Showroom & Experience Center, Dubai
We have strengthened our capabilities through targeted acquisitions such as Kentix, which enables us to offer comprehensive solutions for data center environments
worldwide. How is ASSA ABLOY tailoring these technologies in general?
Garcia: Mobile credentials and biometric integrations are both following a strong adoption curve globally. At ASSA ABLOY, we don’t just look at these technologies through the lens of convenience and security, but also sustainability. Mobile credentials, in particular, eliminate the need for physical cards, reducing plastic waste while offering a seamless and secure user experience. This is why, at our Middle East regional headquarters, we have adopted mobile credentials in place of issuing plastic access cards to employees and visitors. By doing so, we’re able to demonstrate the real-world value of the technology. When customers and
partners visit our offices, they experience first-hand how mobile credentials simplify access while also supporting sustainability goals. This practical adoption helps build confidence in these solutions and reinforces their role in future-ready access ecosystems.
a&s Middle East: With cyber-physical threats on the rise and regulations on cyber resilience setting global standards, how is ASSA ABLOY ensuring regional customers stay secure and compliant?
Garcia: Cyberphysical threats are evolving rapidly, especially with the rise of AI driven attacks and increasingly interconnected digital systems. Regulations such as NIS2 and the upcoming Cyber Resilience Act
are setting clearer global standards, and customers in our region are looking for solutions that are both secure and compliant. At ASSA ABLOY, we address this by integrating cybersecurity into the entire lifecycle of our digital and connected products. Dedicated teams and crossfunctional working groups ensure that requirements from NIS2, the CRA, and other emerging regulations are understood and applied consistently across our portfolio. Beyond product security, we also focus on education and partnership. Through guidance, workshops, and expert insights, we help customers translate complex regulatory requirements into practical steps tailored to their operations. By combining secure-by-design solutions with regulatory alignment and customer support, we help organizations across the Middle East strengthen cyber resilience and stay protected in an increasingly complex threat landscape.
a&s Middle East: Within the Middle East market, which ASSA ABLOY Opening Solutions’ products or solutions have proven to

be the most popular or best-selling, and what factors do you believe are contributing to their success in the region?
Garcia: Within the Middle East, our wireless locking solutions—particularly SMARTair and Aperio—have proven to be among the most popular and best-performing within ASSA ABLOY Opening Solutions. Their success is driven by a combination of flexibility, scalability, and ease of integration, which are critical requirements in the region’s project-based environments. SMARTair has gained strong traction due to its simplicity, reliability, and suitability for both standalone and networked applications, making it especially attractive for hospitality, education, and commercial buildings. Aperio, on the other hand, has been widely adopted in more complex environments because it enables wireless locks to integrate seamlessly with existing access control systems— allowing customers to upgrade security without extensive wiring or infrastructure changes.
a&s Middle East: Your 2025 Wireless Access Control Report shows wireless systems overtaking wired ones globally. Is the Middle East following this trend, or are there unique regional dynamics at play?
Garcia: The global shift toward wireless access control is clearly reflected in the Middle East as well, but the pace of adoption is more gradual compared to global averages. Demand for wireless solutions is steadily increasing; however, regional project dynamics influence adoption rates. One key factor is the high volume of residential developments in the region, where traditional wired systems are still widely preferred due to cost structures, established specifications, and contractor familiarity. As a result, wired solutions continue to dominate many large-scale projects. That said, adoption varies significantly by sector. Hospitality is currently leading the way, with much higher uptake of wireless access control due to the need for flexibility, faster deployment, and enhanced guest experience. In contrast, commercial, government, and critical infrastructure sectors remain more cautious, often favoring wired systems because of perceived reliability and long-standing security standards. As a global access solutions provider, we are seeing increasing interest in wireless access control across the Middle East, and as more successful implementations come to market, confidence in these solutions continues to grow. This will play an important role in accelerating adoption across the region over time.
The appeal of these solutions is further strengthened by the region’s growing demand for faster project delivery, reduced
installation complexity, and future-proofed systems. Wireless locks offer a practical balance between advanced security, op-

erational efficiency, and flexibility, which aligns well with the evolving needs of Middle Eastern customers across sectors such as hospitality, commercial real estate, and mixed‑use developments.
a&s Middle East: What is ASSA ABLOY’s vision for expanding this regional footprint over the next three to five years? What can your customers expect in terms of new products, solutions, and services?
Garcia: Over the next three to five years, our vision for the Middle East is focused
on deepening our presence in key verticals where demand for advanced and resilient access solutions continues to grow. In particular, we see strong opportunities in residential, healthcare, and data center environments. Data centers are a key area of strategic focus for us.
As part of this expansion, we have strengthened our capabilities through targeted acquisitions such as Kentix, which enables us to offer comprehensive solutions for data center environments, including monitoring and securing ‘grey spaces’ alongside physical access control. This al-
Hospitality is leading the way with higher uptake of wireless access control due to the need for flexibility, faster deployment, and enhanced guest experience
Mobile credentials eliminate the need for physical cards, reducing plastic waste while offering a seamless and secure user experience
lows us to address not only access, but also environmental and operational security requirements in highly critical facilities. We are also continuing to invest in our security door manufacturing capabilities, with a strong emphasis on developing high‑security doors designed to meet regional requirements and standards. For our customers in the region, this means access to more integrated, end‑to‑end solutions, tailored to local market needs, supported by ongoing innovation, regional expertise, and a growing portfolio of specialized products and services. n


As regional uncertainty persists, Gulf security operators are responding not with reactive procurement but with deliberate investment in integrated platforms, AI‑ driven analytics, and operational resilience, building systems designed to perform under pressure, not just respond to it
n By: Roman Ivanković editorial@asmideast.com
The Gulf security market has long been built on a simple premise: continuity is not a luxury, but a requirement. In a region where critical infrastructure, large-scale economic activity, and ambitious national development programs run in parallel, any disruption carries consequences that extend well beyond its immediate source. Both governments and operators know this, and technology providers have built their entire value proposition around it.



This understanding has shaped the market for years. It also explains why the current environment has not produced the kind of volatility one might expect. The foundations were designed to absorb pressure. So far, they are holding.
Recent developments, which influenced both regional uncertainty and shifted global conditions, have not upset the market’s fundamental logic. Quite on the contrary. Rather than triggering reactive procurement or abrupt strategic shifts, the response across the Gulf has been measured and deliberate. Organizations are recalibrating, not retreating. They are reinforcing what works, addressing gaps where they exist, and directing investment toward long-term solutions, rather than focusing on short-term fixes.
What makes this moment particularly significant is the convergence of several forces reshaping security operations at the same time. The shift from standalone systems to integrated platforms is well underway. Artificial intelligence is moving from the edges of security infrastructure toward its operational core. Procurement decisions are becoming even more strategic, and the people who manage these systems are being equipped with tools that extend their capabilities without replacing their judgment.
Unified dashboards, automated alerts, and centralized command and control platforms are becoming standard expectations, particularly in sectors where the cost of failure is high and the margin for error is narrow.
Across supply chains, workforce management, and technology investment, the
same pattern keeps emerging. Stability is being maintained not through expansion or overreaction, but through greater precision and tighter control. The Gulf is not a market defined by crisis response. It is one that has made resilience a standard operating principle. The months ahead are expected to deepen that commitment even further.
Recent developments in the region have not triggered a surge in demand, but rather reinforced and refined existing priorities in the security market across the Gulf region. Governments and organizations continue to treat security as a foundational requirement, with a consistent focus on protecting critical infrastructure while ensuring operational continuity. Gulf states continue to prioritize uninterrupted economic activity even during periods of heightened regional tension, driving a growing need for comprehensive security, safety, and consistent operations. In that sense, demand is not reactive, but anchored in long-term strategic planning.
“Across the market, we are observing a measured but steady demand for advanced security and safety solutions – particularly those that enhance operational continuity, real-time visibility, and protection of critical assets. There is also a growing emphasis on technical advisory, system audits, and optimization of
existing infrastructure, reflecting a more mature and forward-looking industry,” underlined Norma Bitar, Managing Director of AlignTech International.
This stability is important, as it indicates that organizations are not responding to regional developments with urgencydriven procurement. Instead, they are reinforcing existing systems and investing in capabilities that support resilience over time. Bitar explained that the GCC overall continues to position itself as a benchmark for secure, well-regulated, and resilient markets, balancing immediate operational needs with long-term strategic development.
At the same time, there is a clear qualitative shift in how demand is structured. Organizations are moving away from standalone technologies toward integrated systems. Across the Gulf, organizations are showing stronger interest in solutions that can improve visibility, coordination, and response across facilities, rather than relying on standalone systems.
“At ScreenCheck, we are seeing growing relevance for integrated platforms that combine access control, video analytics, alarm management, visitor management, and connected monitoring into one operational framework. Procurement discussions are becoming more strategic, with clients placing greater focus on interoperability, faster incident response, scalability, and long-term operational value,” noted Shaji Abdul Kader, Chief Operating Officer of ScreenCheck.
GCC overall continues to position itself as a benchmark for secure, well-regulated, and resilient markets, balancing immediate operational needs with long-term strategic development
He also pointed out that the strongest momentum is expected to come from sectors where continuity and asset protection are especially important, including critical infrastructure, logistics, transport, healthcare, education, and large campuses. Procurement processes themselves are becoming more strategic, with buyers placing greater emphasis on interoperability, scalability, and value, rather than focusing solely on technical specifications – particularly evident in sectors such as energy, transport, and logistics.
This translates into strong demand for technologies that strengthen early threat detection, secure communication channels, enable surveillance, and protect critical infrastructure – all aimed at allowing organizations to operate with confidence despite an unpredictable regional environment.
“Across sectors such as energy, transportation, logistics, and public safety, we are observing a renewed focus on resilience and preparedness. Organizations are not necessarily reacting with panicdriven procurement, but rather with more structured investment in integrated security ecosystems that support longterm operational continuity,” underlined Loubna Tabbara, Marketing and Sales Director at Tabbara Electronics.
At a broader level, the regional focus remains on maintaining normal economic activity despite external uncertainty. Organizations are prioritizing resilience and preparedness while ensuring that operations continue without disruption –reinforcing the view that demand is not expanding impulsively, but evolving in line with more mature and structured operational requirements.
Across the Gulf, organizations are not facing widespread challenges in maintaining trained security personnel or ensuring operational continuity. Security operations continue to function normally, supported by stable institutional environments and well-established frameworks for safety and coordination.
“While there may be minor, localized challenges in deploying specialized personnel,
From an operational standpoint, the Gulf security market continues to function with a high degree of stability. There is no evidence of systemic disruption across supply chains, logistics, or delivery timelines, despite the ongoing situation in the Middle East. However, what has changed is the level of attention and control applied to these processes.
Organizations are approaching supply chain management with increased caution, not because of immediate breakdowns, but due to a recognition of potential variability in global logistics conditions. For ScreenCheck, the top priority is to stay ahead of the disruption. That means maintaining close coordination with global partners, planning inventory carefully, keeping communication transparent with customers, and building buffers where needed.
Other suppliers also confirm that delivery schedules remain largely unaffected. Deliveries are continuing on schedule, and distributors report minimal disruption. AlignTech International has implemented a set of protective measures to ensure stable operations – optimizing routing options, maintaining flexibility in delivery planning, and strengthening coordination with logistics partners to absorb any variability in global supply conditions.
A parallel approach can be seen in inventory strategies. Rather than reacting to disruptions as they occur, some organizations are deliberately maintaining local stock levels to absorb short-term fluctuations. This strategy, combined with close coordination with manufacturing partners, allows companies such as Tabbara Electronics to provide stability and reliability even when global logistics conditions are evolving. The operational environment can be described as stable but more actively managed. The system is not under strain, but it is being monitored and adjusted with greater precision. This reflects a broader shift toward proactive risk management, where continuity is ensured not by reacting to disruption but by anticipating and mitigating it in advance.


Strongest momentum is expected to come from sectors such as critical infrastructure, logistics, transport, healthcare, education, and large campuses
these are effectively managed through flexible staffing, cross-training, and close coordination with service partners. At the same time, increased adoption of remote monitoring and centralized systems is helping reduce reliance on physical presence while maintaining high security standards,” explained Norma Bitar.
Suppliers deem that operations are underpinned by strong safety frameworks, well-established contingency planning, and a high level of confidence in the region’s security environment, which have been key in ensuring continuity. The system is structurally resilient, with sufficient capacity to maintain performance even during periods of uncertainty. This ensures that operational coverage remains consistent without requiring large-scale structural changes.
“Security teams feel safe and supported in performing their roles, which allows organizations to maintain a high level of preparedness even during periods of regional uncertainty. At the same time, many organizations continue to invest in technologies that enhance the effectiveness of their security teams. Integrated command and control platforms, advanced video analytics, and secure com-
munications systems allow operators to monitor large environments more efficiently and coordinate responses when needed,” said Loubna Tabbara.
There is also a noticeable shift in how organizations approach workforce readiness. Rather than focusing solely on staffing levels, there is greater emphasis on training continuity, preparedness, and the ability to maintain performance under varying conditions.
“Many organizations are looking more closely at technology that can support personnel on the ground, for example, unified monitoring, automated alerts, centralized dashboards, and systems that reduce manual effort while improving situational awareness. In our view, operational continuity is strongest when trained teams are supported by well-integrated technology that helps them act faster, coordinate better, and maintain consistency under pressure. This is partly an inference from recent operationalreadiness guidance and from the wider industry focus on crisis leadership and control-room performance,” underlined Shaji Abdul Kader.
The key dynamic is not workforce shortage, but workforce optimization. Organi-
zations are ensuring continuity by combining stable staffing structures with enhanced technological support, creating systems that are both resilient and adaptable.
What is shifting now is not just the preference for integrated systems – that trend is well established – but the role that artificial intelligence is beginning to play within them.
AI-driven analytics are moving from the periphery to the core of security operations, enabling platforms to do more than connect data streams: they can interpret them, flag anomalies, predict patterns, and support faster decision-making with minimal human intervention.
This matters because the scale and complexity of modern security environments have outpaced what traditional monitoring approaches can effectively handle. Human operators, however well-trained, face inherent limitations when managing large volumes of simultaneous data inputs. AI addresses this gap not by replacing personnel, but by filtering noise, prioritizing alerts, and ensuring that attention is directed where it is needed most.
For organizations across the Gulf, this represents a meaningful upgrade in operational intelligence. The focus is no longer on simply having visibility, but on making that visibility actionable, automated, and

While shipment delays are not currently a concern, cost volatility is emerging as a variable worth monitoring. Shaji Abdul Kader noted that freight charges remain highly unpredictable given the current environment. However, he pointed out that this has not slowed things down – on the contrary, security projects such as biometrics, surveillance, and life safety accelerate the decision-making and distribution process.
in real time. Systems that once required significant manual oversight are becoming increasingly self-correcting, capable of adapting to changing conditions without waiting for human instruction.
The practical implications extend beyond security operations themselves. When AI is embedded into broader operational frameworks, it contributes to efficiency gains across facilities management, access control, and incident response. This reinforces the case for security investment not just as a protective measure, but as an operational asset.
This direction is clearly visible in procurement conversations happening across the region. According to ScreenCheck, organizations are gravitating toward connected ecosystems that offer a single operational view – consolidating events, identities, movements, and alerts into one coherent picture. The emphasis is on solutions that are interoperable and scalable, rather than feature-rich but
fragmented. In safety-critical environments in particular, the appetite for smarter monitoring, automated anomaly detection, and faster verification is growing – precisely because these capabilities reduce operational complexity rather than adding to it.
Equally significant is the shift in how organizations are approaching technology investment. There is a trend of integrating new capabilities into existing infrastructure while preserving what already works. This reflects a growing maturity in the market, where procurement decisions are driven by long-term operational logic rather than the appeal of novelty.
“There is a noticeable shift toward system optimization, upgrades of existing infrastructure, and intelligent automation, rather than complete system overhauls. This is especially relevant in sectors such as energy, utilities, transportation, and large-scale developments, where uninterrupted operations are essential. Overall, the trend is not just about adopting new technologies, but about investing in scalable, interoperable, and regulation-compliant solu-
tions that can adapt to evolving operational and geopolitical requirements,” said Norma Bitar.
The practical applications are becoming more concrete. AI-based monitoring is expanding beyond perimeter security into daily operations: tracking compliance, flagging anomalies early, and automating routine checks that would otherwise require continuous human attention. In high-risk environments such as industrial facilities and critical infrastructure sites, this means safer working conditions and more consistent adherence to safety protocols.
“We continue to see strong interest in advanced video surveillance with intelligent analytics, secure mission-critical communications, perimeter protection systems, and integrated command-andcontrol platforms that allow operators to manage security operations from a unified environment. Another important trend is the emphasis on interoperability. Organizations increasingly prioritize solutions that integrate seamlessly with existing infrastructure, allowing multiple systems to work together and provide a comprehensive operational picture across facilities, transportation networks, and critical infrastructure,” clarified Loubna Tabbara.
More broadly, security and operational systems are no longer evaluated purely as protective infrastructure. They are increasingly seen as tools for managing complexity and extracting value from data that organizations are al-

ready generating. They are making the case for intelligent systems not just on safety grounds, but on operational ones as well.
What is changing in the Gulf security market is not the direction, but the depth of commitment. Integrated platforms, AI-driven analytics, and automation are increasingly treated as essential components of operational strategy rather than optional upgrades. Organizations are moving toward full integration, recogniz-
Operational continuity is strongest when trained teams are supported by well-integrated technology that helps them act faster, coordinate better, and maintain consistency under pressure
ing that intelligent systems are a present operational requirement, not a future consideration.
Critical infrastructure, energy, transportation, and smart city development each bring specific demands, but share a common requirement: coordinated,

The key dynamic is not workforce shortage, but workforce optimization
technology-enabled security management at scale. Public safety agencies and law enforcement authorities are expected to continue modernizing along the same lines, with the emphasis on connecting and equipping existing resources rather than simply expanding them.
What this points to is a market that has quietly crossed a threshold. Security technology is no longer evaluated primarily as a protective measure — it is assessed as operational infrastructure, held to the same standards of reliability, integration, and return on investment as any other core system. That shift in how organizations think about security is arguably more significant than any individual procurement trend.
The question facing organizations is not whether to invest, but how to invest in ways that deliver lasting value — through smarter integration, stronger partnerships, and systems that can adapt as needs evolve. The Gulf has never been a market that responds well to disruption. What it has built instead is something more durable: a culture of continuity, backed by the technology and the institutional will to sustain it. n

Across the Middle East, oil and gas facilities operate in environments shaped by geopolitical tension, regulatory change, remote infrastructure, and multinational workforces. In such conditions, security cannot be measured solely by visible presence, technology, or force deployment. Its real strength lies in its ability to endure disruption. The decisive variable is logistics
n By: Raul Gonzalez, Senior Logistics Manager, Aldra Alameen Security Services, Dubai UAE raul@aldrasecurity.ae
Security strategies often prioritize perimeter systems, surveillance platforms, access control, and guarding forces. These components are essential. However, when disruption occurs (whether political, social, or operational), the determining factor is not whether security exists, but whether it can be sustained under pressure. Logistics transforms security from a static arrangement into a resilient operational system.
Traditional security models emphasize posture: personnel numbers, equipment capability, and procedural compliance. Yet posture without sustainment deteriorates rapidly in volatile environments. Fatigue, inconsistent rotations, supply interruptions, transport delays, and inadequate welfare standards gradually weaken performance. In high-risk energy operations, these weaknesses compromise continuity
long before a visible incident occurs. A logistics-centred approach shifts evaluation toward personnel endurance and welfare sustainability, redundancy in critical supply chains, transport reliability, modular support systems adaptable to operational tempo and speed in logistical decision-making. This reframing aligns security with business continuity, ensuring protection remains durable rather than symbolic.

Raul Gonzalez
Many energy installations in the region operate in remote desert locations, offshore platforms, or politically sensitive areas where external support may be delayed. In such contexts, autonomy becomes a strategic requirement. Operational autonomy depends on logistical depth. Security leadership must define how long operations can be sustained independently, which resources are mission-critical, where redundancy is essential, and what decision authority exists at the site level. When these parameters are structured through clear logistical standards, executive leadership gains confidence in continuity. Autonomy reduces vulnerability to supply chain disruption and strengthens resilience during regional instability.
Oil and gas projects in the Middle East typically involve multinational security teams operating within diverse cultural environments. Consistency becomes a stabilizing factor. “Logistics provides that consistency.”
Standardized equipment management, rotation cycles, accommodation protocols, and welfare provisions create predictability. This predictability fosters cohesion without imposing cultural rigidity and aligns security teams with corporate expectations and regulatory frameworks. Logistics, therefore, functions as a governance mechanism, reinforcing professionalism through systems rather than declarations.
Energy infrastructure must operate under the assumption that disruption is inevitable. Effective security logistics must therefore be modular and adaptable. “Rigid systems fail under stress. Adaptive systems absorb pressure.”
Resilient logistics frameworks include predefined contingency pathways, controlled decentralization of decision-making, targeted redundancy in critical functions, and continuous feedback mechanisms that refine standards. Security logistics should operate as a living system where operational experience informs improved sustainment models.
“Infrastructure protection is evolving from visibility-based metrics to readiness-

based evaluation.” Personnel numbers and equipment inventories do not automatically translate into resilience. A more advanced assessment considers sustainment capacity under prolonged operational stress, personnel resilience over time, supply chain robustness, decision velocity under uncertainty, and defined autonomy thresholds. This perspective shifts executive discussions from “Do we have security?” to “Can our security endure disruption?” In high-value energy environments, endurance (not appearance) is the true indicator of protection.
Recent geopolitical developments in the Gulf have once again highlighted how

When disruption occurs, the determining factor is not whether security exists, but whether it can be sustained under pressure. Logistics transforms security from a static arrangement into a resilient operational system
quickly regional tensions can influence energy security dynamics. Pressure on maritime routes, heightened military alert levels, and uncertainty surrounding strategic waterways such as the Strait of Hormuz demonstrate that disruption is not a theoretical risk but an operational reality. In this environment, resilience increasingly depends on logistical systems capable of sustaining stability when external conditions become unpredictable.
For oil and gas operators in the Middle East, logistics must be treated as a strategic security capability. Investment that neglects sustainment creates fragility. Structured, measurable, and adaptive logistical standards generate resilience that protects revenue, compliance, and reputation. In a region where volatility is constant, security systems must be designed not only to deter threats but to withstand pressure. “Logistics is the element that converts security architecture into a sustainable operational reality.” In the Middle East energy sector, it is not a support function; it is the decisive pillar of resilience.
Finally, as global energy demand continues to grow and geopolitical dynamics remain uncertain, the resilience of oil and gas operations will depend on systems capable of sustaining stability under pressure. Security strategies focused only on deterrence risk, overlooking the deeper requirement of operational endurance. By integrating logistical readiness into security planning, energy operators move beyond reactive protection toward sustainable resilience, safeguarding not only infrastructure but the continuity of energy supply itself. n

n By: Fatima Al Husseiny editorial@asmideast.com
The Middle East’s Public Address and Voice Alarm (PAVA) market is undergoing a quiet but significant shift. Largescale infrastructure investment, tightening life-safety regulation, and a wave of landmark worship projects across the Gulf are driving demand for systems that
are not only certified, but intelligible and resilient. For integrators and consultants, the question is no longer whether to specify PAVA, but how to do it correctly in environments where acoustic complexity, cultural expectations, and regulatory scrutiny converge. This article draws on interviews with senior figures from Zenitel, TOA, and Keenfinity Group to examine the forces reshap-
ing PAVA deployment across EMEA’s worship spaces.
The same architecture that makes the space feel sacred makes it acoustically treacherous. Ask any experienced PAVA engineer where a worship space project is
won or lost, and they’ll give you the same answer: long before installation day. Worship spaces present a predictable acoustic challenge defined by volume, reflective materials, and limited scope for intervention. Zenitel addresses this through predictive acoustic analysis followed by DSP-based tuning to control reflections and maintain clarity under real operating conditions. Ehab Fraij, Area
Walk into any house of worship in the Middle East, and the acoustic challenge is immediate. Domed interiors and marble prayer halls were built for awe, not intelligibility. The best PAVA deployments operate invisibly, delivering clarity under normal conditions and reliability when it matters most

Manager for Safety & Security at Zenitel Middle East, notes that “our priority is always speech intelligibility.”
TOA approaches the acoustic challenge through platform flexibility, allowing parameters to be adjusted to the specific environment. This enables operators to control reflections during speech while preserving natural reverberation where it supports liturgical or musical elements.
Ali Ullah Sabri, Middle East Manager at TOA, adds, “Great audio in a mosque doesn’t just fill the space – it respects the silence between the words.”
Keenfinity Group experts frame the diagnostic challenge with particular clarity. Maarten Wings, Director of Technical Sales Support, puts it plainly: “Houses of worship present a formidable acoustic challenge. Large volumes, soaring ceilings,
and the hard reflective surfaces typical of stone, marble, and tile construction generate significant reverberation, the natural enemy of speech intelligibility.”
Understanding a room’s acoustic character is the diagnosis. What follows is the treatment, and no two engineers prescribe it quite the same way. Zenitel, TOA, and Keenfinity Group each bring a distinct technical philosophy to the challenge.

Ehab
Fraij, Area Manager, Safety & Security, Zenitel Middle East
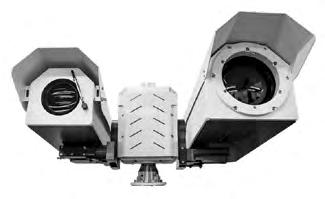
Keenfinity Group approaches reverberation as a problem of control rather than amplification. As Wings puts it, “the solution lies in precise sound steering.”Bosch’s LAS-BEAM active column loudspeakers direct audio energy toward the audience instead of dispersing it across reflective surfaces. By limiting spill onto walls and ceilings, the system reduces secondary reflections that typically degrade clarity in large or acoustically challenging spaces. This is achieved through multiple independently aimable beams, allowing installers to match sound distribution to the geometry of each room. Coverage can therefore be shaped with a high degree of precision, maintaining consistency from the front rows to distant galleries.
The loudspeakers are paired with the PRAESENSA public address system and supported by DSP-based processing, including individual volume control. Together, these elements are designed to improve speech intelligibility even in environments where reverberation would otherwise compromise audibility.
Zenitel works at the digital layer, shaping sound with a precision that lets installers respond to the specific reflective character of each space, room by room, surface by surface. Fraij explains that “Our built-in DSP tools, such as time alignment, EQ shaping, dynamic compression, and automatic volume control, allow us to finely tune the system so the spoken word remains clear even in highly reverberant halls.”
TOA’s approach pairs purpose-built hardware with adaptive processing, covering the acoustic challenge from two directions at once. Sabri notes, “On the loudspeaker side, we offer both powerful horn

Ali Ullah Sabri, Middle East Manager, TOA
speakers for clear outdoor broadcasts (e.g., the adhan) and line array loudspeakers designed for challenging indoor environments.”
In worship spaces, technical performance matters, but invisibility matters more. Poor integration is an intrusion, regardless of how good it sounds. Zenitel has made aesthetic discretion a core design principle. As Fraij notes, “We also recognize that aesthetics matter deeply in sacred environments. To respect architectural integrity, we use low-profile, sleek wall-mounted speakers and equipment like compact Integra-format units that blend discreetly into the surrounding structure without requiring invasive installation work.”
Sabri echoes this commitment, noting that their loudspeaker solutions provide

Wings, Director of Technical Sales Support, Keenfinity Group
controlled sound dispersion, helping to minimize reflections while maintaining a discreet visual appearance that respects the architectural integrity of historic buildings. This alignment between form and function has broader implications for how the PAVA industry positions itself in the heritage and cultural sector.
A system failure during prayers with a large number of people or an emergency evacuation carries consequences far beyond disappointment, and PAVA providers in this sector design accordingly. According to Zenitel, resilience is embedded at the infrastructure level. “Reliability is never compromised. Our systems include dual power paths, network redundancy, hardware bypass modes, and hot-swappable amplifiers to ensure
Mosques demand purpose-built solutions; their acoustics, layout, and liturgical rhythm set them apart from any other space. TOA has developed dedicated solutions for the mosque market, such as the MX-6224D, a compact all-in-one mixeramplifier designed for small- to mid-sized mosques. Mosques present specific challenges due to their open architecture and the need for clear and consistent speech reproduction during prayers and sermons. The MX-6224D supports this through integrated signal processing, multiple microphone inputs, and separate amplification for indoor and outdoor zones, for example, for the Adhan. Their attention to ritual-specific function extends to headset and handheld microphone selection as well, enabling flexible use depending on the ritual and the speaker’s movement patterns. For mosque applications, TOA offers a dedicated neck-worn microphone, the EM-362-EB, which ensures stable speech pickup during movement while keeping the speaker’s hands free. The EM-362-EB is a small detail in a large system, but it is the kind of detail that can separate a generalist audio solution from one that has been engineered with cultural intelligence.
services and safety messaging remain uninterrupted at all times.” For Keenfinity Group, the reliability argument is most sharply expressed through the lens of emergency communication. “For safety managers, this translates directly to one outcome: when an alarm sounds, people hear and understand it.” PRAESENSA has build-in spare amplifiers to cater for redundancy. Even if digital audio fails, an analog lifeline allows evacuation messages to continue, going beyond standard requirements. Power circuits and IP connections are fully redundant.
The shift from analog to IP has redefined PAVA as distributed, scalable, and remotely manageable, a transformation that extends far beyond infrastructure for religious facilities of any scale. IP architecture enables integration, scalability, and remote system management. “Our modern PAVA platforms are designed to combine secure IP-based audio, strong cybersecurity practices, and comprehensive remote supervision into a single resilient system. Their open, network-centric architecture allows seamless integration with SIP telephony and other communication or security technologies, which is particularly beneficial for large churches, mosques, or multi-building religious campuses,” said Fraij.
On a multi-building campus, SIP integration routes emergency voice messages across a shared network, eliminating parallel cabling and enabling faster, more coordinated emergency response. Sabri lays out a similarly expansive vision of what IP connectivity enables at scale. He explains, “Our larger PAVA and intercom systems are based on IP audio technology, enabling flexible system design across buildings, campuses, or even city-wide infrastructures…”
ONVIF integration signals PAVA’s direction toward unified platforms where audio, video, access control, and emergency broadcasts operate as one, and is the new standard for credible life-safety infrastructure in large worship spaces. Sabri further notes that “The integration of our new IP-based PA and intercom series with broader safety networks,
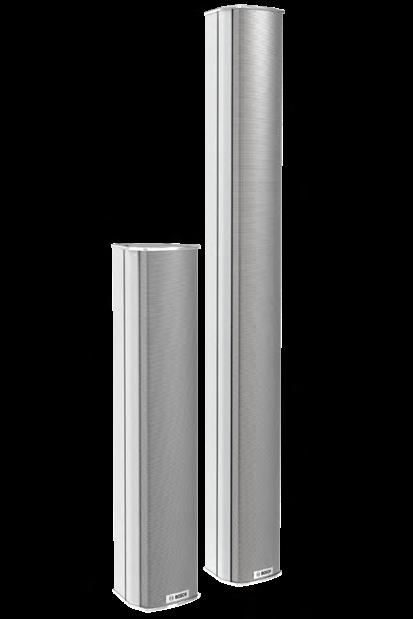
LAS-BEAM steerable column loudspeaker familyKeenfinity Group
Great audio in a mosque doesn’t just fill the space – it respects the silence between the words
including CCTV, intercom, and access control, allows centralized monitoring and control, which is particularly valuable in large religious facilities and public buildings where safety and operational reliability are critical.”
IP connectivity is the foundation, but in large worship environments, latency, synchronization, and signal integrity become
the key engineering challenges. This is where Dante has emerged as a differentiating factor. According to Sabri, Dante compatibility is central to their approach for complex sites, “for larger or more complex sites, TOA PAVA systems scale from a single zone up to over 2,500 loudspeaker zones. Dante-compatible mixers and loudspeakers, like our SR-D200-EB, ensure low-latency, high-quality audio distribution across multiple zones, simplifying management of prayers, sermons, and musical elements.”
Regulatory
compliance for PAVA systems across EMEA
is far from
uniform,
and nowhere is that complexity more apparent than in the Middle East,
where a distinct hybrid model has emerged. The region’s acceptance of both major certification frameworks, EN 54 (European) and UL 2572 (North American), introduces a level of flexibility that European-only deployments do not enjoy
IP migration has brought capability and vulnerability in equal measure, and in a house of worship where the PAVA system may be the only means of reaching thousands in an emergency, a successful intrusion is not only an operational issue but a life-safety risk. As Wings states, “A public address system is, by its nature, a tool for mass communication. That capability also makes it a potential target. An unauthorized party gaining access to a worship venue’s PA system could trigger false evacuations, broadcast harmful content, or simply disable life-safety functionality at a critical moment. For secu-
rity managers, cyber risk is no longer a peripheral concern; it is central to a PA system design.”
The question is no longer whether these systems will be targeted, but whether they are built to survive it. PRAESENSA, for instance, addresses this through multiple layers of protection. All audio transmission and control communications are encrypted, and the system uses digital certificates to verify the identity of connected devices, preventing third-party interference. The platform has achieved UR-E27 certification, the industry standard for secure IP-based communication in life-safety systems, as well as ISO 27001 and ISO 27701. On the product level, OMNEO uses encrypted audio data and encrypted audio control plus exchange of certificates.
Zenitel approaches cybersecurity from an equally principled but architecturally broader perspective, embedding security not as a product feature but as a design philosophy. They align system deployment with evolving standards that highlight cyberrisk management, ensuring that life-safety functions remain shielded from unauthorized access or tampering. Cybersecurity in life-safety systems is not static; threat vectors evolve, and so must system design.
A high-performance system that depends on a trained engineer being present is inherently limited, and remote monitoring and management exist to close that gap in life-safety infrastructure that cannot afford such dependency.
According to Fraij, supervision is built into the platform architecture itself: “Continuous supervision of signal paths, inputs, and outputs enables rapid fault detection, whether staff is on site or monitoring remotely.” The implication is clear: fault detection is not dependent on a technician noticing a problem; it is automated, continuous, and triggered the moment a signal path deviation occurs, regardless of whether anyone is physically present in the facility.
Remote management is a particular asset for smaller sites, a cohort that is often underserved by solutions designed for large, technically staffed venues. As Sabri notes, “Remote maintenance enables firmware updates, system checks, and troubleshooting without on-site technicians, which is particularly valuable for smaller sites with limited staff.”
Wings positions remote management within a broader framework of operational availability, linking it explicitly to the open standards architecture that makes it possible. “Open and standardized interfaces allow remote monitoring and management, reducing the need for on-site intervention and enabling rapid response to any anomaly. The use of open interfaces, rather than proprietary protocols,
IP infrastructure and cybersecurity frameworks suit landmark sites, but most worship spaces are small and volunteer-run, and the providers worth watching are those who understand both markets. “Houses of worship are a specific use case. Many churches, mosques, and synagogues, particularly smaller or midsized sites, do not have dedicated technical staff. In these environments, ease of use, reliability, and long-term durability are far more important than complex IT features. Our focus here is on intuitive, cost-effective systems that reliably support daily worship,” said Sabri from TOA. That balance is ultimately what defines a credible modern offering in this sector: the goal is to provide systems that match the real operational needs of each house of worship, combining proven reliability and ease of use with modern, future-ready technology where it truly adds value.
is an important distinction: it means that remote management is accessible to any authorized operator using standard tools, rather than requiring vendor-specific software or specialist training.”
In a life-safety system, cybersecurity, remote monitoring, and redundancy are all essential because partial operation during an emergency is not a fallback; it’s a failure.
According to Fraij, high-availability architecture is embedded across every critical system component: to safeguard uninterrupted operation, their systems incorporate high-availability features such as redundant power supplies, dual network paths, automatic failover functionality, dual-hosted microphones, and hot-swappable amplifiers.

TOA EM-362-EB neck-worn microphone
for facilities hosting thousands, designing above them builds the margin between a system that ticks boxes and one that can actually be trusted.
IP architecture, cybersecurity, and remote monitoring have transformed PAVA systems in worship spaces into a full communication infrastructure, while the communities they serve carry centuries of tradition that technology must respect.
Alongside these, intelligent DSP capabilities, such as automatic volume control and precise time alignment, ensure consistent clarity even as ambient noise conditions change. Together, these capabilities create a secure, reliable, and future-ready safety infrastructure for worship environments. True resilience means both surviving hardware failure through redundant components and maintaining performance quality through intelligent DSP that compensates automatically as conditions shift. Wings makes an even bolder claim in this field: “Built-in redundancy ensures the system remains operational under fault conditions, and the level of redundancy designed into PRAESENSA actually exceeds what current safety standards mandate. For a venue that may host thousands of worshippers simultaneously, that engineering margin is not a luxury.” Safety standards set a floor, and
A PAVA system that performs flawlessly but fails compliance will hardly be deployed. Regulatory compliance for PAVA systems across EMEA is far from uniform, and nowhere is that complexity more apparent than in the Middle East, where a distinct hybrid model has emerged. The region’s acceptance of both major certification frameworks, EN 54 (European) and UL 2572 (North American), introduces a level of flexibility that Europeanonly deployments do not enjoy. Across EMEA, regulatory fragmentation makes that risk unavoidable, with multiple jurisdictions, overlapping standards, and locally enforced life-safety requirements shaping every project.

PRAESENSA family -
Keenfinity Group
Natural and loud are not the same, and intelligible and processed are not the same. In spaces where acoustic character carries spiritual weight, overengineering the audio is not an improvement; it’s a violation
The first thing experienced PAVA engineers learn about EMEA regulation is that no two markets are quite the same. EN 54 offers a foundation across Europe, but it’s applied inconsistently and carries no universal mandate. The foundational principle of this field is variability itself: regulatory requirements for PA and PAVA systems in houses of worship vary depending on the specific project and country. Factors such as building size, occupancy, architectural complexity, and the fire protection concept determine whether a certified voice alarm system is required. Compliance in this sector cannot be reduced to a checklist; every project begins with a jurisdictional assessment that determines whether the installation falls under life-safety regulation.
Unlike Europe’s conditional framework, the Middle East layers local Civil Defense authority and municipal mandates on top of international certification, making compliance a multi-tiered obligation.
According to Fraij, this layered structure is the defining feature of the GCC compliance environment. In the Middle East, regulatory authorities add another layer. Civil Defense bodies require systems to be local code compliant; tested and certified to international standards is always a plus, and EN 54 compliance is a widely accepted product testing standard. This means manufacturers must complete product registration, work with accredited contractors, and meet detailed documentation and inspection requirements. As a result, the operational model across the GCC follows a dual-compliance structure: international certification supported by local civil defense authorization. Dual compliance means meeting both international equipment standards and local civil defense requirements for installation and emergency connectivity. Treating them as interchangeable can be one of the most expensive mistakes in cross-border deployments.
The practical implications of this structure become clearer at the project level. Wings’ analysis goes further, outlining regional mandates that must be engineered into any Middle Eastern PAVA
deployment, requirements with no direct equivalent in European frameworks. These include bilingual evacuation messaging in Arabic and English, a mandatory priority override for the Adhan, 2-hour fire-rated cabling, and emergency logic aligned with local Civil Defense codes, which run parallel to, and take precedence over, NFPA 72.
Together, these requirements reflect deliberate cultural and regulatory choices, positioning the region as a standardssetter rather than a follower.
Beneath the formal regulatory picture lies a subtler shift in market expectation, one that is reshaping what consultants, end users, and authorities consider adequate, even where full certification is not yet legally required.
According to Sabri, this transition is already visible across the region: across parts of the EMEA region, especially in the Middle East, we are also seeing a gradual shift in expectations. Consultants and end users are increasingly considering life safety, operational reliability, and long-term system sustainability. This is driving a transition from traditional standalone mixer-amplifier setups towardmore advanced and certified PAVA solutions, especially in large mosques and landmark religious sites.
As flagship religious sites push standards higher, the entire supply chain follows.
Credible integrators don’t wait for a formal mandate. As Sabri notes, “Overall, requirements are typically defined on a projectspecific basis by local authorities and consultants. TOA supports both scenarios, offering fully EN 54-certified voice alarm systems as well as highly reliable public address solutions tailored to each project.”
Technology in a house of worship must enhance without altering, extend without diminishing, and deliver clarity without imposing a broadcast signature on a space built for prayer. This philosophy of purposeful invisibility is the foundational principle of their approach. “Religious venues are constantly navigating the balance between safeguarding sacred tradition and meeting contemporary expectations. Our job is to ensure technology enhances the
On projects where EN 54 and UL 2572 both apply, a platform’s ability to satisfy multiple standards without duplicating infrastructure stops being a procurement detail and becomes a competitive advantage. As Wings points out, few platforms are positioned to meet this dual-standard requirement without architectural compromise: the Bosch PRAESENSA PAVA system carries certification under EN 5416 and is certified for UL 864/UL 2572 certified fire evacuation/mass notification system (MNS), making it one of the few platforms capable of meeting this dual-standard requirement without compromise. For a security manager operating across multiple jurisdictions, that flexibility is a significant operational advantage. A platform carrying both EN 54-16 and UL 2572 certification, configurable for local protocols and bilingual messaging, isn’t just better specified but built for a future single-standard platform.
worship experience without overshadowing it. Today’s PAVA and AV systems are therefore designed to be dual-purpose; the same infrastructure that carries calls to prayers, sermons, chanting, or musical elements can also support announce-
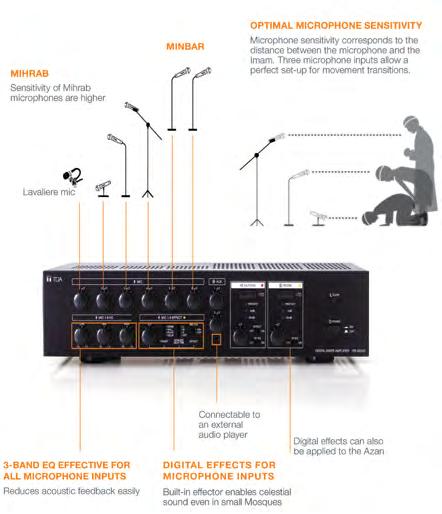
ments, streaming feeds, and emergency messaging, preserving the authenticity of liturgical sound while improving clarity and consistency,” said Fraij.
The distinction is critical in worship environments. Natural and loud are not the same, and intelligible and processed are not the same. In spaces where acoustic character carries spiritual weight, overengineering the audio is not an improvement; it’s a violation.
Unified infrastructure lets the call to prayer, choir, and emergency alerts share one network with the right priority logic, while separate infrastructures mean higher cost, greater complexity, and more physical intrusion into spaces where every visible cable is a compromise.
Today’s congregations are multilingual by nature, shaped by migration, diaspora, and global movement. A PA system that wasn’t designed for them isn’t a minor shortcoming. Multilingual AV capability isn’t a technical upgrade. It’s a commitment to serving everyone equally.
According to Fraij, multilingual capability now spans both pre-recorded and live audio functions: for increasingly diverse congregations, the systems support multilingual pre-recorded messages, live translation routing, and clean audio capture for streaming, ensuring that services reach both in-person worshippers and remote audiences effectively.
There’s a significant gap between playing a pre-recorded multilingual message and routing live simultaneous interpretation in real time. The first is a scheduling challenge. The second demands low

When technology is implemented with respect and intention, it becomes invisible, and the worship experience remains seamless
latency, precise zone control, and signal isolation that only purpose-built infrastructure can deliver. Wings addresses that infrastructure challenge with a level of technical specificity that underscores the complexity involved. As he explains, multilingual accessibility is addressed through seamless integration with interpretation platforms. Via Dante and AES67 digital networking, PRAESENSA connects with systems such as the DICENTIS conference system and the Integrus wireless language distribution system, or any third-party Dante-enabled device, delivering real-time multilingual translation to worshippers. Dante’s and AES67’s open architecture allows multilingual facilities to build interoperable systems from best-in-class components across manufacturers, rather than being locked to a single vendor.
TOA approaches multilingual complexity through the lens of system integration and acoustic planning, acknowledging that modern language requirements add meaningful design layers to an already demanding brief. As Sabri observes, “Modern requirements such as multilingual announcements, live streaming, or realtime audio distribution across multiple zones add additional layers of complexity. Despite this, the fundamentals remain the same: speech and music must be clear, natural, and intelligible, and the system must always be reliable.”
The industry has moved beyond treating hearing loops as compliance checkboxes, recognizing that a faith community unable to guarantee full participation for every worshipper falls short of its intended role within the community.
Zenitel’s systems integrate smoothly with hearing-assistance technologies and incorporate thoughtful loudspeaker placement and visual alerting, ensuring that worshippers with hearing impairments can fully participate. “Fully participate” sets a higher bar than “compliant” with equal access to the liturgy and the community. Loudspeaker placement serves hearing aid users. Visual alerting ensures those who cannot hear are never excluded from the safety and communal life of the space.
Keenfinity Group’s approach to hearing accessibility is grounded in a hardware integration framework that supports both proprietary and third-party assistive listening solutions. As Wings explains, for congregants with hearing impairments, the system’s Audio Interface Module enables integration with induction loop amplifiers, including Bosch’s own PLN-1LA10 or compatible third-party solutions. This ensures that every word of the liturgy reaches every member of the congregation, whether
they are present in the building, connected digitally, or relying on assistive listening technology.
For remote congregants, stream quality matters as much as room acoustics, and a system designed to serve both reflects broader operational requirements. TOA acknowledges hearing accessibility as a dimension of the broader integration challenge, noting that where specialist solutions are required, seamless third-party integration is the operative standard. As Sabri explains, “If a feature cannot be provided in-house, we integrate third-party solutions, such as assistive listening devices for the hearing impaired, as seamlessly as possible.”
Acoustic simulation is risk management, not a premium add-on, because discovering flutter echo, comb filtering, and dead zones after installation is expensive, while discovering them in simulation is not. “We work closely with local partners to develop tailored solutions. Multi-zone amplification ensures that sermons or prayers are clearly audible in every hall, courtyard, or overflow area, while live music or choirs are reproduced with natural tonal quality,” Sabri explains. “For highly complex projects, we support the planning phase with acoustic simulations and speaker placement studies.”
The modern house of worship is not a single room. Overflow halls, courtyards, classrooms, ablution areas, each with its own acoustic character, each requiring the right audio at the right moment. Multi-zone architecture exists to manage these environments in real time, to the standard that both liturgy and life-safety demand.
Sabri approaches this challenge with particular sensitivity to the architectural specificity of different worship traditions. According to Sabri, balancing the traditional requirements of religious ceremonies with modern AV expectations is particularly important in the Middle East, where mosques often include multiple prayer halls, open courtyards, and outdoor areas for the Adhan. Churches and synagogues also frequently feature galleries, balconies, and multi-level layouts. Each of these areas requires consistent and intelligible sound coverage. There is no generic worship-space AV solution. A mosque, a Baptist church, and a synagogue each have fundamentally different zone requirements. The system must be designed around the specific spatial logic of each tradition, and that begins with listening, not a product catalogue.
Zenitel elaborates on this principle with a specificity that speaks directly to the operational needs of diverse faith communities. As Fraij explains, multi-zone control provides the flexibility religious facilities need; male-female prayer halls, sanctuaries, chapels, classrooms, youth areas, and overflow halls can each be managed independently. This allows venues to maintain intimacy in traditional spaces while supporting teaching, translation, streaming, or community activities elsewhere and ensuring coordinated or phased evacuation when required. Multi-zone architecture serves worship by delivering the right audio to the right space and serves emergencies by sequencing evacuation across zones in controlled phases. Both functions require the same infrastructure, just different logic.
The real test of any PAVA system comes after installation, under the conditions it was designed to serve. The following projects illustrate how different approaches perform in practice, across a range of architectural, acoustic, and operational contexts.
The ADCO Mosque presented a challenge of physics. As Fraij describes, “The ADCO Mosque in Abu Dhabi offers a different set of lessons. As a large, modern mosque accommodating up to 2,000 worshippers, its architecture uses expansive glass walls that fill the interior with natural light and create a serene, open aesthetic.”
Glass reflects sound with near-total efficiency, and when an architect specifies expansive glass walls, the PAVA system must solve the acoustic problem the architecture created, because it cannot easily be mitigated through treatment alone. Here, intelligibility was the main challenge: large reflective surfaces and
a high ceiling meant that DSP-driven corrections, loudspeaker placement, and calibrated reinforcement were essential to achieve clarity for daily prayers and sermons. Operationally, this project reinforced how crucial it is to align system performance with building conditions.
TOA’s project portfolio spans a range of worship traditions and geographies that few providers can match. Three installations, in southern France, Tanzania, and Egypt, illustrate both the diversity of challenges the company has encountered and the consistency of the design principles that have guided its responses.
Alès Cathedral in the south of France is a protected historic monument with extremely challenging acoustics — high ceilings, hard stone surfaces, and long reverberation times. When the interior was restored, the cathedral needed a
new sound system that would deliver clear speech for services but remain easy to operate for non-technical staff. “Our colleagues in France worked closely with the engineering firm ADRET right from the early design phase. Together, they selected controlled directivity solutions — mainly our SR-H2S line arrays and BS-1030 in-wall speakers — to minimize reflections. Combined with our D-900 digital matrix and digital amplifiers, the system achieved STI values between 0.46 and 0.57, which is an excellent result for a building of that size and age,” said Sabri.
A strong example from East Africa is the Masjid Mtoro Mosque in Kariakoo, Tanzania. The mosque has large open spaces and significant reverberation, so achieving clear and consistent sound for prayers and announcements was essential. TOA designed a system using our MX-6224D mosque amplifier, digital amplifiers, and SR-S4 Slimline Array speakers to provide even coverage inside


The UAE is one of the most demanding markets for worship-space PAVA in the world. Its flagship religious projects are conceptually complex, culturally significant, and visited by audiences whose audio expectations have been shaped by world-class performance venues.
Few projects anywhere in the world carry the symbolic weight of the Abrahamic Family House, and fewer still present its particular combination of technical and philosophical complexity. As Fraij describes it, “The Abrahamic Family House in Abu Dhabi is a rare and deeply meaningful project, an interfaith complex that brings together a mosque, a church, and a synagogue within a single cultural site. Each house of worship is architecturally distinct yet designed to coexist in harmony, supporting reflection, ritual, and public engagement. Honoring the distinct acoustic priorities of a mosque, church, and synagogue simultaneously within a shared facility required a level of zoning sophistication that redefines what multi-zone architecture is capable of.”
The lessons from this project extend across the technical, operational, and compliance domains: from an operational standpoint, this Zenitel’s project underscored the importance of precise acoustic modeling for three very different worship styles, careful zoning to preserve each faith’s liturgical character, and system designs capable of supporting high visitor throughput while respecting sacred sound. It also highlighted the need for coordinated compliance and consistency across all three spaces, given the unified visitor experience and interfaith programming.
the prayer hall. This was complemented by wall speakers and horn speakers for the outdoor areas, alongside a flexible microphone setup — from neck-worn to handheld and wireless — to ensure clear pickup even during movement. “What we learned from this project is the impor-
tance of aligning the system closely with the everyday needs of a mosque: daily prayers, sermons, and indoor and outdoor communication. When the design reflects these patterns, the result is a natural and highly intelligible sound experience,” Sabri concluded.
Another notable TOA project is the sound system installation at the Al Masjed Al Jami’ Mosque in El Shorouk, on the northeastern outskirts of Cairo. The mosque features Egypt’s largest single dome, measuring an impressive 32 meters in diameter — a highly demanding acoustic environment. The interior is dominated by hard, reflective materials, so reverberation posed a significant challenge. The client also specified that the number of loudspeakers had to be kept to an absolute minimum. The final solution centered around TOA’s SR-S4 Slimline Array Speakers, supported by SR-H2 units to deliver balanced coverage throughout the large dome volume. The system is powered by the M 9000M2 digital mixer paired with the DA-250 amplifier, ensuring reliable processing and amplification. A carefully selected set of microphones completed the installation, enabling clear and flexible reproduction of speeches, recitations, and lectures.
Rather than individual case studies, Keenfinity Group’s Maarten Wings draws on over twenty large-scale mosque in-

Cathédrale SaintJean-Baptiste d’Alès
The Middle East’s houses of worship are not simply acoustically demanding venues. They are living institutions where life-safety, cultural identity, and centuries of tradition converge within a single space
stallations across the Gulf and Pakistan, plus numerous European church projects, to identify lessons that only scale can produce.
Across those projects, reverberation emerges not as a context-specific problem but as a structural challenge inherent to worship-space architecture, and any
deployment strategy that doesn’t center intelligibility management risks missing the core challenge. From this body of experience, Wings identifies three consistent operational lessons. Acoustic analysis and simulation must be conducted during the design phase, not after installation, as predicting sound behavior early helps
eliminate dead zones and avoid costly remediation. Loudspeaker selection is equally critical, with coverage pattern, directivity, and room acoustics all shaping performance, meaning no single solution fits every space. Commissioning, finally, is not a final step but an optimization phase, where tools such as parametric equalization allow installers to refine system performance and control residual reflections. Wings closes with an observation about the broader market context that has shaped this body of experience and that has implications for how the sector’s standards are being set: “The scale of mosque deployments across the Gulf region also reflects a broader market reality: the Middle East represents one of the most active and technically demanding environments for PAVA integration in houses of worship globally. Security managers in the region should expect that best practice is being defined not in textbooks but on live projects.”
The Middle East’s houses of worship are not simply acoustically demanding venues. They are living institutions where lifesafety, cultural identity, and centuries of tradition converge within a single space. The providers examined in this article, Zenitel, TOA, and Keenfinity Group, demonstrate that serving these environments requires more than technical competence. It requires a clear understanding of what the space is for, and how it is used.The lessons from the field are consistent. Reverberation is a structural challenge, not a site-specific one, and intelligibility must be placed at the center of every design methodology. Compliance is multi-tiered, and treating international certification as sufficient remains one of the costliest assumptions a specifier can make. Cybersecurity is no longer peripheral; it is a core life-safety consideration. At the same time, system design must extend beyond performance metrics to include usability, integration, and long-term operational reliability. Ultimately, the most advanced system offers little value if it cannot be used effectively when it matters most. A life-safety system is only as reliable as the people who operate it, and no level of redundancy or certification compensates for an interface that cannot be used with clarity and confidence under pressure. n
Building Management Systems

Building Management Systems across the EMEA region are moving beyond automation and evolving into integrated platforms shaped by data‑driven intelligence. This shift comes as the very idea of the “intelligent” building is being redefined by stricter environmental regulation, growing cybersecurity demands, and rising user expectations
n By: Mirza Bahic mirza.bahic@asmideast.com
Building Management Systems are moving decisively beyond their traditional niche. The reason is simple: the old is becoming obsolete, while the alternatives remain too expensive and insufficiently tested. This is most visible in Europe’s residential building stock, much of which is ageing and under
growing systemic pressure. Much of this building stock is now several decades old, fragmented, and dependent on retrofit and renovation. Nor do regulatory frameworks tied to decarbonization, energy performance, and operational transparency favor older buildings; instead, they are accelerating modernization. Building owners today are under pressure not only to upgrade their buildings but also to integrate
systems capable of delivering measurable operational outcomes. By contrast, Europe does not share the greenfield advantages of faster-growing regions such as the Middle East, where BMS systems are built into megaprojects, hotels, airports, medical facilities, and smart cities from the outset. In such environments, digital infrastructure is embedded early, but that advantage also

comes with significantly higher user expectations.
Across the EMEA region, BMS now sits at the intersection of buildings’ operational needs and the rise of information technology capable of supporting them. At the same time, instability in the global energy market has pushed efficiency in the use of utilities and resources to the forefront. This is no longer an abstract environmental issue, but one with direct financial implications, while occupant satisfaction has long since ceased to be a peripheral concern. In this context, BMS is no longer seen merely as a control platform, but as a multi-layered source of intelligence shaping quality of life and the pace of investment in the construction sector.
At the conceptual level, BMS has highlighted a long-standing divide between smart and intelligent buildings. For professionals working with BMS, this difference comes down to the concept of anticipation versus reaction. Valentin Vasile, CEE Digital Energy VP at Schneider Electric, draws a very clear line between the two concepts. “A smart building reacts, but an intelligent building anticipates,” says Vasile. The concept of anticipation is contextual. Vasile illustrates this with a concrete scenario. An intelligent building, for example, will not react only when occupancy sensors hit their thresholds, but can
recognize in advance that occupancy is rising and that a weather change will affect comfort forty-five minutes from now. “It’s no longer ‘Turn the chiller on at 7 AM.’ It’s ‘Based on yesterday’s patterns, today’s weather forecast, and predicted occupancy, we should pre-cool Level 4 by 0.8°C at 6:43 AM for optimal comfort and minimal peak load exposure,’” he says. That shift, Vasile argues, makes a building not only smart but intelligent. At Honeywell, this transition is viewed through the lens of portfolio-wide learning. Dejan Petrović, Senior Sales Manager Balkans/Adria – BMS at Honeywell, emphasizes that truly intelligent systems do not simply optimize a single facility; they identify recurring patterns across




entire portfolios, correlating HVAC, energy, fire safety, and security domains to improve performance at scale.
At Johnson Controls, the emphasis shifts to adaptability. Ilan Yaniv, Senior Digital Solutions Sales Leader at that company, explains that static rule-based automation is slowly giving way to adaptive systems. This is because such systems can proactively identify inefficiencies through fault detection and diagnostics. The focus is not only on anticipation but also on operational agility, reducing dependence on fixed thresholds and pre-programmed responses. Siemens approaches BMS’s evolving role through diagnostics. Saša Matošić, DB Sales specialist LC-AT & Portfolio Sales Professional SI BP Hub at that company, highlights ML-based anomaly detection and pattern recognition as indicators that systems are moving beyond traditional automation. In this framework, intelligence becomes visible when deviations are detected before alarms fire and corrective action is proactive rather than reactive. This means that rule-based automation is no longer sufficient and that intelligence is a multi-dimensional concept that includes anticipation, portfolio learning, adaptability, and diagnostic depth. “The system moves beyond simple automation to become a decision-making platform that adapts to changing conditions, learns from operational patterns, and continuously improves performance without human intervention,” says Matošić.
Yet the industry emphasizes one more important factor: intelligence is only possible where integration is deep. Honeywell positions integration as con-
Perhaps the most significant organizational shift driven by intelligent BMS platforms is a new level of support for the people who run buildings. The BMS previously represented a “silent” infrastructure layer: steady, predictable, and reactive. Today, Vasile argues, it is becoming the thinking layer of the building, and this change begins with data. When thousands of disparate data points are unified into a common semantic layer, the building gains context. Intelligent software turns that raw data into insight, giving operators the clarity they never previously had. Artificial intelligence is fundamentally reshaping the operator’s role. “Instead of reacting to alarms, operators receive interpretations, confidence-based predictions, likely outcomes, and recommended actions,” Vasile explains. They move from firefighting to orchestration, from “What went wrong?” to “What’s the best scenario we can shape?” “AI doesn’t automate the building. It augments the people who run it. It gives them a co-pilot that can see what no one human could track alone,” he says. Johnson Controls applies a similar philosophy through its OpenBlue platform. Fault Detection and Diagnostics brings early fault detection, while AI-powered recommendations shift facility managers from reactive maintenance to proactive optimization. At Honeywell, AI is also being integrated into solutions for predictive insights, automated optimization, and portfolio-level benchmarking. There is also the Buildings Sustainability Manager platform, which uses machine learning to predict anomalies, optimize performance, and support long-term sustainability and resilience goals.
vergence across HVAC, energy management, life safety, security, and IT/OT infrastructure under a unified operational model. Petrović explains that correlating these data streams reveals patterns previously invisible to operators, generating insights that improve performance in real time across the portfolio. Another key element is data aggregation across systems and IoT devices. Yaniv from Johnson Controls highlights the importance of transforming raw signals into actionable insights, moving from monitoring to decision support. Platforms integrate data from BAS, meters, and IoT devices through open protocols while applying advanced analytics. In addition, they use AI to surface recommendations
through dashboards tracking energy management, carbon monitoring, and space performance. However, integration is much more than mere technical unification. For Schneider Electric, it is an operational backbone aligning comfort, carbon reduction, cost efficiency, and resilience objectives. The company’s EcoStruxure platform places building management at the center and unifies HVAC, lighting, blinds, sensors, and energy systems. At the same time, the Power Monitoring Expert function brings energy intelligence into this unified environment. The analytics layers play a central role, turning the building into what Vasile describes as “a coordinated, transparent, self-learning ecosystem.”
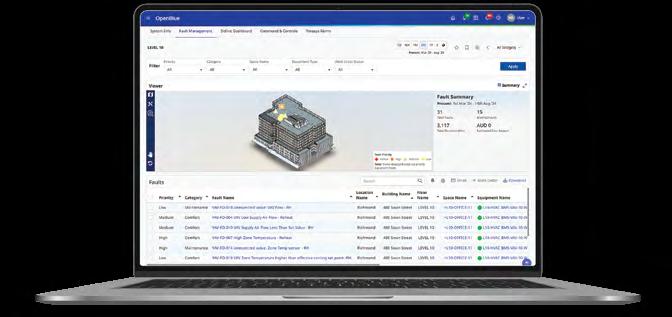
At Siemens, unified dashboards and hybrid cloud deployment models play a similarly important role. They connect HVAC, fire safety, lighting, and security systems under a single interface. Matošić highlights usability and cross-disciplinary visibility as critical to effective oversight, while cloud integration through Building X enables sophisticated analytics and multisite optimization.
Unlike Honeywell and Johnson Controls, which focus on correlation and analytics, Schneider Electric primarily frames integration in terms of outcome alignment, while Siemens delivers operational clarity and user interaction. All in all, integration has become the shared language of the market, even if vendors emphasize different aspects of its role.
At the same time, all respondents agree that digital intelligence without cyber resilience is untenable. While Honeywell and Schneider Electric emphasize control hierarchy, Johnson Controls focuses on cybersecurity architecture. Yaniv describes layered security mechanisms and identity-based controls designed to reduce exposure as buildings become increasingly connected. As an example, he cites their OpenBlue Airwall zero-trust networking solution. It creates a virtual air-gap, making devices invisible to attackers and eliminating lateral movement. As an ad-
AI doesn’t automate the building. It augments the people who run it. It gives them a co-pilot that can see what no one human could track alone
ditional security layer, Airwall also relies on Host Identity Protocol (HIP) and cryptographic IDs for secure, identity-based routing, coupled with AES-256 encryption and multi-factor authentication.
For Siemens, security relies on compliance with IEC 62443-4-2 standards, support for Active Directory, LDAP, and centralized multi-factor authentication. For additional protection of converged infrastructures, there is also the Siemens Cybersecurity Initiative, which aims to protect critical infrastructure, facilities, and networked devices through publicprivate sector cooperation.
For all the foregoing reasons, cybersecurity today is not an add-on to BMS but one of its load-bearing pillars. In Europe, regulatory attention on critical infrastructure protection and data governance continues to grow. In the Middle East, rapid digital adoption in high-profile developments places reputational and operational resilience under scrutiny. In this EMEA environment, cybersecurity is a core design requirement, a view reflected in Honeywell’s holistic audits and targeted controls for converged IT/OT environments. For Yaniv, one of the key vulnerabilities is reliance on VPN systems, which Johnson Controls is today replacing with cryptographically secure identity-based routing.
“This approach protects critical infrastructure and enables secure remote access without relying on vulnerable VPNs or complex firewall rules,” says Yaniv. Ultimately, for most companies offering BMS technology, this is an area where there is no room for compromise.
Energy efficiency remains a primary modernization driver, particularly in Europe, where decarbonization mandates intensify. Yet the story goes beyond kilowatthour savings. Vasile notes that it is often underestimated how much working and residential environments influence cognition. Air quality shapes alertness. Temperature stability affects focus. Light color and intensity influence circadian rhythms. Noise patterns modulate stress levels. What is new today, Vasile believes, is the ability to quantify these effects in real time using so-called comfort metrics — parameters such as indoor air quality, occupancy trends, and workplace performance indicators that can easily be correlated with the building’s environmental conditions. “When you optimize for people, you often optimize for efficiency too. The building becomes an active contribu-

tor to wellbeing and productivity, not just a container for work,” says Vasile. These factors are now readily measurable rather than abstract. “These benefits are measurable today via KPIs such as Tenant Satisfaction Index, occupancy rates, and IAQ scores displayed on dashboards,” says Yaniv. Alongside operational savings, a less visible but equally important factor is the overall improvement in the quality of the occupant experience, with the accompanying growth in productivity and user satisfaction.
For Honeywell, the most important measurable indicators include indoor air quality optimization, thermal comfort stability, reduced false alarms, and improved incident response times, while at Siemens, these outcomes are delivered through the Desigo CC platform for comfort scoring and visualization of ambient conditions within the building. The platform also supports mobile applications, which allow users to report issues and directly adjust comfort settings according to their preferences. BMS intelligence, in this framework, is measured through the feedback loops it creates with the people inside the building. Regardless of differences in approach to priorities, all respondents agree that intelligent buildings must deliver measurable value, with the un-
Instead of reacting to alarms, operators receive interpretations, confidence-based predictions, likely outcomes, and recommended actions
derstanding that value will always be defined differently for each building.
Scaling the concept of intelligent buildings across the EMEA region is a particular structural challenge that no single architecture can resolve in every situation.
The European construction landscape is dominated by retrofit and renovation, requiring phased modernization, interoperability with existing platforms, and compliance with diverse regulatory frameworks.
“Scaling intelligent buildings across EMEA is challenging due to diverse regulatory requirements, varying digital maturity levels, and the prevalence of mixed-vintage, brownfield infrastructure,” says Petrović.
He also emphasizes the importance of a gradual, vendor-agnostic approach, as this allows clients to modernize through roadmaps rather than costly wholesale replacement programs.
His colleague Vasile also highlights that experiences can vary considerably in the
field, particularly in Europe, where each country, and often every city, comes with its own codes, legacy systems, and operational cultures. Some buildings are digitally advanced; others rely on infrastructure that predates the internet. For this reason, the challenge that BMS needs to resolve is not only technical but also regulatory, cultural, and logistical. According to him, ultimate success in adaptation and scaling depends greatly on open standards, adaptable architectures, and strong local ecosystems. There is no one-size-fits-all approach, because every strategy must respect regional diversity and turn it into an operational advantage.
In response to varying digital maturity, Johnson Controls advocates modular, standards-based architectures built on open protocols such as BACnet, Modbus, and MQTT. Siemens, on the other hand, highlights hybrid deployment strategies that balance local compliance requirements (including GDPR data residency obligations) with centralized portfolio oversight. In this way, their Desigo CC

Yet as intelligence layers in building management systems expand, so does the need to draw clear boundaries. All respondents note that life-safety systems must remain deterministic and fail-safe. Dejan Petrović from Honeywell emphasizes that critical fire functions must operate locally and independently, even when cloud connectivity enhances monitoring and compliance processes. The reason is simple: the need for optimization cannot “override” safety logic. Valentin Vasile from Schneider Electric formulates this principle even more directly. According to him, system autonomy must have boundaries, and in sensitive environments, these boundaries matter more than the intelligence itself. Life-safety systems must always override optimization logic, and security functions must retain their independent authority. Schneider Electric’s ecosystem deliberately maintains certified, fail-safe hierarchies. Ultimately, Vasile argues, autonomy is not about giving the building free rein; it is about giving it the capacity to protect itself more effectively and alert humans earlier when something breaks the expected pattern.

Family scales from small installations to large multi-site deployments, while simplified migration capabilities help bridge the gap between legacy infrastructure and modern intelligent platforms. “Standardized interfaces and consistent workflows reduce training requirements,” says Matošić, “thereby addressing the problem of skilled labor shortages, with support for broader adoption of intelligent building concepts.”
Elsewhere in the EMEA region, particularly in the Middle East, integration for scaling purposes can begin as early as the design stage. Yet the scale and complexity of those projects carry their own challenges: cybersecurity expectations, cross-disciplinary coordination, and highperformance benchmarks from inception. As these projects mature from the construction phase to operational lifecycle, the emphasis shifts from deployment speed to long-term operational resilience. This, too, shows that scalability is not a uniform technical challenge, but one shaped by regional, structural, and operational realities.
The evolution of building management systems points in a clear direction. The path from smart to intelligent buildings runs through BMS, meaning that system integration must be deeper, analytics more mature, cybersecurity stronger, and the user experience more measurable. The essence is the same: BMS enables buildings to do more than simply follow rules; it allows them to “collaborate” with operators and align their operation with business objectives.
New and renovated buildings equipped with intelligence-enabled BMS systems will be evaluated on their ability to harmonize data, generate reports, and standardize control over the key parameters of their function. Across the EMEA region, this transition will not be measured by dry technical terminology but by implementation credibility and measurable results. Intelligence as a BMS concept must prove itself through integration depth, safety guarantees, cyber resilience, and measurable operational outcomes. This also marks a broader shift away from simply measuring monthly energy savings and toward a model in which buildings influence productivity and user satisfaction in more meaningful ways. n
SHORT-CIRCUIT PROOF ACCORDING TO CURRENT STANDARD
As data center workloads and power demands grow, short circuits can generate extreme forces within milliseconds. Panduit’s cable restraint solutions, developed and tested according to IEC 61914:2021, help protect infrastructure, personnel and operational continuity
n By: Martin Kandziora, Senior Manager Marketing EMEA, Panduit GmbH Martin.Kandziora@panduit.com
On the one hand, the amount of data to be processed in data centers is constantly increasing, while on the other hand, power consumption is also rising due to the higher performance. A reliable power supply is crucial for the reliability of data centers and buildings. A failure is not necessarily caused by the user or the power supply. The path from the generator to the system harbors risks that should be kept in mind to ensure a reliable power supply. Short circuits are critical for data center availability even after the actual event. Standard-compliant measures for cable installation in the grey space of the data center offer more security and investment protection.
The electrical short circuit leads to a massively increased current flow through low and medium voltage cables in just a few milliseconds. The current strength can be up to 200,000 A in such events. The significant current flow and the resulting increased magnetic field around the cable create dynamic forces due to the interaction of 50 Hz. As a result, the cables are made to vibrate. In the worst case of a three-phase short circuit, the magnetic field-induced impact forces between the cables can be up to 45,000 Newtons and develop within 1/100 of a second. Considerable damage can occur before the circuit breakers can trip on the short circuit. As a result, cable restraint is crucial for protecting personnel and infrastructure and reducing downtime.

Such dynamic forces are absorbed by the cable clamps and the associated cable support system. The cable clamps, which are attached to the support system, prevent individual cables from being torn loose by the vibrations and damaging the electrical installation in the entire data center. Unfortunately, in both new and existing data centers, quick but inadequate cable fastening solutions are still sometimes used. The worst-case scenarios are hard to imagine. Yet it is relatively easy to apply a professional and safe installation solution.
Current-carrying cables in data centers can be laid and secured in different ways. As a structural-mechanical solution, for example, the new cable clamps from Panduit protect against short cir-
cuits and thus significantly increase overall data center safety.
IEC 61914:2021 Edition 3 very precisely documents the test setup that simulates the resistance to electromechanical forces and how the forces on cables and cable holders can be calculated. Panduit’s research and development department uses a modern simulation program to identify how the electromagnetic forces develop in the event of a short circuit and which material composition of the cable clamps is suitable. The virtual observation is ideal preparation for the test in accordance with IEC 61914:2021 Ed. 3. Only after the simulation on the computer are the components subjected to real short-circuit tests in a certified laboratory to confirm that they comply with this standard. Panduit’s research and development engineers use modern simulation software to model the dynamic 3-phase AC short-circuit test. The virtual test takes place over a period of one tenth of a second.
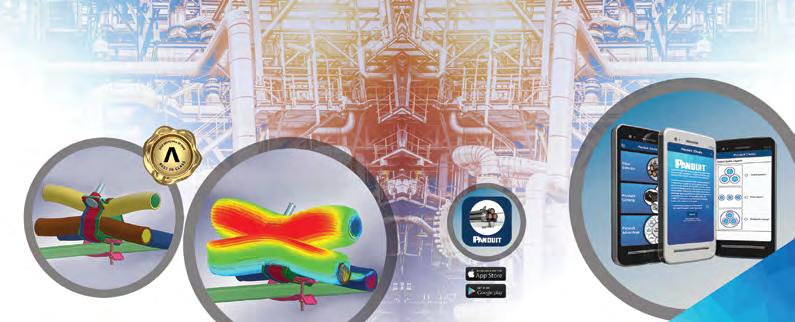
The newly developed product lines of Panduit cable clamps are tested for their short-circuit resistance by the Damstra Lab testing institute in the Netherlands. The peak values of the short-circuit current are very close to those of the simulation.
Overall, Panduit’s research and development department was able to determine the variables involved in the threephase short circuit faster and more accurately. Repeated simulations verified design changes and determined peak current certification levels. In summary, the prototype and test cycle was significantly reduced.
The simulation and the real tests reinforce how fundamental short-circuitproof fastening of live low-voltage and medium-voltage cables is. The IEC defines the cable clamp as a component that secures cables when they are installed at fixed intervals along the length of the cable. In other words: The aim is to absorb static and dynamic forces and hold the power lines firmly in place. In addition, the cables should remain undamaged in the event of a short circuit so that the entire system can be switched back on and continue to be used.
IEC standard 61914:2021 Edition 3 plays a special role in the development of Panduit cable clamps. The standard with the addition “2021 Ed. 3” is the current, most comprehensive and globally recognized requirement for testing cable clamps. Founded in 1955, the American family-owned company meets these stringent requirements so that the cable clamps can safely withstand enormous mechanical forces in the event of a short circuit. In detail: The greatest load during short circuits occurs up to 0.005 seconds before circuit breakers and other protective devices are tripped. The new cable clamps fix cable bundles and ensure that cables remain securely fastened and in place in the event of a short circuit. This provides the best possible protection for the working environment, including equipment and employees, and prevents downtime.
The new cable clamps from Panduit vary in size, design and materials and are suit-
able for a wide range of applications in process plants, information technology and industrial manufacturing. The materials available for the various applications include aluminum, plastic and the highly corrosion-resistant, dual-certified stainless steel 316/316L. The stainless steel cable clamps have folded and rounded edges to prevent damage to the cables. The buckle has its own cable holder and can accommodate cables in quad and cloverleaf formations as well as multi-core cables. Once the cables have been laid, the cable clamp can be attached using a mounting bracket that is unique in the industry. The bracket can be tensioned and cut to length using a hand-operated ratchet installation tool or a tool for tightening a tensioning screw. The straps are often used with a damping sleeve inserted between the strap and the cable for added protection. A plastic buckle is also available for the stainless steel cable ties, as well as various fixing brackets. For example, stainless steel cable clamps are available for cable diameters of 12 to 86 mm in widths of 12.7 to 19.1 mm for short-circuit currents of 45 to 188 kA. Of course, professional tools for quick and professional installation are also available. n
AI-DRIVEN MULTI-ENERGY X-RAY INSPECTION TECHNOLOGY
Across the Middle East, cargo security is undergoing a structural transformation. Trade volumes continue to grow as new ports, logistics corridors, and border infrastructures expand under national development strategies. At the same time, the nature of security risks has evolved. Modern threats are smaller, more modular, and increasingly designed to exploit the limitations of conventional inspection systems
n By: Igor Bondarev/Director/LVS Equipment Trading bondarev@lvs.ae
Authorities today are concerned not only with traditional smuggling, but also with concealed drone components, military-grade electronics, modular weapon assemblies, counterfeit industrial systems, and dual-use technologies embedded within legitimate shipments. These items are often distributed throughout cargo, shielded by dense materials, or positioned to reduce detectability. In this environment, inspection technology must do more than produce high-contrast images. It must generate reliable intelligence under operational pressure.
Most cargo inspection systems historically improved performance along one of two axes: penetration power or viewing geometry. High-energy systems were developed to see through dense cargo, while Dual-View architectures were introduced to eliminate geometric blind zones. While both approaches represent meaningful progress, they typically operate as separate enhancements. Increased energy improves penetration but does not necessarily resolve material ambiguity. Additional viewing angles reduce certain
blind spots, yet complex shielding and layered cargo configurations can still obscure critical details. Modern concealment techniques often exploit this separation precisely. An object that is partially masked in one projection may remain indistinct if energy parameters are not optimized. Conversely, a high-energy scan alone may penetrate deeply but fail to provide the material contrast required for confident classification. Addressing these limitations requires not incremental upgrades, but coordinated system design.
The Multi-Energy X-Ray Array Portal (MEAP) was engineered to integrate geometry and energy into a unified inspection architecture. Instead of alternating between energy levels or relying solely on increased penetration, MEAP employs synchronized, geometrically aligned sources operating at different energies. The resulting data is fused into a single, information-rich inspection output. This simultaneous multi-energy irradiation allows the system to analyze how materials behave across energy levels while being viewed from multiple projections. A structure that appears ambiguous at one energy may reveal distinctive characteristics at another. An object partially
obscured in one projection can be better understood when evaluated using fused energy data from a complementary angle. By coordinating energy diversity with multi-view acquisition, MEAP moves beyond simple imaging toward enhanced material interpretation. The interaction between geometry and energy becomes an active detection tool rather than a passive visual aid.
Another distinguishing feature of the MEAP platform is its development philosophy. In many inspection systems, artificial intelligence is introduced after the hardware architecture has been finalized. In the case of MEAP, the analytical core was defined first, and hardware parameters were optimized to supply the AI engine with the most stable and information-dense data possible.
Detector configuration, energy synchronization, and acquisition timing were designed to support high-confidence algorithmic analysis. As a result, the AI system does not merely assist operators by flagging suspicious shapes; it evaluates material response across fused energy layers and correlates multi-view projections in real time. This approach enhances detection reliability while reducing unnecessary alarms. Operators benefit from more consistent analytical support, particularly

in high-throughput environments where cognitive fatigue can compromise performance. Rather than replacing human expertise, the system reinforces it with structured, data-driven insight.
The current security landscape in the region includes risks that extend beyond conventional contraband. Authorities are increasingly focused on preventing the unauthorized movement of drone platforms, embedded military electronics, precision components, and dual-use technologies that may be concealed within otherwise legitimate cargo flows. These items are often compact and deliberately engineered
to blend with standard industrial materials. MEAP’s multi-energy fusion capability enhances the differentiation between organic, inorganic, and metallic signatures, even within dense or layered shipments. When combined with synchronized DualView geometry and AI-based anomaly detection, this enables a higher level of analytical confidence. In strategic trade environments where the consequences of missed detection can affect national stability and public safety, such a coordinated detection architecture becomes critical.
The Middle East continues to invest heavily in smart ports, modernized
border checkpoints, and integrated logistics zones. Inspection systems must therefore combine performance with long-term adaptability. MEAP’s modular configuration allows deployment across a range of operational environments, from compact checkpoint installations to largescale port infrastructures. As throughput demands increase or threat models evolve, system capabilities can be expanded within the same architectural framework. This scalability ensures that inspection infrastructure remains aligned with both economic growth and evolving security priorities.
Cargo inspection has historically focused on producing clearer images. The next stage of evolution lies in transforming those images into structured intelligence. By integrating synchronized multi-energy sources, coordinated viewing geometry, and an AI-centered analytical core, MEAP represents a shift toward inspection systems designed to interpret—not merely visualize—cargo content.
In an era where threats are engineered to avoid detection, inspection technologies must be engineered with equal sophistication. For regions positioned at the crossroads of global trade, the ability to understand cargo in real time is not simply an operational advantage. It is a strategic necessity.
For more detailed information, please visit https://multienergyportal.com. n
SECUROS VIDEO INTELLIGENCE PLATFORM
Seaports across the GCC are deploying the SecurOS Video Intelligence Platform to unify cargo, vehicle, and security operations, enabling high‑throughput logistics and real‑ time oversight within a single AI‑driven environment
n By: Sandy Issa, Marketing Manager, Middle East, Intelligent Security Systems sandy.issa@issivs.com
Major commercial seaports across the Middle East — including Khalifa Port in Abu Dhabi, King Abdul Aziz Port in Saudi Arabia, Old Doha Port in Qatar, and Sohar Port in Oman—manage immense volumes of containerized cargo, vehicle traffic, and cross-border logistics operations. As vital hubs of regional commerce, these ports process millions of containers annually and coordinate thousands of truck movements each day, highlighting the importance of efficient intelligent infrastructure management. To streamline security and operational efficiency, these ports have implemented a fully integrated solution powered by the SecurOS Video Intelligence Platform, which unifies multiple AI-driven modules into a centralized command system. Key components of the platform include a variety of SecurOS modules, including Enterprise (VMS), FaceX, Auto, UVSS, Cargo, and Cargo Terminal, delivering advanced monitoring and analytics capabilities.
Port authorities faced a range of operational and security challenges, including high
traffic volumes that caused congestion at entry and exit gates, as well as limitations in manual inspections, which led to delays and increased the risk of human error. At the same time, security threats such as smuggling, unauthorized access, and vehicle-based risks remained a constant concern. These issues were further compounded by a lack of integration between key systems, including video surveillance,
access control, and cargo management platforms, resulting in limited visibility into cargo movement and container tracking.
The deployed system was based on a layered architecture, comprising an edge layer with cameras, UVSS scanners, and sensors installed at entry and exit


The project’s success was driven by a unified platform approach that replaced fragmented, multi-vendor environments with a single ecosystem, as well as the adoption of AI-driven automation to reduce reliance on manual processes
points; a processing layer powered by AI analytics for facial recognition, vehicle identification, and cargo analysis; and a platform layer built around the SecurOS VMS, which unified all modules. This was complemented by an integration layer connecting the system to terminal operating systems (TOS), access control, and customs platforms, as well as a centralized command center for monitoring and control. All modules operate within a single unified interface, enabling operators to manage both security and logistics simultaneously.
The implementation was carried out across multiple port gates and cargo terminals. The system was seamlessly integrated with existing customs and lo-
gistics platforms, enabling efficient data exchange and coordination. A phased rollout approach was adopted to avoid operational disruption, while comprehensive training programs were delivered to both operators and security personnel to ensure effective system use and long-term sustainability.
The deployment delivered significant results and operational impact across multiple areas. Security was enhanced through complete vehicle inspection coverage, improved threat detection, and full traceability of vehicles, drivers, and cargo. At the same time, operational efficiency increased as vehicle processing times at entry points were reduced, eliminating the need for manual data
entry and enabling faster cargo clearance and turnaround. Throughput was also improved, with a continuous flow of trucks, higher gate capacity, and reduced congestion, supported by a system designed to scale with future expansion. In addition, real-time dashboards and analytics enabled data-driven decision-making, providing both live operational insights and historical data for audits and performance monitoring. Finally, seamless integration across security, logistics, and access control systems created a unified platform, reducing silos and overall operational complexity.
The project’s success was driven by several key factors, including a unified platform approach that replaced fragmented, multi-vendor environments with a single ecosystem, as well as the adoption of AI-driven automation to reduce reliance on manual processes. The system’s scalability enabled it to efficiently support large and complex port operations, while its interoperability ensured seamless integration with third-party and legacy systems. n
Intelligent search reflects a practical evolution in how video is used during investigations. Rather than changing what security teams do, it changes how quickly and confidently they can do it. By simplifying review workflows and reducing manual effort, intelligent search helps teams manage investigation workloads more effectively
n By: Hassan Makki, Area Sales Director, Genetec info@genetec.com,
In a security operations center, operators are often asked to review hours of video surveillance footage to understand incidents that lasted only minutes. Investigations typically involve switching between camera views, aligning timelines, and manually scanning recordings inside a video management system (VMS) to reconstruct events. This approach is time-consuming, especially when operators are managing multiple cases at once. Modern video management systems are now incorporating metadata indexing, analytics, and natural language search. These capabilities change how operators interact with recorded video. Instead of manually scanning timelines, teams can narrow results based on visual attributes, movement, or contextual data, making investigations more efficient.
This new generation of search capabilities helps operators locate relevant footage faster, and results are presented in a way that supports investigative workflows. In-

stead of relying solely on timestamps and camera names, operators can describe what they are looking for or center the investigation on a person or vehicle of interest captured on screen. For example, an operator might enter the query “find a black car between 8 am and 8 pm.” The system scans recorded video and returns a subset of relevant thumbnails and their associated recordings that match the description. Rather
than reviewing every camera manually, the operator starts with a smaller, more focused set of results.
Let’s say a vehicle is reported stolen from a parking lot. Traditionally, an operator might begin by reviewing footage from the nearest camera and then work outward

Modern video management systems are now incorporating metadata indexing, analytics, and natural language search. Instead of manually scanning timelines, teams can narrow results based on visual attributes, movement, or contextual data
to determine when the vehicle entered and exited the area.
With intelligent search, the operator can begin with a description of the vehicle or select it directly on screen. Entry and exit detection helps establish a clear timeline. If the driver exits the vehicle, the operator can search for that person and follow their movement across multiple cameras using similarity search, even as lighting conditions or camera angles change.
Related clips are connected into a single investigative view, making it easier to understand what happened before, during, and after the incident. What once required extensive rewinding and crossreferencing becomes a more guided process that can be completed in minutes rather than hours.
Many search tools return results based on fixed criteria. Intelligent search adds value by incorporating context into the investigation process. If an operator is focused on a person, the system can surface other recordings that feature individuals with similar characteristics. If a vehicle is the focus, it can highlight activity that occurred nearby or around the same time. This helps operators connect events that might otherwise appear unrelated. By enabling natural language search, intelligent search reduces reliance on complex filters and detailed system knowledge. Operators can concentrate on understanding events rather than managing the mechanics of the search.

Faster access to relevant footage has a direct effect on incident response. When operators can establish timelines and identify key moments more quickly, they can escalate issues, share evidence, or close cases with greater efficiency. This applies not only to major incidents, but also to the routine investigations that make up much of daily security work. Shorter review cycles help teams keep pace with demand and maintain consistency across shifts. Clearer investigative outputs also support better collaboration. When findings are easier to interpret and share, coordination with facilities teams, management, or external partners becomes more straightforward.
Training and onboarding are other considerations. Learning traditional video review workflows can take time, particularly in complex environments. Search tools that support everyday language and simple visual interaction help lower that barrier. New operators can contribute sooner, while experienced staff benefit from workflows that reduce repetitive review and highlight what matters most. Over time, this supports a security operations center that feels more controlled and less reactive.
Intelligent search reflects a practical evolution in how video is used during investigations. Rather than changing what security teams do, it changes how quickly and confidently they can do it. By simplifying review workflows and reducing manual effort, intelligent search helps teams manage investigation workloads more effectively. The technology works best when it remains in the background, supporting human judgment and helping operators make informed decisions. n
Mobile credentials are slowly becoming the new standard in access control. Their growing adoption is shaped by security rather than convenience, reducing long‑term operational costs, and the need to support hybrid environments where mobile and physical credentials coexist
n By: Sam Cherif, Senior Director, Middle East & Africa, HID PACSGlobalMarcom@hidglobal.com
The debate over whether mobile credentials represent the future of physical access control is effectively over. According to HID’s 2026 State of Security and Identity Report, 74% of organizations have either already deployed mobile credentials (36%) or are actively planning to do so (38%). That is an infrastructure decision being made right now across the majority of enterprise environments, and it changes the nature of the conversation that security integrators and distributors need to be having with their clients.
What is shifting is the reason organizations are making that decision. In previous years, user convenience dominated the adoption argument. The 2026 data tells a different story: security improvements now lead as the primary driver at 50%, with user convenience trailing at 34%. Clients are no longer buying mobile access because it is easier. They are buying it because they believe it is more secure, and they are looking to partners who can substantiate that belief with architecture and evidence. Mobile credentials operate through encrypted communication channels and mutual authentication protocols that physical cards cannot replicate. A credential on a device cannot be cloned the way a proximity card can. Access rights can be updated remotely, in real time, and former employees can be deprovisioned the moment they exit the organization.
Wallet-based credentials extend this further. Where mobile access once required a dedicated application, wallet credentials allow organizations to issue, manage, and revoke access through the same infrastructure employees use for payments and travel

The value of mobile credentials scales with how comprehensively they are deployed, and scoping that at the outset is where the strongest deployments begin
documents. Lifecycle management becomes immediate: new hires are provisioned before day one, access rights are updated as roles change, and employees are removed without a card to collect. For organizations operating across multiple sites or in
regions with high device penetration, wallet-based credentialing is a deployment model that is operationally lean and straightforward to scale.
The deployment reality is more complex than a clean migration would suggest, however. The majority of end users (84%) report maintaining a mix of mobile and physical credentials. This reflects genuine operational diversity: visitors and contractors often require physical credentials, and environments where a visible badge serves a compliance function cannot rely only on a smartphone screen. Integrators who approach mobile deployments as a binary replacement exercise will find themselves solving the wrong problem. A mobile credential that covers the main entry but requires a separate card for secure printing, parking, or time-and-attendance is not a mobile access system. It is a partial deployment with two parallel administrative overheads. The value of mobile credentials scales with how comprehensively they are deployed, and scoping that at the outset is where the strongest deployments begin.
The remaining barriers are worth addressing directly. Cost sensitivity has intensified: 44% of end users now cite perceived implementation costs as their primary obstacle, up from 24% the prior year. This rise reflects economic pressure and insufficient ROI communication from the security industry. A mobile


Clients are no longer buying mobile access because it is easier. They are buying it because they believe it is more secure, and they are looking to partners who can substantiate that belief with architecture and evidence
credential system eliminates card stock, printing infrastructure, and the overhead of managing lost or expired credentials. Integrators who lead with total cost of ownership analysis rather than upfront pricing will find the conversation changes. About 37% of organizations also cite a lack of in-house expertise as a reason for not progressing. That gap will not close internally in the short term. It is a gap the channel is positioned to fill. Finally, 80% of respondents expect a mostly mobile or balanced credential environment within five years. Organizations have already committed to where they are heading. The integrators who will earn long-term relationships in this market are those who help clients navigate the path competently, with architecture thinking, honest cost analysis, and the capability to deliver environments where mobile and physical credentials coexist without compromise. The window to establish that positioning is now: clients evaluating deployment today are setting infrastructure standards their organizations will operate within for the next decade. n
By eliminating cables, extending battery life, maximizing coverage, and leveraging AI to reduce inefficiencies, Reconeyez offers a low total cost of ownership that aligns perfectly with the demands of the Middle East market—where protecting vast, high‑value assets must be both effective and economically sustainable
n By: Andy Keeley, Marketing Director, Reconeyez andy.keeley@reconeyez.com
In regions where security risks intersect with vast, often remote assets, the total cost of ownership has become a defining factor in selecting intrusion detection technology. Across the Middle East—where construction megaprojects, energy infrastructure, and national assets span large and often harsh environments—solutions must deliver not only performance, but also long-term cost efficiency. Intelligent systems such as Reconeyez are part of this shift by combining advanced AI with a fundamentally lowcost deployment and operational model.
Traditional security systems often carry hidden costs. Trenching for power and network cables, ongoing maintenance visits, and frequent false alarms all add up over time. Reconeyez addresses these challenges directly through a fully wireless architecture. With no need for power or network cabling, installation is faster, less disruptive, and significantly more costeffective—particularly in remote or tempo-

Across the Middle East—where construction megaprojects, energy infrastructure, and national assets span large and often harsh environments—solutions must deliver not only performance, but also long-term cost efficiency
rary locations such as construction sites or desert-based infrastructure. This eliminates one of the largest upfront expenses and makes it viable to secure areas that would otherwise be cost-prohibitive.
Substantial Savings in Labour and Logistics
Battery performance is another major contributor to the total cost of ownership. Re-

With no need for power or network cabling, installation is suitable in remote or temporary locations such as construction sites or desert-based infrastructure
coneyez devices are optimized for efficiency, offering up to 400 days of battery life on a single set. This dramatically reduces the need for maintenance visits, which can be both time-consuming and expensive—especially when sites are difficult to access. When paired with Reconeyez solar panels, the system can achieve near-continuous operation throughout the battery lifecycle. For organizations managing multiple remote sites, this translates into substantial savings in both labour and logistics. Coverage efficiency further enhances cost effectiveness. With a detection range of up to 35 metres—longer than typical short-range solutions—Reconeyez requires fewer detectors to secure the same area. Fewer devices mean lower hardware costs, reduced installation time, and simplified system management. This is particularly valuable in large-scale environments such
as oil and gas facilities or critical national infrastructure, where perimeter distances can be extensive.
These hardware and deployment efficiencies are complemented by Reconeyez’s AI-driven capabilities. By accurately distinguishing between real threats and environmental noise, the system minimizes false alarms. This reduces unnecessary callouts and allows security teams to focus only on verified incidents, improving operational efficiency and lowering ongoing monitoring costs.
In construction environments, where sites evolve rapidly and budgets are tightly managed, the ability to deploy a fully wireless, long-lasting, and wide-coverage system offers immediate financial benefits. Equipment can be protected without
investing in permanent infrastructure, and systems can be easily relocated as projects progress.
For critical national infrastructure and oil and gas operations, the financial impact is even more pronounced. Reduced maintenance requirements, fewer devices, and minimal infrastructure needs combine to deliver a scalable, resilient security solution with predictable and manageable costs over time.
Ultimately, Reconeyez demonstrates that high-performance intrusion detection does not have to come with high operational expense. By eliminating cables, extending battery life, maximizing coverage, and leveraging AI to reduce inefficiencies, it offers a low total cost of ownership that aligns with the demands of the Middle East market, where protecting vast, highvalue assets must be both effective and economically sustainable. n
EFFECTIVE SOLUTIONS DRIVEN BY COLLABORATION
By eliminating cables, extending battery life, maximizing coverage, and leveraging AI to reduce inefficiencies, Reconeyez offers a low total cost of ownership that aligns perfectly with the demands of the Middle East market—where protecting vast, high‑value assets must be both effective and economically sustainable
n By: Faisal Mohamed, CEO, ScreenCheck faisal.mohamed@centena.com
When the doors of a new terminal open at a major Gulf airport, passengers rarely think about what it took to secure it. They do not see the months of system architecture work, the thousands of access points, or the biometric identity management layer that verifies who should be there. They experience the outcome: seamless, safe, and invisible. That is exactly the point.
Across the Middle East, physical security has undergone a transformation that goes far beyond better cameras or faster biometrics. For the region’s most ambitious infrastructure programs, from Saudi Arabia’s giga-projects to the UAE’s expanding smart city portfolio, security is no longer procured as a product category. It is designed as a strategic layer, woven into a building’s operating logic from the first blueprint.
The numbers bear this out. The Middle East and Africa physical security market is projected to exceed USD 11 billion by 2027, driven by government mandates, smart city development, and a generational wave of construction. Yet the more telling trend is not the scale of spend, it is the shift in how that spend is being directed.

A decade ago, a large security deployment meant specifying cameras, access readers, and alarm panels from a catalogue, then handing installation to the lowest bidder. Today, that model is largely obsolete for tier-one projects. End users are asking different questions: How does my video analytics platform communicate with my access control layer? If an RFID credential
is revoked at 3 am, how quickly does that change propagate across 40 entry points? These are integration questions, not product questions. Yet many organizations still fall into a tool-first trap, investing in technology before defining what needs protecting and what risks they face. The result: controls that look impressive but do not meaningfully reduce risk. This is closely tied to a second issue: misalignment with business priorities. Not all assets carry equal value, yet many organizations still try
“The projects we are involved in today are defined by complexity, not volume. A client is asking us to help design a system that will still be performing at full capacity ten years from now. That requires a completely different conversation at the design stage, and it requires partners who can be accountable across the entire lifecycle.” — Faisal Mohamed, CEO, ScreenCheck

to protect everything the same way. ScreenCheck has operated in this space for over two decades, watching the inflection point arrive in real time. What was once a distribution model, getting the right hardware to the right integrator, has evolved into something closer to solution architecture: defining system logic before a single component is ordered.
The most persistent challenge in the regional market is not a shortage of technology. There is a shortage of expertise to make that technology work cohesively. Video surveillance, access control, RFIDbased asset tracking, biometric authentication, and alarm management are all mature disciplines in isolation. The difficulty lies in getting them to function as a unified intelligence layer rather than a collection of parallel systems generating siloed data. This gap is most visible in retrofit projects, where organizations attempt to layer modern analytics onto infrastructure never built for integration. It also appears in greenfield developments, where ambitious designs often exceed the implementation capabilities of local teams. A related pitfall is mistaking compliance for security. Frameworks such as ISO or NIST provide a useful baseline, but passing an audit and operating securely are not the same thing. It is entirely possible to satisfy a compliance checklist while meaningful gaps remain in how systems actually perform under real operating conditions. ScreenCheck’s model addresses this directly. By working upstream with consultants and system integrators well before
procurement decisions are made, the company helps define architecture that is achievable, not just impressive on paper. The focus is on what the system needs to do operationally and building backwards from that requirement to the right combination of technologies.
That means asking hard questions about lifecycle: not just whether a biometric access control system works on day one, but whether the integrator deploying it has the training to manage firmware updates, credential database migrations, and hardware refresh cycles over a multi-year contract.
No assessment of the regional security landscape is complete without acknowledging the talent gap. AI-driven video analytics, network-based identity management, and cloud-integrated access control are all areas where regional expertise is still maturing. The rapid pace of project delivery compounds this: integrators are frequently asked to deploy technologies they have limited experience with, on timelines that leave little room for on-the-job learning.
The consequences are not always immediately visible. A poorly integrated biometric system may appear functional at handover but degrade under real-world load. An access control network with inadequate segmentation may reveal vulnerabilities only during an audit. There is also a tendency to over-index on technology while underestimating human and process risk, where weak governance and inconsistent access policies can undermine even advanced platforms. This is where ScreenCheck’s training and ongoing support offering has become in-
creasingly significant. Building technical capability across the integrator community is a commercial necessity for a market being asked to deliver at unprecedented scale and sophistication.
The conversation in regional procurement circles has shifted. Decision-makers are looking beyond specifications and price points, asking instead about long-term performance, vendor accountability, and the quality of post-installation support. The era of buying a security system and largely forgetting about it until something breaks is ending.
What organizations want now is consistency: systems that function identically across multiple sites, platforms that surface actionable intelligence rather than raw data, and partners who remain engaged beyond the installation certificate. That is a meaningful change for a market that was, not long ago, predominantly transactional.
ScreenCheck’s evolution mirrors this shift. The company has moved from product supply toward end-to-end accountability, a model that encompasses design consultation, component supply, integration support, training, and maintenance. It is a more demanding position, but one the market increasingly requires.
The Middle East is building at a scale and speed that has no real precedent in the physical security industry’s recent history. The technology to secure these environments exists. So does the ambition. The variable is execution, and execution, in a market this complex, comes down to who you trust to get it right. n
XPASS Q2 UNVEILED
New QR/RFID reader delivers fast, secure authentication for visitors, contractors, members, and ticket holders—bridging access control and visitor management across offices, manufacturing sites, event venues, and more
n By: Mohamed ElShenawy, Regional Manager, Suprema Middle East m.shenawy@supremainc.com
Suprema’s XPass Q2 is an intelligent QR/RFID reader purpose-built for environments that manage a wide mix of users—from daily employees and longterm contractors to one-time visitors and event ticket holders. By supporting QR codes, barcodes, RFID cards, and BLE/ NFC mobile credentials through a single compact device, XPass Q2 enables organizations to unify physical access and visitor management workflows at every entrance point.
As organizations increasingly manage a rotating population of visitors, contractors, and temporary workers alongside permanent staff, the demand for credentials that are secure, cost-effective, and easy to issue has grown rapidly. The global QR Code Access Control System market was valued at USD 1.2 billion in 2024 and is projected to reach USD 3.5

billion by 2033, with the office segment alone accounting for approximately 40 percent of total market revenue. QR-based credentials are uniquely suited to temporary access scenarios. Unlike physical cards or fobs, QR codes can be generated instantly and delivered remotely via email or SMS—before a visitor even arrives on site. They carry zero
material cost: no cards to produce, program, distribute, or collect. Administrators can set precise time-based expiration, restricting a credential to a single visit, a specific time window, or a defined number of days. Once expired, the credential becomes unusable automatically, eliminating the risk of unreturned badges circulating indefinitely.

Dynamic QR codes—which now represent over 64 percent of the QR market—add an additional layer of security by changing with each use or at set intervals, rendering screenshots or photocopies ineffective. Every scan produces a complete audit trail with time, location, and authentication result, a critical requirement for compliance-driven environments such as manufacturing plants, healthcare facilities, and government buildings.
Today’s access environment extends far beyond traditional office lobbies. Corporate campuses, coworking spaces, manufacturing facilities, logistics hubs, healthcare institutions, and event venues all face a common challenge: securely managing a diverse population of permanent employees, recurring contractors, and temporary visitors through the same entry points. The global Visitor Management System market—valued at approximately USD 1.9 billion in 2025 and projected to reach USD 5.5 billion by 2032—reflects the growing urgency to solve this problem.
XPass Q2 addresses this convergence by processing all credential types— from emailed QR/barcode tickets to RFID cards and BLE/NFC mobile access—through a single reader at each entrance. This eliminates the need for separate devices, dedicated visitor lanes, or additional hardware at every door, reducing deployment cost, wiring
The global QR Code Access Control System market was valued at USD 1.2 billion in 2024 and is projected to reach USD 3.5 billion by 2033, with the office segment alone accounting for approximately 40 percent of total market revenue
complexity, and ongoing maintenance. Whether the use case is a corporate office issuing time-limited QR codes to interview candidates, a manufacturing site credentialing daily contractor rotation, a gym verifying member check-ins, or a stadium processing thousands of ticket holders at peak entry, XPass Q2 handles it all from one device.
Most conventional readers either function as basic QR scanners or add a separate scanner module to existing card readers as an afterthought. XPass Q2 takes a different approach: it was purpose-built from the start as an intelligent reader optimized for QR and barcode authentication. Its dedicated QR scanning module reads codes quickly and reliably at short range—approximately 5 to 15 cm—even in low-light conditions. Clear LED indicators and adaptive audio feedback guide users through the authentication process, improving throughput during peak entry times.
With an IP65-rated, durable design, XPass Q2 is equally at home at outdoor gates, loading docks, and indoor lobbies, giving operators a single device they can deploy confidently across diverse environments.
XPass Q2 integrates seamlessly with Suprema’s open platform ecosystem. Through the BioStar X API and SDKs, as well as the CLUe cloud integration platform’s standard REST APIs, Suprema’s integration partners can build tailored visitor management, ticketing, membership, contractor credentialing, and workforce management solutions on top of XPass Q2. This open architecture enables system integrators and software developers to create end-to-end workflows—from preregistration and credential issuance to real-time access logging and compliance reporting—without requiring proprietary middleware or on-premise servers. n
In large‑scale security and communications projects, compliance often defines procurement, but it does not guarantee performance. The gap between specification and execution remains the point where systems succeed or fail under real operating conditions
n By: Abed Tabbara, Executive Vice President, Hader Security & Communications Systems PR@hscsystem.com
Many systems pass every compliance check and still fail when it matters. In large-scale security and communications programs, compliance has become the default proxy for capability. Technical alignment with specifications, structures, and procurement simplifies evaluation and provides a measurable basis for award. It creates clarity, but it does not ensure delivery. The prevailing assumption is that a compliant solution will translate into a functional system. When put into operation, these outcomes often diverge.
Specifications define scope in static terms. They capture features, thresholds, and configurations, but they do not fully represent system behavior under operational conditions. They also fail to account for interdependency across platforms, environmental variability, or system performance under sustained load.
As system architectures become more integrated, this limitation becomes more pronounced. A solution can meet every
stated requirement and still lack coherence at the system level.
In complex environments, such as multisite surveillance networks or critical communications platforms, this gap emerges quickly. Systems that appear aligned during design validation begin to show instability once real-time data flows, crossplatform dependencies, and user load are introduced.
The distinction between compliance and capability becomes visible during integration and commissioning. This is the point where systems transition from isolated components to a unified

operating environment, and where limitations begin to emerge. Interfaces are activated, dependencies converge, and performance is measured beyond theoretical assumptions.
Interoperability that appeared aligned at the specification stage proves unstable


in operation. Redundancy exists in design but does not translate into effective resilience. Capacity calculations hold under nominal conditions but degrade under real load. None of these outcomes constitutes non-compliance. All of them impact execution.
The issue is not with specifications themselves, but with how they are interpreted. Compliance confirms that the required elements are present. It does not confirm that they will operate cohesively, reliably, or sustainably.
Execution is a separate discipline. It requires translating design into operation, actively managing interdependencies, and validating assumptions against real conditions, not simulated ones. It also demands accountability. Ownership of system performance does not end with documentation; it begins where documentation stops. These factors are rarely visible within a compliance frame-
work, yet they determine whether a system will perform as intended.
Procurement models that prioritize compliance without adequately assessing execution capability introduce a structural risk. This risk is not visible during evaluation. It materializes during delivery, when alignment must translate into operation. At that stage, correction becomes complex, costly, and time-sensitive. The focus shifts from validating compliance to recovering functionality. More critically, the burden shifts to the end user, who depends on the system to perform under conditions where failure is not an option.
The difference between selecting a solution and delivering a system is material. Selection is driven by documentation. Delivery is driven by execution. Bridging the two requires more than conformity to specification. It requires a system-
Systems do not fail at the point of specification. They fail at the point of execution
Bridging the gap between solution selection and system delivery requires a systemlevel approach that considers integration pathways, operational environments, and long-term performance from the outset
level approach that considers integration pathways, operational environments, and long-term performance from the outset. It also requires the ability to anticipate where design assumptions will be challenged and to resolve those gaps before they become operational issues.
At HSCS, compliance is treated as an entry condition, not a measure of success. The approach is structured around execution from the outset. This includes early-stage engineering involvement beyond design validation, active ownership of integration across subsystems, and continuous alignment between system architecture and real operating conditions. In practice, this means identifying integration risks before commissioning, stresstesting assumptions under realistic load scenarios, and ensuring that system performance is sustained, not just demonstrated in controlled environments. This is not an added layer. It is essential. In critical communications and security, systems do not fail at the point of specification. They fail at the point of execution. The distinction between compliance and capability is not theoretical. It is operational and determines whether a system can be deployed, commissioned, and relied upon when required. This is where value is created, or quietly lost long before failure becomes visible. n
INFRASTRUCTURE UNDER PRESSURE
Organizations cannot afford to take risks with their infrastructure. Surveillance systems must be reliable, scalable, and ready to perform under pressure. Equally important is the ability to work with a partner who understands both the technical and operational aspects of these deployments
n By: Corina Denov, Marketing &
Business Development EMEA, Velasea corina.denov@velasea.com
In periods of uncertainty, whether driven by geopolitical instability, economic pressure, or rapid technological change, organizations are forced to reassess what truly keeps their operations secure and resilient. Among the most critical components in this equation is surveillance infrastructure. Far beyond basic monitoring, modern surveillance systems play a central role in protecting assets, ensuring continuity, and enabling informed decision-making in real time.
Today’s environments are more complex than ever. Critical infrastructure such as airports, ports, energy facilities, financial institutions, and largescale commercial developments must operate without interruption, even under heightened risk. In these conditions, surveillance is not simply about visibility; it is about control, accountability, and rapid response. Reliable systems allow organizations to detect threats early, coordinate responses efficiently, and maintain operational oversight across multiple locations.

At the same time, the landscape in which these systems are deployed is evolving. The rise of AI-driven applications and dataintensive workloads is placing increased demands on underlying hardware. Organizations now require infrastructure that
can process, store, and analyze large volumes of video data without compromising performance. This shift has made the quality and reliability of backend infrastructure – servers, storage, and networking – just as important as the cameras and software at the edge.
Compounding this challenge is the reality of global supply chain disruption. Component shortages, particularly in memory and storage, are driving price volatility and longer lead times across the industry. For organizations planning new projects or expansions, delays in securing infrastructure can result in increased costs, missed deadlines, and operational risk. In this environment, the ability to access reliable hardware quickly and at predictable pricing has become a strategic advantage. This is where Velasea positions itself within the market.
Velasea specializes in delivering purposebuilt hardware for surveillance, AI, and edge computing environments, with a strong focus on performance, reliability, and scalability. Through its Iron Link hardware line, Velasea provides systems that are specifically designed to handle the demands of modern video workloads, ensuring consistent performance even in demanding conditions.
With a growing presence across the EMEA and APAC regions, Velasea combines global reach with local expertise. The company supports a wide range of industries, including government surveillance, smart cities, mining, oil and gas, financial services, ports, airports, and hospitality developments. This crosssector experience enables Velasea to understand the unique requirements of each environment and deliver solutions that are aligned with operational realities. Over the past years, Velasea has contributed to more than 500 projects across the EMEA region, ranging from single-site deployments to large-scale, multi-location infrastructures. These projects reflect not only technical capability but also the

A key differentiator for Velasea is its regional support structure. With dedicated teams across the EMEA, customers benefit from timely communication, faster response times, and on-the-ground support when it matters most
ability to execute consistently across different markets, regulatory environments, and operational challenges.
A key differentiator for Velasea is its regional support structure. With dedicated teams across the EMEA and APAC regions, customers benefit from timely communication, faster response times, and on-the-ground support when it matters most. This local presence, combined with global engineering expertise, ensures that projects are not only delivered successfully but also supported throughout their lifecycle. In uncertain times, organizations cannot afford to take risks with their infra-
structure. Surveillance systems must be reliable, scalable, and ready to perform under pressure. Equally important is the ability to work with a partner who understands both the technical and operational aspects of these deployments. By combining high-performance hardware, strong global presence, proven project experience, and localized support, Velasea enables organizations to build surveillance infrastructure that is resilient, future-ready, and capable of supporting their operations, no matter the conditions. In a world where uncertainty is becoming the norm, investing in the right infrastructure is not just a technical decision; it is a strategic one. n
When it comes to security in data centers, cyberattacks very much dominate the headlines. But among the multiple heightening challenges caused by the AI‑driven proliferation of facilities is the threat of physical security failures. Peter Dempsey from Axis explains how data center growth is transforming security needs
n By: Editorial, a&s Middle East editorial@asmideast.com
It has been estimated, for example, that one in 10 malicious breaches result from such incidents, potentially costing millions in damages and downtime as criminals, vandals, and activists steal and sabotage equipment and operations. Aside from malicious attacks, the growth in operations results in greater risk of equipment failures, unseen defects, and hazards like fires as rack density increases, further compounded by the decreased presence of human security patrols as data centers become more automated over time. The size of the issue is only set to grow as data center activity accelerates and transforms, amid the rise in both data centers at the edge and large hyperscale facilities.
“Over the past five years, hyperscale data centers have typically ranged from 30 to 60MW per building, but now they’re building and talking about hundreds-ofmegawatt and even gigawatt buildings and campuses,” says Peter Dempsey, Key Account Manager and Data Centre Lead for the EMEA region at Axis Com-

munications. “The scale of these facilities is off the charts, and data centers are also moving to the edge, bringing new physical security challenges.” Like multiple other areas of data centers, the need to accelerate the provision of physical security is a double-edged sword. On the one hand, it creates a challenge to rapidly build up the watertight systems needed for larger-scale and more distributed facilities. But on the other hand, it
ramps up the pace of innovation to keep up with demands.
Among the trends that he highlights in this area is the need to get cameras to do more through analytics and AI at the edge, while being able to monitor a wider area. “There’s a shift towards more intelligent analytics for security, with Axis

“Designers are looking to design buildings now around technology that they predict will come out in the next two or three years”
pushing both hardware and platform innovation,” says Dempsey. “We’re seeing a lot more convergence between the physical and IT world.
That opens up many more opportunities, even though there are also more challenges and risks associated with it.”
Axis pursues what it calls a “multi-layered” approach to physical security, with comprehensive services for all areas of a data centre that enable the provision of a holistic overview and also allow premises to be monitored with fewer human patrols. The company identifies five basic layers, starting with the facility’s perimeter, followed by the area inside the main gate, access areas and systems, individual server rooms, and, finally, the server rack. “When we talk about the security landscape, we go all the way from the perimeter to the rack,” says Dempsey. “We’re originally associated with being a camera manufacturer, whereas we’re actually an end-to-end security supplier.” He adds that providing services and analytics at all different scales is in line with players in the data center industry increasingly seeking lifecycle management options, wanting to know multiple types of information on assets across their lifespans. To illustrate some of the big changes in the industry, Dempsey goes on to describe some of the innovations happening at both the first and final layers of this scale. At the perimeter, Axis is increasingly combining the use of different camera technologies to enable better track-

ing – including a large-scale detection and verification service purpose-built for mega-campus environments. “Traditionally, we used thermal-based camera technology for the perimeter, but we’ve more recently been incorporating our thermal solutions with radar and optical solutions,” says Dempsey. “We have three different technologies working together autonomously at the edge.”
Working in tandem, these systems can better detect intruders and then push information back to the data center’s control center without the need for intervention from an operator.
At the other end of the scale, Axis is getting more requests for in-rack detection products as racks grow in density to boost computing power for AI, creating extra risks from factors like overheating. The company is therefore designing cameras to be put inside racks. “One of the key considerations when it comes to in-rack density is in providing proactive maintenance, identifying when the heat signature of certain electrical components or other parts inside a rack is hitting a point at which we should push out a notification,” says Dempsey. Axis is also creating sensors to perform tasks such as identifying that only employees with authorized access to racks or other equipment in the data center are those who are actually using them, with some
even requesting the deployment of facialrecognition technology for this purpose. Meanwhile, the rapid growth of liquid-cooling systems as a more efficient alternative to air-based cooling brings additional evolving challenges to the data center. There is, for example, a risk that water could pool in certain areas, potentially causing a hazard to people or damaging equipment. “More immersion and liquidcooling systems being brought in means more liquid is coming into the data center environment,” says Dempsey. “Smart analytics running on cameras can identify if water starts to pool in a certain area and send out a command to get somebody to take action.” He adds that data center players are seeking visual verification of faults before they even reach sensors, helping to avoid issues before they become real problems – with large-scale failures not an option in the modern-day data center. “We need to make sure these systems work continuously, while giving an advance heads-up as to when some elements of a system are possibly going to fail,” says Dempsey.
With the data center industry advancing so fast, Dempsey says one key impact is that it is necessary to more rapidly forecast into the future to see what might come next. “Designers are looking to design buildings now around technology that they predict will come out in the next two or three years,” he says. “We’re heavily involved in that design side and the evolving challenge.” As well as that, Axis is learning through partnerships it has throughout the data center industry, giving it the best access to knowledge on potential upcoming trends and technologies. This includes major hyperscalers, colocation players, and designers.
“The rapid growth in the data center industry is reshaping not just capacity requirements, but the physical design and risk profile of modern data centers,” he says. “The field is continuously evolving, and the growth in need for security is exponential.” n
NBOX1 FACILITY
iXAfrica built a highly resilient, carrier‑neutral data center in Nairobi to support East Africa’s digital transformation. By implementing an integrated security approach, the company achieved full visibility, stronger compliance, and a scalable foundation for protecting critical infrastructure as it grows
n By: Sienna Cacan, Enterprise Segment Marketing Manager, Axis Communications sienna.cacan@axis.com
iXAfrica is a carrier-neutral colocation provider focused on delivering world-class digital infrastructure for East Africa. When the company set out to build its flagship facility, NBOX1, the goal was to create a trusted environment for enterprises, cloud providers, and connectivity partners that rely on uninterrupted service and resilient infrastructure.
From the outset, data center security and operational resilience were central to the project. As a greenfield development, iXAfrica had the opportunity to design a comprehensive physical security framework aligned with international standards and customer expectations for transparency, uptime, and risk management.
During construction, iXAfrica identified risks including perimeter intrusion, cable theft, tailgating, insider threats, and potential attacks on critical systems — all significant concerns when securing critical infrastructure. Initially dependent on manned guarding and manual checks, the site

lacked the real-time visibility required for a modern Tier III facility. This made it difficult to respond quickly to incidents and maintain consistent oversight across the environment. To address this, iXAfrica needed an integrated approach combining video surveillance, perimeter protection, and intelligent access control to safeguard operations and support long-term resilience.
To achieve this, iXAfrica implemented a comprehensive, end-to-end solution across indoor and outdoor environments, working closely with Axis and its local partner, Securex Agencies. High-resolution network cameras now monitor the

“The solution provided the integration, reliability, and image quality we needed. The system is cohesive, stable, scalable, and designed to work together.” – Clement Martineau, Co-Founder, IXAfrica
perimeter, entrances, equipment rooms, and operational areas, strengthening situational awareness across the site. Network-based door controllers secure sensitive areas, enforce permissions, and maintain detailed audit trails essential for compliance.
By using a unified Axis Video Management Software (VMS), which manages both video surveillance and access control, iXAfrica can detect potential threats, streamline investigations, and maintain continuous visibility across the facility within a single platform. Built-in analytics further support proactive operations. Motion-triggered recording, door-heldopen alerts, and automated notifications enable faster response while reducing the need for constant manual monitoring. “The solution provided the integration,
reliability, and image quality we needed,” says Clement Martineau, co-founder of IXAfrica. “The system is cohesive, stable, scalable, and designed to work together.”
With improved visibility across the facility, iXAfrica can now verify incidents more quickly and respond with greater accuracy — directly addressing the earlier challenge of limited real-time oversight. Unauthorized access attempts and tailgating events are captured clearly, strengthening investigations and reinforcing physical security controls. This enhanced visibility also allows the team to monitor contractor activity more effectively and reduce the risk of infrastructure theft.

As a result, iXAfrica has strengthened its alignment with global standards such as ISO 27001 and PCI DSS — a critical requirement for organizations managing sensitive data and mission-critical services. A clearer understanding of risk has also contributed to reduced insurance costs. For the security team, this shift has changed day-to-day operations. Instead of relying on routine patrols, personnel can now focus on more strategic tasks, improving efficiency while maintaining strong protection of critical assets.
iXAfrica highlights the importance of collaboration in delivering a reliable and future-ready security strategy. “It has been a smooth and professional experience,” Martineau says. “The support, training, and long-term thinking have been just as valuable as the technology itself.” Sustainability, ethical business practices, and cybersecurity were also key considerations throughout the project. The chosen solution aligned with iXAfrica’s vision for responsible, energy-efficient, and secure infrastructure — supporting both operational goals and broader business values.
As demand for digital services continues to grow, iXAfrica plans to expand the facility with additional halls and operational spaces. The scalable security platform allows new cameras, access points, and analytics capabilities to be integrated seamlessly as the environment evolves. “Our expectations were fully met and, in many ways, exceeded,” Martineau concludes. “The system delivers reliability, stability, and complete visibility across the data centre.”
By investing in a future-ready security foundation, iXAfrica has created a modern, trusted environment that supports East Africa’s digital evolution — giving the team confidence in their ability to scale securely and sustainably into the future. n
With record international participation and a new identity, Intersec Dubai has further strengthened its position as a key hub for the exchange of knowledge, partnerships, and technological solutions for the resilience of modern society
n By: Denver Lobo, Senior Marketing Executive, Messe Frankfurt Middle East denver.lobo@uae.messefrankfurt.com
The three-day event, which celebrated its 27th edition, was held under the patronage of His Highness Sheikh Mansoor Bin Mohammed bin Rashid Al Maktoum, Chairman of the Dubai Ports and Borders Security Council, and welcomed 44,764 trade visitors from 151 countries, with a 60/40 domestic versus international split, reinforcing Intersec’s position as the global meeting point for government authorities, regulators, industry leaders and solution providers shaping the future of security, safety and resilience.
Spanning over 65,000 square metres of gross exhibition space, Intersec 2026 featured 1,180 exhibitors from 56 countries, supported by 10 international country pavilions and a comprehensive programme of 14 conferences and specialist features, reflecting the growing complexity and convergence of physical, digital and human safety and security.
Global participation remained a key feature of the 2026 edition, with 82% of total exhibitors coming from international markets, underscoring the event’s role as a global marketplace. Exhibitor participation was led by the world’s leading markets, including the United States and China; high-growth economies such as India and South Korea; and Europe’s most established industrial and innovative hubs, including France, Germany, Italy, Türkiye, and the United Kingdom.

The 27th edition of Intersec welcomed a record number of international exhibitors and nearly 45,000 trade visitors, representing more than 150 countries, making it the most globally connected edition to date
The United Arab Emirates remained the event’s largest and most influential domestic exhibiting market, reflecting the country’s growing prominence across the global security, safety and fire protection landscape. This momentum is being driven by bold national initiatives that continue to strengthen regulatory frameworks, accelerate the adoption of advanced technologies, and embed resilience, innovation, and convergence across the entire ecosystem.
This leadership was clearly reflected on the exhibition floor, where solutions aligned with national and international priorities were brought to life across five core sectors, including Homeland Security & Policing, Cybersecurity, Commercial & Perimeter Security, Fire & Rescue, and Health & Safety. Together, exhibitors showcased next-generation technologies, integrated systems, and operational solutions that address critical challenges,
including infrastructure protection, emergency response, cyber resilience, workforce safety, and crisis preparedness.
Intersec 2026 marked a significant milestone, unveiling the new Intersec Global identity during a press conference attended by strategic partners and industry leaders. As part of the Global platform, the evolution of Intersec’s sectors reflects a deliberate macro-to-micro narrative, moving from safeguarding nations to protecting individual lives within a unified international framework.
At the macro level, National Security & Resilience supports ministries, police and border authorities shaping sovereign risk strategy, while Cybersecurity underpins digital governance and critical infrastructure protection. This extends into Surveillance & Physical Security for built environments and smart cities, and Fire, Rescue & Emergency Response for civil defence and climate-driven readiness. This culminates at the micro level with Safety & Wellbeing, aligned with ESG priorities and workforce protection, safeguarding people in their daily environments and demonstrating how Intersec Global connects national resilience with human-centred safety across its worldwide ecosystem.
Dishan Isaac, Show Director of Intersec at Messe Frankfurt Middle East: “This edition represents a pivotal moment for the platform, highlighting its expanded scale and the increased engagement from the global safety and security community. The launch of the Intersec Global identity reflects the on-the-ground reality, emphasising an international ecosystem rooted in Dubai, with increasing involvement from both established markets and high-growth regions.
“With a significant increase in international exhibitors and visitors, the quality

Industry achievement took centre stage at the Intersec Awards 2026, held during a prestigious gala dinner in Dubai. Now in their fifth edition, the Awards recognised excellence across 17 categories, celebrating leadership, innovation, talent, and impact in security, safety, and fire protection. Headline winners included Khalid Mubarak of Dubai Municipality, who received the H.H. Sheikh Mansoor bin Mohammed bin Rashid Al Maktoum Emirati Rising Star Award, and Albadr Jannah of Saudi Aramco, named Industry Leader of the Year for his sustained contributions to advancing security and resilience at regional and global levels.
The Women Trailblazers in Security, Fire Safety and HSE award was presented to Jazyah Aldossary, also of Saudi Aramco, recognising her leadership in driving professional excellence, inclusion and safety culture. “Now in their fifth edition, the Intersec Awards highlight the individuals and organisations setting the pace for leadership, innovation and impact across security, safety and fire protection. This year’s winners reflect the depth of talent shaping the industry, from rising Emirati professionals and women leaders to global figures whose work continues to strengthen resilience and best practice worldwide,” concluded Isaac.
of dialogue has been excellent. From strategic policy discussions to frontline operational challenges, the focus has been firmly on real-world resilience, readiness

and collaboration. The breadth of engagement from government authorities, critical infrastructure operators, emergency services and the private sector reinforces Intersec Global’s role as an international platform where meaningful partnerships are formed, knowledge is shared, and industry progress is accelerated.”
The event will return to Dubai from 1214 January 2027 at the Dubai World Trade Centre, continuing to build on its role as the world’s leading platform for advancing safety, security, and resilience across nations, networks, infrastructure, and people. n
With a market exceeding $7 billion, South Korea’s security ecosystem marked the show’s 25th anniversary by demonstrating full convergence between physical and cybersecurity, redefining the role of AI in protecting critical infrastructure and future smart cities
n By: Dženana Bulbul editorial@asmideast.com
As the global security industry faces the fastest technological changes in its history, one theme dominates every conversation: how to build trust in the age of artificial intelligence.
That exact question was at the center of SECON & eGISEC 2026, which opened on March 18 in South Korea and became a focal point for addressing the challenges of the modern security landscape.
“Building Trust in the Age of AI” was not just a convenient event slogan. It articulated the fundamental dilemma the entire industry is currently confronting. On the occasion of its 25th anniversary, the exhibition positioned South Korea as a meeting point of theory and concrete application, where solutions that will define the coming years are already being tested and deployed.
The event’s importance on the global stage is also confirmed by Trevor Clarke, Chief Analyst at Omdia, who sees SECON as an excellent platform for establishing relationships with South Korean companies in both cybersecurity and physical security. According to him, as one of the largest events in the region, it provides an outstanding environment for learning about market trends and technological developments.
Across 28,000 square meters of exhibition space at KINTEX, SECON & eGISEC brought together 412 companies and institutions from 19 countries, with a total of 1,770 booths. The exhibition welcomed 26,389 visitors from 31 countries and regions, including security professionals, managers, decision-makers, procurement leaders, and government officials, as well as more than 100 hosted buyers.
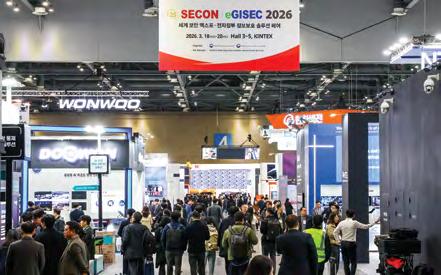
The event also holds the status of “International Certified Exhibition+”, the highest certification awarded by the Association of Korean Exhibition Industry.
At SECON & eGISEC 2026, the boundaries between physical and digital security effectively disappeared. The exhibition presented a full convergence of security solutions, from AI-based video surveillance and access control to critical infrastructure protection,
smart city security, and the protection of autonomous vehicles and maritime traffic.
In the field of physical security, the emphasis was placed on harmonizing video surveillance and biometric access control within advanced cyber monitoring platforms. At the same time, the industry is shifting from


detection to prevention. Sophisticated solutions are now capable of identifying anomalies in real time, including falling, loitering, concealment, and possession of weapons.
Particular attention was given to next-generation artificial intelligence. This primarily refers to Explainable AI, which enables systems to explain why a certain decision was made. At the same time, proactive AI was presented as a model that does not wait for incidents to occur, but instead predicts threats and acts preventively before situations escalate.
This approach was best illustrated by Hanwha Vision, a key player not only in the Korean but also in the global market, which demonstrated how AI theory is being translated into practical security infrastructure. According to the company, the exhibition proved highly productive, with a noticeable increase in enterprise-level clients seeking concrete solutions, as well as industry professionals looking for deployable security infrastructure.
“Interest in AI analytics and workplace safety has never been higher. That was clearly re-
Held across 28,000 square meters at KINTEX, SECON & eGISEC 2026 brought together 412 companies and institutions from 19 countries, featuring 1,770 exhibition booths.
flected in the response to our key product lines, such as the Wisenet 9 chipset, T AI PTZ ruggedized cameras, and AI-based industrial and traffic solutions. We deliberately designed our booth to focus on live demonstrations. Seeing our cameras and AI systems operating in real time allowed visitors to validate the technology on the spot,” says ManGeun Cho, Head of Business in Korea. Engagement exceeded expectations, with visitors moving from general inquiries to in-depth discussions about how AI video surveillance can address specific operational challenges.
“Our presence this year focused on our latest camera lines powered by the next-generation Wisenet 9 chipset. By integrating two neural processing units for AI analytics and image enhancement, this chipset sets a new industry standard in both image quality and intelligence. The response has been outstanding,” Cho adds.

For demanding environments, Hanwha’s AI PTZ ruggedized cameras attracted strong interest from infrastructure and energy sectors due to their reliability under extreme conditions. By combining highly durable hardware with advanced AI analytics, these cameras enable precise object detection and automated monitoring even in the harshest environments, from intense heat to industrial locations with high vibration.
“By showcasing real-time AI capabilities, such as forklift detection, we demonstrated how Hanwha Vision now delivers proactive security solutions that actively protect both critical assets and personnel,” Cho explains.
The company’s strategy is focused on evolving into a comprehensive visual solutions provider, supported by significant investments in AI research and development and the strengthening of its global supply chain.
“Our goal is to expand our international presence by delivering localized solutions tailored to specific industries, such as smart cities and automated logistics, and to strengthen our position in key markets by building long-term ecosystem partnerships,” Cho concludes.
Hanwha Vision places particular strategic importance on the Middle East, which it sees as a key growth hub due to rapid digital transformation and ambitious infrastructure projects. “Our Wisenet 9-powered cameras and AI ruggedized PTZ cameras
are primary growth drivers, as they directly reflect our deep understanding of this environment. Our Wisenet 9 SoC delivers a new level of image clarity and AI precision required for intense lighting conditions and demanding environments typical of the region. At the same time, our ruggedized PTZ cameras are engineered to meet the high durability requirements needed to operate in extreme heat. By combining our specialized regional expertise with these advanced technologies, we aim to remain a key partner in the Middle East’s ongoing transition toward a smarter and safer future across multiple sectors,” Cho says.
Among the companies present at SECON & eGISEC 2026 was CMITech, a Korean manufacturer specializing in advanced biometric technologies, particularly iris and facial recognition systems.
In an interview, Deputy CEO Jay Jeong reflected on the key trends shaping the biometric market. Since its founding, the company has focused on developing highprecision, contactless biometric solutions for identity authentication, border control, access control, and attendance tracking across various sectors.
“Our technologies are currently deployed globally in government, airport, and corporate environments where a high level of security and reliability is required. What sets CMITech apart is our long-standing expertise in iris recognition technology, which is considered one of the most accurate contactless methods of identity verification,” Jeong explains.
In recent years, CMITech has expanded its portfolio by introducing advanced facial recognition with Novaface-3 and multimodal biometric systems EF-70 and EFM-70. These solutions allow users to choose the most appropriate authentication method depending on the application and required security level. “One of the biggest changes in the biometric market is the rapid adoption of contactless authentication technologies. After the pandemic, users increasingly demand solutions that are both secure and hygienic, which has accelerated the adoption of iris and facial recognition,” Jeong notes.
Another key trend is the rapid advancement of AI-based facial recognition technologies. Modern systems can now achieve highly accurate and reliable results even in

The value of the South Korean security market in 2026 is estimated at $7.15 billion, of which cybersecurity accounts for $2.72 billion and physical security for $4.43 billion
challenging conditions, such as outdoor environments and low-light scenarios.
“We are also seeing growing demand from government and border control sectors, especially at airports and within national identity programs where large-scale biometric identification is required. Given the current situation in the Middle East and future prospects for the region, the security market leveraging biometric technologies is expected to continue growing,” Jeong adds.
A similar direction is evident in the approach of KJTech, another Korean manufacturer whose solutions further confirm that contactless biometrics are becoming the global standard. In recent years, the company has increasingly focused on palm vein recognition, which is gaining importance due to its higher level of security and hygienic advantages compared to traditional methods. KJTech has experience across multiple international markets, including Asia and parts of Europe, and has established partnerships abroad. The company continues to expand its international
presence by participating in global industry events, with a particular focus on building partnerships in the European market.
The KINTEX exhibition space also enabled direct testing of future technologies. MONITORAPP used interactive reflex-based activities to educate visitors about Zero Trust architecture, while SAENUN demonstrated realtime smart city security through intelligent kiosks. IDIS attracted significant attention with its Safety CINEMA tour, which simulated fire detection scenarios. The power of AI was further demonstrated by INNODEP and HUNESION, whose systems allow operators to manage surveillance through natural language interaction. CATIS presented advanced hidden-object scanning technologies, while Cudo Communication combined technological innovation with artistic performances and influencer engagement.
While exhibitors such as Hanwha Vision dominated the exhibition floor, the parallel




One of the exhibition’s key strategic focuses was cybersecurity, which is no surprise given that global spending in this sector is expected to reach $311 billion in 2026, with growth of 12 percent, according to Trevor Clarke of Omdia. This figure does not reflect only the increase in threats. It signals a structural transformation of the industry in the age of AI, defined by five key trends. For starters, platformization is accelerating. Clients are overwhelmed by fragmented systems, which is why as many as 70 percent of companies plan to consolidate their security solutions to reduce training and maintenance burdens. Next, sovereignty is becoming a design principle. Geopolitics and regulations such as NIS2 and DORA are reshaping how companies manage data, with data residency becoming a central risk management factor. At the same time, ecosystem economics are evolving. Every dollar invested in technology now generates up to two dollars in services, while within platform ecosystems, this multiplier can reach four. Speaking of new technologies, artificial intelligence is becoming the operational model. AI-driven service delivery is replacing traditional labor-based approaches, with the main challenge being the integration of automation and orchestration into core intellectual property. Finally, the surveillance paradox is intensifying. While AI takes over investigative and reactive tasks, human oversight becomes more important than ever, requiring new governance structures to maintain trust and accountability in high-risk environments.
conference program delivered equally ambitious content, featuring 32 thematic tracks and 159 sessions over three days of intensive knowledge exchange. More than 100 international buyers and
delegates from 18 countries participated in the networking program.
The first day focused on future infrastructure and research and development, the second on artificial intelligence, aviation, and

global cooperation, while the third addressed counterterrorism, privacy, and specialized defense. The program also included specialized sessions by ASIS International and the Asia-Pacific Security Association, linking global trends with regional needs.
In cybersecurity, the focus was on reducing the risks associated with AI misuse, strengthening defenses against phishing, ransomware, and credential stuffing, and developing operational security frameworks tailored to modern organizations.
The activities of companies such as Hanwha Vision, CMITech, and KJTech are clear indicators of the momentum with which the Korean security ecosystem is expanding globally, and the figures confirm this.
South Korea’s security market is today one of the most dynamic and technologically advanced ecosystems in the global industry.
The exhibition once again confirmed that the country not only follows global trends but actively shapes them, particularly in artificial intelligence, cybersecurity, and integrated security systems.
One of the key messages concerns the continued growth of cyber threats. Despite a high level of digitalization and technological sophistication, the Korean market faces constant and increasingly complex cyber incidents. As a result, companies are investing heavily in AI-based defense solutions. At the same time, AI is increasingly used as a potential attack tool, adding further complexity to the security landscape.
The regulatory framework in South Korea is also evolving rapidly. Strengthening laws and policies in the areas of security and data protection is becoming a key response to growing threats, as well as a means of restoring user trust in digital and security systems. Trust itself stands out as one of the central challenges for the industry in the coming period. In terms of market size, South Korea’s total security market is projected to reach $7.15 billion in 2026. Of this, cybersecurity accounts for $2.72 billion, while physical security remains dominant at $4.43 billion. These figures clearly show that, despite the rapid growth of digital threats, traditional segments such as video surveillance, access control, and physical protection continue to play a central role, while increasingly integrating with advanced IT solutions. n

Secutech Taiwan
Key Security Events in 2023
22–24 Apr, 2026, Taipei, Taiwan Nangang Exhibition Center https://secutech.tw.messefrankfurt.com

GISEC GLOBAL
5–7 May, 2026 Dubai, UAE Dubai Exhibition Center https://gisec.ae

ISNR

The Security Event
28–30 Apr, 2026 Birmingham, UK NEC https://www.thesecurityevent.co.uk
Intersec Shanghai
7–9 May, 2026, Shanghai, China National Exhibition and Convention Center https://intersec-shanghai.hk.messefrankfurt.com
19–21 May, 2026, Abu Dhabi, UAE ADNEC Center www.isnrabudhabi.com

Security Essen
22–25 Sep, 2026 Essen, Germany Messe Essen
https://www.security-essen.de

World Police Summit 23–25 June, 2026 Dubai, UAE Dubai World Trade Center https://worldpolicesummit.com OKT SEP

ISAF
7–10 Oct, 2026, 2026 Istanbul, Turkey Istanbul Expo Center https://www.isaffuari.com
















































































































































Vendor-neutral Physical Security Information Management (PSIM) Bosch empowers you to build a
Advancis Middle East
P.O. Box 73309
Abu Dhabi, United Arab Emirates
Tel. +971 2 444 2503
Email: info@advancis.ae
Web: https://advancis.net


www.assaabloy.com/ae/en patricia.lomboy@assaabloy.com
Man Guarding
Technical protection
• Video surveillance
• Access control
• Intrusion detection
• Item theft protection
• IP and network solutions
• Perimeter protection
• Fire detection
• Gas detection
Mechanical protection
Cash/valuables-in-transit
Cyber security
Digital forensics
Software solutions
Smart home
Internet of things
Security management
Investigations
Building management
Market research
Legislation and standards







Physical Security
• Video surveillance
• Access control
• Intrusion detection
• Item theft protection
• IP and network solutions
• Perimeter protection
• Fire detection
• Gas detection
Mechanical protection
Cyber security
Digital forensics
Software solutions
Smart home
Internet of Things
Security management
Investigations
Building management
Market research
Legislation and standards