THE NEXT DECADE: ACCELERATING OUR CYBER DEFENCE_
WELCOME TO CYBERUK 2026!
Ten years ago, the National Cyber Security Centre (NCSC) was born from a simple and ambitious vision: to make the UK the safest place to live and work online. Over the past decade, we have built resilience, confronted fast-evolving threats, and forged partnerships that strengthen our nation’s cyber defences.
And by convening CYBERUK, the NCSC has brought the national security community together. The connections made, debates had and decisions taken have made us collectively stronger. But the challenge is far from over.
In 2026, the question isn’t just whether we can defend against current cyber threats – it’s whether we can accelerate our entire approach fast enough to stay ahead of what’s coming next.
This year’s CYBERUK is both a celebration of the collective progress the community has made and a spur to action.
We are bringing together leaders, practitioners, innovators and visionaries from across the cyber security ecosystem and beyond to address one critical question: How will we accelerate our collective cyber defence for the decade ahead?
The cyber landscape of 2036 will be shaped by the decisions, technologies and collaborations we make today. We must move faster, think smarter and collaborate at a scale we have never seen before.
Our headline plenary sessions will, as ever, feature leaders from across a range of sectors, reflecting on the most pressing issues facing us in cyber security today. From international perspectives on resiliencebuilding to insights into the latest threats, you can expect to hear thought-provoking and diverse views on how we build our collective cyber security.
To make it easier to navigate the agenda and find content relevant to you, we have introduced keywords and the cross-learning threads of Transparency, Recovery and Continuity, AI for Cyber Defence, and Economic Security. Additionally, we have a line-up of Tech Talks delivered by global experts to deep dive into the latest research and perspectives.
No one is in any doubt about the scale of the cyber security challenge, and CYBERUK 2026 provides a forum for the whole national security community, including leading experts from government, industry and academia, to debate the key issues and set the future direction of travel.
A transformative approach is needed for a safer digital world, and that approach begins at CYBERUK 2026.



It’s a pleasure to be bringing CYBERUK back to Scotland and returning to Glasgow for 2026. We last gathered here in 2019, during GCHQ’s centenary year. This return is timely, as the NCSC marks its tenth anniversary this year.
Glasgow has a long history of innovation, with inventors and industries that have shaped developments well beyond the city. Today, that same spirit of imagination and creativity is driving a new wave of innovation, but this time in technology. With a growing reputation as a hub for digital excellence and a vibrant cyber ecosystem, this city promises to be a wonderful setting to celebrate a decade of progress and collaboration.
As a national security community, we should be proud of what we’ve achieved over the past decade. However, we know that in the face of an increasingly complex and diversified cyber threat, we cannot be complacent. That’s why throughout this year’s conference we will
“ Glasgow has a long history of innovation, with inventors and industries that have shaped developments well beyond the city.”
Richard Horne, Chief Executive Officer
be exploring the theme: The Next Decade: Accelerating our Cyber Defence. How can we work together to face the rising challenge in front of us?
I’m excited about the programme we have lined up for you this year. The main stage will bring together leading international voices from across the cyber and policy communities for conversations that both challenge and inspire. One session I’m particularly looking forward to is our keynote from Margaret Heffernan, the author of Wilful Blindness. With so much of cyber security shaped by human behaviour and organisational culture, this offers an opportunity to explore the psychology behind how leaders engage with it.
Our Threat Track dives into the cyber threat landscape in greater depth and breadth. Expect to hear how geopolitics is influencing state actors, cyber criminals, and tradecraft. In the Technology Track, we will be looking at innovations, governance and standards that can accelerate secure digital transformation.

The Resilience Track will be considering how we can advance our defences over the next decade. And our Ecosystem track explores how we grow our future workforce, develop robust standards and assurance, and build a thriving, secure marketplace of services and innovators ready for tomorrow’s challenges.
“Tech Talks” replace our Technical Masterclasses and will connect the CYBERUK audience with the latest technical innovations and developments. Our open call for papers generated a strong response from industry, academia, and government. So much so, that we expanded our agenda to include a wider range of contributions.
You’ll also find hands‑on workshops, high‑energy networking, and access to 150 sponsors and exhibitors showcasing the newest breakthroughs in cyber security. Building on last year’s pilot CISO programme, we’ll be bringing together 150 CISOs from key industries for an exclusive two-day track diving into everything from the shifting threat landscape to maintaining mental wellbeing under increasing pressure.
Throughout the conference, we’ll be joined by cyber security professionals, thought leaders, technical specialists and industry pioneers from across the UK and around the world. Sparking the conversations that truly matter, both on and off the stage. To help you navigate a packed agenda, we’ve curated cross-learning threads, giving delegates clear pathways through our key themes: AI for cyber defence, recovery and continuity, transparency, and economic security.
I encourage you to explore the programme, plan your sessions, and make the most of all the opportunities available across CYBERUK. If you’re anything like me, you’ll find there’s far more on offer than you can possibly attend in person. The good news is that this year, we are improving how we capture and package content from across the conference, making it available online after the event. That means you’ll have the chance to catch up on the sessions you couldn’t make and revisit the ones you enjoyed most.
This event is made possible only through the invaluable support of our sponsors and exhibitors, and I am deeply grateful for their continued partnership.
And lastly, a huge thank you to all of you for joining us as we celebrate our tenth anniversary year. This milestone event is set to bring the community together to inspire, innovate and ignite change.
Richard Horne Chief Executive Officer, National Cyber Security Centre (NCSC)






ENVIRONMENT FOR ALL_
The NCSC is committed to diversity and inclusion and, as the organiser of CYBERUK 2026, is dedicated to ensuring that the event is accessible and a positive experience for all.
CYBERUK 2026 is designed to be an enjoyable and informative event, which fosters a culture of inclusion, and encourages a diverse mix of viewpoints, backgrounds and abilities.
Our priority is for every attendee to feel safe and enjoy an environment of mutual respect. NCSC’s code of conduct. We operate a zero-tolerance policy on any discrimination, hate speech or inappropriate behaviour.
Accessibility
The Scottish Event Campus is committed to making every visit an enjoyable experience for everyone. The venue is easily accessible for visitors with mobility difficulties and accessibility needs. For more information on venue accessibility, click here.
Live captioning will be available for all plenary and track sessions held in the Armadillo. An induction loop system will be available in all content session rooms. Should you require assistance, please do not hesitate to speak with one of our event team members located throughout the venue or at the Information Point in the Exhibition Hall.
Quiet Area Mezzanine
A Quiet Area located at the Mezzanine will be available for those who need time away from the main programme and networking.
Prayer Room
Main Concourse
A Prayer Room will be available throughout the event. Located in the Main Concourse next to Exit 5B.
CYBERUK 2026
At CYBERUK, we are committed to delivering a responsible and environmentally conscious event. Working with venues and our wider suppliers, we are taking meaningful steps to reduce our environmental footprint and champion more sustainable event
Initiatives at CYBERUK 2026
• We track carbon, waste, travel, materials and energy to drive year-on-year improvements in CYBERUK’s environmental performance.
• The Scottish Event Campus aims to be net zero by 2030, powered by 100% renewable electricity. Find out more here.
• All rPET lanyards can be fully recycled. Please return your badge and lanyard to the recycling points at the end of the event. Badges will be securely disposed of.
• We have created a menu with increased plant-based options, and a strong focus on local, seasonal and sustainable Scottish produce.
• Exhibition and event materials are rented, reused or locally sourced where possible to support a circular economy and minimise transport emissions.
• The exhibition hall walkways are uncarpeted, saving 4,120sqm of carpet and avoiding 6.77 tCO2e, equivalent to removing 3 cars from the road for a year.
• Water stations are available throughout the venue to refill bottles.
• We have worked with local public transport providers to offer discounted travel rates.
onboard:earth
We are proud to work again with onboard:earth, specialists in addressing the travel impact of events. Delegates can choose to contribute to environmental restoration projects that help mitigate emissions from travel to CYBERUK.
If you haven’t yet contributed, you can update your registration at any time to donate.
Sponsored by


Who Controls Your Root of Trust?
Modern digital infrastructure relies heavily on cryptographic certificates — securing encrypted services, software updates, connected devices, digital signatures and machine-to-machine communication.
Those certificates ultimately trace back to a Root Certificate Authority: the trust anchor at the top of the system.
As digital systems become more software-defined, more autonomous and more critical to national resilience, control of that trust anchor becomes strategic.
Trust can no longer be assumed or quietly outsourced. It must be anchored deliberately — in structures that are governed, accountable and resilient.
Aretiico
We
Sovereign Control
Root trust established under UK jurisdiction.
Operational Independence
Reduced dependency on hyperscale cloud providers.
Resilience by Design
Infrastructure built to scale, evolve and support future cryptographic transition.
GET INVOLVED AT CYBERUK 2026_
CYBERUK sessions are designed to stimulate conversation. Get involved and contribute to the debates on stage using the Slido web app. Follow the QR code below or visit www.slido.com to join using event code #CYBERUK26.
The password will be available on the screens during content sessions. Please use Slido responsibly, with our inclusion policy in mind. We ask that you submit anonymously or use your first name only.

Follow us on X @CYBERUKevents and share your ideas, thoughts and plans with the community throughout the event: #CYBERUK26.
Subscribe to the CYBERUK ONLINE YouTube channel to view track sessions and CYBERUK content, and to join the conversation in the comments.
Follow us on LinkedIn for 15-minute reminders throughout the event of session start times. Comment on CYBERUK articles and connect with fellow delegates.

VENUE MAP_
GROUND LEVEL UPPER
HALL 5
REGISTRATION / MEETING ROOMS
HALL 4
EXHIBITION HALL
SPOTLIGHT STAGE
LIGHTNING TALKS
HALL 1
TRACK SESSIONS
HALL 2
TRACK SESSIONS
LOMOND AUDITORIUM
TECH TALKS
ALSH
TRACK SESSIONS
BOISDALE
INTERACTIVE WORKSHOPS
LEGEND
TOILETS
LIFT
ESCALATOR
LOMOND AUDITORIUM
TECH TALKS
CARRON
INTERACTIVE WORKSHOPS
DOCHART
SCHOOLS OUTREACH PROGRAMME
MEZZANINE
QUIET ZONE
ARMADILLO
ARMADILLO
PLENARY & SUPER SESSIONS
MAIN ENTRANCE
DELEGATE ROUTE
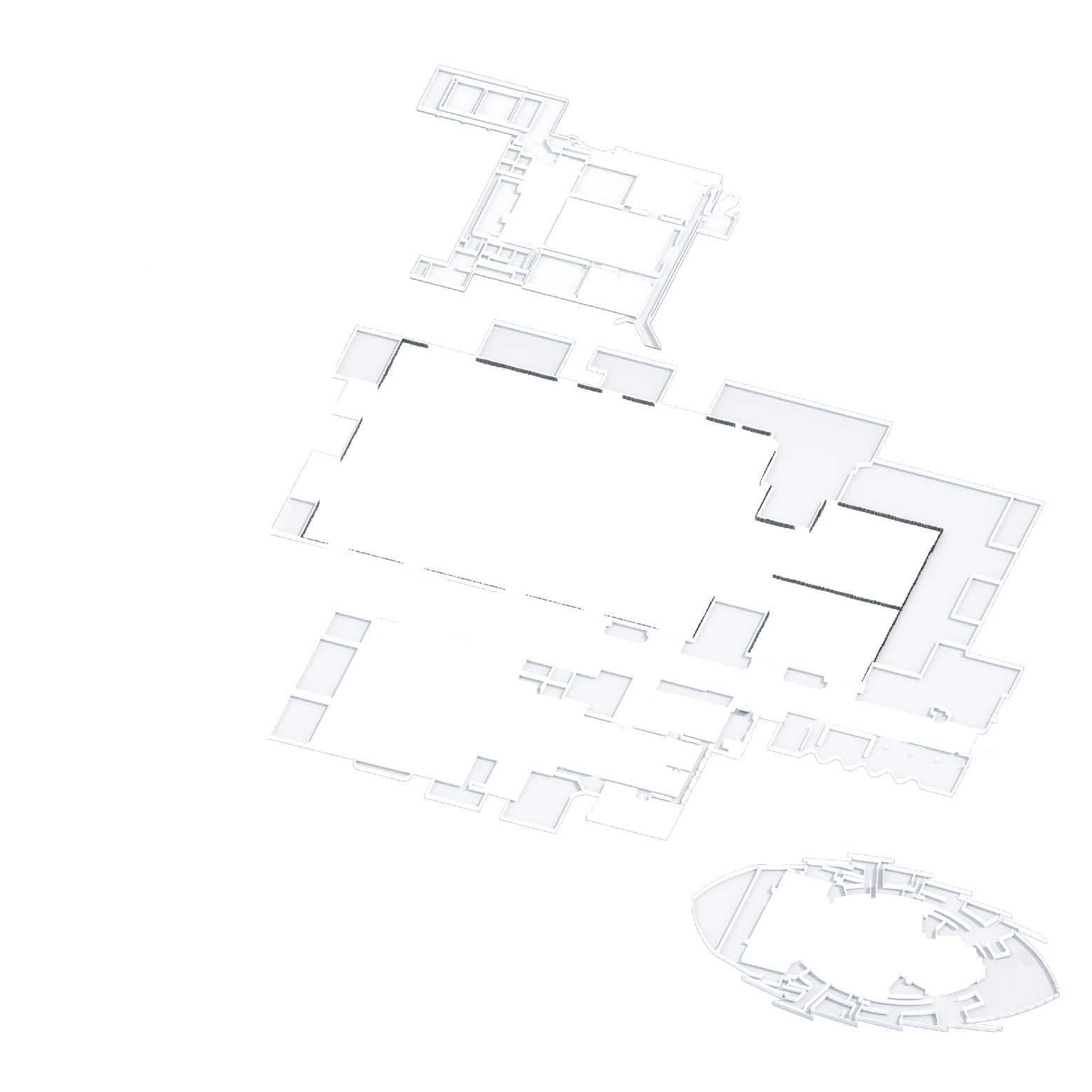
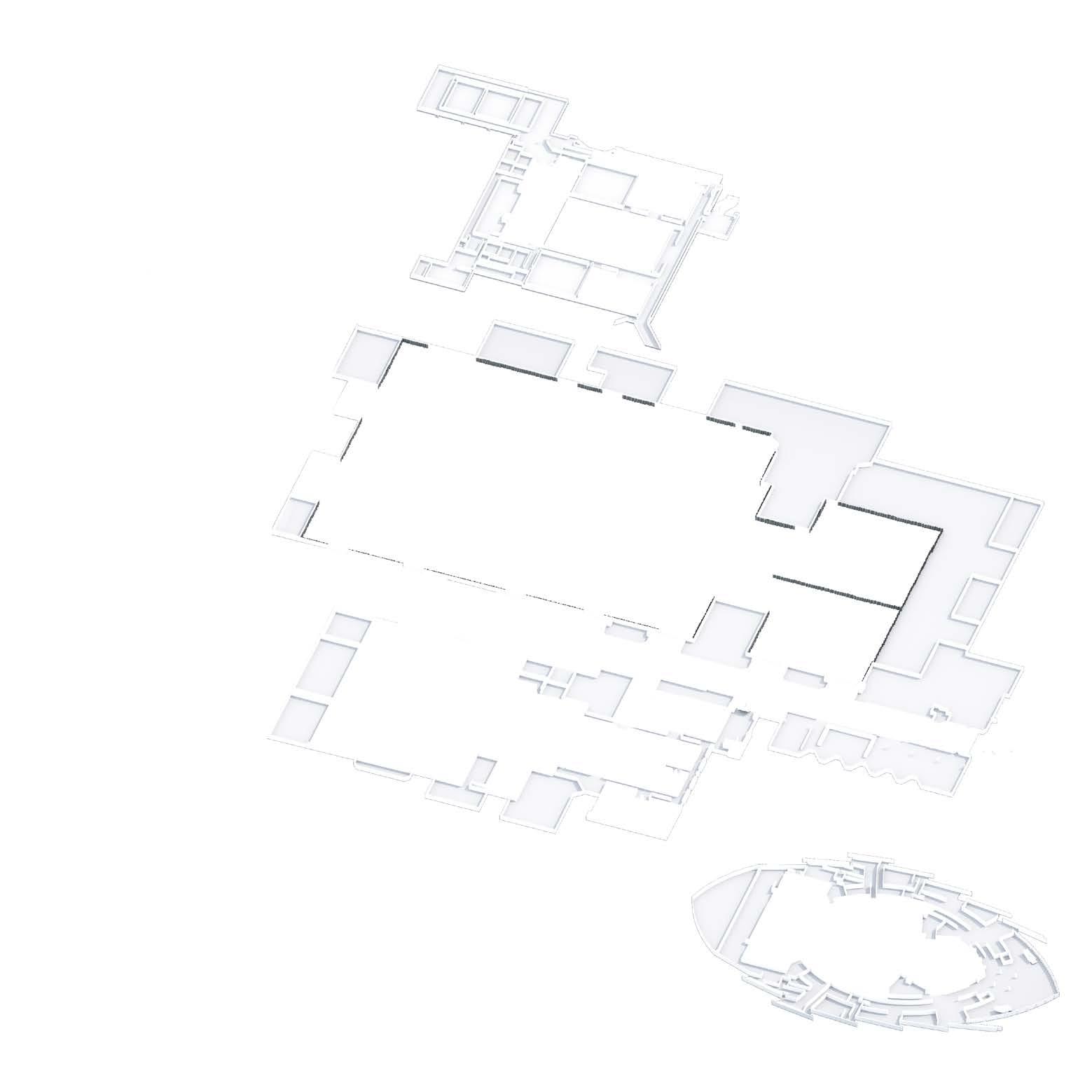
SEC GROUND LEVEL
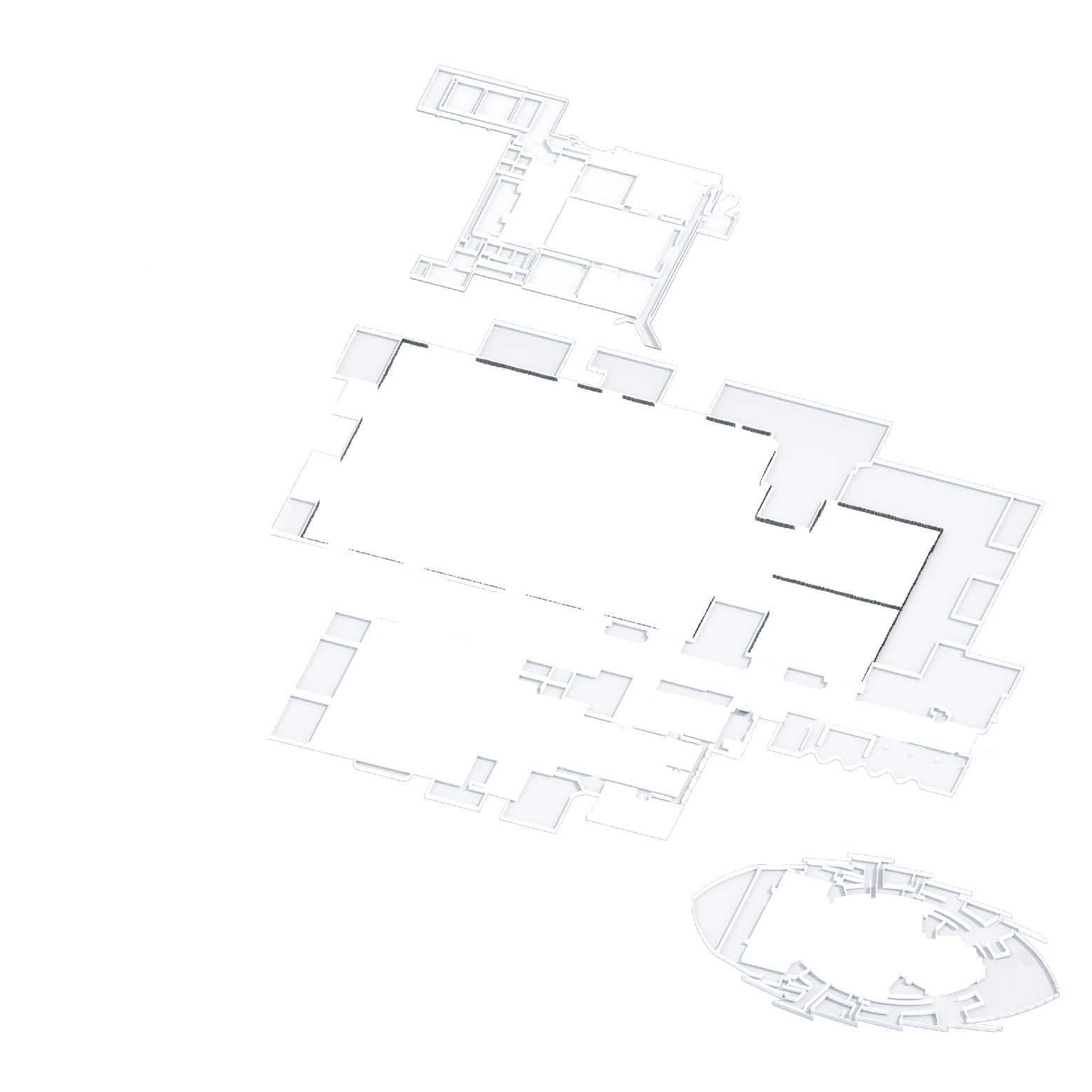
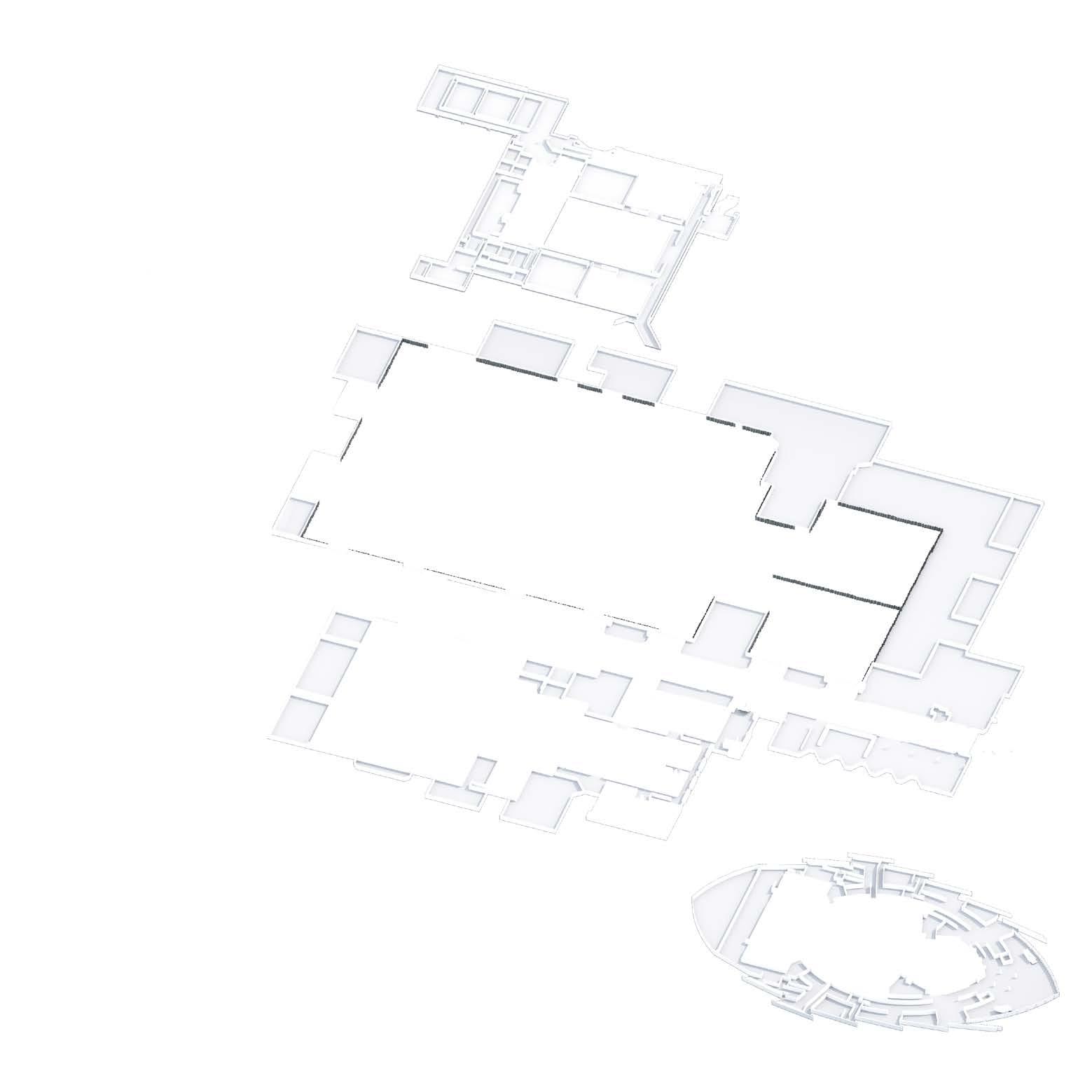
ARMADILLO
NETWORK, MEET AND COLLABORATE AT CYBERUK 2026_
CYBERUK 2026 provides opportunities to develop partnerships and collaborate. Sharing insights and experiences within the community is a huge part of the CYBERUK experience.
Attend networking sessions with leaders and experts in the sector or arrange your own private meetings throughout the event.
Meeting Hub
Exhibition Hall
The Meeting Hub, sponsored by IBM, is a popular feature of CYBERUK.
Designed for private meetings for 2-4 people, spaces can be reserved at the Meeting Hub’s reception desk.

Sponsored by
NETWORKING EVENTS SCHEDULE_
NETWORKING EVENTS
Welcome Drinks (Location details in Delegate Information Pack)
Tuesday 21 April 18:00 – 22:00
Wednesday 22 April 17:15 – 18:45
Thursday 8 May 08:00 – 09:05
Start CYBERUK 2026 in style, reconnect with peers, meet new people and enjoy delicious food and drinks. Open to all delegates. Entry is granted on a first come, first served basis, and capacity is capped at 800 attendees.
CYBERUK Informal Networking Reception (SEC)
Join fellow delegates, sponsors and exhibitors to unwind after Day 1 with networking and drinks held in and around the Exhibition Hall
Women in Cyber Networking Breakfast (SEC)
Open to all delegates, the Women in Cyber networking breakfast is a chance to discuss opportunities to support gender diversity in cyber. Capacity is capped at 180 attendees – arrive early!
CYBERSCOTLAND STREET – NEW – Exhibition Hall
Supported by
CyberScotland Street, supported by the Scottish Government, brings together a diverse mix of organisations; from SMEs, to CyberScotland’s established partners, all with a key focus to enhance cyber resilience across Scotland.
The CyberScotland pavilion, located on the Street in Hall 4, will bring people, organisations and sectors together to network, share knowledge and celebrate innovation in cyber security.


Securing a better future, quicker.

Just like the blades on our windfarms, we never stand still. We’re doubling our efforts to deliver the clean, green power the UK needs — investing up to £24 billion by 2028.
But securing the future isn’t only about clean energy. It’s about protecting the systems, people, and infrastructure that keep the UK moving.
From the 100% green electricity we generate to the communities we support — and the cyber resilient systems that keep it all running — all our energy goes towards building a better future, quicker.
Strengthening the UK’s energy security and resilience
Securing national networks across our partners and supply chain
Come and see us at stand MA3
Innovating a smarter, safer system through digitalisation, AI and data driven operations
Empowering our people and building a future‑ready security culture



Securing Tomorrow, Together Tech Talks Sponsor | Stand C14
Visit out stand to:
Put your security instincts to the test in our ‘Crack the Safe’ challenge
Test the real-world impact of deepfakes in our interactive booth
Hear Extraordinary Stories from experts quietly preventing tomorrow’s headlines
Explore our ‘World-Firsts’ research, where long-held assumptions were challenged
Pick up pre-release insights on global cyber policy, threat intelligence and more
Engage with leading cyber experts to discuss your challenges, priorities and the next decade of cyber defence
CYBER DEN_
Who will emerge victorious from the den?
Alsh Content Room
The Cyber Den gives emerging cyber security businesses the opportunity to pitch their ideas to a panel of industry specialists. The winner will receive assistance for 12 months from the NCSC in assessing, developing and piloting their product or service. This may include consultancy on the technology, targeted VR and the potential of working with a Government Department to test a deployment of the offering. The NCSC will also provide mentoring sessions with the NCSC CTO and NCSC Growth team.

Join us to hear from innovative suppliers competing to win.
Hosted by the Department for Science, Innovation and Technology (DSIT), this year’s contestants will be seeking to impress our cyber ‘Dragons’.
Helen Lovekin, Head of the Office of the CTO, NCSC
Ollie Whitehouse, CTO, NCSC
Lynda McQuilken, CISO, Scottish Power
Adele Tredoux, CISO, Aretiico
Previous Cyber Den winners include Mindgard (2025), Optalysys (2024), ITUS Secure Technologies (2023), CyberHive (2022), MaCRA (2021), Risk Ledger (2019) and Awen Collective (2018).
Hosted by Department for Science, Innovation & Technology


SCHOOLS OUTREACH PROGRAMME_


Designed to inspire the next generation of cyber professionals, local secondary school children are given an opportunity to visit CYBERUK.
The Schools Outreach Programme, sponsored by Accenture, will include a range of interactive talks, challenges and activities designed to inspire and spark interest in pursuing a career in the cyber security sector.
Please be mindful that younger audiences will be in the building each day.
Sponsored by






RECHARGE AND REFRESH_
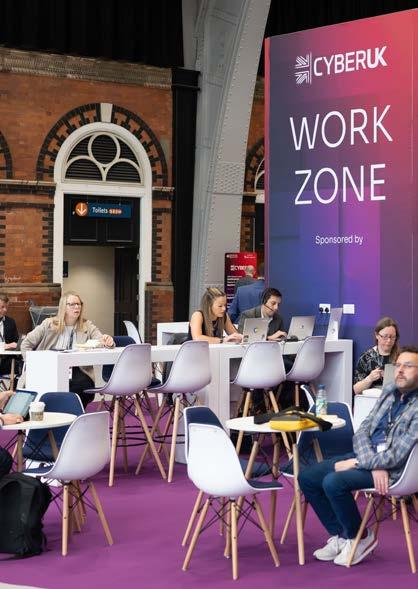
Work Zone
Exhibition Hall
Make the most of your time at CYBERUK – even if that means keeping an eye on emails. Head to our dedicated Work Zone between Hall 4 and Hall 5 to check in.
Barista Bar
Exhibition Hall
Kick start your CYBERUK day with a delicious barista coffee.
Wellness Lounge and Juice Bar
Exhibition Hall
Take a moment to recharge in our dedicated wellness space. With a fresh juice bar and a calm, comfortable setting, it’s an ideal spot to relax.

Sponsored by
Sponsored by
Sponsored by


Powering the Future of Cybersecurity Together
Discover how Cisco and Splunk are revolutionizing cybersecurity with AI-powered threat detection, investigation, and response. Together, we deliver unparalleled visibility and actionable insights across your entire digital footprint.
NCSC ZONE_
Come and meet the team behind the UK’s technical authority for cyber security and discover how they’re working with partners to strengthen the UK’s resilience to evolving threats.
Throughout the conference, NCSC experts will be on hand in the Zone to discuss current threats and risks and mitigations, as well as showcase NCSC guidance, tools and services, and practical advice through interactive demonstrations. Come for an informal chat or join a scheduled session on:
• Protecting against evolving cyber-attacks and hostile access attempts using Zero Trust architectures, passkeys, and Privileged Access Management (PAM).
• Making high value systems defensible by using Privileged Access Workstations.
• Operational Technology (OT) threats are already here meaning designing secure connectivity and system understanding is more important than ever.
• Using Cross-Domain to prevent compromise across security boundaries.
• The role of RF security in identifying, assessing and mitigating risks to sensitive environments.
• Innovations from Initiate’s partners including Goldilock Labs, PenTenAmio and Quantum Secret.
Exhibition Hall – NCSC Zone

Strengthening our Critical National Infrastructure
The NCSC’s Cyber Assessment Framework (CAF) is a set of resources for organisations responsible for securing critical network and information systems to achieve and demonstrate cyber resilience.
The CAF supports organisations that carry out core oversight responsibilities that help defend and protect our Critical National Infrastructure from cyber incidents.
The National Cyber Security Centre (NCSC), a part of GCHQ, is the UK’s technical authority for cyber security. Since 2016, it has worked to make the UK the safest place to live and work online, and to bring clarity and insight to an increasingly complex online world.
Come and speak to our experts at the NCSC Zone.
SUPPORTING INNOVATION AND GROWTH_
Bursary Places
As part of our commitment to increasing access to the cyber security sector for all, we have provided several complimentary and discounted event passes to selected delegates from charities, small businesses and academia.
CYBERUK’s bursary places ensure that attendance at this year’s event is as wide and diverse as possible, and that there is the opportunity for all organisations, large or small, to have a presence at CYBERUK.
Sponsored by

SME Stands
Exhibition Hall
Looking for fresh approaches to threats and resilience? Meet SMEs showcasing ambitious work and creative ideas in this zone.
The SME stands are a collection of smaller firms making a big impact on the future of the industry.

SME Innovation Zone
Exhibition Hall
Which new technologies will shape the next 10 years of cyber? Hosted by DSIT, the Innovation Zone features 12 SME stands focused on the future of our burgeoning industry.
These businesses will also be pitching their products and ideas in the Cyber Den. CYBERUK’s Innovation Zone looks firmly towards the future of the cyber security industry.
Hosted by
Government and Academia Stands
Exhibition Hall
Collaboration is key to building a strong cyber security community. We are proud to welcome some partners from government and academia.
CONTENT OVERVIEW_
The CYBERUK 2026 theme THE NEXT DECADE: ACCELERATING OUR CYBER DEFENCE_ focuses our attention on how we will accelerate our collective cyber defence for the decade the challenge ahead.
All organisations need to play their part in transforming cyber security resilience because it underpins every aspect of our daily lives, and secures our path to growth and prosperity. Our adversaries are increasingly sophisticated, and our collective efforts to counter threats need to not only keep pace, but to outpace them.
At CYBERUK 2026, you can learn first hand from practitioners, experts and leaders about the work and best practices that we can adopt now, and how we can remain vigilant for emerging threats from bad actors to make sure the UK is the safest place to live and work online.
Cross-Learning Threads and Keywords
For 2026, we have been more intentional with session definitions, and have removed the chilli rating of previous years. We have instead introduced keywords and cross learning threads.
On the website agenda you can now search for content by either of these methods to allow you to plan your perfect custom-made programme for CYBERUK 2026.
This symbol indicates sessions that are live-streamed on YouTube. Selected sessions will also be available to watch on YouTube after the event.

PROGRAMME OVERVIEW_
PLENARY_ Lead Sponsors
Five plenaries over two days will bring together UK and international cyber leaders from government, industry and academia to discuss this year’s theme:
THE NEXT DECADE: ACCELERATING OUR CYBER DEFENCE_
TRACK OVERVIEW_
There are the four core content tracks that align to the subject matter areas of Resilience, Technology, Threat and Ecosystem, which focus on policy, debate, challenge and cyber security implications.
RESILIENCE TRACK_
Sponsored by
How can the UK strengthen its resilience to the cyber challenges of the next decade?
This track explores rapid-response frameworks, real-time threat sharing, and the partnerships that can defend our most critical infrastructure – alongside the policy and legislative changes needed to enable defence at pace and scale.
TECHNOLOGY TRACK_
Sponsored by
Technology moves fast – our policy and practice must move faster.
This track examines innovations, governance and standards that can accelerate secure digital transformation. Delegates will explore proven solutions, the trade-offs, and how to embed enduring security for the decade ahead.
ECOSYSTEM TRACK_ THREAT TRACK_
Sponsored by
Our adversaries are agile, adaptive and global.
This track focuses on accelerating our ability to identify, analyse and anticipate threats from state actors and cyber criminals – turning intelligence into defensive advantage. Sessions will share insight into emerging risks and vulnerabilities from leading UK and international experts.
Sponsored by
Strong cyber defence depends on people, partnerships and trust.
This track explores how we grow our future workforce, develop robust standards and trusted accreditation, and build a thriving, secure marketplace of services and innovators ready for tomorrow’s challenges.
INTERACTIVE WORKSHOPS_
Sponsored by

As the cyber landscape shifts, solutions must be shaped in real time. Developed by government and industry sponsors, these 12 sessions explore live challenges, share strategies, and codevelop approaches that strengthen our collective defence at pace. Come prepared to get involved in some truly interactive workshops.
TECH TALKS_ CISO TRACK_ LIGHTNING
Sponsored by
This newly shaped track features a series of Tech Talks; 20 minute advanced briefings on innovation, future technology or a piece of research followed by five minutes of interactive questions. These advanced briefings will provide insight into some of the latest thinking and research into our most pressing current and future technical challenges, and are given by worldclass experts and academics, in person, for experienced practitioners.
A closed track with a series of invite-only sessions designed specifically for the CISO community. They are scheduled to ensure invitees can participate in parts of the main agenda relevant to them, while offering sessions that are crafted and convened by the NCSC for this important cohort of cyber leaders.
TALKS_
Sponsored by
The Lightning Talks take place on the Spotlight Stage in the Exhibition Hall during the morning, afternoon and lunchtime breaks. These are 5-minute, bite-size shots of inspiration, single-speaker, single-idea, solutionfocused practitioner or research-led presentations curated by the NCSC.
PROGRAMME AT A GLANCE_
DISCLAIMER_
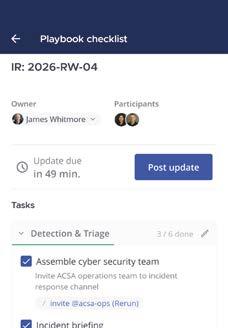
Organisations Keep Running When Trust Is Gone
14:30 – 15:20 INTERACTIVE WORKSHOPS The Future of Cyber Regulation: co-designing CSR Bill implementation and secondary legislation. Collaborative Roundtable
Unique Perspectives: Threat Realities We Should Know And Care About CLOSED SESSION INVITE ONLY
12:20 – 13:50 CISO TRACK
Lunch Networking and Post-Quantum Cryptography: Managing the UK’s Quantum Risk CLOSED SESSION INVITE ONLY
12:00 - 13:00 CISO TRACK We’re All In This Together: How Government and Industry Can Help and Learn from Each Other CLOSED SESSION INVITE ONLY
PLENARY PROGRAMME_
DAY 1 – WEDNESDAY 22 APRIL
NCSC Keynote
Richard Horne, Chief Executive Officer, National Cyber Security Centre (NCSC)
Ministerial Keynote
Senior representative, Cabinet Office and Home Office
Guest Keynote
PL01
Opening Plenary
09:00 – 10:30
Armadillo
Margaret Heffernan, Author, Chief Executive Officer and Professor of Practice, University of Bath
Opening Plenary
Cyber on the Front Line: Protection, Advantage and the Next Decade
As the geopolitical landscape grows increasingly volatile, cyber capability has never been more central to national security. In this exclusive fireside conversation, Anne Keast Butler, Director GCHQ, and General Sir Rob Magowan, Commander Cyber & Specialist Operations Command, reflect on the role of defensive and offensive cyber operations, and what the next decade demands of the UK’s collective cyber capability. A rare opportunity to hear two of the UK’s most senior national security figures speak candidly about the responsibilities, challenges and opportunities ahead.
Speakers
Anne Keast-Butler, Director Government Communications Headquarters (GCHQ)
General Sir Rob Magowan, Commander Cyber & Specialist Operations Command, Ministry of Defence (MOD) PL02
Ecosystem Plenary
11:20 - 12:20
Armadillo
Lead Sponsor Keynote
Richard Parris, Executive Chairman, Aretiico
Ecosystem Plenary
Cyber in the UK’s Industry Strategy: Breaking Barriers to Growth
Already worth over £13.2bn, the UK cyber sector is growing; but so too are the challenges the sector faces. While cyber security is still often undervalued, its significant untapped potential can fuel not only the resilience of the UK but drive innovation and growth across the economy to meet the challenges of the next decade.
Now is the time to invest in our cyber culture, leadership and places to maximise their impact and force change at a systemic level.
We have the talent, ambition and opportunity to lead in cyber security, but how do we align growth with resilience and make strategic choices that benefit the whole economy?
Chair
Chris Ensor, Deputy Director, National Resilience Capability, National Cyber Security Centre (NCSC)
Panellists
Kirsten Connell, Investor, Octopus Ventures
Dr Ali El Kaafarani, Founder and Chief Executive Officer, PQShield, Andrew Elliot, Deputy Director of Cyber Security, Department for Science, Innovation and Technology (DSIT)
Professor Simon Shiu, Professor of Cyber Security, University of Bristol, Senior representative, Trust Elevate
PL05
Threat and International Plenary
15:30 - 17:15
Armadillo
DAY 1 – WEDNESDAY 22 APRIL
Networking Drinks Sponsor Address
Stephen Dane, Managing Director, Cisco Security, Cisco Systems
International Panel
Global Perspectives on How to Stop Threat Outpacing Resilience
To mark our tenth CYBERUK, NCSC will invite – for the first time – a key international partner to chair a plenary panel. Senior international government figures from across the globe will bring their considerable experience to bear to reflect on the last decade, how we got here, where we must change course and what sources of optimism they foresee over the coming ten years.
Threat Plenary
Looking Back, Looking Forward – In Conversation with Chich:
The Evolution of the Cyber Threat
NCSC Director of Operations, Paul Chichester CMG, sits down with author and investigative journalist, Geoff White, to talk all things cyber threat, reflecting on themes from across the threat track. A lot has changed over the last 10 years, but a lot hasn’t – and Paul and Geoff have seen it all. How has the threat evolved, and what factors are driving change? How have we evolved our approach to cyber defence, and how can we stay ahead of the threat?
Speakers
Paul Chichester CMG, Director of Operations, National Cyber Security Centre (NCSC), Geoff White, Author & Investigative Journalist
Chair
David Koh, Commissioner of Cybersecurity, Chief Executive & Chief (Digital Security & Technology), Cyber Security Agency of Singapore & Ministry of Digital Development and Information
Panellists
Rajiv Gupta, Head, Canadian Centre for Cybersecurity
Yoichi Iida, National Cyber Director, National Cybersecurity Office, Japan
Vincent Strubel, Director General, French National Cybersecurity Agency (ANSSI) Senior representative, CERT.LV
Closing Remarks
Darragh McElroy, Director of Communications, NCSC
PLENARY PROGRAMME_
DAY 2 – THURSDAY 23 APRIL
Welcome to Day 2
Beth Hopkins, Chief Operating Officer and NCSC Director Delivery, Engineering and Crypt Key, National Cyber Security Centre
Lead Sponsor Keynote
Nicola Connelly, Chief Executive Officer, SP Energy Networks
PL04
Resilience Plenary
09:10 – 10:20
Armadillo
Resilience Plenary
Secure By Law: How Regulation Shapes the Nation’s Cyber Future
In a panel session facilitated by Jonathon Ellison OBE, participants from across government and regulators will reflect on the role regulation and legislation has on building a secure nation, particularly in our most critical sectors. This plenary will be used to bring together experts on regulation in a candid discussion on recent cyber security legislation, reviewing the impact this has had on organisations and businesses we rely upon.
Chair
Jonathon Ellison OBE, Director for National Resilience, National Cyber Security Centre (NCSC)
Panellists
Natalie Black CBE, Group Director, Infrastructure and Connectivity, Ofcom
Rod Latham, Cyber Security and Digital Identity Director, Department for Science, Innovation and Technology,
Claudia Plattner, President, Federal Office for Information Security (BSI)
Senior representative, Australian Cyber Security Centre
PL03
Technology and Leadership Plenary
15:35 - 17:00
Armadillo
DAY 2 – THURSDAY 23 APRIL
Technology Plenary
Chief Technology Officer Keynote and Technology Panel
A Stitch in Time… What Will Our Future Selves Thank Us for Doing Now?
Many big technology changes take time. It is tempting to put off doing the really hard things and focus on the near term; there’s certainly no shortage of crises and incidents to deal with. What are the actions we can take now that will shape trends, policies and technology evolution for the next decades?
Keynote
Ollie Whitehouse, Chief Technology Officer, National Cyber Security Centre (NCSC)
Chair
Ollie Whitehouse, Chief Technology Officer, National Cyber Security Centre (NCSC)
Panellists
Catherine Day, Founder, National Strategy Project, National Strategy Project
Barbara Grewe, Chief Executive Officer, Glenwood Global Risk Management LLC, Jamie MacColl, Senior Research Fellow, Royal United Services Institute
Senior representative, Cybersecurity and Infrastructure Security Agency (CISA)
Cyber Den Winner Announcement
Carolyn Ainsworth, Deputy Director Chief Engineer, National Cyber Security Centre (NCSC)
Leadership Panel
Leading Through Crisis: Lessons Across Sectors
What does crisis reveal about leadership, culture, and the people at the heart of our organisations?
Richard Horne, NCSC CEO, is joined by Keri Gilder, Colt Technology Services CEO, and Dr. Els Debuf, International Committee of the Red Cross, Head of Delegation for Cyberspace, for an honest, cross-sectoral conversation about leading through the most challenging moments.
From major cyber-attacks to humanitarian emergencies, this session draws on hard-won experience to explore how organisations prepare their people, maintain resilience under sustained pressure, and emerge stronger. Essential listening for anyone responsible for leading teams through uncertainty.
Chair
Richard Horne, Chief Executive Officer, National Cyber Security Centre (NCSC)
Panellists
Els Debuf, Head of Delegation for Cyberspace - Global Cyber Hub, International Committee of the Red Cross
Keri Gilder, Chief Executive Officer, Colt Technology Services
PLENARY CHAIRS_

Deputy Director, National Resilience Capability
National Cyber Security Centre
Chris has worked in Cyber Security for over 30 years in a variety of roles, all of which have involved building new capabilities to help organisations protect themselves. As Deputy Director, National Resilience Capability, he is charged with using NCSC’s expertise and brand to build national cyber security capabilities in education, skills, research, innovation and industry.

Jonathon Ellison OBE
Director for National Resilience
National Cyber Security Centre
Jonathon is the NCSC Director for National Resilience. He formerly served as the interim Policy Director. In his current role, he leads the NCSC’s initiatives to enhance cyber resilience throughout the UK, spanning government, critical national infrastructure, and organisations of all sizes across the economy. He is responsible for the NCSC’s work to build resilience at scale, which includes the NCSC’s Active Cyber Defence Programme.

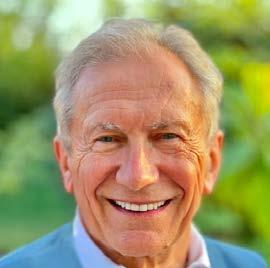
Richard Horne
Chief Executive Officer
National Cyber Security Centre
Richard Horne has been CEO of the NCSC since October 2024. Before joining, Richard was a Cyber Security Partner and chair of the Cyber Security Practice at PwC UK, helping global boards shape cyber risk strategies and led the response to critical incidents. He oversaw the post incident review for the Irish Health Service after the ransomware attack disrupted healthcare services across Ireland in 2021. Richard was Managing Director of Cyber Security for Barclays PLC, responsible for cyber security risk management. In 2011 he went to the Cabinet Office to develop and implement the first national plan for cyber security, impacting both government operations and the wider economy. Richard holds a PhD in Mathematics from Royal Holloway, University of London.

Commissioner of Cybersecurity, Chief Executive & Chief (Digital Security & Technology)
Cyber Security Agency of Singapore & Ministry of Digital Development and Information
Mr David Koh is Singapore’s first Commissioner of Cybersecurity, the founding Chief Executive of the Cyber Security Agency of Singapore, and Chief (Digital Security & Technology) at the Ministry of Digital Development and Information. He also sits on the Boards of the Government Technology Agency, DSO National Laboratories, the Monetary Authority of Singapore Cyber Security Advisory Panel and the Healthcare Cybersecurity Advisory Panel.
Chris Ensor
David Koh

Geoff White
Author & Investigative Journalist
As one of the world’s leading journalists covering organised crime and tech, Geoff White has spent decades investigating the shadowy forces of fraudsters, hackers and money launderers. His work’s been featured by BBC News, Audible, Sky News, The Sunday Times and many more. His latest book, Rinsed, reveals technology’s impact on the world of money laundering. It springs from his work on the hit podcast and book The Lazarus Heist, which explored North Korea’s computer hacking campaign. He has given more than 300 keynote talks for some of the biggest global brands, including Microsoft, HSBC, Sky, Mastercard and Atos.

Ollie Whitehouse
Chief Technology Officer
National Cyber Security Centre
Ollie is a fellow of the Royal Academy of Engineering whose career in cyber security spans over 30 years. Today he serves as the Chief Technical Officer for the National Cyber Security Centre, a role he assumed in late 2023. Prior to joining the NCSC Ollie had an extensive career within the private sector including his most recent roles as Chief Technical Officer at NCC Group, non-executive Director to PortSwigger and Interrupt Labs and advisor to 1011 Venture Capital. Additionally he has held numerous science and technology advisory roles to UK Government. At the NCSC, Ollie is responsible for maintaining the NCSC’s status as the National Technical Authority for cyber security through its people, research and technology impact.
SECURE YOUR ORGANISATION

OPENING PLENARY SPEAKERS_

Margaret Heffernan
Author, Chief Executive Officer and Professor of Practice
University of Bath
Margaret is an entrepreneur, chief executive and author. She writes books and blogs, teaches and mentors leaders, and has built and led organisations of all sizes. She analyses the nature of good leadership with examples from new tech disruptors to established multinationals. She considers the culture of disruptive businesses that have revolutionised the workplace. Margaret writes extensively on effective leadership and culture and challenged many assumptions and stereotypes. She is a Professor of Practice at the University of Bath, chairs the board of DACS, and has advised the Casey Review into the into the culture and standards of the Met Police. She has also consulted on the Independent Inquiry into Child Sexual Abuse.

Anne Keast-Butler
Director GCHQ
Anne Keast-Butler is the Director GCHQ, the UK’s Intelligence, Cyber and Security Agency. Appointed in May 2023, she is the 17th person to hold role and succeeded Sir Jeremy Fleming. Anne, who describes herself as a spy, a mathematician and a mother, joined GCHQ from MI5 where she was Deputy Director General for operational investigative and protective security work.

Richard Horne Chief Executive Officer
National Cyber Security Centre
Richard Horne has been CEO of the NCSC since October 2024. Before joining, Richard was a Cyber Security Partner and chair of the Cyber Security Practice at PwC UK, helping global boards shape cyber risk strategies and led the response to critical incidents. He oversaw the post incident review for the Irish Health Service after the ransomware attack disrupted healthcare services across Ireland in 2021. Richard was Managing Director of Cyber Security for Barclays PLC, responsible for cyber security risk management. In 2011 he went to the Cabinet Office to develop and implement the first national plan for cyber security, impacting both government operations and the wider economy. Richard holds a PhD in Mathematics from Royal Holloway, University of London.

Senior representative, Cabinet Office and Home Office

Genral Sir Rob Magowan
Commander Cyber & Specialist Operations Command Ministry of Defence
Rob Magowan joined the Royal Marines in 1989. His career to Lt Col included an operational tour of Northern Ireland, US Marine Corps staff college, the first deployment to Afghanistan post 9/11 and the invasion of Iraq in 2003. Subsequently, he worked in the Cabinet Office, the Foreign and Commonwealth Office and the Ministry of Defence, with a focus on intelligence. He commanded the Royal Marines 30 Commando Information Exploitation Group, redeploying to Afghanistan. As a Brigadier he commanded the UK’s Joint Forces Intelligence Group. As a Lieutenant General, he was deputy commander of the then UK Strategic Command and then head of capability for Defence. He was appointed Commander Cyber & Specialist Operations Command in March 2026.
Cybersecurity for an always online world
Wherever your organisation will go, whatever it might touch, whoever it may work with online, you need cybersecurity that covers it all.
See how we can help secure your operations at accenture.com/security

ECOSYSTEM PLENARY SPEAKERS_

Kirsten Connell Investor
Octopus Ventures
Kirsten has over a decade of experience working with Europe’s most exciting high-growth start-ups. She began her career at Seedcamp, where during her five‑year tenure as General Manager she travelled across Europe, backing trailblazers including Wise, UiPath & Revolut. In 2015, Kirsten became Managing Director of CyLon, growing Europe’s first cyber security accelerator into a global programme spanning Europe, the Middle East & Asia. Over five years, she accelerated more than 100 companies to a combined portfolio value exceeding £600m. Kirsten is also an active angel investor, with investments including Tessian (exited to Proofpoint), Immersive Labs, Cybersmart, Zamna & RiskLedger. In 2021, she joined Octopus Ventures to launch FCF, its dedicated pre-seed fund, which has backed 60 startups across Europe.

Dr Ali El Kaafarani Founder & Chief Executive Officer
PQShield
Dr. Ali El Kaafarani is a mathematician turned cryptographer, blending academic rigour with entrepreneurial vision. From the lecture halls of Oxford to the frontier of quantum-era cybersecurity, his journey has been defined by a single mission: to future-proof the world’s digital foundations. With a PhD in cryptography and years of research at the University of Oxford and HP Labs, he founded PQShield in 2018, a spinout from Oxford’s Mathematical Institute, to build quantum-resistant cryptographic systems capable of defending against the most powerful computers yet to come.Today, as CEO of PQShield, he leads a team of worldclass scientists and engineers shaping global standards and developing security solutions for governments, enterprises, and chipmakers.

Dr. Andrew Elliot Deputy Director of Cyber Security Department for Science, Innovation and Technology
Andrew is a cyber security leader driving innovation at the intersection of technology, skills, and economic growth. He led the team that secured cyber’s recognition as a frontier technology in the UK’s Industrial Strategy, shaping its role in national growth. Andrew also leads the government’s TechFirst programme, ensuring tech skills are never a barrier to scaling the UK’s fastest-growing sectors. His work supports innovation through the Cyber Runway and Cyber ASAP accelerator programmes, helping startups translate cutting-edge research into real-world impact. Most recently, Andrew is advancing design partnerships to accelerate adoption of CHERI technology, reducing risks from memory vulnerabilities and strengthening the foundations of secure digital systems.

Dr Rachel O’Connell Founder & Chief Executive Officer TrustElevate
Dr Rachel O’Connell is Founder and CEO of TrustElevate, a delegated authority orchestration engine providing the governance layer for agentic AI. A recognised expert in digital identity and technical governance, she authored the PAS 1296 Age Checking Code of Practice for BSI, which evolved into ISO 27566, the global Age Assurance Framework. She is leading an OpenID Foundation initiative to develop Delegated Authority technical specifications, covering secure parental/legal guardianship verification and the governance of agentic AI. As AI agents begin executing autonomous financial transactions, her work defines guardrails to prevent malicious agents exceeding their mandates, aligning UK cyber innovation with global digital-economy resilience.
Richard Parris
Executive Chairman
Aretiico Group plc
Richard Parris is an impact investor, entrepreneur and public company chairman with over 30 years’ experience in the cybersecurity industry, building and leading technology businesses globally. A former CEO, he has deep expertise in cybersecurity, digital trust and green technology. As Executive Chair of Aretiico, he is focused on strengthening trust in the digital world—helping organisations verify identity, protect systems and operate with confidence in an increasingly complex threat landscape—while driving job creation and long-term economic value. His work also supports a cleaner, more sustainable future by tackling environmental pollution and climate risk. Richard brings a commercial, strategic perspective on how trust, security and sustainability intersect in today’s digital economy.

Senior representative
Trust Elevate

Professor Simon Shiu
Professor of Cyber Security University of Bristol
Simon spent over 30 years in the tech industry, mostly with HP and focused on cyber security research. For his last 10 years at HP, he was Director and then VP of the HP Security Lab, a global research organisation with a strong track record of commercial security impact and innovation. Now a professor of practice in cybersecurity at the University of Bristol, Simon was the lead author of the 2025 UK Cyber Growth Action Plan. Simon holds a PhD in computer science and is a member of the advisory board for the Research Institute for Sociotechnical Cyber Security (RISCS).
THREAT AND LEADERSHIP PLENARY SPEAKERS_

Paul Chichester CMG
Director of Operations
National Cyber Security Centre
Paul is Director Operations of the National Cyber Security Centre. He has worked in the UK government intelligence and security community for over 25 years in a variety of offensive and defensive cyber roles. Paul was awarded the MBE in 2005 for his ground-breaking work in cyber, and the CMG in the King’s Birthday Honours in 2024.

Stephen Dane
Managing Director, Managing Director, Cisco Security
Stephen is a Global Technology and Cyber Security Executive with over 25 years of experience across SaaS, IoT, Cloud, and Security markets. He is currently serving as Managing Director Security at Cisco UKI, leading a team of Cyber Security specialists, responsible for providing solutions and services to Public Sector and Enterprise customers across the UK and Ireland. Prior to this role, Stephen led the Cisco Security business in Asia Pacific for 7 years. Stephen re-joined Cisco recently after 6 years at Ericsson and Aeris, where he led Global Channels for IoT.

Rajiv Gupta
Head, Canadian Centre of Cyber Security
Rajiv Gupta is the Head of the Canadian Centre for Cyber Security (Cyber Centre) within the Communications Security Establishment Canada (CSE). He leads the delivery of cyber security advice, guidance, and services to the Government of Canada, critical infrastructure sectors, and the Canadian public. Previously, Rajiv served for three years as Associate Head of the Cyber Centre, driving national cyber security outcomes through close collaboration with industry partners. Since joining CSE in 2007, he has held several senior leadership roles, including Director General of Cyber Defence Capabilities and Director of Security Architecture and Risk Mitigation. Rajiv holds bachelor’s and master’s degrees in engineering and is a Professional Engineer in Ontario.

National Cyber Director, National Cybersecurity Office, Japan
Government Communications Headquarters
Mr. IIDA was appointed National Cyber Director and Deputy National Security Advisor on July 1, 2025, after serving as Deputy Chief Executive at the National Center of Incident Readiness and Strategy for Cybersecurity (NISC), DirectorGeneral for Economic Security at the Cabinet Office, several key positions in international trade and industrial policies at the Ministry of Economy, Trade and Industry (METI), including Director-General of the Trade and Economic Cooperation Bureau and Director-General of the Trade Control Department. He currently leads the National Cybersecurity Office, which formulates a national cybersecurity strategy and develops detailed rules of the Active Cyber Defense Act.
Yoichi Iida

Senior representative


Vincent Strubel Director General
French National Cybersecurity Agency (ANSSI)
CERT.LV
RESILIENCE PLENARY SPEAKERS_

Natalie Black CBE
Group Director, Infrastructure and Connectivity Ofcom
Natalie Black CBE joined Ofcom in 2024 as Group Director for Communications and Networks and Executive Board Member. She is also responsible for leading Ofcom’s work on the implications of Artificial Intelligence. Previously, Natalie was the UK’s first His Majesty’s Trade Commissioner for Asia Pacific. Based in Singapore, she led the UK’s trade strategy and operations across 15 countries and was the UK’s first Senior Economic Official to ASEAN. Highlights included the UK’s first Digital Economy Agreement, securing new investment deals from Australia and Japan and joining the Comprehensive and Progressive Agreement for the TransPacific Partnership.

Rita Erfurt
Assistant Director General, Global Powers and Counter Cybercrime
Australian Cyber Security Centre

Nicola Connelly Chief Executive Officer
SP Energy Networks
Nicola Connelly is Chief Executive Officer of SP Energy Networks, responsible for transmission and distribution network operations across Central and Southern Scotland, North and Mid Wales, Cheshire, and Merseyside. She is overseeing a £12 billion investment programme to modernise and expand the grid, enabling the connection of up to 1.8 million electric vehicles, 1.1 million heat pumps, and 10.4 GW of new generation and storage capacity. With over two decades in the energy industry, including senior finance roles across the ScottishPower Group, Nicola brings deep strategic and operational expertise. She is committed to delivering a smarter, more resilient and customer centric network for the UK’s net zero future.

Beth Hopkins
Chief Operating Officer and NCSC Director Delivery, Engineering and Crypt Key National Cyber Security Centre
Beth was appointed as NCSC’s Chief Operating Officer in 2024. She has been part of GCHQ since 2004, working primarily in operations, leading a variety of teams across intelligence and cyber defence.

Rod Latham
Cyber Security and
Digital
Identity Director Department for Science, Innovation and Technology
Rod Latham took up post as the Director for Cyber Security and Digital Identity in the Department for Science, Innovation and Technology (DSIT) on 1 July 2024. In that role, he is responsible for driving improvements in the UK’s cyber security, resilience and skills base and supporting the creation of a safe and thriving digital identity market, delivered through a combination of policy, legislation and a series of programmes. Rod joined the Civil Service in 2006. Prior to arriving in DSIT, he worked in various roles in the Cabinet Office, Home Office, and Ministry of Defence. He has degrees in history from Cambridge, international relations from Johns Hopkins, and international security from Kings College London.

Claudia Plattner President Federal Office for Information Security
Claudia Plattner has been the President of the German Federal Office for Information Security (BSI) since 1 July 2023. Claudia Plattner was born in Mainz in 1973. She has more than 20 years of experience in IT functions for companies and institutions. Most recently, she served as the Director General for Information Systems at the European Central Bank and previously held a senior position as Chief Information Officer (CIO) of DB Systel GmbH, the internal IT service provider of Deutsche Bahn. Claudia Plattner holds a degree in mathematics (TU Darmstadt) and a master’s degree in applied mathematics from Tulane University (USA).

TECHNOLOGY AND LEADERSHIP PLENARY SPEAKERS_

Carolyn Ainsworth
Deputy Director Engineering
National Cyber Security Centre
Carolyn leads the engineering teams at NCSC, overseeing development and support of specialist IT infrastructure. She is also the Chief Technology Officer for the Joint Crypt Key Program, ensuring the security of MoD operations. With a career spanning over two decades, Carolyn has held various roles within NCSC and GCHQ, including Lead Software Evaluator and Technical Director. Prior to this, she spent 16 years in the aircraft industry, working on both military and civilian aircraft. She designed and built software for various safety and mission-critical systems, eventually becoming the Design Authority for software approval for aircraft supplied by Boeing and BAE Systems. In 2024 Carolyn was voted one of the Top 50 Women In Engineering by the Women’s Engineering Society.

Els Debuf
Head of Delegation for Cyberspace
Global Cyber Hub, International Committee of the Red Cross
Ms. Els Debuf heads the International Committee of the Red Cross’ (ICRC) Delegation for Cyberspace and Global Cyber Hub, based in Luxembourg. Previously she held senior leadership roles, including Representative to the Palestinian Authority and Head of Mission based in Jerusalem, Strategic Advisor to the ICRC Delegation in Tel Aviv, and Deputy Head of the ICRC Regional Delegation for Southern Europe, where she oversaw operations in multiple countries. Ms. Debuf also worked as ICRC’s legal advisor on privileges and immunities and worked in ICRC field delegations in Guinea Conakry, Colombia and Georgia. With a PhD in public international law from the Graduate Institute in Geneva, Ms. Debuf is a published author and speaker on humanitarian action and international humanitarian law.

Catherine Day
Founder
National Strategy Project
Catherine Day is Founder of the National Strategy Project, building a practical, independent way for the UK to think, decide and act together on its long-term future. In 2026, it will launch a first National Dialogue a starting point for asking the country what future it wants, and building the means to achieve it - including on critical issues like cybersecurity and national resilience. Catherine spent 25 years at the centre of UK government, working in No.10, the Cabinet Office and FCDO, advising Prime Ministers on strategy, national security and reform. Her work focuses on how countries face reality, make choices and act with continuity.

Keri Gilder Chief Executive Officer
Colt
Technology Services
Keri is at the helm of our mission to make effortless connections everywhere and enable extraordinary outcomes for customers. She strives to make every interaction with Colt as easy as pushing a button.

Barbara Grewe
Chief Executive Officer
Glenwood Global Risk Management LLC
Barbara is CEO of Glenwood Global Risk Management LLC. Previously she served as a Senior Principal for International Strategy and Policy at the MITRE Corporation with a focus on Japan. Barbara’s government experience includes serving on the FBI’s 9/11 Review Commission, on the original 9/11 Commission, and as a federal prosecutor. Prior to government service Barbara worked as an attorney in private practice and at McKinsey & Company. Barbara is a graduate of the University of Michigan Law School, Oxford University (Rhodes Scholar), and Wellesley College. She is currently at Cambridge University as part of the Cambridge Better Futures Program. Barbara is a non-executive Director for Cellebrite Federal Solutions, Inc. and a co-host of the “Are We Safer Today?” podcast.

Jamie MacColl
Senior Research Fellow
Royal United Services Institute
Jamie MacColl is a Senior Research Fellow at the Royal United Services Institute. His current research focuses on ransomware and other financially motivated cybercrimes, the UK’s national cyber strategy, and risk management approaches to ‘high-risk’ ICT vendors. He is also currently a Senior Research Associate at Virtual Routes, a European think tank, a Project Fellow at the Research Institute for Sociotechnical Cyber Security, and a member of the technical committee Cyber Monitoring Centre. Jamie also represents RUSI at the Counter Ransomware Initiative’s private sector advisory panel. He holds an MPhil in International Relations and Politics from the University of Cambridge and BA in War Studies from King’s College London.

Richard Horne
Chief Executive Officer
National Cyber Security Centre
Richard Horne has been CEO of the NCSC since October 2024. Before joining, Richard was a Cyber Security Partner and chair of the Cyber Security Practice at PwC UK, helping global boards shape cyber risk strategies and led the response to critical incidents. He oversaw the post incident review for the Irish Health Service after the ransomware attack disrupted healthcare services across Ireland in 2021. Richard was Managing Director of Cyber Security for Barclays PLC, responsible for cyber security risk management. In 2011 he went to the Cabinet Office to develop and implement the first national plan for cyber security, impacting both government operations and the wider economy. Richard holds a PhD in Mathematics from Royal Holloway, University of London.

Senior representative
Cybersecurity and Infrastructure Security Agency (CISA)
TECH TALKS_
Join us in the Lomond Auditorium for the 2026 Tech Talks and listen to highly technical talks across two-days presented in five series.
Tech Talks are 20 minute advanced briefings on innovation, future technologies or pieces of research followed by 5 minutes of questions. Led by experts in their fields, these advanced sessions will provide insight into the latest cyber knowledge illuminating research and detailed analysis and actionable conclusions.
DAY 1 – WEDNESDAY 22 APRIL
Tech Talks – Series 1
Talks included in the Tech Talks Series 1 are:
TT01.1 - This Is Not a Forecast: AI-Enabled Cyber, Twelve Months On
11:20 – 12:50
Lomond Auditorium
13:20 – 15:20
Lomond Auditorium
TT01.2 - Provenance by Design: Securing Journalism & Media with C2PA Standards
TT01.3 - Cybercrime as a Service: Mapping Future Threats Through a Policy Delphi Study
Cross-Learning Threads
AI for Cyber Defence; Transparency
Session Keywords
AI enabled threat; Emerging and frontier topics; Human factors and culture; Legal, regulatory, and policy; Offensive resilience; Threat landscape and intelligence
Tech Talks – Series 2
Talks included in the Tech Talks Series 2 are:
TT02.1 - The Era of the Self-Propagating Cloud Worm: Dissecting The “Shai-Hulud” Campaigns
TT02.2 - Predicting Vulnerabilities: How Industrialized Adversaries Reveal CVEs Weeks Before Disclosure
TT02.3 - Advanced Persistent Hunting: A Multi-Year Investigation of a New APT
TT02.4 - AI in Incident Response: What Worked, What Failed, and What We Learned
Cross-Learning Threads
AI for Cyber Defence
Session Keywords
AI enabled threat; Cloud and SaaS security; Detecting, response, and forensics; Network, endpoint, and email security; Theat landscape and intelligence
DAY 2 – THURSDAY 23 APRIL
Tech Talks – Series 3
Talks included in the Tech Talks Series 3 are:
TT03.1 - Clarity in the AI Haze
TT03
09:10 – 10:40
Lomond Auditorium
TT04
11:20 – 13:00
Lomond Auditorium
TT03.2 - Turning AI into Actionable Cyber Intelligence Across Critical Sectors
TT03.3 - The Threat is Already Here: What OT Attacks Are Teaching Us
Cross-Learning Threads
AI for Cyber Defence
Session Keywords
AI for Cyber Defence; Detection, response and forensics; Network, endpoint, and email security; Theat landscape and intelligence
Tech Talks – Series 4
Talks included in the Tech Talks Series 4 are:
TT04.1 - How to Justify Security Investments with Actual Evidence
TT04.2 - Evidence-Based Defence: What Works, According to Microsoft’s Experiences in Incident Response
TT04.3 - The Next Generation of NCSC’s Active Cyber Defence services (ACD2.0): A Story Of Experimentation, Data, and Evidence of Impact
TT04.4 - Passkeys at Sophos: Making CISOs, CIOs & Employees Happy (All at Once)
Cross-Learning Threads
AI for Cyber Defence
Session Keywords
Application and product security; Detection, response, and forensics; Human factors and culture; Identity, authentication, and access; Strategy, governance, and risk
Tech Talks – Series 5
Talks included in the Tech Talks Series 5 are:
TT05.1 - Why Cyber Defenders Need to be Ready for Frontier AI
TT05
13:30 – 15:20
Lomond Auditorium
TT05.2 - At the Front Line of CNI Resilience: AI, Data Modalities and System Challenges
TT05.3 - From Automation to Autonomy: Agentic AI for Offensive Security Testing
TT05.4 - Views from the Reasoning Frontier; New Eyes on the Security Pipeline
Cross-Learning Threads
AI for Cyber Defence
Session Keywords
AI enabled threat; Application and product security; DevSecOps and platform security; Network, endpoint, and email security; OT/ICS and cyber-physical security
RESILIENCE TRACK_
TR1A
13:50 - 14:40
Armadillo
DAY 1 – WEDNESDAY 22 APRIL
From Rehearsal to Reality:
Building Effective Testing, Exercising and Incident Response Across CNI
This panel brings together leaders from industry and government to explore how mature approaches to testing, exercising and recovery can strengthen resilience across the UK’s Critical National Infrastructure (CNI). Drawing on lessons from the finance sector, the discussion will examine what drives effective incident response, and what does not.
Panellists will consider how these practices can be adapted to sectors with different risk profiles, regulatory pressures and resource constraints. Expect a candid conversation on moving from paper plans to operational readiness, the role of cross-sector collaboration, and how organisations can scale proportionate, realistic exercising that delivers real-world resilience rather than compliance alone.
Chair
Rosehanna Chowdhury, Chief Executive Officer, UK Resilience Academy
Panellists
Jessica Colvin, Managing Director - Global Head of Cybersecurity Operations, Citi Blake Darché, Head of Cloudforce One, Cloudflare
Eloise Hindes, Deputy Chief Information Security Officer, Bank of England
Cross-Learning Threads
Recovery and Continuity; Transparency
Session Keywords
Detection, response and forensics; Legal, regulatory and policy; Sector specific; Strategy, governance and risk
TR4A
11:00 - 11:50
Hall 2
DAY 2 – THURSDAY 23 APRIL
Cyber Essentials in Corporate Supply Chains
Attaining Cyber Essentials (CE) is proven to significantly reduce the likelihood of an organisation suffering a cyber attack. This panel, comprised of NCSC, DSIT, IASME and industry, will discuss a recent initiative by some of the UK’s largest organisations and our trust group members to drive up national cyber resilience at scale by mandating CE in their supply chain. The session will also examine the benefits of adopting the Cyber Action Toolkit, the Governance Code of Practice and Early Warning strategies.
Chair
Chris Ensor, Deputy Director, National Resilience Capability, National Cyber Security Centre (NCSC)
Panellists
Dr Neil Binnie, Chief Information Security Officer, Morgan Sindall Group
Irfan Hemani, Deputy Director - Cyber Security & Resilience Policy, Department for Science, Innovation and Technology (DSIT)
Dr Emma Philpott MBE, Chief Executive Officer, IASME
Stephanie Perry, Global Chief Information Security Officer, Babcock International
Cross-Learning Threads Transparency
Session Keywords Transparency
Defending as One – Learning From The Past 10 Years to Shape The Next 100 Years
Our digital ecosystems are increasingly interconnected, transcending organisational and geographical boundaries, and affecting critical infrastructure, public services and private enterprise alike. No single sector can meet this challenge in isolation.
Participants will hear from leaders driving whole-system approaches to resilience, and will consider practical steps for aligning strategic priorities, bridging cultural divides and sustaining trust. The session will conclude with a vision and roadmap for the next decade to reinforce the point that resilience is not a competitive advantage, but an imperative to secure our foundations for economic prosperity and national security.
Chair
TR2A
12:10 – 13:00
Alsh
Bryony C, Deputy Head Government Cyber Resilience, National Cyber Security Centre (NCSC)
Panellists
Eleanor Fairford, Director for Cyber Defence and Risk, Ministry of Defence (MOD)
Chantal McEwan, Deputy Director - Government Cyber Strategy, Department for Science, Innovation and Technology (DSIT)
Russell Kerr, Detective Chief Inspector - Cyber and Fraud Unit, Police Scotland
Mike Sewart, Chief Technology Officer, Thales UK
Nuhad Zoght, Senior Executive Security Advisor, Canadian Centre for Cyber Security
Cross-Learning Threads
Recovery and Continuity; Transparency
Session Keywords
Detection, response and forensics; Legal, regulatory and policy; Strategy, governance and risk
RESILIENCE TRACK_
TR3A
14:30 - 15:20
Hall 1
DAY 2 – THURSDAY 23 APRIL
Resilience as a Research Agenda: How Science and Research Can Strengthen Cyber Security Technology is constantly evolving around us. In this session, academic panellists will explore the impact of this evolution on the UK’s national security and the levers required across the cyber ecosystem to allow organisations to remain resilient despite the advancing geopolitical threat. How can generated knowledge steer those empowered to make change?
Chair
Professor Dan George, Chief Scientific Adviser for National Security, Government Communications Headquarters (GCHQ)
Panellists
Professor Muffy Calder, Professor of Formal Methods, University of Glasgow Professor Professor Adam Joinson, Professor of Information Systems, University of Bath
Professor Shahid Raza, Professor and Chair of Cyber Security, University of Glasgow
Dr Kathryn Magnay, Programme Director, National Security and Defence, Engineering and Physical Sciences Research Council
Session Keywords
AI enabled threat; Detection, response and forensics; Emerging and frontier topics; Human factors and culture; Threat landscape and intelligence

Thales | CyberUK
Resilience Stream Sponsor


TECHNOLOGY TRACK_
TR1B
13:50 - 14:40
Hall 1
DAY 1 – WEDNESDAY 22 APRIL
Cross Domain to Enable Sustainable Resilience
Achieving net-zero requires a more connected grid, increasing cyber risks. Hear technical details on NCSC’s new guidance on how to design secure data flows by following a Cross Domain approach. This session will provide architects and technical risk managers details of NCSC’s new approach to Cross Domain technology. Currently Cross Domain is mainly used in defence & intelligence, our new approach looks to cater to wider sectors, including critical systems such as energy systems.
Chair
Senior representative, National Cyber Security Centre (NCSC)
Panellists
Sarah Hadfield, Head of Energy Sector Security, National Energy System Operator (NESO)
Dr Duncan M, Principal Security Architect, National Cyber Security Centre (NCSC)
Cross-Learning Threads
Economic Security Session
Keywords
Application and product security; DevSecOps and platform security; Emerging and rontier topics; Network, endpoint and email security; Security architecture and design
TR3B
11:00 - 11:50
AIsh
DAY 2 – THURSDAY 23 APRIL
Engineering Resilience – How Can We Worry Less When Our Systems are Compromised?
To what extent is it possible to architect systems to be more resilient in the event of compromise? NCSC shares its latest thinking on best practice, and the panel discuss where they have seen this done well, the extent to which the chosen technical patterns matter and how generalisable approaches are.
Chair
Harry G1, Deputy Director, National Cyber Security Centre (NCSC)
Panellists
Carolyn Ainsworth, Deputy Director Engineering, National Cyber Security Centre (NCSC)
David Brown, Principal Security Consultant, NCC Group
David I, Security Architect, National Cyber Security Centre (NCSC)
Senior representative, Google
Cross-Learning Threads
AI for Cyber Defence Recovery and Continuity Session
Keywords
Detection, response and forensics; DevSecOps and platform security; Security architecture and design
“I’m sorry Dave, I’m afraid I can’t do that” – Is Agentic AI the Solution for Scalable Cyber Defence?
2025 saw an unprecedented increase in serious cyber breaches in the UK. In parallel, the adoption of AI capabilities by threat actors is contributing to it being ever more difficult for defenders to protect their systems as the speed, scale and sophistication of cyber attack campaigns increases at an ever-advancing pace. The panel will explore the adoption and integration of agentic AI capabilities by the cyber defender in order to try to level the playing field and regain the initiative by allowing AI to automatically harden systems and respond to threats.
TR2B
11:00 - 11:50
Hall 2
Chair
Senior representative, National Cyber Security Centre (NCSC)
Panellists
Perri Adams, Chief Executive Officer, Inflection Points LLC
Dr Gudmund Grov, Principal Scientist, Norwegian Defence Research Establishment (FFI)
Toby Lewis, Global Head of Threat Analysis, Darktrace
Cross-Learning Threads
AI for Cyber Defence Session
Keywords
AI enabled threat; Application and product security; Data security; DevSecOps and platform security; Network, endpoint and email security
TECHNOLOGY TRACK_
DAY 2 – THURSDAY 23 APRIL
Radical Transparency – How Much Should We Share?
Transparency helps decision making but could also help attackers. Hear how NCSC is promoting transparency in assurance and operation of digital infrastructure and ask what more we could do. Should all devices share their version information?
Chair
TR4B
14:30 - 15:20
Armadillo
Paul Waller, Principal Technical Director, National Cyber Security Centre (NCSC)
Panellists
Carla Baker, Senior Director, Public Policy, Palo Alto Networks
Ross McKerchar, Chief Information Security Officer, Sophos
Glenn Thorpe III, Senior Director of Security Research & Detection Engineering, GreyNoise Intelligence
Senior representative, Cybersecurity and Infrastructure Security Agency (CISA)
Cross-Learning Threads
Transparency
Session Keywords
Application and product security; Legal, regulatory and policy; Security architecture and design


THREAT TRACK_
TR1C
13:50 - 14:40
Hall 2
DAY 1 – WEDNESDAY 22 APRIL
What is Really Happening in Cyber Crime?
Why has cyber crime been hitting the headlines more than ever? A panel of experts from government and industry dive into recent shifts and trends in the cyber crime landscape: tactics, operating models, actors and their motivations. Panellists will look back over the last 10 years, and look to the future: what next, and how do we accelerate resilience against these threats?
Chair
Charlie S1, Head of Assessment, National Cyber Security Centre (NCSC)
Panellists
Paul Foster, Head of Cyber Crime, National Cyber Crime Unit National Crime Agency (NCA) Cynthia Kaiser, Senior Vice President, Ransomware Research Center, Halcyon Tech Senior representative, European Union Agency for Cybersecurity (ENISA)
Session Keywords
AI enabled threat; Detection, response and forensics; Threat landscape and intelligence
TR2C
11:00 - 11:50
Hall 1
DAY 2 – THURSDAY 23 APRIL
Are Today’s Biggest Cyber Threats Caused by Artificial Intelligence or Active Inertia?
For months, news headlines have warned us of an AI-powered cyber apocalypse – a relentless, hyper-sophisticated threat that renders traditional defences obsolete.
We’ve been told that machine learning is the new supervillain, making every organisation fundamentally vulnerable. But what if this narrative is the most significant distraction facing the industry?
This session challenges the fear-mongering and asks uncomfortable questions: Are we really being defeated by bleeding-edge AI malware, or are we failing to adapt to the new normal by trying to scale the human processes that worked before to defend against machine speed attacks? Will today’s approaches to cyber security be fit for purpose in the agentic future? Is active inertia, not artificial intelligence itself, the real AI problem?
In this panel, Tenable’s Product Vice President, Gavin Millard, and guests will debate these questions, drawing on data-driven insights to understand future AI cyber threats and how we can defend against them.
Chair
Gavin Millard, Vice President, Product, Tenable
Panellists
Didem B, AI Technical Director, National Cyber Security Centre (NCSC)
Simon Kellow, Principal Consultant, Kellow Associates
Cross-Learning Threads
AI for Cyber Defence
Session Keywords
AI enabled threat; AI for Cyber Defence; Human factors and culture
Deep Dive Into the Evolution of Advanced State Actors
State actors continue to present a significant threat to UK and global cyber security, aided by an evolving cyber intrusion sector. In this session, experts from across the threat intelligence community reflect on trends and themes they’ve observed in tracking the activity and tradecraft of advanced state cyber actors. Covering both technical and strategic perspectives, the panel will look back over the last 10 years, and look to the future: what’s coming next, what keeps them up at night, what should we do about it, and how do we defend our systems against the threat?
Chair
TR3C
12:10 - 13:00
Armadillo
Beth Hopkins, Chief Operating Officer and NCSC Director Delivery, Engineering and Crypt Key, National Cyber Security Centre (NCSC)
Panellists
Dr Monica Kello, Lecturer in Cyber Security and Co-Director of the Cyber Security Research Group, King’s College London
Saher Naumaan, Senior Threat Researcher, Proofpoint
Senior representative, PwC United Kingdom
Don Smith, Vice President of Threat Research, Sophos
Cross-Learning Threads
Economic Security; Recovery and Continuity
Session Keywords
AI enabled threat; Detection, response, and forensics; Threat landscape and intelligence
THREAT TRACK_
TR4C
14:30 - 15:20
AIsh
DAY 2 – THURSDAY 23 APRIL
Oh, That Was Clever! When Even Jaded Incident Handlers Are Impressed and Future Implications
NCSC’s Annual Review 2025 highlighted a 50% increase in highly significant incidents for the third consecutive year. In this session, the Incident Management team for NCSC joined by international counterparts, take us behind the scenes. They’ll review some of the cleverest and most intriguing tradecraft they’ve seen in the last year, highlighting the escalating cyber threat, but also the key responses. What’s changed over recent years, and what has stayed the same?
Speakers
Lori Blencowe, Senior Director, Cyber Security Incident Management, Canadian Centre for Cyber Security
Harry W, Tech Director for Incident Management, National Cyber Security Centre (NCSC)
Session Keywords
Detection, response and forensics; Threat landscape and intelligence



ECOSYSTEM TRACK_
TR1D
13:50 - 14:40
AIsh
DAY 1 – WEDNESDAY 22 APRIL
Transparency as the Foundation: Standards, Assurance and Trust in Cyber Security “Can we have security without transparency?” “Where does standardisation end and innovation begin?” This session will explore the tension between operational security and collective defence, connecting workforce development with real-world transparency dilemmas in cyber security practice. We will explore how transparency requirements affect incident recovery and lessons learned and discuss approaches to making complex standards more accessible to SMEs and educational institutions, supporting a thriving marketplace of services.
Chair
Dr Charles Clarke, Director of Operations, CSE Connect Panellists
Dr Natalie Coull, Head of Department of Cybersecurity and Computing, Abertay University
Professor Phil Legg, Professor in Cyber Security & Co-Founder, University of the West of England & CSE Connect
Professor Keith Martin, Professor of Information Security, Royal Holloway, University of London Findlay Whitelaw, Field Chief Information Security Officer, Strategist & Researcher, Exabeam
Cross-Learning Threads
Transparency
Session Keywords
AI for Cyber Defence; Human factors and culture; Legal, regulatory and policy; Strategy, governance and risk
TR2D
11:00 - 11:50
Armadillo
DAY 2 – THURSDAY 23 APRIL
Making Scotland a Hard Target: The Small Nation Leading Big Cyber Change
There are advantages to being a small nation – agility is one. Mobilisation is another.
The Scottish Government is now utilising this dexterity as it aims to transform cyber security into a “whole-of-nation effort”, reshaping how it defends, responds and innovates; making Scotland a hard target for cyber threats.
We’ll explore what that means in practice, and what we can all learn from this bold approach. What are the unique challenges facing Scotland as it reimagines cyber resilience? And can an entire nation really galvanise to meet tomorrow’s cyber challenges?
Chair
Alan Gray, Head of Cyber Division, Scottish Government
Panellists
Jessica Elizabeth Amery, IT Infrastructure Director, The Weir Group PLC
Keith McDevitt MBE, SC3 Cyber Exercising Lead, Scottish Government
Karen Meechan, Chief Executive Officer, ScotlandIS
Maggie Titmuss MBE, Chair NCRAB, MET Edinburgh Consulting Ltd
Session Keywords
Emerging and frontier topics; Human factors and culture; Legal, regulatory and policy; Strategy, governance and risk
Lessons From Your Future Workforce: How We Are Breaking Barriers and Building Skills
We often hear about the cyber skills gap – but how often do we hear directly from the talent expected to close it?
TR4D
12:10 - 13:00
Hall 1
This panel brings their voices to the forefront. What motivates the next generation to pursue a career in cyber? What barriers stand in their way? Is the issue truly a skills gap – or a gap in investment and opportunity? Are we bridging the divide between education and industry expectations? And as AI reshapes technology careers, what does the future hold for cyber professionals? There are lessons here for all of us – insights that could redefine how we attract, develop and retain the talent we need.
See the companion session TR3D, Diverse Minds Stronger Cyber at 14:30.
Chair
Jane Wright, Senior Consultant, QinetiQ
Panellists
Thomas B, Cyber Security Certification Specialist, Civil Aviation Authority
Alex C, PortSwigger
Jack L, Student, CyberFirst Bursary Scheme
Lorne R, Applied Intelligence Lead, The Hacking Games
Session Keywords
Emerging and frontier topics; Human factors and culture
ECOSYSTEM TRACK_
TR3D
14:30 - 15:20
Hall 2
DAY 2 – THURSDAY 23 APRIL
Diverse Minds, Stronger Cyber: Building Inclusive Workforces That Thrive
In a fast-changing digital world, diversity isn’t an ideal - it’s essential.
You’ve heard from our future workforce, now hear from a panel of cybersecurity leaders, with decades of experience, as they share insights into building an inclusive, resilient and innovative cyber sector.
The UK cyber workforce is approximately 143,000 professionals, yet almost half of organisations report skills shortages. Representation remains uneven: women 17%, disabled professionals 8%, and while 19% are from ethnic minority backgrounds, only 8% hold senior roles.
Our panel will explore the strategies that have shaped careers in this dynamic industry – from empowering underrepresented talent to fostering environments where confidence can thrive. They’ll share honest reflections on their journeys, challenges and interventions needed to create and retain a truly diverse cyber workforce.
Whether starting out or leading, this conversation will inspire you to champion inclusion and support the perspectives that make cybersecurity stronger.
Chair
Carolyn Ainsworth, Deputy Director Engineering, National Cyber Security Centre (NCSC)
Panellists
Richard Bate, Chief Technology Officer, Goldilock Labs Ltd
Natalie Billingham, Senior Vice President of EMEA Sales and EMEA Managing Director, Akamai Technologies Ltd
Jane Wright, Senior Consultant, QinetiQ
Purvi Kay, Head of Cyber Security, BAE Systems
Cross-Learning Threads
Economic Security
Session Keywords
Education and skills; Human factors and culture





CISO TRACK_
11:20 – 12:20
DAY 1 – WEDNESDAY 22 APRIL
CLOSED TRACK
Unique Perspectives: Threat Realities We Should Know and Care About
An opportunity to hear from a panel of senior leaders from across intelligence and law enforcement. They will share their views on the threats their teams are dealing with now, what we should be thinking about in the future, and how CISOs should be addressing these threats in their roles.
Chair
Beth Hopkins, Chief Operating Officer and NCSC Director Delivery, Engineering and Crypt Key, National Cyber Security Centre (NCSC)
Panellists
Anne Keast-Butler, Director, Government Communications Headquarters (GCHQ) Senior representative, Federal Bureau of Investigation (FBI)
Stephen Rodhouse, Director General Threats, National Crime Agency Senior representative, National Protective Security Authority (NPSA)
Session Keywords
Detection, response, and forensics; Threat landscape and intelligence
CLOSED TRACK
Post-Quantum Cryptography: Managing the UK’s Quantum Risk
CS02
12:20 – 13:50 M1
INVITE ONLY
The UK’s digital security is underpinned by robust cryptography. Over the coming years, there will be a global migration to post-quantum cryptography, to protect against the threat from future quantum computers. We will discuss the challenges this presents for CISOs: getting buy-in from boards; accessing skills; and cross-sector transparency. We will hear some practical examples of the steps some organisations are already taking and there will be an opportunity to ask your own questions of the government and industry representatives on the panel.
Chair
Dr Jeremy B, Principal Technical Director for Cryptography, National Cyber Security Centre (NCSC)
Panellists
Will Collison, Technical Director – Cryptography, HSBC Flo D, Deputy Chief Technology Officer for Cyber Policy and Assessments, National Cyber Security Centre (NCSC)
Senior representative, GSK
Cross-Learning Threads
Transparency
Session Keywords
Application and product security; Cryptography and post-quantum
DAY 1 – WEDNESDAY 22 APRIL CS03
13:50 – 15:20
CLOSED TRACK
Sustaining High Performance: Resilience as a CISO
Cyber security professionals live in a constant state of urgency – firefighting incidents, responding to alerts at all hours and carrying the weight of organisational risk. For CISOs and security teams, the pressure is relentless: limited resources, rising expectations and the all-too-common experience of ‘talking into a vacuum’ when advocating for change.
This session will be led by Rob Archer, a Chartered Psychologist who helps build resilience, improve mental health and sustain high performance.
This interactive workshop will use the latest in cognitive behavioural science to help participants deal with challenges, change and stress more effectively.
Speaker
Dr Rob Archer, Chartered Psychologist, Rob Archer Psychology Ltd
Cross-Learning Threads
Recovery and Continuity
Session Keywords
Human factors and culture
CISO TRACK_
CS04
11:00 – 12:00 M1
INVITE ONLY
DAY 2 – THURSDAY 23 APRIL
CLOSED TRACK
Voices From the Breach: Lessons Learned From Cyber Attack Victims
Most weeks we hear news of cyber attacks. But responding to them is not always as expected. This session will hear from victims of cyber attacks from across government, defence and industry. We will discuss what really happens when an attack is first discovered, what CISOs were asked to do that they didn’t expect , as well as lessons learnt, which will helpothers better prepare for when it might happen to them.
Chair
Senior representative, National Cyber Security Centre (NCSC)
Panellists
Eleanor Fairford, Director for Cyber Defence and Risk, Ministry of Defence (MOD)
Lucy Jones, Deputy Chief Executive, Legal Aid Agency
Dr Zibby Kwecka, Chief Information Security Officer, Arnold Clark Senior representative, Weir Group
Scott McElney, Chief Information Security Officer, Weir Group
Cross-Learning Threads Recovery and Continuity
CLOSED TRACK
We’re All in This Together: How Government and Industry Can Help and Learn From Each Other
CS05
12:00 – 13:00 M1
INVITE ONLY
Governments expect industry to take action and keep themselves secure and resilient, but governments should really be leading by example when to comes to cyber security and resilience of their networks, services, and capabilities. This session will hear more about what governments are doing to protect themselves, and explore how industry have a part to play in that and what that should mean for CISOs whether they are a supplier to government or not.
Chair
Johnny M, Deputy Director for Government Cyber Resilience, National Cyber Security Centre (NCSC)
Panellists
Bella Powell, Director of the Government Cyber Unit and Government Chief Information Security Officer, Department of Science, Innovation and Technology (DSIT)
Stephanie Perry, Global Chief Information Security Officer, Babcock International
Michael Duffy, U.S. Federal Chief Information Security Officer, Executive Office of the President
Cross-Learning Threads Transparency
Meet us at CYBER UK 2026
Australia is a top-tier global cybersecurity powerhouse, recognised for its high standards, commitment to innovation, and robust growth Our companies offer world-class cyber solutions that promise to protect and enhance your competitive edge – solutions born of a globally regarded and rapidly growing cybersecurity sector.
Visit us at the Australia Pavillion C24











Securing the
UK’s Public Sector
The UK's threat landscape shifted dramatically in 2025, and most organisations haven't kept up. Check Point Research reveals the UK is now the most targeted country in Europe, accounting for 16% of all regional attacks. But it's not just the volume that's alarming; it's the nature of the attacks. Ransomware is no longer the dominant threat. Website defacement now accounts for nearly half of all attacks on UK organisations, driven by politically motivated actors focused on maximum disruption, not financial gain. In December 2025 alone, over 450 attacks were recorded, 90% of them defacements, timed deliberately to exploit reduced security staffing and peak commercial activity. Sectors most at risk include business services, technology, retail, energy, and government. Attackers are no longer choosing victims by size or revenue. They're choosing by blast radius. The consequences are real: retailers suffered weeks-long outages, manufacturers shut down production lines, and airlines reverted to manual check-in. Cyber risk has become operational risk, and it now sits firmly on the board agenda. Many of the vulnerabilities exploited were not zero-days. They were known, unpatched, and avoidable.

Check Point's AI-driven platform delivers continuous exposure management, real-time threat intelligence, and automated response across network, endpoint, cloud, and identity, helping UK organisations move from reactive defence to proactive resilience. To find out more, visit Check Point at Booth D21.
At CYBERUK 2026 we are proud to be celebrating Women in Cyber. Across the globe, we have talented professionals dedicated to the support and advocacy of women in this vibrant industry. Visit stand A16 to have your say on how the UK’s cyber ecosystem could further develop the Women in Cyber network.

INTERACTIVE WORKSHOPS_
DAY 1 – WEDNESDAY 22 APRIL
How Do You Address The Commercial Cyber Intrusion Problem?
Strategic Discussion: Commercial Cyber Intrusion Capabilities (CCICs) have become a defining feature of today’s cyber threat landscape. Developed and sold by private companies but used by a wide range of state and non-state actors, these capabilities can blur the line between responsible and irresponsible cyber activity. Their global availability, incentivisation, and uneven standards of accountability, precision, oversight and transparency create real risks: to victims, to international stability, and to the defenders tasked with detecting and responding to abuse.
WK02
12:40 – 13:30
Boisdale 1 & 2
In partnership with
This workshop will explore how we can respond more effectively to this challenge by working differently. Attendees will examine how cross-sector collaboration can create an “aggregate advantage” that outperforms isolated action. Through facilitated discussion and interactive exercises, participants will contribute ideas on how to deliberately combine capabilities such as vulnerability research, threat intelligence, forensics, policy expertise, victim support, and shared telemetry. The session is designed to be participatory, drawing on the collective experience in the room to identify practical models for collaboration and coordinated response. Bringing together government, industry, civil society, and the technical community.
The discussion is grounded in recent real-world examples where distributed teams of investigators, analysts, NGOs and journalists have acted in parallel to expose irresponsible actors, illuminate advanced intrusion capabilities, and provide tangible indicators of compromise to support victims. It also builds on the momentum of the Pall Mall Process, now in its third year, which has helped establish a shared framework for responsible behaviour in this space, led by the UK and France.
By the end of the workshop, participants will have helped shape thinking on what effective, responsible partnership looks like in practice, and how we can better detect, deter and respond to irresponsible behaviour. Insights from the session will directly inform ongoing work across the NCSC and FCDO, helping to define future approaches to commercial cyber intrusion tools and the ecosystems that sustain them.
Speakers
Dave L3, Technical Director Cyber Marketplace, National Cyber Security Centre (NCSC)
Senior representative, Foreign, Commonwealth and Development Office (FCDO)
Senior representative, National Cyber Security Centre (NCSC)
Session Keywords
Detection, response, and forensics; Emerging and frontier topics; Threat landscape and intelligence; Legal, regulatory, and policy
WK10
12:40 – 13:30
Carron 1 & 2
In partnership with
DAY 1 – WEDNESDAY 22 APRIL
Cyber in Crisis and Conflict – Learning From The Past to Respond The Future
Strategic Discussion: Cyber is now at the heart of modern warfare. From the Russian invasion of Ukraine to sustained state-backed targeting of critical infrastructure, government and industry now operate within a shared crisis environment. Ukraine has shown that a nation’s Armed Forces are only as strong as the industry supporting them, highlighting the need for governments to work with industry and society to defend the digital homeland.
Aligned with this year’s theme, Accelerating UK Cyber Defence, this workshop welcomes industry leaders to explore how cyber activity evolves during periods of crisis and conflict, and what approaches can strengthen effective collaboration between government and industry.
The session will begin with a short briefing setting out emerging UK Government thinking on cyber in crisis and conflict. Participants will then move into focused small group discussions exploring experiences from previous and current conflict, industry approaches to crisis readiness, and practical models for partnership when cyber activity intersects with wider conflict. This workshop aims to generate real world insights to refine shared expectations and improve collaboration in future crises between governments and industry.
Speakers
Dr Natasha Grayson, Deputy Director, Ministry of Defence (MOD) Senior representative, National Cyber Security Centre (NCSC)
Session Keywords
Strategy, governance, and risk; Legal, regulatory, and policy; Threat landscape and intelligence; Offensive security; Economics and program management; Emerging and frontier topics
INTERACTIVE WORKSHOPS_
DAY 1 – WEDNESDAY 22 APRIL
Digital Sovereignty: Where Does the Power Really Lie?
Collaborative Roundtable: “Sovereignty” is appearing more and more in conversations about cybersecurity and the digital world. But what does it actually mean, and is it something that can truly be applied in practice? This workshop presents new research exploring the growing emphasis on digital sovereignty across governments and organisations. Is this wave driven primarily by geopolitical uncertainty and shifting global alliances, or does it reflect deeper questions about control, dependence, and power in an interconnected world?
13:50 – 14:40
Boisdale 1 & 2
Sponsored by
Participants will share their perspectives on sovereignty, control, and responsibility in digital environments and through live questions and facilitated discussion, will be asked what they believe sovereignty means in practice and where they think power truly resides. These views will then be contrasted with the findings from the latest research, creating space for reflection, debate, and reassessment of assumptions.
This workshop is suitable for senior decision-makers, cybersecurity leaders, CIOs and CTOs, risk and compliance professionals, government officials, and policy advisors. It is particularly relevant for those responsible for shaping long-term cyber strategy and strengthening organisational resilience in a rapidly evolving geopolitical landscape.
Participants will gain a clearer understanding of what digital sovereignty means in strategic terms and how it connects to long-term cyber resilience. The session will challenge assumptions about who is truly in control of the technology their organisations rely on, encouraging a deeper examination of dependency, influence, and decision making power.”
Speakers
Professor Victoria Baines, Founder and Principal, Cartimandua Insight
Cross-Learning Threads
Economic Security
Session Keywords
Emerging and frontier topics; Identify, authentication, and access; Legal, regulatory, and policy; Offensive resilience; Privacy and data protection
WK04
13:50 – 14:40
Carron 1 & 2
Sponsored by
DAY 1 – WEDNESDAY 22 APRIL
Accelerating Critical Infrastructure Cyber Defence
Tabletop Exercise: In this workshop, we will provide an overview into Operational Technology (OT) based malware and cyberattacks. We will discuss the evolution of attacks on Industrial control systems (ICS), how the use of attack techniques has changed, and provide demonstrations on how different cyberattacks manifest within the OT environment and the underlying physical processes. Suitable for OT, ICS and cyber security professionals, engineers and resilience teams.
Interactive elements of the workshop will include; a tabletop exercise focused on identifying OT/ICS cyber threats from architecture diagrams, hands-on activity with current cyber defence solutions that can mitigate the threats and demonstrations on how such defences can be deployed, and an interactive discussion around organisational aspects of OT cyber defence.
Speakers
Kelsey Collington, Research Associate, University of Glasgow
Dr Marco Cook, Senior Research Associate, University of Glasgow
Bikram Singh Deol, Doctoral Researcher, University of Glasgow
Dr Stefanos Evripidou, Research Assistant, University of Glasgow
Dr Filip Holik, Research Associate, University of Glasgow
Professor Dimitrios Pezaros, Professor and RAEng Research Chair, University of Glasgow
Session Keywords
Detection, response, and forensics; Emerging and frontier topics; Threat landscape and intelligence; Legal, regulatory, and policy
INTERACTIVE WORKSHOPS_
DAY 2 – THURSDAY 23 APRIL
The AI Achilles’ Heel: How Your AI Can Get Hacked
Learning Workshop: As enterprise AI adoption skyrockets, a dangerous new blind spot has emerged: the perception that AI components are secure by design. Although your network and application infrastructure might be protected, the AI models and agents living within it are inherently insecure and quickly emerging as the newest, weakest link in your cybersecurity posture. Join this hands-on workshop to challenge your assumptions, assess your own AI Security plan maturity, and expose the hidden insecurities in the LLM and Agentic AI landscape. We’re moving beyond theory to systematically help you develop your AI Security plan while practically demonstrating high-priority threats against AI Confidentiality, Integrity, and Safety that traditional security controls often miss or simply are not equipped to address.
What to Expect: Overview of the “AI Security Problem”: A brief update on the current and future risks from AI both as a frontier Attack Vector and Attack Surface.
Your AI Security Plan: Assess AI Framework maturity in an interactive Q&A using an AI Security framework plan that enables you to self reflect on your current AI Security status and work toward a 90-day action plan.
WK05
11:00 – 11:50
Boisdale 1 & 2
Sponsored by
Live Attack & Defence Simulation: Apply your AI Security plan thinking in interactive scenarios where we simulate a corporate AI application and demonstrate how easily an attacker (or an unwitting insider) can compromise its Confidentiality, Integrity and Safety, such as triggering unauthorised data exposure, injecting toxic content and jailbreaking guardrails.
Defence in Depth: Share your thoughts in real-time on appropriate defence measures to discover which platform-led approaches provide real-time protection through measures such as Prompt Sanitisation, Contextual Detection, and I/O Validation.
Learn how to build a robust defence strategy that protects your organisation from the unique risks of AI models and agents, empowering transformative AI adoption responsibly and securely.
This session is suitable for a wide-ranging audience such as CISOs, Network Security Professionals, Security Architects, SOC Managers/Engineers, and AI Security Architects, Security Engineers, DevSecOps. Participants will gain a first hand understanding of the key tenant of model specific vulnerabilities and attack vectors within AI applications.
Speakers
Dr Ryan Hearfield, Cybersecurity Architect, Palo Alto Networks
Jack Hughes, Senior Director – Unit 42, Palo Alto Networks
Cross-Learning Threads
AI for Cyber Defence
Session Keywords
AI enabled threat; AI security; Application and product security; Cloud and SaaS security; Detection, response, and forensics
WK08
11:00 - 11:50
Carron 1 & 2
Sponsored by
DAY 2 – THURSDAY 23 APRIL
When Communication Fails: Tabletop Exercise on Out-of-Band Coordination
Tabletop Exercise: As cyber-attacks and large-scale outages increasingly disrupt national infrastructure, the next decade of cyber defence will depend not only on stronger prevention but on the ability to continue secure operations when critical systems, including communications, are compromised. This workshop explores how organisations can maintain control, compliance, and coordination under such conditions.
Participants will step into a simulated incident where essential infrastructure has failed or been breached. Working in small teams, attendees will be challenged to plan, prioritise, and coordinate an effective response without access to their normal communication channels. Facilitators will introduce evolving developments throughout the scenario, forcing participants to make rapid decisions as the situation changes, balancing the need for compliant communication with the operational urgency of effective remediation. The exercise concludes with a structured debrief summarising key lessons and practical actions for building resilient communication frameworks, defining minimum viable continuity channels, and incorporating out-of-band coordination into existing incident response and governance plans.
This session is suitable for CIOs, CISOs, CSOs, CEOs, COOs, CFOs, Incident Responders, Heads of Information Security, IT Managers and Threat Intelligence Analysts.
Participants will leave with a clear understanding of how to preserve decision-making and operational tempo when trusted systems are unavailable, and how pre-planning for out-ofband communication can accelerate national cyber defence in the decade ahead.
Speakers
Chris Fowler, Account Executive, EMEA, Mattermost
James Mullins, Vice President Sales – EMEA & APAC, Mattermost Richard Preece, Chief Training Officer, OSP Cyber Academy
Cross-Learning Threads
Recovery and Continuity
Session Keywords
Detection, response, and forensics; DevSecOps and platform security; Offensive resilience; Strategy, governance, and risk
INTERACTIVE WORKSHOPS_
DAY 2 – THURSDAY 23 APRIL
Under Attack: A Live Cyber Incident Simulation
Scenario Exercise: As organisations across the UK prepare for the next decade of cyber defence, the reality is clear: attacks are moving faster, spreading wider, and exploiting the interconnected nature of modern environments. Cloud adoption, identity based access, and shared service providers have changed how incidents unfold, while AI is accelerating both defensive capabilities and adversary tradecraft.
The CrowdStrike Incident Response team brings attendees inside a realistic cyber incident based on real world adversary activity observed across Europe. The simulation centres on a highly sophisticated China-nexus adversary compromising a managed service provider, triggering cascading impact across multiple customer environments. This attack pattern is increasingly common and highlights how thirdparty risk, speed of response, and decision making under pressure can determine the scale of disruption.
WK07
12:10 – 13:00
Boisdale 1 & 2
Sponsored by
Participants will take an active role throughout the session. Using live audience polling on personal devices, attendees will vote on response actions at critical stages of the incident, from initial detection and containment through investigation, communication, and recovery. Each decision directly influences how the scenario evolves, revealing how modern attacks adapt in real time and how seemingly small choices can significantly alter outcomes.
Designed for both technical practitioners and security leaders, this workshop cuts through complexity to deliver practical insight into incident response realities. Attendees will leave with a clearer understanding of how today’s attacks progress, what effective response looks like in high pressure situations, and how organisations can prepare to act decisively when it matters most.
Speakers
Will Barlow, Director, Incident Response EMEA, CrowdStrike
Stuart Wiggins, Practice Director, Horizon North Europe, CrowdStrike
Cross-Learning Threads
AI for Cyber Defence; Recovery and Continuity
Session Keywords
AI enabled threat; AI for Cyber Defence; Detection, response, and forensics; Human factors and culture; Threat landscape and intelligence
WK06
12:10 - 13:00
Carron 1 & 2
Sponsored by
DAY 2 – THURSDAY 23 APRIL
Operationalising Offensive Security at National Scale
Public sector organisations face complex, persistent threats. Yet offensive security often remains episodic, manual, and disconnected from enterprise architecture. This session explores how to design and operationalise offensive security as a scalable, repeatable capability embedded within your security architecture. We’ll break down the architectural components required to support continuous adversary simulation, attack path validation, and measurable risk reduction across distributed environments.
In this interactive workshop, we will:
- Deconstruct a scalable offensive security reference architecture Explore automation, orchestration, and integration patterns
- Examine how to align offensive operations with defensive telemetry
- Test your knowledge in a live Kahoot challenge. Walk through a technical run-through of the platform in action
Designed for practitioners from both Public sector and enterprise organisations at technical and CISO levels. If you’re responsible for building, integrating, or evolving security architecture in complex environments, this is for you.
Speaker
AJ Nurcombe, Solutions Engineer UKI Lead, Horizon3.AI
Dan Bird MBE, Field Chief Technology Officer EMEA, Horizon3.AI
Cross-Learning Threads
AI for Cyber Defence
Session Keywords
AI enabled threat; AI security; Emerging and frontier topics; Offensive security; Offensive resilience
INTERACTIVE WORKSHOPS_
DAY 2 – THURSDAY 23 APRIL
Command, Control, Conversation: Detecting and Mitigating LLM Cyber-Attacks and C2
Interactive Deep Dive: As the adoption of AI accelerates, so too does its use within offensive cyber workflows across the kill chain; from offensive cyber operations and hacking, to command and control, and exploitation. Industry, academia, and government must ensure that our defensive capabilities evolve at this same pace.
This interactive, scenario driven, workshop will focus on the dual nature of AI in cyber security covering two key themes. The first theme will explore the real threat posed by attackers who are weaponising LLMs in the wild. We will explore open-source threat reporting on LLM-powered malware, cyber operations, and hacking, looking at the technical details behind these attacks.
WK09
13:20 – 14:10
Boisdale 1 & 2
In partnership with
The second theme will focus on defence. We will introduce the current art of the possible in AI attack detection, highlight what we are seeing from industry and academia, and connect this with more conventional deception techniques.
This workshop is ideal for researchers, industry, and academia working, or seeking to work, in identifying and responding to AI enabled cyber-attacks.
In this workshop participants will: understand how the threat landscape is evolving as LLMs are misused; explore techniques for detecting and mitigating LLM cyber-attacks and C2; and engage with academia, industry, and government on existing capabilities and how the threat landscape may evolve in future.
Speakers
Ricky L, Tech Director ACD2.0, National Cyber Security Centre
James S7, AI And Security Researcher, National Cyber Security Centre
Rachel P, Data Science and AI Research Lead, National Cyber Security Centre
Kate C, Senior Researcher, National Cyber Security Centre
Matthew B8, Active Cyber Defence Tech Lead, National Cyber Security Centre
Senior representative, National Cyber Security Centre
Session Keywords
AI Enabled Threat; AI Security; Detection, response and forensics; Threat landscape and intelligence
WK12
13:20 - 14:10
Carron 1 & 2
Sponsored by
DAY 2 – THURSDAY 23 APRIL
Defining Minimum Viable Company: How Organisations Keep Running When Trust Is Gone
Scenario Exercise: When a major cyber incident strikes, attempting to “recover everything” is often unrealistic — and sometimes unsafe. What matters is knowing your Minimum Viable Company (MVC): the smallest set of capabilities your organisation must restore to continue operating, communicate clearly, and retain trust under pressure.
In this fast-paced, hands-on workshop, participants are placed into a shared cyber crisis scenario where trust in systems, identity, and data is already compromised. Working in mixed leadership roles — spanning board, executive, financial, operational, and security perspectives — each table must make a series of real-world recovery decisions as the situation escalates.
Each industry specific table produces clear, practical outputs: explicit MVC trigger statements, ownership of key decisions, chosen recovery posture, and the risks they are prepared to accept. In just 45 minutes, participants experience the tension of making high-impact decisions with incomplete information — and leave with a sharper understanding that cyber resilience is not about more tools, but about fewer, clearer decisions made early and rehearsed before they are needed.
This workshop is ideal for CISOs, business leaders, board-level stakeholders, and anyone responsible for operational resilience, crisis decision-making, or organisational continuity.
Speakers
Lesley Kipling, Chief Security Advisor, Microsoft
Dr Jon Davies, Chief Security Advisor, Microsoft
Session Keywords
Legal, regulatory, and policy; Recovery & Continuity; Strategy, governance, and risk
INTERACTIVE WORKSHOPS_
DAY 2 – THURSDAY 23 APRIL
Best Practice In Securing Cyber Security Investment - Don’t Sell Fear!
Guided workshop: How much should businesses invest in their cyber security?
How do you balance spend and risk? Using Gartner’s Protection Level Agreement (PLA) Framework, participants will be guided through the key considerations that influence cyber security investment decisions. The workshop will explore how to assess protection levels against business outcomes, rather than relying solely on technical controls or fear-driven risk narratives.
WK11
14:30 – 15:20
Boisdale 1 & 2
Sponsored by
Through collaborative discussion, outcome-driven measures, and cross-industry insights from fellow participants, the group will work through the PLA framework together. This interactive approach ensures the session is not only informative, but directly applicable to real-world organisational contexts.
By the end of the workshop, participants will:
– Understand how the PLA framework works and how it can be applied within their organisation
– Learn best practices for aligning cyber security investment with business priorities and outcomes
– Gain practical insight into benchmarking protection levels across different industries
– Be able to articulate cyber security investment in positive, value-based terms, rather than purely as risk mitigation
Who Should Attend:
This workshop is ideal for CIOs, CISOs, Heads of IS, Heads of Risk and CFOs.
Speakers
Nigel Pink, Head of Corporate Solutions UK, ESET
Session Keywords
Economics and programme management
WK01
14:30 - 15:20
Carron 1 & 2
In partnership with
DAY 2 – THURSDAY 23 APRIL
The Future of Cyber Regulation: Co-Designing CSR Bill Implementation and Secondary Legislation
Collaborative Roundtable: The Cyber Security and Resilience Bill marks a step-change in how the UK regulates the cyber resilience of essential, digital and managed services and their supply chains to strengthen economic and national security. Effective implementation, secondary legislation, and guidance to regulators and industry will be critical to ensuring the regime is proportionate, effective and delivers real-world outcomes.
The policy team in the Department for Science Innovation and Technology responsible for the Bill and implementation will run a collaborative session at a formative moment in the policy cycle, as they develop the proposals for implementation ahead of formal consultation later this year. This workshop is for regulators, industry, digital and managed service providers, and policy professionals.
The workshop will be structured as a policy studio, with facilitated discussions focused on specific elements of implementation, secondary legislation and other related products like guidance. Participants will be invited to share their expertise, insights, and operational experiences, to help shape solutions that balance national security and resilience outcomes with compliance burdens.
Speakers
Veena Dholiwar, Cyber Security and Resilience, Senior Policy Lead, Department for Science, Innovation and Technology (DSIT)
Nicholas Dodd, Head of Regulatory Policy, Cyber Security and Resilience Bill, Department for Science, Innovation and Technology (DSIT)
Leora Kent, Head of Security and Resilience Requirements, Cyber Security and Resilience Bill, Department for Science, Innovation and Technology (DSIT)
Senior representatives, Department for Science, Innovation and Technology (DSIT)
Session Keywords
Legal, regulatory and policy; Strategy governance, risk; Sector specific
IN THE SPOTLIGHT AT CYBERUK
Lightning Talks on the Spotlight Stage
Exhibition Hall
Head to the Spotlight Stage in the Exhibition Hall during the refreshment and lunch breaks to enjoy 5-minute, bite-size shots of inspiration, solutionfocused practitioner or research-led talks delivered by delegates.
Sponsored
by
Live Streaming Zone
Exhibition
Hall
Make your way to the Live Streaming Zone where you can watch live all plenary and selected track sessions in a more informal setting. Or switch between parallel sessions. Headphones are available.
All plenary and selected track sessions are also streamed to YouTube for you to watch on any connected device. Look out for the CYBERUK ONLINE symbol in the programme for sessions available on YouTube.
Sponsored
by


LIGHTNING TALKS_
CYBER ECOSYSTEM ZONE_
The Cyber Ecosystem is an integral part of CYBERUK.
The Cyber Ecosystem Zone, sponsored by IASME, showcases how collaboration across industry, government and education can unlock scale, resilience and meaningful impact in the UK’s cyber landscape. By building trusted, inspiring and resilient environments, we create fertile conditions for regional and national partnerships to flourish and for a dynamic cyber ecosystem to thrive.
In this zone, you’ll discover how the NCSC is leveraging its trusted brand to grow and scale the UK’s cyber ecosystem—strengthening national resilience, building skills, and developing the capability needed to meet tomorrow’s challenges. Explore the achievements of the past decade, learn about the exciting initiatives underway, and find out how you can be part of shaping the UK’s cyber future.
Securing the future. Together.
Exhibition Hall – next to the NCSC Zone
LIGHTNING TALKS_
EXHIBITION FLOORPLAN_
C3 2T Security
E1 Accenture
C6 Acubed IT Solutions Limited
E25 Acumen Cyber
C26 Airbus Defence and Space
D5 Akamai
MA1 Amazon Web Services
E17 Amentum
MA4 Aretiico
C17 Armis
B20 Arqit
F16 Assurix
C24 Australian Trade and Investment Commission (Austrade)
A32 Awerian
D8 Babcock International Group
D3 BAE Systems Digital Intelligence
SS5 Barrier
F17 BeCrypt
B17 Belkin Cybersecurity
E13 Bridewell
B10 BT Business
A4 Bureau Veritas Cybersecurity B23 CACI Ltd
IVC-1 Cavero Quantum B5 Censys C1 CGI D21 Check Point Software Technologies Ltd
F2 CHEDDAR
C22 Cisco
B4 Citation Cyber
SS6 Closed Door Security MA8 Cloudflare
IVC-2 CloudPeek AI
SS9 Condatis MA10 Corelight + Endace
G5 CRANE
C21 Cribl
B6 Cryptify AB
F6 CSIT, Queen’s University Belfast
IVC-3
F27 Cyberfort SS1 CyberScotland F8 CyBOK Community Interest Company
A30 Cyderes G35 Cymru Wales F15 CYSIAM A16 Deloitte IVC DSIT F30 Dstl B29 DXC C23 Elastic
B16 Firebrand Training Limited
B22 Fognigma B15 Forescout D17 Fortinet D9 FullProxy
G3 Glasgow Cyber Defence Lab: University of Glasgow
F5 GOLDEN VALLEY
C20 Google Cloud
G27 Government Cyber Unit and Goverment Cyber Profession
D2 GreyNoise Intelligence
F4 Hacktivity Cyber Security Labs
IVC-4 Hacktonics
E30 Hexegic
G25 HMGCC
D10 HORIZON3.AI
B2 HP Inc.
F13 IASME
A8 IBM
SS8 i confidential
G17 Indelible Data Ltd
G1 Information Security Group, Royal Holloway
E28 Island
IVC-5 Juliett
B7 JUMPSEC Ltd
SS2 Kick ICT Group
F25 Kocho
C15 KPMG
D1 L3Harris
F20 Lab539
G7 Lancaster University
SS11 Leidos
E21 Leonardo
F18 lowRISC
B25 LRQA
SS4 Lupovis
C9 Mattermost
F29 Methods
C7 Microsoft Security
F34 MHCLG - Local Digital
G29 MOD
IVC-6 MyCena Limited
G31 National Crime Agency
F36 National Cyber Force (GCHQ)
C14 NCC Group
A22 Netcraft
E26 Netskope
D4 Nexor
F19 Northrop Grumman
D22 Nozomi Networks
E23 Obrela
F32 Ofcom
F12 opliciti
D6 OPSWAT
SS12 OSP Cyber Academy
IVC-7 PA Consulting
C13 Palo Alto Networks D19 PentenAmio
IVC-8 Photarix
D24 PointWire B11 PQShield
IVC-9 PRAEFERRE
B18 QA
C19 QinetiQ E24 Rapid7 A18 Raytheon UK
D11 Recorded Future
IVC-10 Reliable Insights
E19 Reliance Cyber
G13 Report URI
F7 Restore Technology
A6 Reversec
F23 Risk Ledger
C11 Roke
G11 ROOTWALL.AI
F38 Rosa Service Organisation
F14 Salt Communications
C5 Salus
E11 SANS Institute
C8 Sapphire A26 Saviynt
LEAD SPONSOR STANDS
PARTNER STANDS
PREMIUM STANDS
STANDARD STANDS
SME STANDS
GOVERNMENT STANDS
ACADEMIA STANDS
SCOTLAND STREET
INNOVATION ZONE
SS14 SCC
SS7 Schneider Electric G15 SCI Semiconductor
MA3 ScottishPower
E20 Searchlight Cyber A24 Silobreaker
F9 Sitehop Ltd
F3 Socura F40 Software Ambassador Scheme & PSTI
A12 Softwerx A14 Sonatype
D20 SpecterOps
B1 Surevine
SS3 Systal Technology Solutions
D15 Tanium
C16 Tenable®
C10 Thales
B13 The CRC Network
SS10 The Cyber Scheme
B9 Thinkst Canary
E22 Tines
B24 Trellix
E15 TrendAI™ and Atos: In Partnership
B14 Twinstream F21 UK Research and Innovation (UKRI)
D16 Ultra I&C Cyber UK
IVC-11 Unhacked™
E18 Varonis
D14 Viasat
IVC-12 VIVIDA
B3 VulnCheck
SS16 Waterstons Ltd
B21 Wiz
G9 Wolf Network Security
B27 WorkNest Secure
G19 Xewli
F10 Zaizi
B12 Zscaler
SPONSORS_
Lead Sponsor
Stand MA4
Aretiico
Aretiico is the UK’s first and only WebTrust backed Certificate Authority, created to strengthen national digital sovereignty and long-term resilience. It was founded to ensure the UK retains direct control over its cryptographic roots, key material, and trust infrastructure. Aretiico delivers WebTrustbacked public PKI capability alongside private PKI services, enabling organisations to operate sovereign, independently governed trust environments.
Sovereignty defines Aretiico’s mission. National trust services must remain under UK jurisdiction, free from external dependencies and opaque supply chains. For years, organisations were constrained by rigid on-premise PKI or cloud models that weakened self-determination, while root control frequently sat overseas. Aretiico was created to change this—delivering a sovereign trust platform designed to evolve as cryptographic standards, threats, and national requirements shift. The platform reflects a modern, engineering-led approach to PKI. Its modular, standards-aligned architecture supports secure deployment across on-premises, trusted cloud, and tightly controlled operational settings. High-assurance cryptography, automated and auditable infrastructure, and policy-driven configuration ensure operational integrity while allowing organisations to align PKI estates with regulatory, mission, and sovereignty needs.
The transition to post-quantum cryptography makes this engineering discipline essential. Current algorithms will not endure against quantum-capable adversaries, and only those with sovereign control of their cryptographic roots will transition with clarity and credibility. Aretiico ensures the UK approaches this shift with confidence and long term assurance. Aretiico supports organisations across identity, devices, operational technology, enterprise infrastructure, and machine-to-machine trust—securing the future by securing its cryptographic roots.
Lead Sponsor
Stand MA3
Scottish Power
We’re on a journey to a better future.
ScottishPower is part of the Iberdrola Group, a global energy company, one of the world’s largest integrated utilities and a leader in wind energy. We are securing affordable and clean energy, modernising networks to improve quality of service and increasing customer choice through digital enhancements to put our customers in control of their energy usage.
We employ over 6,000 people including highly skilled engineers working on cutting edge innovation projects in our networks business and building offshore windfarms in the most challenging conditions. Sustainability drives everything we do. Our climate ambitions, the importance of energy security and the cost-of-living crisis all point to a need for speed in delivering more green, more secure, and more affordable energy.
We want to go faster and we’ve been leading the way for decades. As the UK’s only vertically integrated energy company, we are delivering the UK’s green energy transition. From building the clean renewable power needed to reduce reliance on fossil fuels, to rewiring the electricity grid for the future and supporting customers with clean technology in their homes and businesses, all our energy is going towards building a better future. And we’re investing £18m every working day to make this happen. We connect communities, we invest in communities, we help to build communities. What we do really does matter, for both people and for the planet, and this is what drives our teams to do extraordinary things, every, single day.
TechTalks Sponsor
Stand C14
NCC Group
We’re a people powered, tech-enabled global cyber security and resilience company with over 2000 colleagues around the world.
For over 25 years we’ve been trusted by the world’s leading companies and Governments to manage and deliver cyber resilience, working together to create a more secure digital future.
We are proud to deliver important and groundbreaking projects for our clients.
Leaders’ Dinner Sponsor
Stand MA1
Amazon Web Services
Amazon Web Services (AWS), the world’s most comprehensive and broadly adopted cloud, enables customers to build anything they can imagine with the industry’s greatest choice of fullyfeatured services and solutions. Security is our top priority. Our infrastructure and services are architected to provide the most secure cloud computing environment available today, to meet the unique requirements of even the most sensitive workloads across government, financial services, and healthcare sectors.
Powered by the world’s largest and most extensive global infrastructure, AWS delivers unparalleled scalability, performance, and reliability for applications running in the cloud, on-premises, or at the edge. We’re also driven by a commitment to deliver industryfirst capabilities, constantly looking around corners and thinking years ahead to innovate on behalf of our customers. Through our trusted partner network, customers can leverage trusted third-party offerings and expertise to optimize their cloud-native workloads, fill expertise gaps, and maximize their investments.
Networking Sponsor
Welcome Drinks Sponsor
Stand C22
Cisco is revolutionizing how infrastructure and data connect and protect organizations in the AI era. We help organizations transform data centers to power AI, create future-proofed workplaces, and ensure digital resilience. Only Cisco combines the power of the network with security, observability, and collaboration to help organizations thrive.
Stand F23 Risk Ledger
Risk Ledger is the cutting-edge platform for third-party risk management, transforming how organisations secure their supply chains. By empowering security and procurement teams with real-time insights, Risk Ledger ensures complete visibility and control over third-party risks.
Our Defend-as-One approach fosters collaboration, reduces compliance burdens, and strengthens your cyber defences with evidence-based, up-to-date risk assessments. With Risk Ledger, every link in your supply chain is fortified, ensuring your organisation is protected against emerging threats in the supply chain. Together, we are building a more secure future because every link matters in cybersecurity.
SPONSORS_
Resilience Track Sponsor
Technology Track Sponsor
Thales is a global technology leader in defence, security, aerospace, space, and digital identity. With a strong UK presence across multiple key sites, we deliver cutting-edge solutions that secure borders, protect data, and enable digital transformation for governments and businesses. From cybersecurity and artificial intelligence to secure communications and space technologies, we underpin national resilience and digital security.
As an organisation deeply invested in the UK’s digital future, we secure critical national infrastructure and protect millions of digital identities, from passports to banking credentials and eSIMs. We have pioneered market leading solutions that enhance security and trust. Our digital identity solutions have transformed the way people access services securely, and our expertise in AI and data analytics ensures smarter, safer decision-making.
Threat Track Sponsor
Akamai is the cybersecurity and cloud computing company that powers and protects business online. Akamai Security provides market-leading solutions to secure your applications and networks using real-time intelligence and adaptive AI. Stand C10
Tenable® is the exposure management company, exposing and closing the cybersecurity gaps that erode business value, reputation and trust. The company’s AI-powered exposure management platform radically unifies security visibility, insight and action across the attack surface, equipping modern organizations to protect against attacks from IT infrastructure to cloud environments to critical infrastructure and everywhere in between. By protecting enterprises from security exposure, Tenable reduces business risk for approximately 44,000 customers around the globe.
Learn more at tenable.com
Make Google part of your security team with unmatched threat visibility, a unified security platform, and Mandiant frontline experts — supercharged by AI.
Organisations can reduce digital risk and secure their AI transformation with the same cybersecurity specialists, capabilities, and secure enterprise platforms Google uses to keep more people and organisations safe online than anyone else in the world, powered by our industry-leading threat intelligence. AI enhances all of these components, enabling security teams to detect more threats, minimise toil, and take productivity to new levels.
Ecosystem Track Sponsor
Cyber Ecosystem Zone Sponsor
Live Streaming Zone Sponsor
F13
IASME is an NCSC Delivery Partner for Cyber Essentials, Cyber Incident Exercising and Cyber Incident Response (Standard Level). We also deliver the Defence Cyber Certification in partnership with the Ministry of Defence (MOD) and our own certification schemes in IoT and Maritime cyber security.
IASME work with a network of 400 Certification Bodies that employ more than 950 Assessors across the UK and Crown Dependencies. We are committed to inclusion and fairness, and we strive to ensure cyber security certification is accessible and affordable for all organisations.
Stand C15
KPMG Cyber helps organisations stay ahead of evolving threats with end-to-end security solutions.
We deliver strategy, transformation and resilience, backed by advanced tools like 4DI and Cyber Risk Insights, and global insights through the I4 Forum. Our capabilities span NCSC Assured Incident Response and Penetration Testing, Security Operations, OT security, AI, data security, and identity management.
From building secure architectures to managing complex risks, we combine deep sector expertise with cutting-edge technology to enable trust, resilience and accelerate digital transformation. KPMG empowers businesses to anticipate, withstand, and recover from cyber threats – driving trust and confidence in a connected world. Stand
Scotland Street
Stand SS1
CyberScotland
Our partners are committed to delivering the ambitions of The Strategic Framework for a Cyber Resilient Scotland – building a safer, more secure digital future for everyone.

Lanyard Sponsor
Stand C17 Armis
Armis, the cyber exposure management & security company, protects the entire attack surface and manages the organization’s cyber risk exposure in real time. In a rapidly evolving, perimeter-less world Armis ensures that organizations continuously see, protect and manage all critical assets – from the ground to the cloud. Armis secures Fortune 100, 200 and 500 companies as well as national governments, state and local entities to help keep critical infrastructure, economies and society stay safe and secure 24/7. Armis is a privately held company headquartered in California.
SPONSORS_
Interactive Workshops Sponsors
Purpose-built in the cloud with a single lightweight-agent architecture, the Falcon platform delivers rapid and scalable deployment, superior protection and performance, reduced complexity and immediate time-to-value.
ESET® is a global cybersecurity leader trusted by more than 500,000 businesses worldwide. For over 30 years, we’ve delivered AI-powered, human-enhanced protection that stops threats before they happen. Whether it’s endpoint, cloud or mobile protection, our AI native, cloud first solutions and services remain highly effective and easy to use, keeping organisations protected without interruption. Through 24/7/365 Managed Detection and Response, Threat Intelligence and Cybersecurity Awareness Training, ESET strengthens business resilience in an ever-evolving digital world. Come and talk to us about how ESET can enhance your security posture and safeguard your organisation.
Interactive Workshops Sponsors
Stand D10
Horizon3.ai
Horizon3.ai empowers organizations to continuously verify their security posture with NodeZero®, the industry’s leading autonomous pentesting platform. Built to think and act like an attacker but operate safely in production, NodeZero identifies exploitable weaknesses, prioritizes fixes based on real world impact and verifies remediation at scale. Customers across manufacturing, healthcare, finance and national security rely on NodeZero to reduce risk and accelerate security outcomes.
Stand C9
Mattermost
Mattermost is the secure, sovereign collaboration platform built for mission-critical and cyber resilient operations. Trusted by government, defence, intelligence, and critical infrastructure teams, it powers high stakes workflows, from incident response and threat coordination to mission planning, across DDIL, tactical, and enterprise environments. With on prem and private cloud deployment, workflow automation, and AI-accelerated capabilities, Mattermost delivers full operational control, improved cyber resilience, and reduced mean time to action in even the most demanding conditions.
Interactive Workshops Sponsors
Stand C7
Microsoft Security
As the defender of one of the most targeted estates in the world, we prioritise security above all else. Security is built into the way we design, build, test, and operate all Microsoft technology. Through the Secure Future Initiative, we’re bringing together every part of Microsoft to deliver the most secure cloud – the Microsoft Cloud.
This provides a unique advantage for the customers. We are leveraging these innovations and best practices from securing Microsoft and our 1M Microsoft Security customers to create the AI first end to end security platform – purpose built to support customers in securing their future in the age of AI.
Stand C13
Palo Alto Networks
As the global AI and cybersecurity leader, Palo Alto Networks (NASDAQ: PANW) is dedicated to protecting our digital way of life via continuous innovation. Trusted by more than 70,000 organizations worldwide, we provide comprehensive AI-powered security solutions across network, cloud, security operations and AI, enhanced by the expertise and threat intelligence of Unit 42. Our focus on platformization allows enterprises to streamline security at scale, ensuring protection fuels innovation.
Explore more at paloaltonetworks.com
Bursary Sponsors
Stand A22
Netcraft
Netcraft is a trusted cybersecurity leader in brand protection and digital risk management, relied on by CISOs, anti-fraud teams, and security professionals worldwide. Its advanced cybercrime disruption platform uses AI, machine learning, and automation to process more threat data than any other provider, delivering unmatched visibility across the threat landscape. This intelligence empowers Netcraft to detect, disrupt, and remove scams and cyber threats with speed, precision, and scale. With the industry’s lowest false positive rate for malicious content, Netcraft provides accurate protection while ensuring minimal disruption to legitimate users and operations.
Stand A26
Saviynt
Saviynt’s AI-powered identity platform manages and governs access to an organization’s applications, data, and business processes. Customers trust Saviynt to safeguard their digital assets, drive operational efficiency, and reduce compliance costs. Built for the AI age, Saviynt is helping organizations safely accelerate their deployment and usage of AI today. Saviynt is recognized as the leader in identity security, with solutions that protect and empower the world’s leading brands, Fortune 500 companies, and government institutions. For more information, please visit www.saviynt.com.
SPONSORS_
SME Innovation Zone Partner
Stand IVC Department for Science, Innovation & Technology
The Department for Science, Innovation and Technology (DSIT) brings together the relevant parts of the former Department for Business, Energy and Industrial Strategy and the former Department for Digital, Culture, Media and Sport. DSIT positions the UK at the forefront of global scientific and technological advancement, driving innovations through programmes like Cyber Runway or Cyber ASAP, which improve lives and sustain growth. DSIT also delivers talent programmes, physical and digital infrastructure and regulation to support our economy, security and public services, alongside strong support for research and development.
Sustainability Sponsor
Stand A14
Sonatype is the leader in AI-driven DevSecOps. As the maintainers of Maven Central and creators of Nexus Repository, it has spent two decades securing open source software and supporting modern software supply chains.
With strong visibility and a unified platform, Sonatype helps enterprises safely harness open source and AI. Its solutions guide component and model selection, block malicious code, and automate vulnerability management to ensure faster, more reliable builds. Trusted by over 15 million developers, Sonatype supports nearly 2,000 organizations worldwide, including 70% of the Fortune 100, enabling secure and efficient modern software development.
Women in Cyber Breakfast Sponsor Schools Outreach Sponsor
Accenture is a leading solutions and services company that helps the world’s leading enterprises reinvent by building their digital core and unleashing the power of AI. Our strategy is to be the reinvention partner of choice and the most clientfocused, AI-enabled, great place to work in the world.
Through our Reinvention Services we bring our capabilities together across strategy, consulting, technology, operations, Song and Industry X with our deep industry expertise. Our purpose is to deliver on the promise of technology and human ingenuity and measure our success by the 360° value we create our stakeholders.
Stand A16 Deloitte Stand E1
Our technology and business specialists put cyber to work for you to confidently embrace the future. Our powerful solutions simplify complexity and supercharge transformation. That way, you can operate with resilience and secure success for your organisation.
Our focus on personal relationships, domain experience, and deep technology and product innovation means that whatever your strategic priorities, we’ll help you improve threat awareness and visibility and strengthen your ability to thrive in the face of cyber incidents. We advise, implement, and manage cyber solutions where you need us most, across your entire extended enterprise.
Meeting Hub, Digital Delegate
Brochure & Map Sponsor
Workzone & Wi-Fi Sponsor
IBM is a leading provider of global hybrid cloud and AI, and consulting expertise. We help clients in more than 175 countries capitalize on insights from their data, streamline business processes, reduce costs and gain the competitive edge in their industries.
Thousands of governments and corporate entities in critical infrastructure areas such as financial services, telecommunications and healthcare rely on IBM’s hybrid cloud platform and Red Hat OpenShift to affect their digital transformations quickly, efficiently and securely. IBM’s breakthrough innovations in AI, quantum computing, industry specific cloud solutions and consulting deliver open and flexible options to our clients. All of this is backed by IBM’s long-standing commitment to trust, transparency, responsibility, inclusivity and service.
Barista Bar Sponsor
DXC Technology helps global companies run their missioncritical systems and operations while modernizing IT, optimizing data architectures, and ensuring security and scalability across public, private and hybrid clouds. The world’s largest companies and public sector organizations trust DXC to deploy services to drive new levels of performance, competitiveness, and customer experience across their IT estates.
Headquartered in Cambridge, Softwerx is a trusted security services partner helping resource-limited midmarket organisations stay secure in an increasingly hostile threat landscape. As Managed XDR specialists, we combine advanced Microsoft Security® technologies with automation and expert human insight. Our UK-based team provides 24x7x365 monitoring, proactive threat hunting, rapid incident response, and professional services to reduce risk and strengthen resilience. All security data remains within your environment, and Softwerx activity is always fully visible and transparent. We deliver the Enterprise-grade cybersecurity the midmarket deserves, handling threats so you can run your business with confidence.
Wellness Lounge and Juice Bar Sponsor
Wiz secures everything built and run in the cloud. Our platform powers a new operating model for security, development, and ops teams by providing a holistic view of risk. We give everyone clear visibility into their cloud and AI environments, enriched with context so they can prioritize what matters most.
PARTNER EXHIBITORS_
Stand C6
Acubed IT Solutions Limited
Acubed IT is a UK-based provider of secure, scalable, and innovative technology solutions for National Security, Defence, and the Public Sector. Our fully SC/DV-cleared team specialises in secure application development, cross-domain systems, and advanced cryptographic research.
Core services include cross-domain system integration, post-quantum cryptography risk assessments (PQC-RA), and collaborative R&D through Knowledge Transfer Partnerships. We have developed the Cross Domain Hybrid Application (CDHA) Framework – a unique solution to address crossdomain application challenges. In partnership with academia and Innovate UK, we advance cybersecurity through postquantum cryptography, AI-driven vulnerability scanning, and next-generation encryption technologies, shaping the future of secure digital systems.
Stand C26 Airbus Defence and Space
Airbus Defence and Space Cyber provides products and solutions across all domains as a critical enabler for multidomain operations. Our crypt-key products and solutions are governed to the highest standard, certified by the National Cyber Security Centre (NCSC), ensuring that critical sovereign operations are protected, can be trusted and are reliable.
We remain at the forefront of developing crypt-key solutions of the future, enabling mission-critical solutions to operate safely and securely, in an increasingly connected and hostile world. As a trusted provider of crypt-key solutions, we secure the mission, protecting the interests of the UK and 5 EYES Nations.
Stand C24
Australian Trade and Investment Commission (Austrade)
The Australian Trade & Investment Commission (Austrade) is introducing innovative Australian cyber solutions to the United Kingdom. Capabilities extend across governance and risk intelligence, behavioural analysis of insider threats, open-source and operational intelligence, identity and authentication systems, advanced encryption including quantum and post-quantum methods, and sovereign cyber and defence technologies.
Avertro | www.avertro.com
Cosive | www.cosive.com
DTEX | www.dtex.ai
Elezar | www.elezar.io
OSINT Combine | www.osintcombine.com
PentenAmio | www.pentenamio.com
QuintessenceLabs | www.quintessencelabs.com
Salt Group | www.saltcybersecurity.co.uk
Senetas | www.senetas.com
TomorrowX | www.tomorrowx.com
Stand D3 BAE Systems Digital Intelligence
BAE Systems Digital Intelligence is home to 4,700 digital, cyber and intelligence experts across 16 countries who operate at the cutting edge of digital innovation and at the heart of organisations that keep vital infrastructure running, national security protected and armed forces prepared. We help customers make sense of a complex security and technology landscape – providing the power of perspective so they can confidently make the critical decisions that keep our societies safe and able to thrive. Whether on land, in the air, at sea, in space or cyberspace, we’re customers’ digital mission partner at every step of the journey.
Stand D21
Check Point Software Technologies Ltd
Check Point Software Technologies Ltd. (checkpoint.com) is a leading protector of digital trust, utilizing AI-powered cyber security solutions to safeguard over 100,000 organizations globally. Through its Infinity Platform and an open garden ecosystem, Check Point’s prevention first approach delivers industry leading security efficacy while reducing risk. Employing a hybrid mesh network architecture with SASE at its core, the Infinity Platform unifies the management of on-premises, cloud, and workspace environments to offer flexibility, simplicity and scale for enterprises and service providers.
Stand MA8 Cloudflare
Cloudflare, Inc. (NYSE: NET) is the leading connectivity cloud company. It empowers organizations to make their employees, applications and networks faster and more secure everywhere, while reducing complexity and cost. Cloudflare’s connectivity cloud delivers the most full featured, unified platform of cloud-native products and developer tools, so any organization can gain the control they need to work, develop, and accelerate their business.
Powered by one of the world’s largest and most interconnected networks, Cloudflare blocks billions of threats online for its customers every day. It is trusted by millions of organizations – from the largest brands to entrepreneurs and small businesses to nonprofits, humanitarian groups, and governments across the globe.
Stand MA10
Corelight + Endace
Corelight and Endace protect government, defence, critical infrastructure, and Fortune 1000 enterprise networks around the globe. Together, Corelight and Endace give security and network teams powerful threat detection and the actionable evidence they need to defend against network threats and outages quickly and effectively.
Corelight transforms network and cloud activity into rich insight that security teams can use to detect and hunt for threats, solve network issues and accelerate incident response. Endace’s scalable, always-on packet capture records the definitive, packet level forensic evidence security, network and IT teams need to respond conclusively to even the most challenging threats and issues.
Stand D17 Fortinet
Fortinet (Nasdaq: FTNT) is a driving force in the evolution of cybersecurity and the convergence of networking and security. Our mission is to secure people, devices, and data everywhere, and today we deliver cybersecurity everywhere our customers need it with the largest integrated portfolio of over 50 enterprise-grade products. Well over half a million customers trust Fortinet’s solutions, which are among the most deployed, most patented, and most validated in the industry.
PARTNER EXHIBITORS_
Stand D9
Fullproxy
FullProxy is a rapidly growing cyber security consultancy delivering world-class advice and solutions that help organisations reduce cyber risk and maximise technology investment. We support major public and private sector clients across the UK, particularly in data-sensitive industries such as Healthcare, Education, Financial Services and Critical Infrastructure.
As elite partners of F5, Fortinet and AppViewX, we help customers accelerate value, enhance cryptographic resilience and prepare for post-quantum security.
Shortlisted as Scottish Cyber Security Company of the Year 2025 and recognised as one of TechUK’s Top 200 Growing Companies, FullProxy is headquartered in Glasgow and serves clients across the UK and internationally.
Stand D1
L3Harris
L3Harris Technologies is the Trusted Disruptor in the defence industry. With customers’ mission-critical needs always in mind, our employees deliver end-to-end technology solutions connecting the space, air, land, sea and cyber domains in the interest of national security.
Visit L3Harris.com for more information.
Stand D19
PentenAmio
PentenAmio is proud to protect those who protect us. A leading provider of secure mobile communications, AI enabled cyber defence, and electronic deception technologies, our 300-strong highly experienced experts deliver advanced solutions tailored to the evolving demands of modern defence and security across the UK, Australia, and our allies.
Stand D11
Recorded Future
Recorded Future is the world’s largest threat intelligence company. Recorded Future’s Intelligence Cloud provides end-to-end intelligence across adversaries, infrastructure, and targets. Indexing the internet across the open web, dark web, and technical sources, Recorded Future provides real-time visibility into an expanding attack surface and threat landscape, empowering clients to act with speed and confidence to reduce risk and securely drive business forward. Headquartered in Boston with offices and employees around the world, Recorded Future works with over 1,600 businesses and government organizations across more than 74 countries to provide real-time, unbiased and actionable intelligence.
Stand C8 Saphire
With over 30 years of experience securing organisations across the UK and globally, Sapphire delivers comprehensive cyber solutions tailored to your needs, spanning across consultancy, managed services, IT/OT and beyond.
Our team of experts integrates seamlessly with yours, empowering you to protect your digital infrastructure, mitigate risks, and maintain compliance. From proactive threat monitoring to strategic guidance, we are your trusted partner every step of the way, ensuring the security of your operations, people, and reputation.
Stand D15 Tanium
Tanium Autonomous IT offers the most comprehensive solution for intelligently managing endpoints across industries, providing capabilities for asset discovery and inventory, vulnerability management, endpoint management, incident response, risk and compliance and digital employee experience. The Tanium Autonomous IT platform supports customers worldwide, including 40 of the Fortune 100, to become unstoppable by delivering increasingly efficient operations and an improved security posture at scale, with confidence, and in real time.

PREMIUM EXHIBITORS_
Stand E25 Acumen Cyber
At Acumen, we protect modern businesses from the complexities of cyber threats 24/7. Our commitment is to ensure your business operates seamlessly, free from the disruption of cyber incidents.
We don’t just offer security software; we are architects delivering your peace of mind. Rooted in our deep understanding of the rapidly evolving threat landscape, we are dedicated to innovation and advancement within the industry, staying ahead of the pace of continuous threat so you don’t have to.
Stand E17 Amentum
Amentum is a global leader in advanced engineering and innovative technology solutions, trusted by the UK and US governments to address their most significant and complex challenges in science, security, and sustainability. We have more than 50,000 employees in 70 countries across all 7 continents.We enable governments, their agencies, and operators of essential services to secure their critical assets and generate insight from their data.
Our cyber, data, system integration, and physical security specialists design, develop, implement, assure, and manage the delivery of highly complex digital solutions, working across the project lifecycle to deliver enhanced outcomes to our customers.
Arqit secures the world’s most critical data with quantumsafe encryption software. Simple, scalable, and compliant, its products integrate with existing infrastructure, and requires no rip and replace of hardware. Arqit provides a complete “Detect, Protect, Comply” solution for governments and enterprises that detects and inventories cryptographic assets, protects data, ensures compliance, and safeguards transition to the post-quantum era. Arqit’s primary product offerings are Encryption Intelligence and NetworkSecure™. Encryption Intelligence detects cryptographic exposure, identifies vulnerabilities, and maps dependencies. NetworkSecure™ protects data in transit with provably secure post-quantum cryptography and contributes to establishment of confidential compute environments for complete data sovereignty.
Stand D8
Babcock International Group
Our Purpose, to create a safe and secure world, together, defines our strategy.
We provide through-life technical and engineering support for our customers’ assets, delivering improvements in performance, availability, and programme cost. We deliver these critical services to defence and civil customers, including engineering support to naval, land, air and nuclear operations, frontline support, specialist training and asset management.
We design and manufacture a range of defence and civil specialist equipment, from naval ship and weapons handling systems to liquid gas handling systems. We also provide integrated, technology-enabled solutions to our defence customers in areas such as secure communications, electronic warfare and air defence.

Stand F17
Becrypt
Becrypt provides high-assurance cybersecurity solutions for both public and private sectors, enabling secure operations in a complex digital landscape. With a focus on innovation and customer-centricity, Becrypt delivers a comprehensive range of products and services, including secure endpoint solutions, cross-domain capabilities, and secure mobile applications.
Our flagship offerings, Becrypt OS—the world’s most secure enterprise grade operating system and Becrypt APP-XD— the first API centric Cross Domain Solution, are designed to provide unparalleled protection against cyber threats. Using government-accredited security standards, we help our customers safely and rapidly deploy mobile, endpoint and cloud technologies, driving greater business flexibility, agility and productivity.
Stand B17 Belkin Cybersecurity
Since 2006, Belkin has delivered Secure KVM solutions for government and military users, helping shape NIAP and Common Criteria standards.
Our mission is to protect critical networks while improving efficiency and decluttering operator workspaces. We pioneered innovations such as Secure KVMs, Secure KVM Remote with Integrated Keyboard, and Universal Video Compliant Secure KVMs. By maintaining strict network isolation, our solutions safeguard sensitive assets and enable seamless work across secure and non-secure systems. Belkin Secure KVMs protect against desktop vulnerabilities, preserve air-gap security, and defend mission-critical environments in government, energy, utilities, and finance from increasingly sophisticated cyber threats.

Stand E13
Bridewell
Bridewell is the trusted cyber security partner for organisations operating within Critical National Infrastructure (CNI), as well as companies who want the highest standard of cyber security.
Our team are highly accredited by major industry bodies and have extensive experience of delivering cyber consulting and managed security services across highly regulated sectors. As a long-standing Microsoft partner, our team are experts in maximising the effectiveness of Microsoft Security technology to deliver robust and effective solutions.
We work in continuous partnership with our clients to implement the right security solutions to defend against attacks, allowing them to operate safely and securely
Stand B10 BT Business
BT Business is the UK’s leading provider of secure connectivity and cyber defence, underpinning the nation’s Critical National Infrastructure.
We protect essential services—energy, transport, healthcare, and government—through resilient networks and advanced security solutions. As a trusted partner to government and industry, we deliver end-to-end protection for sovereignty, 5G, IoT, and emerging technologies, ensuring the UK remains connected, secure, and prepared for future threats.
PREMIUM EXHIBITORS_
Stand C1
Your organisation, uninterrupted. Founded in 1976, CGI is one of the largest IT and business consulting services firms in the world. We provide comprehensive, scalable and sustainable IT and business consulting services that are informed globally and delivered locally. CGI is a trusted partner across the UK cyber security landscape, recognised for successfully delivering complex, end-to-end IT security programmes. Our sovereign capability, combined with our expertise in cloud, cyber, data, systems engineering, AI and emerging technologies, enables us to design and operate systems that are resilient, scalable and ready for tomorrow’s threats.
Stand C21 Cribl
Cribl accelerates cyber resilience across government and critical national infrastructure by giving security teams full control over their data. As the leading vendor-neutral data engine, Cribl enables organisations to route, shape and enrich telemetry from any source to any destination, improving threat detection, reducing cost and strengthening operational agility.
With expansive support for security tools and cloud platforms, Cribl helps agencies break down silos, simplify architectures and make smarter use of existing investments. By delivering the right data to the right tools at the right time, Cribl empowers defenders to act faster and protect the UK against evolving threats.
Stand A20
Cyber1st
At Cyber1st, we deliver best in class, High Grade encryption solutions, certified by NCSC and designed to protect your systems, people and reputation. BULLDOG is a PRIME compliant cryptographic device to secure data in transit for classified networks. With a small, discreet form factor, BULLDOG is the UK’s only single Person Carry capability, reducing operational overhead and providing freedom of action. Our Tactical Symmetric Key Manager (T-SKM) provides compliance with Over The Network Keying Standards; digitally generating, delivering and managing key for any PRIME enabled End Cryptographic Unit; including Ectocryp, AltoCrypt Stik and CATAPAN.
Stand F27 Cyberfort
Over the past 20 years we have combined our market leading accreditations, peerless cyber security expertise, strong technology partnerships, and investment in our future cyber professionals to deliver cyber security services which enables organisations to achieve their business and technology goals.
Stand F15
CYSIAM
CYSIAM is a UK based cyber security firm specialising in Managed Detection and Response (MDR) and National Security and Defence (NS&D), underpinned by a robust Cyber Threat Intelligence (CTI) framework. We recognise that understanding the context of cyber risks is crucial for informed security decision-making.
Our fully vetted team, with backgrounds in military intelligence, law enforcement, and national security, is trusted by public sector organisations across the UK and beyond. We provide a comprehensive range of security solutions, including continuous monitoring, threat detection, and incident response, leveraging cutting-edge technologies and intelligence-led threat hunting to mitigate cyber risks effectively.
Stand C23 Elastic
This decentralised approach empowers agencies to treat data as a product, ensuring interoperability across different security classifications (Official to Secret) without compromising sovereignty. By breaking down technical silos, Elastic enables real-time insights for mission-critical decisions, enhancing citizen services and national security while reducing total cost of ownership through infrastructure optimisation.
Stand E32
Everfox
Everfox is a global cybersecurity company specializing in defense-grade, high-assurance solutions that protect critical data, networks, and digital assets from the most complex cyber threats., Everfox builds on a 25-plus year legacy of safeguarding mission-critical systems for governments, defense agencies, regulated industries, and enterprise organizations around the world.
Stand D18
Filigran
Filigran, founded in October 2022, stands out in the crowded cyber security space with its unique open-source, threatinformed approach to Continuous Threat Exposure Management (CTEM). Its mission is to develop innovative, AI-augmented solutions designed to anticipate cyber threats, identify security gaps, and strengthen organizational security posture. The suite currently includes two solutions:
OpenCTI: structures and operationalizes holistic threat intelligence across technical, operational, and strategic levels, enabling security teams to contextualize attacks and act proactively.
OpenAEV: helps identify critical vulnerabilities and strengthen organizational security posture through advanced attack simulations, resilience testing, and crisis management exercises.
PREMIUM EXHIBITORS_
Stand B16
Firebrand Training Limited
As the go-to training provider for top industry innovators, Firebrand (part of the BPP Group) has been ranked among the world’s top 20 IT Training providers for 12 consecutive years. At Firebrand, we have been recognised by the world’s leading IT partners and became the first training provider celebrated by the WorldSkills Excellence Program, Firebrand stands as the trusted leader in accelerated skills development. Our proven accelerated model turns theory into practice. Delivered by certified IT professionals with real world expertise, every course blends hands-on labs, immersive simulations, and structured review sessions – so your teams leave ready to perform and succeed.

Stand B22 Fognigma
Fognigma is a commercial off-the-shelf software capability that enables the rapid deployment of secure, global, obfuscated, zero-trust managed networks, typically within an hour. It delivers mission specific, non attributable digital environments that support secure communications, encrypted file sharing, virtual desktop environments (VDIs), telephony, messaging, as well as secure remote access into control systems. These environments can be withdrawn at the end of an operation and leave no forensic footprint once destroyed.
Stand B15
Forescout
Forescout Technologies, Inc., a global cybersecurity leader, continuously identifies, protects and helps ensure the compliance of all managed and unmanaged cyber assets – IT, IoT, IoMT and OT. For more than 20 years, Fortune 100 organizations and government agencies have trusted Forescout to provide vendor-agnostic, automated cybersecurity at scale.
The Forescout Platform delivers comprehensive capabilities for network security, risk and exposure management, and extended detection and response. With seamless context sharing and workflow orchestration via ecosystem partners, it enables customers to more effectively manage cyber risk and mitigate threats.
Stand E30
Hexegic
Hexegic is an award-winning NCSC Assured Cyber Security Consultancy. We provide governments and high performing businesses the tools, resources and insights to make them resilient and empower them to successfully achieve their missions.
We take pride in working with some of the best organisations, technologies and people to drive innovation and deliver impact across the data and cyber domains, tackling complex problems head-on, together. Our multi-disciplinary teams challenge orthodoxy and work to derive unrealised insights from data and counter complex threats for our clients, always driven by our ethos to deliver excellence differently.

Stand B2
HP Inc.
HP Inc. is a global technology company focused on personal computing and printing solutions. Formed in 2015 after the split of Hewlett-Packard, HP Inc. designs and sells laptops, desktops, workstations, monitors, printers, and related supplies and services.
The company serves consumers, small and medium businesses, enterprises, and governments worldwide. HP is known for innovation in hardware design, security, and sustainability, emphasizing energy efficiency and responsible manufacturing. Headquartered in Palo Alto, California, HP Inc. operates in more than 170 countries and partners widely across the technology ecosystem. Its history traces back to 1939 and founders Bill Hewlett and Dave Packard together.

Stand E28 Island
Island is the developer of the Enterprise Browser – the ideal enterprise workplace, where work flows freely while remaining fundamentally secure. With the core needs of the enterprise naturally embedded in the browser itself, Island gives organizations complete control, visibility, and governance over the last mile, while delivering the same smooth Chromium-based browser experience users expect.
Stand F25
Kocho
Kocho is the UK’s leading Microsoft partner for identity, security, and digital transformation solutions for enterprise and SME organisations.
Recognised as an 8-time winner of Microsoft’s Partner of the Year Award, we provide IT consulting, professional services and managed services for some of the UK biggest organisations, such as Bupa, Aviva, Kingfisher and Informa helping them with their secure digital transformation needs.
By combining the power of Microsoft cloud technology with world-class identity, cyber security and our team of brilliant people - Kocho take our clients on a journey of secure transformation.
Stand SS11 (Scotland Street) Leidos
Accelerating cybersecurity in a changing world
Adversaries seek undetected access to your systems and data, constantly looking for vulnerabilities that give them a way in. But when you’re steps ahead of the adversary, there is no way in.
Steeped in hacker techniques and cyber AI expertise, Leidos anticipates adversarial approaches and rapidly prevents, defends, deters and defeats cyberattacks. We provide research-backed offensive, defensive and cyber resilience capabilities and workforce development to continually stay ahead of evolving threats – and we invest boldly to keep it that way.
PREMIUM EXHIBITORS_
Stand E21 Leonardo
Leonardo is an international industrial group, among the main global companies in Aerospace, Defence, and Security (AD&S). With over 60,000 employees worldwide, the company approaches global security through the Helicopters, Electronics, Aeronautics, Cyber & Security and Space sectors, and is a partner on the most important international programmes such as Eurofighter, JSF, NH 90, FREMM, GCAP, and Eurodrone.
The Cyber & Security Division are a trusted security partner to the Defence, UK Government and Critical National Infrastructure sectors. A NCSC certified consultancy in security risk management, and a recognised and proven specialist in operational secure solutions and services.
Stand F29 Methods
Methods is a leading UK-based digital transformation partner and cyber security consultancy, trusted to deliver NCSCassured services across public and private sectors.
Our services span identity & access management, security architecture, risk-management, secure design, governance, audit & assurance, and secure cloud operations — all aligned with the highest standards including NCSC, Cyber Essentials Plus, and relevant compliance frameworks.
As a professional member of the UK Cyber Security Council and accredited by leading industry bodies, Methods brings deep expertise, government-grade security clearance, and a pragmatic, vendor-agnostic approach to help organisations build resilient, compliant digital environments ready for tomorrow’s threats
Stand E26
Netskope
Netskope is a leader in modern security, networking, and analytics for the cloud and AI era. The unique architecture of its Netskope One platform enables real-time, context-based security for people, devices, and data wherever they go, and optimizes network performance—without trade-offs or sacrifices.
Thousands of customers and partners trust the Netskope One platform, its patented Zero Trust Engine, and its powerful NewEdge Network to reduce risk, simplify converged infrastructure, and provide full visibility and control over cloud, AI, SaaS, web, and private application activity.
Stand F19 Northrop Grumman
We have a proven track record of delivering advanced solutions to the defence, space and security community, working together to solve their hardest challenges across every domain.
We are an industry leader in solutions that harness the latest in data science, machine learning and secure cloud transformation technology, delivered at pace and scale.
Operating from more than ten sites across the UK, we sustain employment for more than 5,000 people in the many British SMEs and partners in our supply chain. As a British business we are committed to generating long-term prosperity and social value in the UK.
Stand D22
Nozomi Networks
Nozomi Networks protects the world’s critical infrastructure from cyber threats. Our platform uniquely combines network and endpoint visibility, threat detection, and AI-powered analysis for faster, more effective incident response. Customers rely on us to minimize risk and complexity while maximizing operational resilience.

Stand E23 Obrela
Obrela is a global cybersecurity provider delivering outcome-driven, risk-aligned security operations that enable organizations to anticipate, prevent, detect, and respond to cyber threats through a unified model combining advanced technology, human expertise, and continuous risk visibility.
Our services include Managed Detection & Response (MDR), Managed Risk & Controls (MRC), Digital Forensics & Incident Response (DFIR), and Continuous Threat Exposure Management (CTEM). Swordfish, our proprietary Cyber Operations Command Center, unifies threat, risk, and business intelligence into a single operational model. Recognized by Gartner and Forrester and supported by CREST certified experts, Obrela is a trusted partner in building cyber resilience.
Stand D6
For the last 20 years OPSWAT, a global leader in IT, OT, and ICS critical infrastructure cybersecurity, has continuously evolved an end-to-end solutions platform that gives public and private sector organizations and enterprises the critical advantage needed to protect their complex networks and ensure compliance. Empowered by a “Trust no file. Trust no device. ™” philosophy, OPSWAT solves customers’ challenges around the world with solutions and patented technologies across every level of their infrastructure, securing their networks, data, and devices, and preventing known and unknown threats, zero-day attacks, and malware.
Discover how OPSWAT protects the world’s critical infrastructure and helps secure our way of life; visit opswat.com.
Stand D24 PointWire
PointWire is a specialist SME delivering advanced cyber security engineering and security services to Public Sector and Critical National Infrastructure organisations. We provide deep technical expertise across secure architecture, system integration, vulnerability management, and operational security. All our engineers hold DV clearance, enabling us to operate confidently within sensitive and mission critical environments.
We partner with Government and CNI clients to solve complex security challenges, strengthen resilience, and drive secure digital transformation, tailored to each customer.
At PointWire, we focus on precision, trust, and measurable outcomes, enhancing security posture and supporting long term success.
PREMIUM EXHIBITORS_
Stand C19
QinetiQ
QinetiQ is an integrated global defence and security company focused on mission-led innovation. Our purpose is protecting lives by serving the national security interests of our customers.
We employ more than 8,000 highly-skilled people, committed to creating new ways of testing technologies, systems, and processes to make sure they meet operational needs; and enabling customers to deploy new and enhanced capabilities with the assurance they will deliver the performance required.
Stand E24 Rapid7
Rapid7, Inc. (NASDAQ: RPD) is dedicated to creating a safer, simpler, and more accessible digital world. We empower security professionals to manage the modern attack surface through a combination of best-in-class technology, leading-edge research, and broad strategic expertise. Our comprehensive security solutions help over 11,000 global customers unite cloud risk management and threat detection.
By providing speed and precision, we enable organisations to significantly reduce their attack surface and eliminate threats effectively.
Stand A18
Raytheon
With over 2,000 employees in the UK, Raytheon UK is a major supplier and systems integrator to the UK Ministry of Defence that designs, develops and manufactures defence and space products. The company is also a leading provider of training transformations services and continues to invest in research and development, supporting innovation and technological advances across the country. Raytheon UK is part of RTX’s Raytheon business.
Stand E19
Reliance Cyber
Reliance Cyber is a leading MSSP with 20+ years of experience delivering advanced security solutions.
We combine deep technical expertise with proven methodologies to help organisations detect, prevent and recover from evolving threats. Trusted across all sectors, we build resilience with a 24x7x365 SOC, providing managed services, including MDR, EDR and SASE.
Our proactive consulting spans threat intelligence, crisis simulations, and compromise assessments, while our reactive capabilities offer CREST certified, NCSC assured incident response and digital forensics. We empower clients to navigate the changing threat landscape with confidence, ensuring security remains a business enabler.
Stand C11 Roke
At Roke, we stand at the forefront of defence and security, delivering cutting-edge intelligence and engineering solutions that protect nations, troops, borders, critical national infrastructure and businesses. We bring the credibility of a long-standing defence and security leader, the precision of a specialist, and the agility to solve complex, high-stakes challenges with purpose and impact.
Roke is at the forefront of shaping the future of digital defence, intelligence, and national security.
Stand E11 SANS Institute
Launched in 1989 as a cooperative for information security thought leadership, SANS Institute is the largest and most trusted provider of cybersecurity training, certifications, programs, and resources in the world. Our ongoing mission is to empower current and future cybersecurity practitioners with practical skills and knowledge that make the digital world safer, and to support the global cybersecurity community at every stage of their journey.
Stand E20 Searchlight Cyber
Searchlight Cyber was founded in 2017 with a mission to stop threat actors from operating with impunity.
Its Preemptive Threat Exposure Management Platform helps organisations identify, understand, and reduce external cyber risk before attacks occur, combining Dark Web Intelligence & Investigations, Attack Surface Management, and cyber risk quantification to deliver early visibility into real world threat exposure.
Trusted by leading global enterprises, government and law enforcement agencies, and security teams worldwide, Searchlight Cyber shifts security from reactive defence to proactive threat prevention. Find out more at www.slcyber.io or follow Searchlight Cyber on LinkedIn and Twitter.

Stand D20 SpectorOps
BloodHound Enterprise is the go-to platform for Attack Path Management, empowering identity and security teams with continuous prioritisation, remediation guidance and verification and reporting metrics that let you see improvement over time in reducing identity attack paths.
Beloved by hundreds of global corporations and government departments, BloodHound Enterprise dramatically reduces the risk of lateral movement and privilege escalation in Active Directory, Azure AD / Entra ID, and hybrid Azure environments. BloodHound Enterprise is made by SpecterOps, is designated FedRAMP High by the U.S. FedRAMP program, and complies with SOC 2 Types 1 & 2 and ISO 27001 & 27017. Learn more: specterops.io/bloodhound-overview/
PREMIUM EXHIBITORS_
Stand B13
The CRC Network
The Cyber Resilience Centre Network (CRC Network) supports SMEs and third-sector organisations through nine regional Centres across England and Wales. As a police-led, business-focused organisation, we provide guidance and signposting to trusted government tools and resources. Through our Cyber PATH programme, we offer a range of technical services that give SMEs access to essential cyber support at no cost, while enabling cyber students to gain valuable real-world experience. Our mission is to help organisations strengthen their cyber resilience, protecting themselves, their customers, and their supply chains.

Stand B9 Thinkst Canary
Most companies discover they’ve been breached way too late. Thinkst Canary fixes this: just 2 minutes of setup; no ongoing overhead; nearly 0 false positives, and you can detect attackers long before they dig in. Check out why our Canaries are deployed + loved on all 7 continents: canary. tools/love
Stand E22
Tines
Tines is an intelligent workflow platform that powers the world’s most important workflows. IT and security teams of all sizes, from Fortune 50 to startups, trust Tines for everything from phishing response, vulnerability and patch management, software lifecycle management, employee lifecycle management, and everything in between. Leaders across a wide array of industries –including Canva, Databricks, Elastic, Kayak, Intercom, and McKesson– use Tines AI powered workflows to operate more effectively, mitigate risk, reduce tech debt, and do the work that matters most.
Stand B24 Trellix
Trellix is a global cybersecurity company delivering intelligence-led cyber resilience for security-conscious organizations at any stage in their journey. Transforming over 30 years of threat intelligence into high fidelity detections and automating AI-driven detection and response across cloud, on-premises, air-gapped, and operational technology environments, Trellix helps minimize organizational risk and ensure business continuity. Working with a broad partner ecosystem, global intelligence partners, and trusted collaborators, Trellix helps customers proactively adapt to the evolving threat landscape while strengthening the collective defense against cybercriminals and statesponsored attacks. More at trellix.com
Stand E15
TrendAI™ and Atos: In Partnership
At CYBERUK 2026, Atos and TrendAI™, a business unit of Trend Micro, are joining forces to protect the UK’s most critical organisations. TrendAI brings AI-powered cybersecurity that unifies cyber risk, security operations and protection in a single sovereign platform. Atos delivers sovereign UK operations and environments with securitycleared expertise to safeguard critical operations. Together, we help public sector, defence and regulated organisations keep data UK sovereign, simplify and strengthen security, cut complexity and cost, and build the resilient cyber posture needed to drive better outcomes - now and for the future.
Stand B14 TwinStream
We have developed an enterprise CDS capability, deployed within some of the UK’s most sensitive environments, enabling secure, trusted information exchange across security boundaries. Delivered as a fully managed service, we take responsibility for the complexity of cross domain, enabling organisations to manage risk while supporting operational and mission outcomes. TwinStream combines deep technical expertise with proven operational delivery to provide high-assurance, resilient CDS capability into government and wider enterprise environments.
Stand F21
UK Research and Innovation (UKRI)
UK Research and Innovation (UKRI) is the national funding agency investing in science and research in the UK. It brings together seven Research Councils, Innovate UK, and Research England to create a unified organisation that supports research and innovation across all disciplines and sectors.
UKRI works in partnership with universities, businesses, government, and other stakeholders to drive knowledge creation, economic growth, and societal impact. Its mission is to ensure the UK remains a world leader in research and innovation, tackling global challenges and improving lives.
Stand D16 Ultra I&C
Ultra I&C’s UK Cyber division protects critical communications against sophisticated threats.
As a defence technology leader, we develop advanced cyber and CryptKey solutions for the British government and allied nations. We continuously evolve our capabilities to counter emerging threats and optimise communication performance in challenging environments. Our end-to-end approach transforms innovative concepts into manufactured products with comprehensive support, ensuring our customers stay ahead of evolving security challenges.
PREMIUM EXHIBITORS_
Stand E18
Varonis
Varonis is the leader in data security, fighting a different battle than conventional cybersecurity companies. Our cloud-native Data Security Platform continuously discovers and classifies critical data, removes exposures, and detects advanced threats with AI-powered automation.
Stand D14 Viasat
Viasat is a global communications company that believes everyone and everything in the world can be connected. With offices around the world, our mission shapes how customers, governments and militaries communicate and connect.
Relied upon by over 90 governments around the globe, Viasat International Government is the perfect partner for all your operational requirements and critical missions with a heritage in delivering situational awareness and increased capability to our customers anywhere, anytime.
Stand B12
Zscaler
Zscaler (NASDAQ: ZS) accelerates digital transformation so customers can be more agile, efficient, resilient, and secure. The Zscaler Zero Trust Exchange™ platform protects thousands of customers from cyberattacks and data loss by securely connecting users, devices, and applications in any location.
Distributed across more than 150 data centers globally, the SASE-based Zero Trust Exchange™ is the world’s largest inline cloud security platform.
For ten years, FullProxy has helped shape Scotland’s cyber security landscape. Our experienced consultants combine strategic insight with deep technical expertise to implement and optimise the premium technologies that actionably reduce risk and improve your resilience.

Sensitive networks rely on L3Harris CATAPAN® high-grade encryption to protect critical data, communications and infrastructure.
For more than 20 years, CATAPAN has delivered trusted information assurance and continues to evolve with next-generation performance for secure networks.
Discover the evolution of CATAPAN. Visit L3Harris. Stand D1.



STANDARD EXHIBITORS_
Stand C3
2T Security
2T Security is a British, independent cyber security consultancy specialising in high-threat environments. We deliver expert risk assessment (CAF), advanced SOC solutions, and assured Cross Domain architectures.
Our mission: help government, CNI and defence teams operate securely, confidently, and at pace in the most demanding conditions.
Stand A32 Awerian
A research and technology development consultancy focused on UK defence and national security. Activities include idea generation, proof-of-concept experimentation, design and development, trials and testing, and special product/ demonstrator development, making use of deep expertise in areas such as AI/ML, electronics, FPGA, firmware/software, modelling and simulation, optics, mechanical design and RF.
Stand SS5 (Scotland Street) Barrier
Founded in 2006, Barrier is a Glasgow and Londonbased MSSP and VAR committed to providing advanced cybersecurity solutions. We offer essential services such as penetration testing and incident response to a global clientele. Our extensive expertise assists organisations in building resilience and developing robust defence strategies against evolving cyber threats.
Stand A4 Bureau Veritas Cybersecurity
Bureau Veritas (founded 1828) is a global leader in testing and certification, delivering OT and IT security expertise across IEC 62443 and ISO 27001. We provide CREST-accredited pentesting, risk assessments, audits, security design, training, crisis management, incident response, and due diligence support to strengthen resilience, reduce risk, and ensure compliance.
Stand
B23 CACI LTD
CACI architect, deliver and evolve core mission applications and cloud platforms to enable insights to be obtained from information; supporting our clients to achieve more with less when keeping the UK safe.
We use both commodity technology and accelerate the adoption of emerging technology in support of mission success.
Stand B5 Censys
Censys is the authority for Internet intelligence, delivering the most complete and up-to-date global map of Internet infrastructure. Its industry-leading solutions support attack surface management, threat hunting, and proactive incident response. Governments, Fortune 500 companies, and security teams worldwide trust Censys to uncover risks faster, respond effectively, and prevent breaches before they occur. Learn more at censys.com
Stand B4
Citation Cyber
Citation Cyber is your one-stop-shop for maintaining your cyber health. Powered by our Atlas Hub, that works as an extension of your business, we provide tailored solutions including Cyber Essentials certification, awareness training, penetration testing, policy management, phishing simulations, and 24/7 vulnerability scanning - to increase cyber posture, ensure compliance, and keep businesses secure.
Stand SS9 (Scotland Street) Condatis
Condatis empowers organisations to thrive in the digital economy through trusted digital identities. As Microsoft Elite Partners, we modernise identity, secure hybrid access, and enable seamless experiences. Our expert team delivers secure, scalable IAM solutions that reduce risk and accelerate business value.

Stand B6 Cryptify AB
Cryptify is a high-assurance communication system that seamlessly combines top-tier security with effortless userfriendliness. Certified for use at both the UK OFFICIAL and NATO RESTRICTED security levels, Cryptify Call is already the trusted choice by numerous governments, military forces and enterprises, ensuring day to day confidential communications without compromise.

Stand A28 Cyber Toolkit
Cyber Toolkit is a new service offering many premium cyber tools in a single toolkit, which is free to use for most. Our aim is to provide SME users with advanced technical auditing & monitoring for free while providing larger organisations & managed service providers with effective supply chain & customer risk management.
Stand B19 CyberArk Software UK Ltd
CyberArk is the global leader in identity security, trusted by organizations around the world to secure human and machine identities in the modern enterprise. CyberArk’s AI-powered Identity Security Platform applies intelligent privilege controls to every identity with continuous threat prevention, detection and response across the identity lifecycle.
Stand A30 Cyderes
Our tireless global team specializes in building practical IAM, exposure management, and risk programs, and stopping active threats fast with MDR that works with your existing security tools — all augmented by AI and driven by seasoned operators. We are laser-focused on cybersecurity, arming organizations with the people, platforms, and perspectives they need to conquer whatever tomorrow throws their way.
STANDARD EXHIBITORS_
Stand F11 Factory Internet
Factory Internet provides managed detection and response, penetration testing, and practical advisory support to strengthen cyber resilience. We deliver cost-effective monitoring, alert triage, and ethical testing, and guide organisations through Cyber Essentials, Cyber Essentials Plus, and IASME Assurance with risk-led expertise to improve security while reducing complexity and cost.
Stand D2 GreyNoise Intelligence
GreyNoise empowers defenders to detect attacks at their network edge by surfacing malicious scanning and exploitation activity. Powered by a global deception network and telemetry from billions of daily sessions, we deliver realtime, verifiable intelligence that helps security teams cut through noise and focus on true threats.
Stand F5 GOLDEN VALLEY
A £1bn science and technology cluster located adjacent to GCHQ in Cheltenham, featuring over 1m sqft of commercial space and 1,000 homes. Golden Valley will scale an existing thriving ecosystem, creating a hub for those in security: culminating R&D facilities, academic institutions and a new platform for international events and festivals.
Stand B7 JUMPSEC Ltd
JUMPSEC are a specialist offensive and defensive cyber security consultancy. Our mindset is that attack informs defence. We deliver deep expertise, innovative capabilities, and tailored solutions that help organisations to transform their cyber security securely and confidently.
Stand B25 LRQA
LRQA supports organisations to manage cyber risk and build resilience through an advisory-led, end-to-end cyber security portfolio. From assurance and compliance to continuous monitoring and threat intelligence, our CREST-accredited specialists help protect critical services, strengthen security maturity, and enable confident decision making in an evolving threat landscape.
Stand D4 Nexor
Nexor delivers trusted, sovereign cyber security solutions enabling secure information exchange for Defence, Government, and Law Enforcement. Our Protean platform, high-assurance guards, and advisory services empower organisations to operate securely across connected domains. We combine innovation, engineering, and expertise to advance national resilience and support NCSC’s mission to keep the UK safe online
Stand B11 PQShield
PQShield is a post-quantum cryptography (PQC) company building the quantum-safe cryptography solutions that are modernizing the vital security systems and components of the global technology supply chain. We deliver real-world, high-quality secure implementations of quantum-safe cryptography in hardware, software and the cloud, as well as being a leading contributor to post-quantum cryptography standardization projects around the world.

Stand B18 QA
At QA, we believe the answer to closing your digital skills gap lies with the people you already have, the talent for the future. We’re experts in reskilling, upskilling and apprenticeships. We offer an unrivalled depth of expertise and programme choice, delivered by accredited industry experts with real-world practitioner experience.
Stand F7 Restore Technology
For nearly three decades, Restore Technology has delivered secure, scalable, and sustainable IT lifecycle solutions to the Central Government and Defence sectors. Approved by NPSA and NSCS CAS(S), Restore Technology has the capabilities to deliver Secure Media Destruction and IT Asset Disposal Services – on-site and off-site – for the most data sensitive environments UK-wide.
Stand A6 Reversec
Reversec, a new name in cybersecurity consulting, helps organizations worldwide tackle their most complex cybersecurity challenges. With a focus on continuous research, practical solutions and knowledge sharing, Reversec’s findings provide the rationale behind informed security decisions.
With over 30 years of experience, Reversec brings together the expertise of renowned companies MWR Infosecurity, F-Secure, WithSecure, Digital Assurance, nSense, and Inverse Path.
Stand C5 Salus
Salus is an award-winning cyber consultancy specialising in penetration testing, red teaming, risk, compliance and vCISO consultancy. With consultants in the NCSC’s Industry 100 initiative and clients in over 15 countries, we have the experience and expertise to defend, detect and assure our clients from adversaries and unknown threats.
Stand SS14 (Scotland Street) SCC
SCC is a leading technology partner delivering advanced cyber defence, cloud, digital transformation, and modern workplace services. With major investments, a CREST-accredited SOC, and deep expertise in threat detection, incident response, and security operations, SCC helps organisations reduce risk and operate with confidence.
STANDARD EXHIBITORS_
Stand SS7 (Scotland Street) Schneider Electric
Schneider Electric is a global energy technology leader, driving efficiency and sustainability by electrifying, automating, and digitalizing industries, businesses, and homes. Its technologies enable buildings, data centers, factories, infrastructure, and grids to operate as open, interconnected ecosystems, enhancing performance, resilience, and sustainability. The portfolio includes intelligent devices, software defined architectures, AI powered systems, digital services, and expert advisory.
Stand A24 Silobreaker
Silobreaker is an AI native intelligence platform that unifies external data, analytics and human expertise to deliver highquality insights quickly. Built for security, threat and risk teams, the Silobreaker intelligence engine automates data collection and analysis so organisations can spot threats sooner, make smarter decisions and protect their people, operations and assets with confidence.
Stand F9 Sitehop Ltd
Sitehop is a deep-tech cybersecurity company securing data in motion at ultra-low latency. Our SAFE Series platform delivers hardware first, crypto agile IPsec encryption from 1G–200G with the world’s lowest latency and 90% lower power use. Trusted by Tier One telecoms, BFSI, Government & CNI, Sitehop is advancing post-quantum-ready network security.
Stand F3 Socura
Socura is a Managed Detection and Response provider bringing the power of calm to organisations across the UK. In an ever-changing landscape, we empower teams with the clarity, control, and confidence to minimise cyber security risk and thrive.
Stand B1 Surevine
UK government departments need mission-critical software delivered quickly without compromising security. Surevine mobilise expert teams within days to build secure-by-design solutions, so public servants can launch new services in weeks or months, not years.
Stand SS3 (Scotland Street) Systal Technology Solutions
Systal is a global managed network, cloud, and security transformation specialist, providing strategic technology services for enterprises across 93 countries.
Our end-to-end security capability provides a holistic approach to physical and cyber defence across IT and OT systems, helping organisations identify, protect, respond, and recover from critical cyber-attacks.
Visit: systaltech.com/security

Stand B3 VulnCheck
aSH VulnCheck is the exploit intelligence company helping enterprises, government organizations, and cybersecurity vendors solve the vulnerability prioritization challenge. Trusted by some of the world’s largest organizations responsible for protecting hundreds of millions of systems and people, VulnCheck helps organizations outpace adversaries by providing the most comprehensive, real-time vulnerability intelligence.
Stand SS16 Waterstons Ltd (Scotland Street)
Waterstons has helped organisations get technology working properly since 1994, meaning better decision making, improved day-to-day operations, and delivering change that sticks.
We cover everything from in-house IT management, cyber security and data analysis, to consulting, M&A, and bespoke software, bringing hands-on experience to help you move forward with confidence.
Stand B27 WorkNest Secure
At WorkNest Secure we offer a unique combination of automation technology and highly trained specialists, making staying ahead of threats simple. Unlock stronger customer trust and loyalty with proven improvements in your security posture.


SME EXHIBITORS_
Stand F16 Assurix
Assurix is a UK based, evidence led trustmark that independently verifies MSP security and operational maturity through continuous monitoring, enforcement, and alignment with the UK Cyber Security and Resilience Bill.
Stand SS6 (Scotland Street) Closed Door Security
Professional cyber security services that protect your business from evolving threats, with comprehensive penetration testing and security assessments.

Stand SS8 (Scotland Street) i-confidential
i confidential is an employee owned cyber and technology risk consultancy helping organisations become secure and resilient. We help clients understand the business impact of security risks through tailored frameworks, controls and expert consultants that strengthen resilience.
Stand SS2 (Scotland Street) Kick ICT Group
Kick is a UK IT services provider delivering cyber security, cloud, communications and business applications. Our KickSecure services help organisations reduce risk, strengthen resilience and stay protected in an evolving threat landscape.
Stand G17 Indelible Data Ltd
Indelible Data is a leading NCSC-approved Cyber Essentials and Cyber Essentials Plus Certification Body. We also specialise in Defence Cyber Certification (DCC), high quality penetration testing, and vulnerability scanning.

Stand F20 Lab539
We hunt threats, disrupt adversaries, and craft tailored defences. We specialise in proactive threat intelligence that enables organisations to disrupt account takeover attacks before they start.
Stand F18 lowRISC
lowRISC is a not for profit company using collaborative engineering to develop and maintain open source silicon designs and tools, through a unique combination of skills, expertise and vision.

Stand F12 Opliciti
Opliciti delivers tailored cyber resilience and security managed services for organisations of all sizes, providing accessible protection for SMBs and personal cyber support for individuals to defend against evolving threats.
Stand SS4 (Scotland Street) Lupovis
Lupovis provides deception environments implemented by clusters of decoys that acquire extensive malicious attack data globally.
The pre-emptive cyber defence posture provides contextual threat intelligence in real-time when deployed outside of networks and manages attackers that have penetrated a network.
Stand SS12 (Scotland Street) OSP Cyber Academy
OSP Cyber Academy delivers engaging, compliance-ready cyber security and data protection training, blending expert consultancy, gamified learning, and outsourced DPO support to build resilient organisations, leaders, and young digital citizens.
Stand G13
Report URI
Discover and reduce unseen browser-side risks, exposing real attacks and security failures - giving security leaders the ability to prevent breaches before they happen.
ROOTWALL.AI
Stand G11
ROOTWALL.AI
ROOTWALL.AI responds to attacks by engaging the originating ISP, enabling local law enforcement and rapid disruption. Attackers notice this pressure and move on to easier targets. Welcome to Active Defense

Stand F14
Salt Communications
Salt Communications provides a secure mobile solution for sharing sensitive information. With total confidence in our solution, organisations have a powerful ally, accelerating decision making, increase productivity and drive efficiency.
Stand SS10 (Scotland Street) The Cyber Scheme
We are a leading UK and international training and assessment body for the technical cybersecurity industry, providing NCSC Certified training, assessments for Government schemes and professional title registration in multiple disciplines.
Stand G15 SCI Semiconductor
SCI Semiconductor designs secure, high-assurance semiconductor solutions, embedding hardware-level cybersecurity to protect data, systems, and infrastructure across mission-critical and high-reliability applications.

Stand G9 Wolf Network Security
Wolf Network Security is a transparent, client-focused cybersecurity consultancy delivering penetration testing, Cyber Essentials and continuous testing. We hunt the threats that keep you up at night.
Stand G19
Xewli
Xewli is an innovative cyber security company from West Yorkshire, researching and developing components for Advanced Mobile Solutions, including multi-domain endpoints, cross domain gateways, and ephemeral edge servers.
Stand F10 Zaizi
Zaizi delivers government technology solutions working side by side with public sector teams to fix broken systems into joined up services that are simpler for users, safer to run and stronger for the future.
GOVERNMENT EXHIBITORS_

Stand G35 Cymru Wales
Wales is a dynamic cyber security powerhouse, giving investors access to top talent, cutting-edge innovation, a supportive government, and a collaborative ecosystem to build, test and scale world-leading secure solutions.
Stand F30 Dstl
Dstl is the Ministry of Defence’s science and technology organisation, providing unique expertise, crucial insights and delivering battlewinning solutions for the benefit of the nation and allies.
Stand G27
Government Cyber Unit and Government Cyber Profession
The Government Cyber Unit and Government Cyber Profession strengthen UK cyber resilience by driving cross-government strategy, standards, assurance and incident coordination, while developing the specialist workforce, capability frameworks and technical expertise needed to secure public services.
Stand F34
Ministry of Housing, Communities and Local Government (MHCLG -
Local Digital)
Local Digital is a team within the Ministry of Housing, Communities and Local Government that helps councils deliver cost-effective, cyber-secure, user-centred public services by sharing digital and cyber expertise.
Stand G25 HMGCC
HMGCC works with the national security community, UK government, academia and private sector partners to bring engineering ingenuity to the national security mission, creating tools and technologies that help protect the nation.
Stand G29 MOD
Cyber Confident is MOD’s narrative led, positivity first approach to human risk in cyber. Replacing stick with carrot, they drive engagement across various demographics to improve overall cyber hygiene within the MOD.
Stand G31
National Crime Agency
The National Cyber Crime Unit within the NCA leads the UK’s response to cybercrime, including the UK’s investigative capabilities and providing specialist cyber support, to safeguard UK citizens from cybercriminals.
Stand F36
National Cyber Force (GCHQ)
The NCF is a defence and intelligence partnership, operating in and through cyberspace to keep the country safe and protect and promote the UK’s interests at home and abroad.

Stand F32 Ofcom
Ofcom is the UK’s communications regulator. We oversee the security and resilience of telecoms and digital infrastructure (in future including data centres) and telecoms fraud.
Stand F38 Rosa Service Organisation
Rosa is the UK government’s only cross-government SECRET IT platform, enabling secure communication, collaboration and information sharing across government departments and international partners.
Stand F40
Software Ambassador Scheme & PSTI
DDSIT ensures safe development and deployment of technologies across the UK, driving digital government, benefiting citizens The primary purpose of OPSS is to protect people and places from product-related harm.
ACADEMIA EXHIBITORS_

Stand F2 CHEDDAR
Cheddar Hub is the UK’s national research consortium advancing next-generation communications and distributed cloud computing, pioneering 6G connectivity, AI-native networks, sustainable infrastructure, and human-centric technologies in collaboration with top universities.
Stand F6 CSIT, Queen’s University Belfast
CSIT is the UK’s Innovation and Knowledge Centre for cyber security. Home to the Cyber-AI Hub, we combine research and industry collaboration to secure cyber physical systems and drive economic impact.
Stand G5 CRANE
CRANE is an EPSRC-funded network to strengthen the UK’s cybersecurity research ecosystem. We evaluate new technologies and threats, and provide opportunities for novel research that will bring tangible cybersecurity interventions.
Stand F8 CyBOK Community
Interest Company
CyBOK (Cyber Security Body of Knowledge) Community Interest Company is an independent, not‑for profit organisation dedicated to eliminating global cyber security capability gaps through developing, curating, and disseminating cyber security knowledge.
Stand G3
Glasgow Cyber Defence Lab: University of Glasgow
The University of Glasgow’s Cyber Defence Lab pioneers research in digital resilience and cybersecurity with a focus on industrial technologies and networks found within Critical National Infrastructure (CNI) sectors.
Stand F4 Hacktivity Cyber Security Labs
Hands-on cyber security education through randomised virtual environments, CTF challenges, games, and CyBOK-mapped courses. Used by universities and industry for ethical hacking and defensive security training.
Stand G1 Information Security Group, Royal Holloway
The Information Security Group is an interdisciplinary department based at Royal Holloway University of London. Our mission is to innovate information and cyber security practice through worldleading education and research.
Stand G7 Lancaster University
Lancaster University delivers impactful, world class interdisciplinary academic cyber capability to keep nations and citizens prosperous, secure and resilient amid complex, volatile and uncertain geopolitical and technological disruption.


SME INNOVATION ZONE
HOSTED BY DSIT_
Stand IVC-1
Cavero Quantum
Cavero is building the trust layer for connected devices, combining continuous authentication and crypto-agile key exchange to secure the edge today and enable the transition to post-quantum security.
Stand IVC-3 Cyber Innovations
Cyber Innovations creates research-backed human-layer cyber resilience solutions that support organisations before, during, and after cyber incidents through practical preparedness, response guidance, recovery support, and assurance-focused tools.
Juliet t
Stand IVC-5 Juliett
Juliett provides intelligence-led threat assessments that model how capable adversaries see your organisation, delivering practitionerled, decision-grade insight on exposure and risk for security, risk, and executive leaders.
Stand IVC-2 CloudpeekAI
One missed threat is one too many. CloudPeek orchestrates across your existing security tooling and any data source - cloud, on-prem or air-gapped - with autonomy that scales from simple triage to complex multi-step investigations. Built for defence, government and critical infrastructure.
Stand IVC-4 Hacktonics
Hacktonics delivers scalable Operational Technology Cyber Security training to build organisational resilience in protecting critical infrastructures. Our innovative platform and equipment develops and measures capability against current and future threats.
Stand IVC-7 PA Consulting
We believe in the power of ingenuity to build a positive human future. We combine innovative thinking and breakthrough technologies to progress further, faster. Our clients adapt and transform, and together we achieve enduring results.
Stand IVC-6 MyCena Limited
MyCena is a patented credential control platform that removes human-managed credentials, so there is nothing to phish, share or steal. Attackers don’t break in, they log in. MyCena makes that impossible.
Stand IVC-8 Photarix
Photarix is a Lancaster University spin-out developing semiconductor quantum light sources at telecom wavelengths, enabling compact, scalable and practical photonic hardware for secure communications and future quantum-secure infrastructure.

Stand IVC-9 PRAEFERRE
Praeferre is a unified Agentic GRC and AI Governance platform. We help enterprises and government entities automate complex privacy, security, and compliance workflows, moving away from manual silos to a real-time, AI driven operating system for data sovereignty.
Stand IVC-10 Reliable Insights
Reliable Insights provides deterministic, explainable AI for cyberphysical infrastructure. Our platform analyses time-series data to detect anomalies, identify emerging risks, and support the secure, resilient operation of industrial and critical systems.
Stand IVC-11
Unhacked™
Unhacked’s mission is to uplift the cybersecurity of the UK at scale. Our consumer-grade SaaS helps mass market SMEs to get their cyber fundamentals right - at the speed of AI.
Stand IVC-12 VIVIDA
Multi-award winning VIVIDA helps organisations security communicate risk in ways employees understand, engage with and act on using social media-style reels, interactive scenarios and escape rooms to drive behaviour change.
A SPECIAL THANKS TO ALL OUR SPONSORS_
WITH THANKS TO OUR LEAD SPONSORS